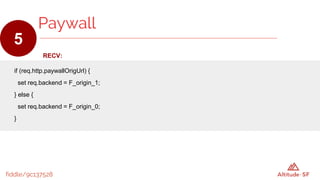
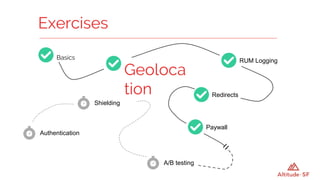
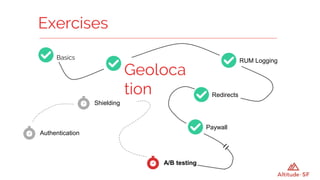
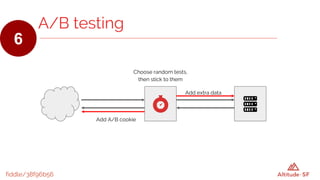
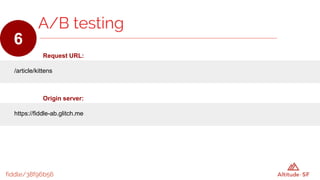
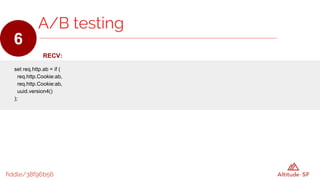
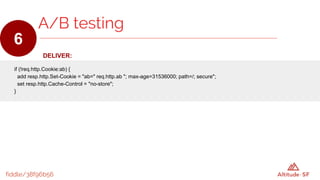
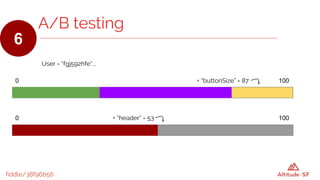
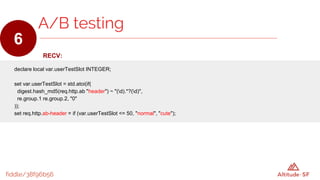
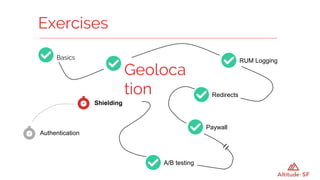
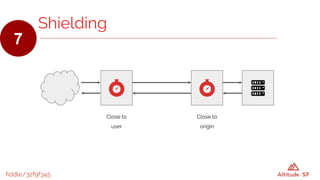
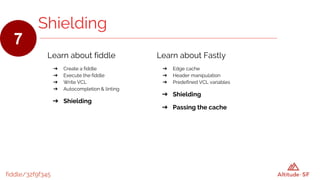
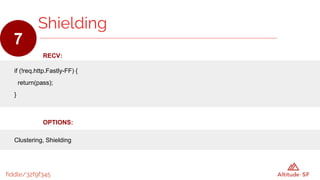
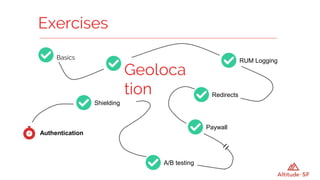
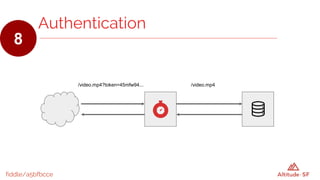
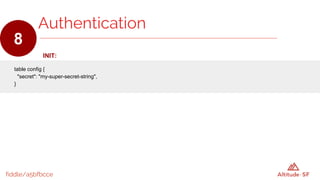
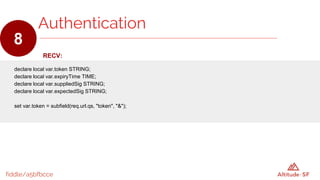
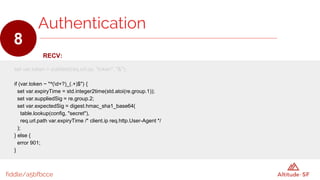
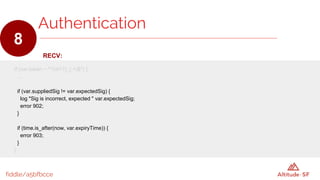
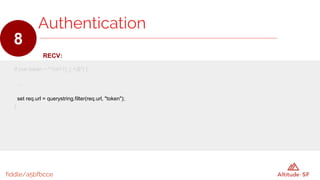
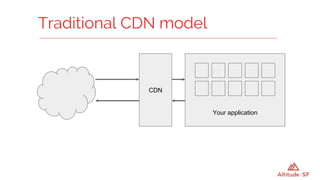
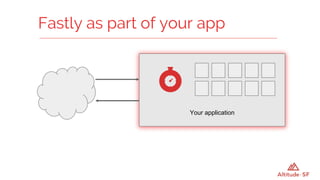
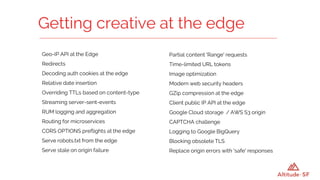
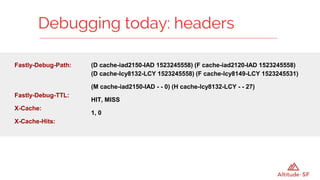
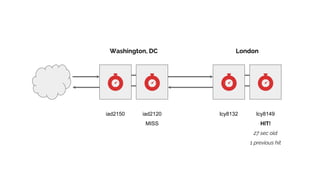
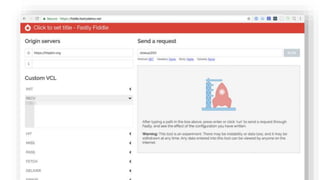
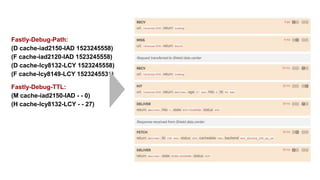
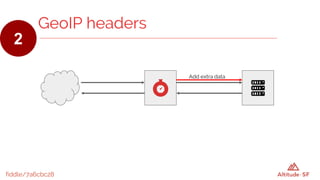
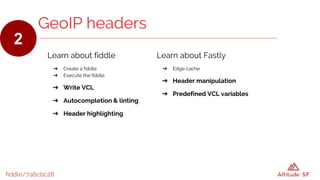
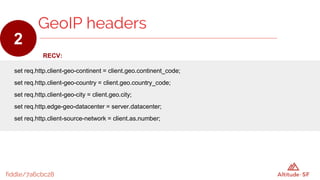
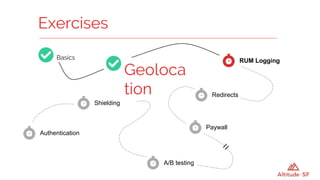
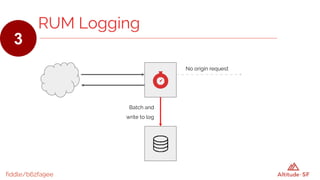
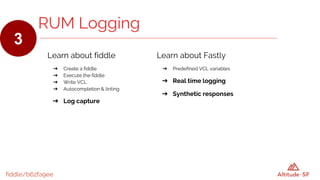
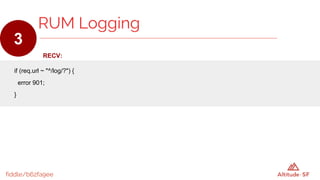
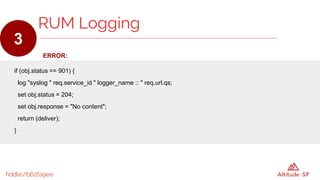
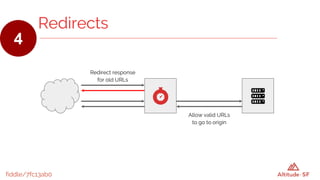
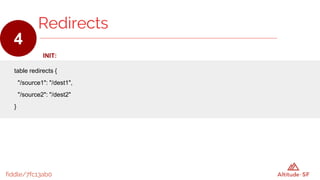
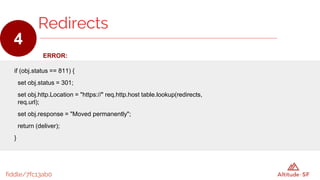
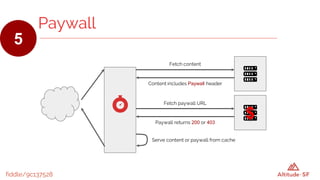
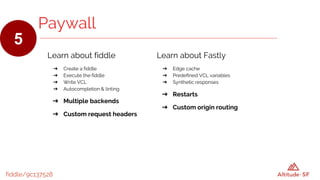
The document discusses the features and functionalities of Fastly's CDN, focusing on edge programming techniques. It covers a variety of topics including geo-location, logging, redirects, paywalls, A/B testing, authentication, and caching, with practical examples provided through 'fiddles'. Users are encouraged to explore Fastly's demos and engage with the community for further advancements in edge programming.


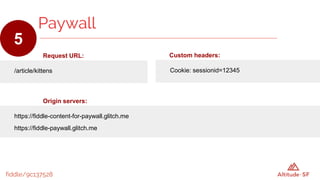
![fiddle/9c137528
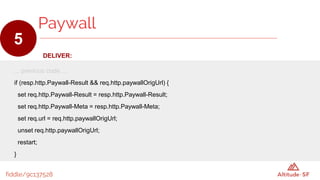
DELIVER:
if (resp.http.Paywall ~ "^https?://[^/]+(.*)$" && !req.http.Paywall-Result) {
set req.http.paywallOrigUrl = req.url;
set req.url = re.group.1;
restart;
}
Paywall
5](https://image.slidesharecdn.com/andrewbettsprogrammingtheedgeworkshop-180925015006/85/Altitude-San-Francisco-2018-Programming-the-Edge-39-320.jpg)