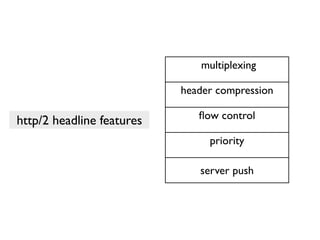
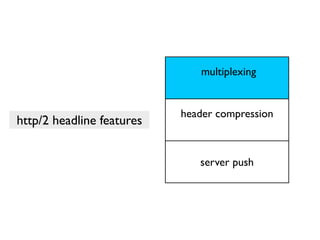
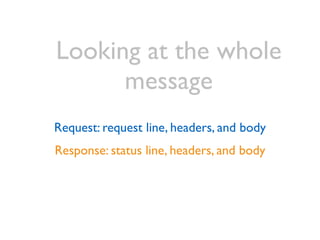
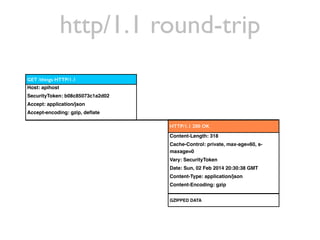
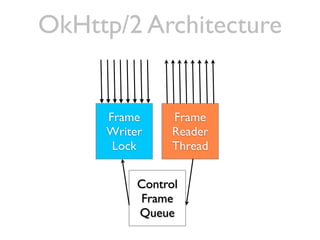
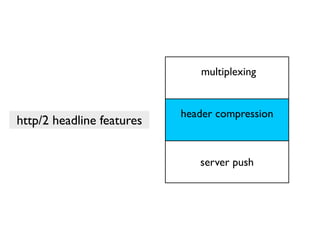
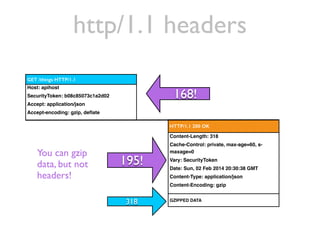
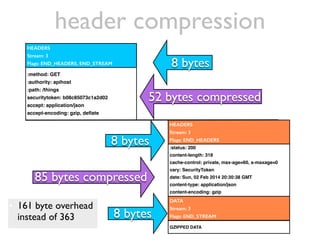
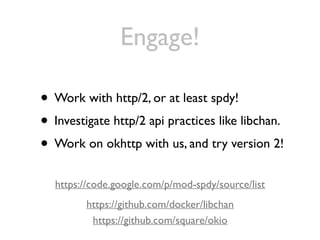
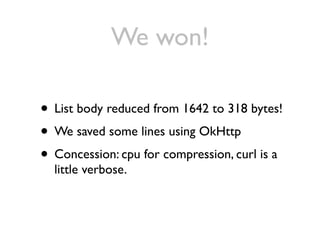
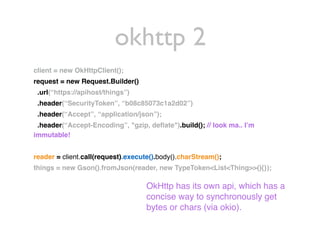
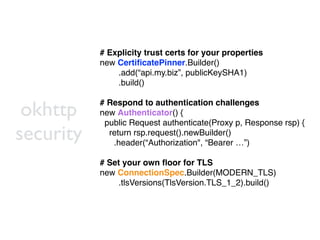
The document discusses the implementation and advantages of using HTTP/2 with OkHttp in Java for building efficient HTTP APIs. It covers the features of OkHttp, including support for HTTP/2, websocket, and capabilities for handling request/response efficiently through compression and caching. The text also highlights performance improvements and best practices for using the OkHttp library in client-server communication.












![HttpUrlConnection
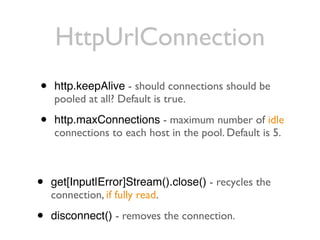
• http.keepAlive - should connections should be
pooled at all? Default is true.
• http.maxConnections - maximum number of idle
connections to each host in the pool. Default is 5.
• get[Input|Error]Stream().close() - recycles the
connection, if fully read.
• disconnect() - removes the connection.](https://image.slidesharecdn.com/efficienthttpapis-140204093354-phpapp02/85/Efficient-HTTP-Apis-25-320.jpg)