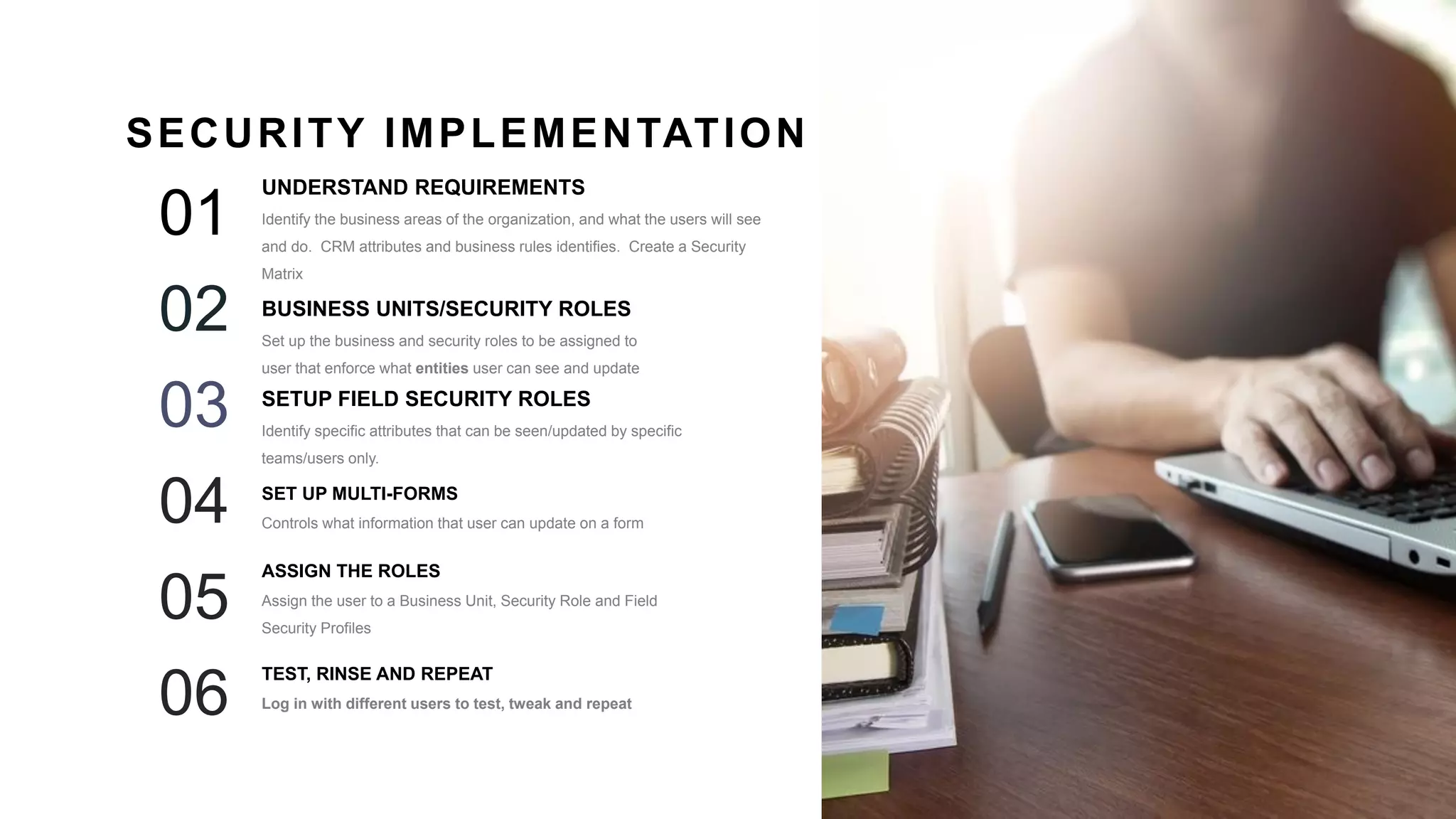
The document outlines a detailed workshop on CRM workflows, business rules, security, and troubleshooting, including hands-on practice and scenarios. It discusses the importance of automating tasks for efficiency, defining workflows, and managing security roles to ensure proper access to CRM functionality. The content emphasizes the necessity of understanding user needs and the processes involved in CRM implementations.






![21
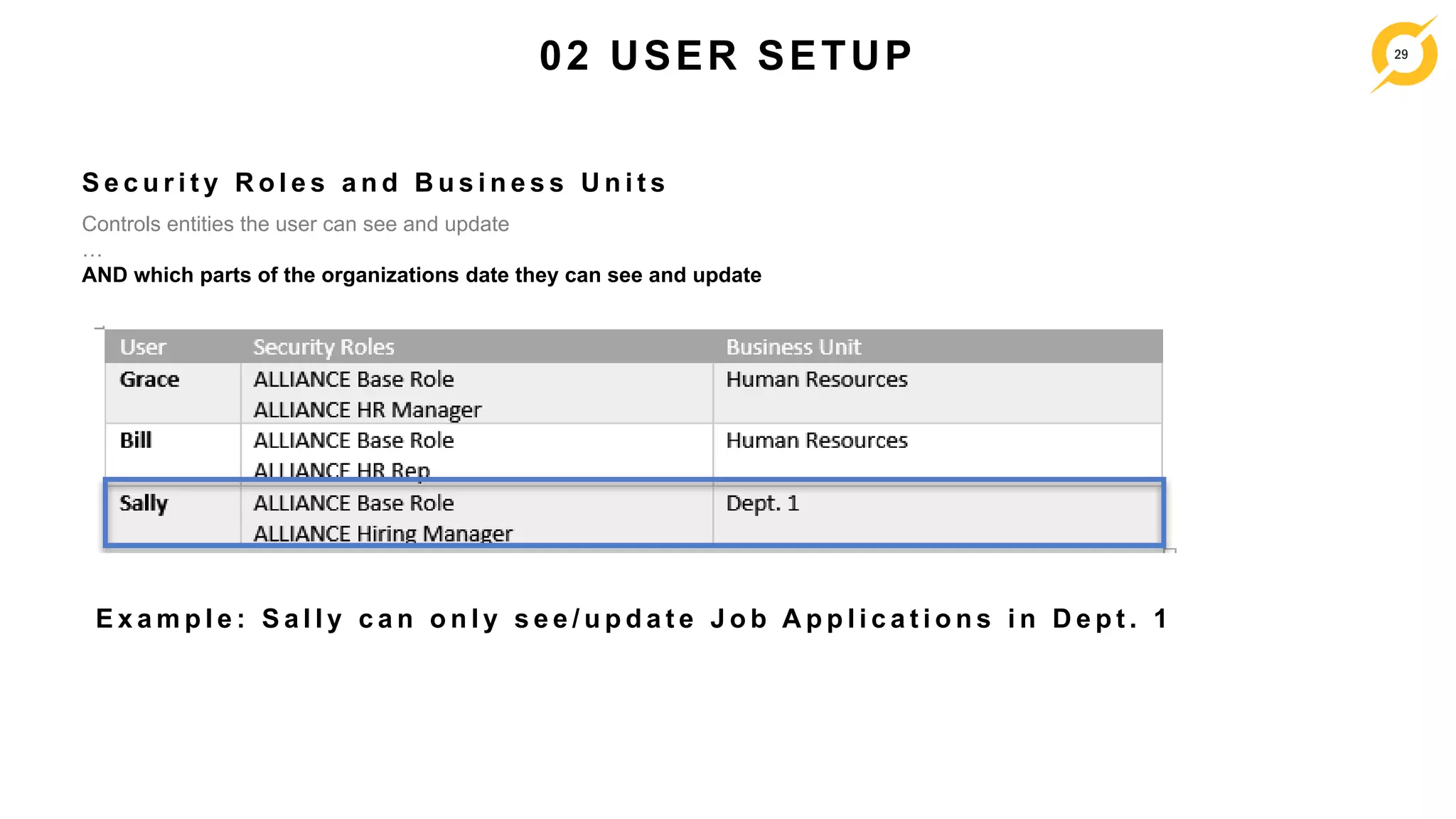
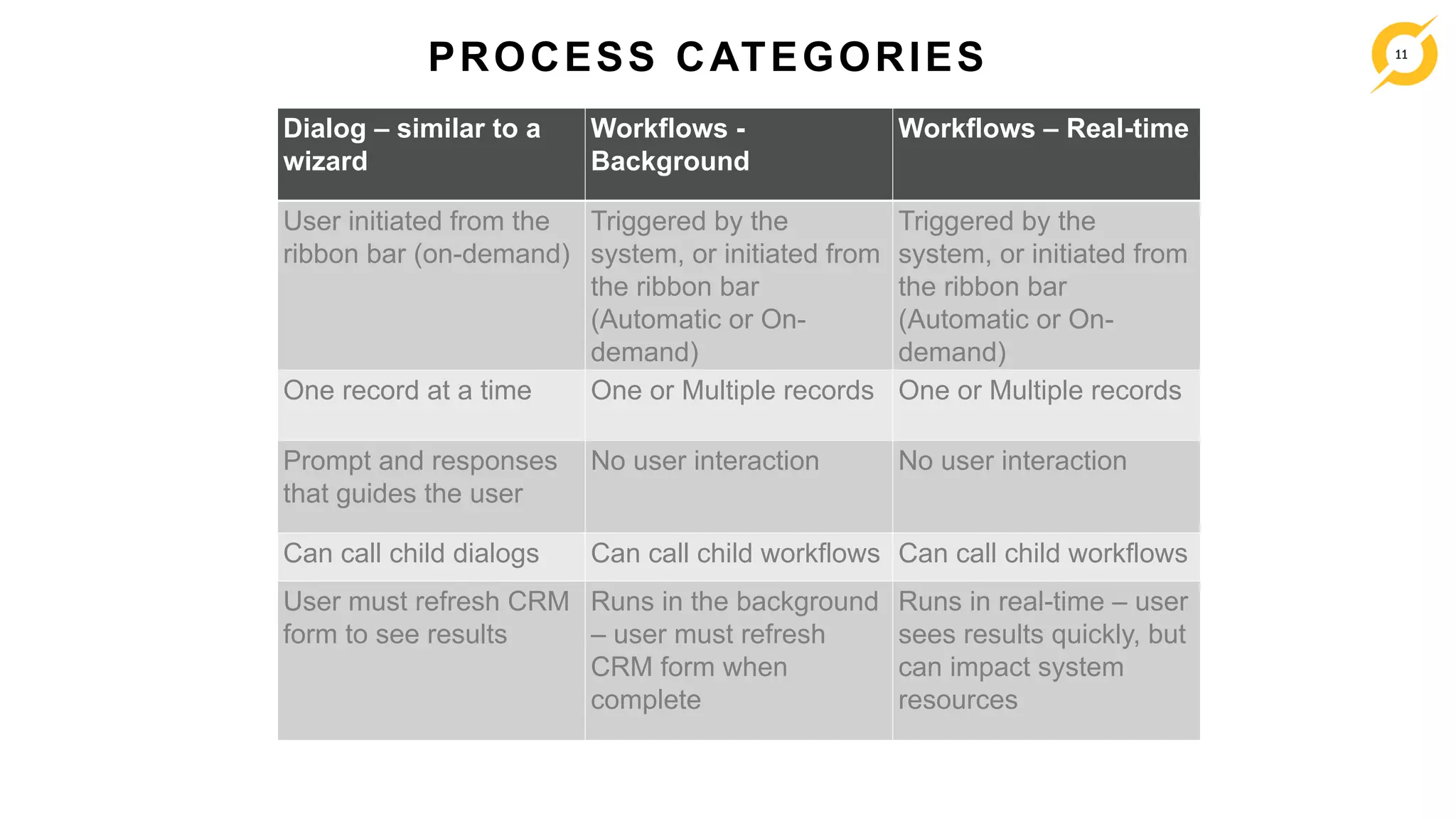
01 DEFINE - SCENARIO
Step Action Who System Details
1 Send paper application Applicant Nothing
2 HR Rep fills in application in CRM from a Contact HR Rep Default status = New
Application Date – Recommend to set to Today’s Date when New
Job Posting
3 HR Rep performs the initial screening HR Rep Date Screening Completed
4 HR Rep approves the application for Interviewing HR Rep Set Status to “Interviewing”
5 System triggers an email on the Status change to
Interviewing and sends it to the Hiring Manager
System Create Email
6 Hiring Manager gets the email and reviews the
application.
Interview the candidates
Hiring Manager Create Tasks/appointments/Notes to manage the interview process
Rank
Date Interviews completed
7-1 REJECT: Hiring Manager Rejects candidates Hiring Manager Date Rejected/Withdrawn
Cancel/Withdrawn Reason
Cancel/Withdrawn Reason Description
7-2 OFFER: Hiring Manager approves to Offer Hiring Manager Click on Approval to Offer
Set Date Offered
Add offer details to the Notes
[System changes status to “Offer”]
8 System triggers an email on the status change to
Offer and sends it to the HR Manager
System Create email
9 HR Manager reviews offer and approves the Hire HR Manager Expected Start Date – validate date is future
Date Hired
Final Decision Notes
Add details to the Notes
Click on Approval to Hire
[System changes status to “Hired”]
[System update the Date Hired on the Contact]](https://image.slidesharecdn.com/alliance2017-crmtraining25-01-2017-170201145239/75/Alliance-2017-CRM-Deep-Dive-Workflows-Business-Rules-Security-and-Troubleshooting-21-2048.jpg)
![22
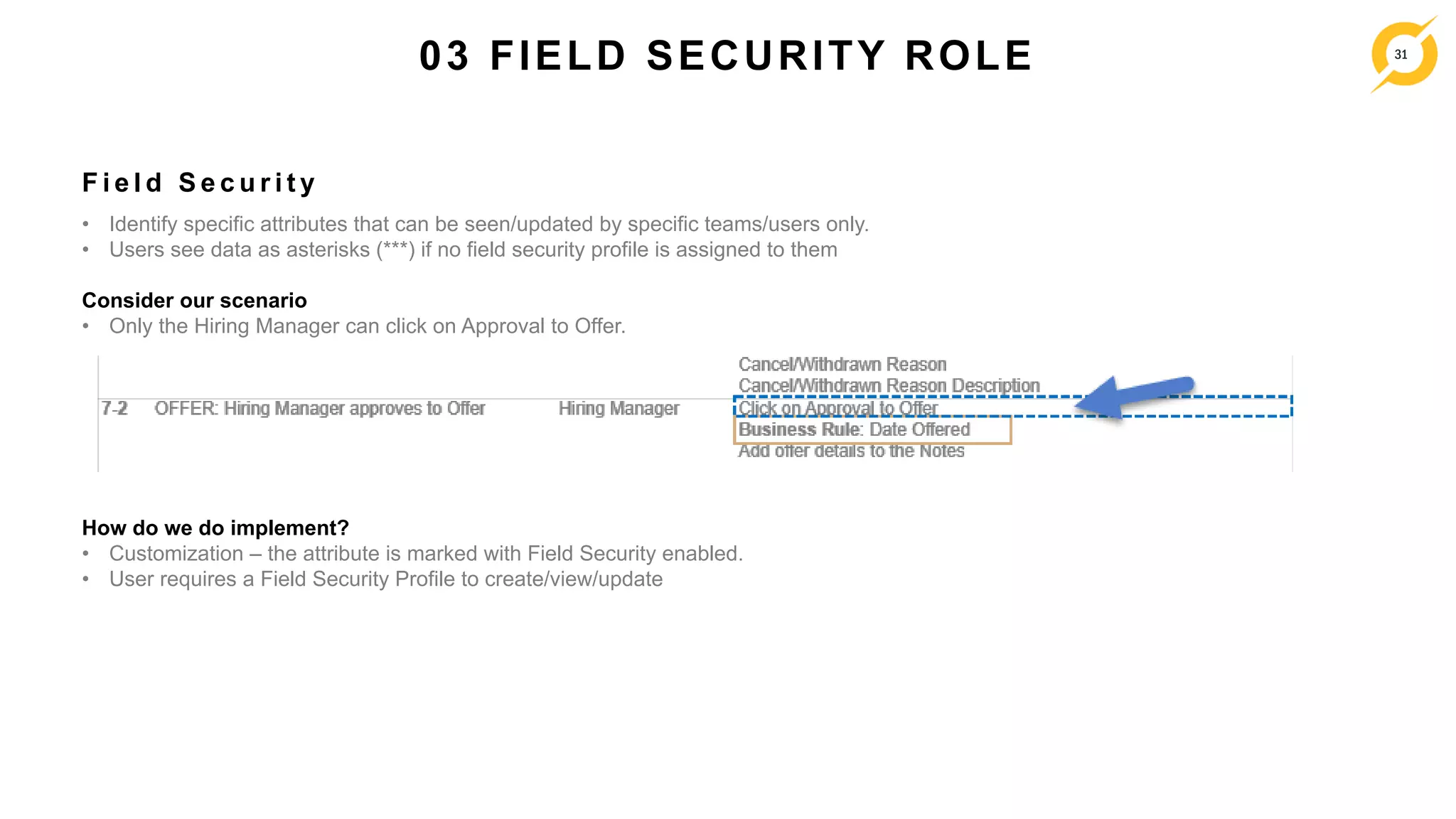
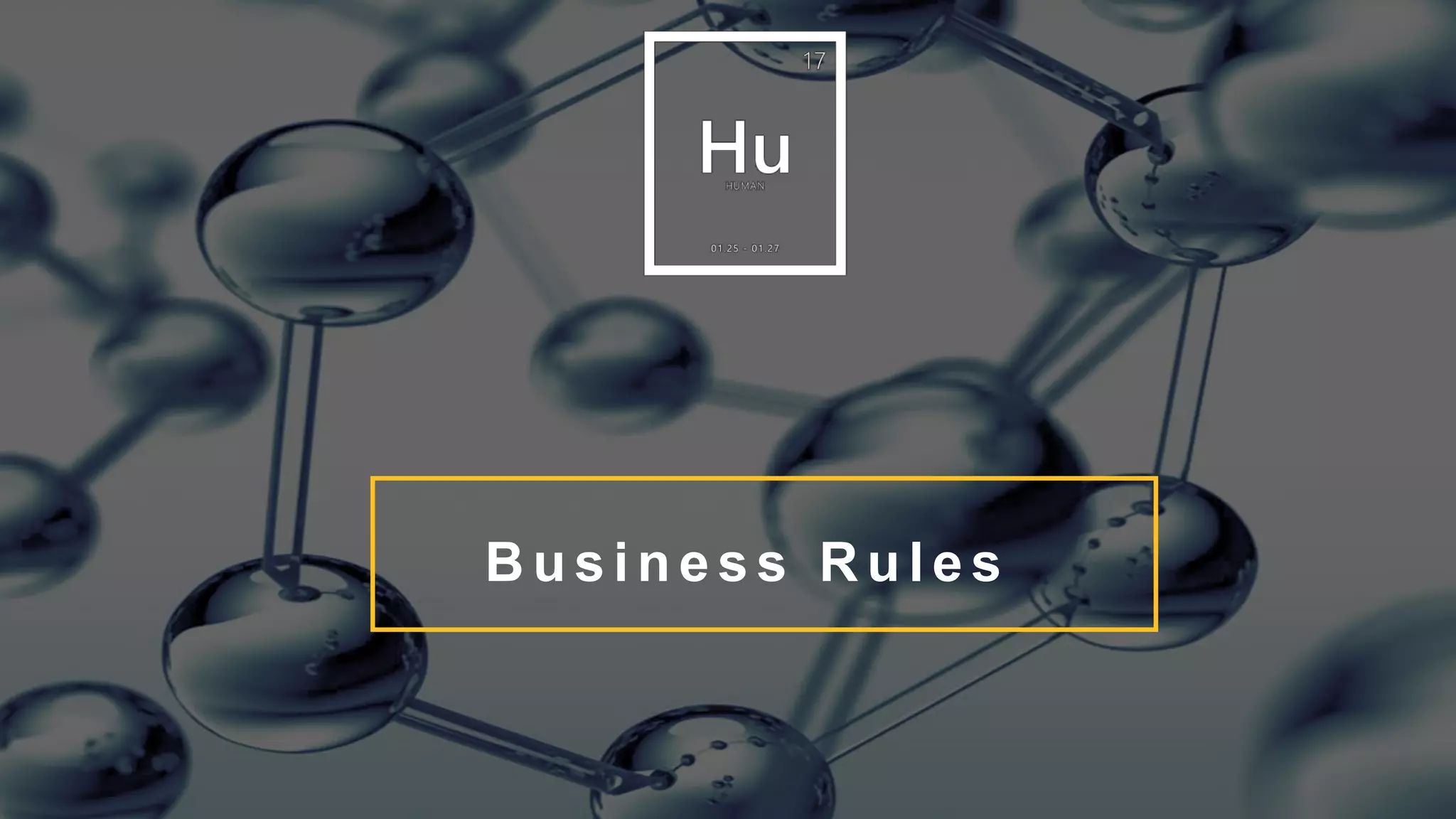
02 ANALYZE - DESIGN
Step Action Who System Details
1 Send paper application Applicant Nothing
2 HR Rep fills in application in CRM from a Contact HR Rep Business Rule: Default status = New
Application Date – Recommend to set to Today’s Date when New
Job Posting
3 HR Rep performs the initial screening HR Rep Date Screening Completed
4 HR Rep approves the application for Interviewing HR Rep Set Status to “Interviewing”
5 System triggers an email on the Status change to
Interviewing and sends it to the Hiring Manager
System Workflow: Create Email
6 Hiring Manager gets the email and reviews the
application.
Interview the candidates
Hiring Manager Create Tasks/appointments/Notes to manage the interview process
Rank
Date Interviews completed
7-1 REJECT: Hiring Manager Rejects candidates Hiring Manager Date Rejected/Withdrawn
Cancel/Withdrawn Reason
Cancel/Withdrawn Reason Description
7-2 OFFER: Hiring Manager approves to Offer Hiring Manager Click on Approval to Offer
Business Rule: Date Offered
Add offer details to the Notes
Workflow: [System changes status to “Offer”]
8 System triggers an email on the status change to
Offer and sends it to the HR Manager
System Workflow: Create email
9 HR Manager reviews offer and approves the Hire HR Manager Expected Start Date – Real-Time Workflow: validate date is future
Date Hired
Final Decision Notes
Add details to the Notes
Click on Approval to Hire
Workflow: [System changes status to “Hired”]
Workflow: [System update the Date Hired on the Contact]](https://image.slidesharecdn.com/alliance2017-crmtraining25-01-2017-170201145239/75/Alliance-2017-CRM-Deep-Dive-Workflows-Business-Rules-Security-and-Troubleshooting-22-2048.jpg)
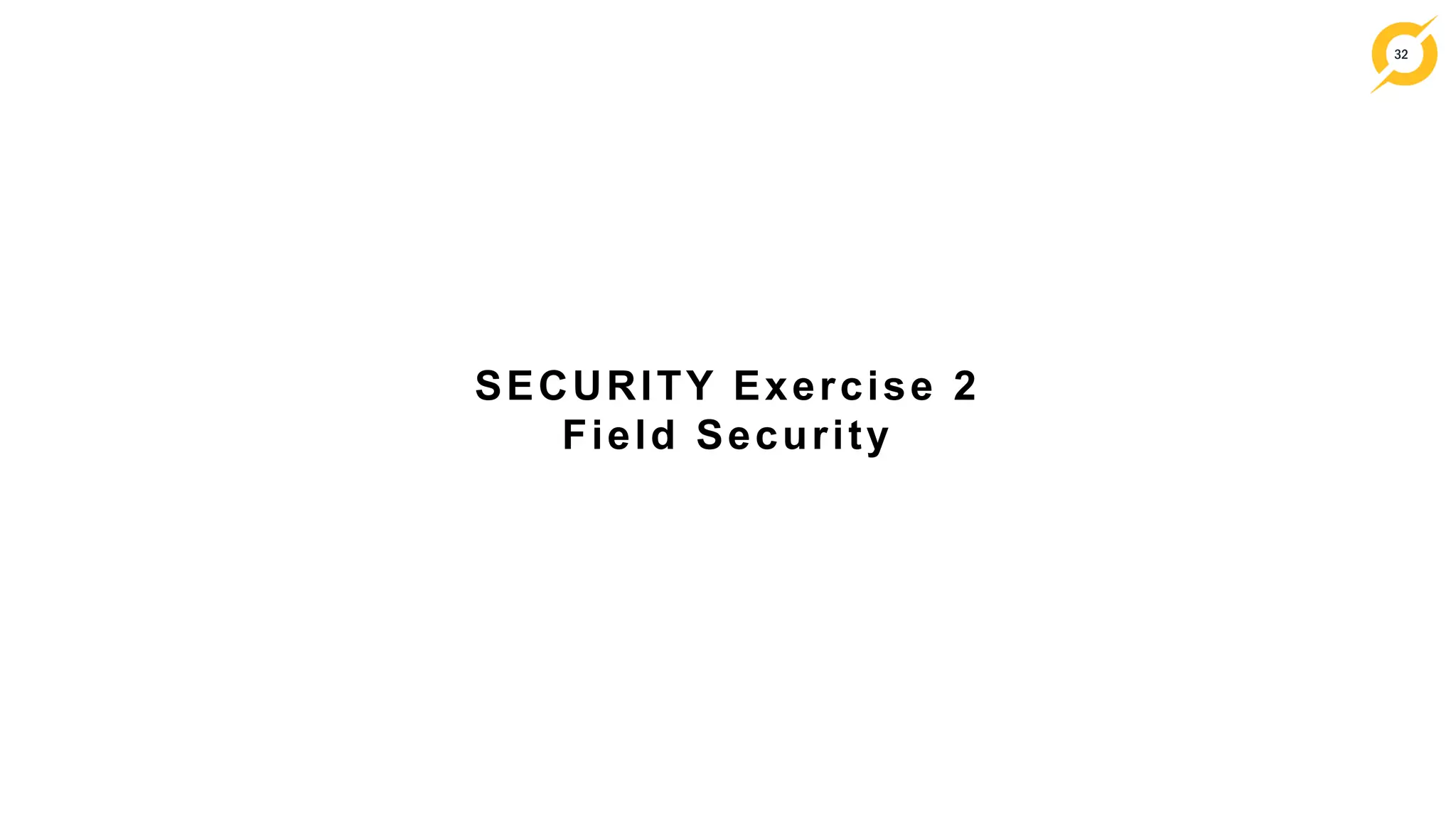
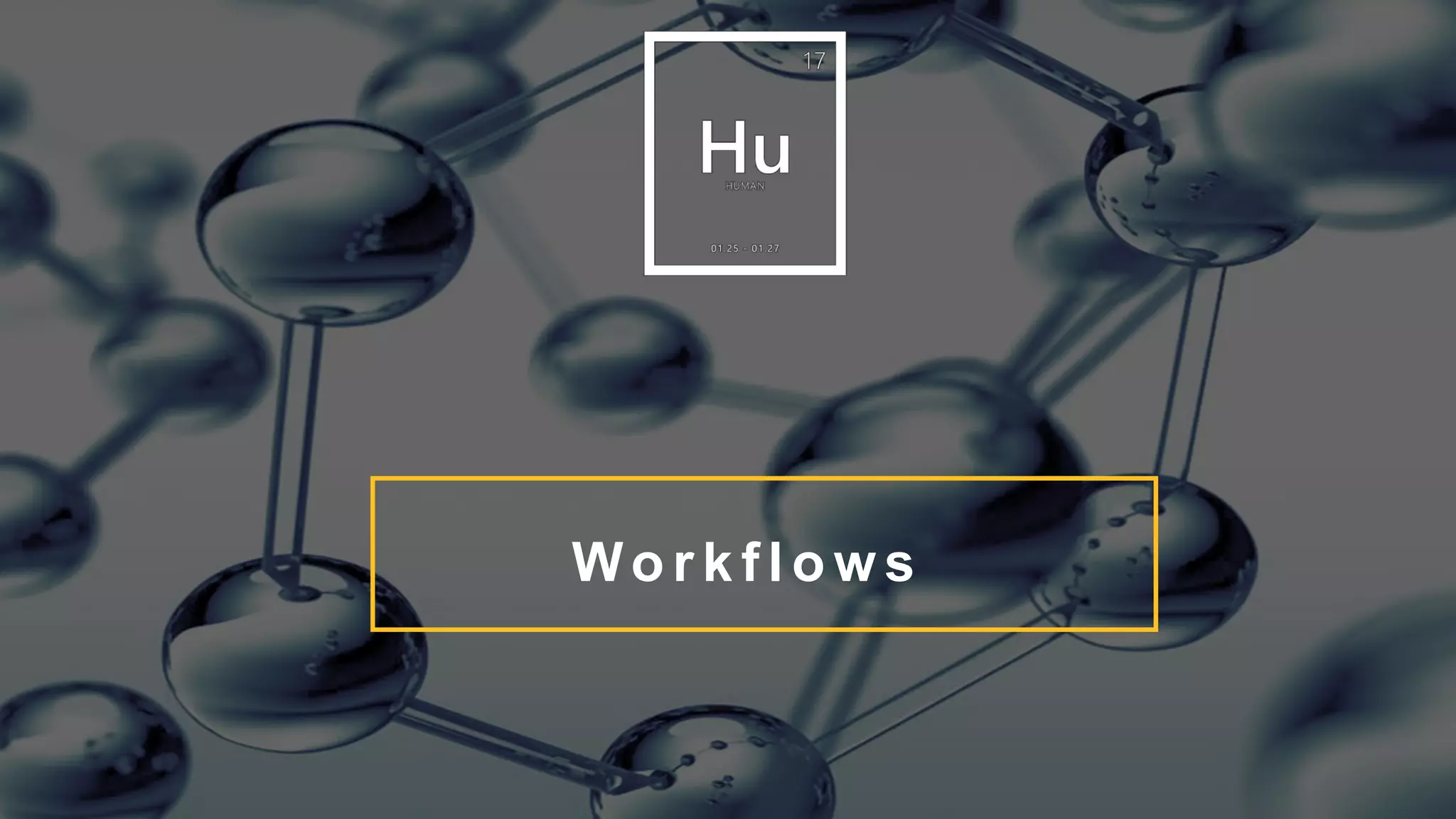
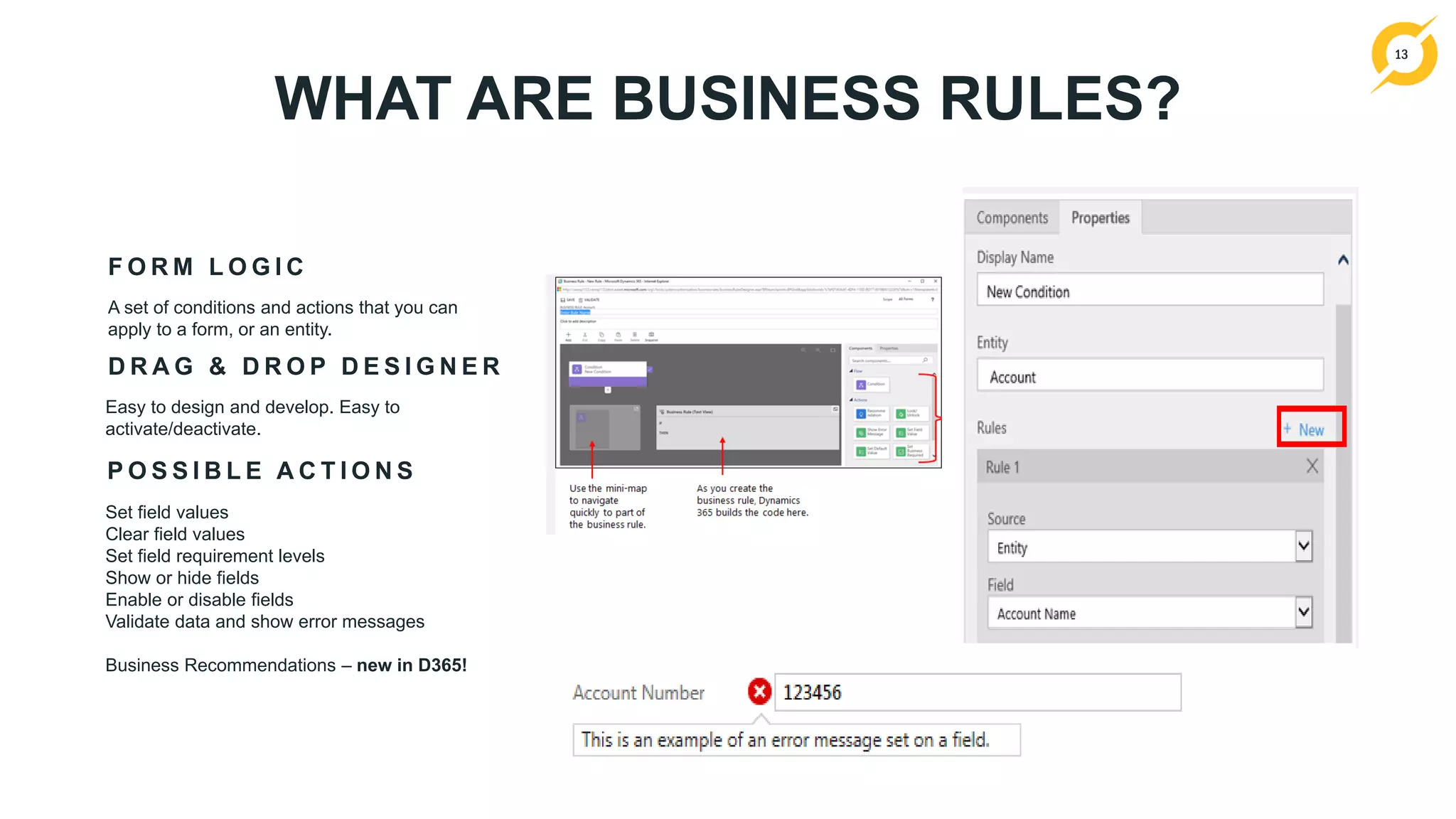
![26
HR
Rep
[Bill]
HR
Manager
[Grace]
Hiring Manager
[Sally]
Add Job
Application
Yes No No
Read Job
Applications
All All Only within the
Department
Approve to Offer No Yes Yes
Approve to Hire No Yes No
Reject No Yes Yes
Can Import Job
Applications
Yes No No
Can Customize No No No
Can create and
publish
workflows?
No Yes No
CXO Levels
HR Rep
[Bill]
HR Manager
[Grace]
Dept. 1
Director
Dept. 1
Hiring
Manager
[Sally]
Dept. 2
Director
Dept. 2
Hiring
Manager
Dept. 2
Hiring
Manager
What entities can users see?
What entities can users update?
This example is a simplistic version of a security matrix
S e c u r i t y M a t r i x
What are the organizational areas of the
business that users are associated with?
W h o a r e t h e u s e r s ?
01 UNDERSTAND REQUIREMENTS](https://image.slidesharecdn.com/alliance2017-crmtraining25-01-2017-170201145239/75/Alliance-2017-CRM-Deep-Dive-Workflows-Business-Rules-Security-and-Troubleshooting-26-2048.jpg)
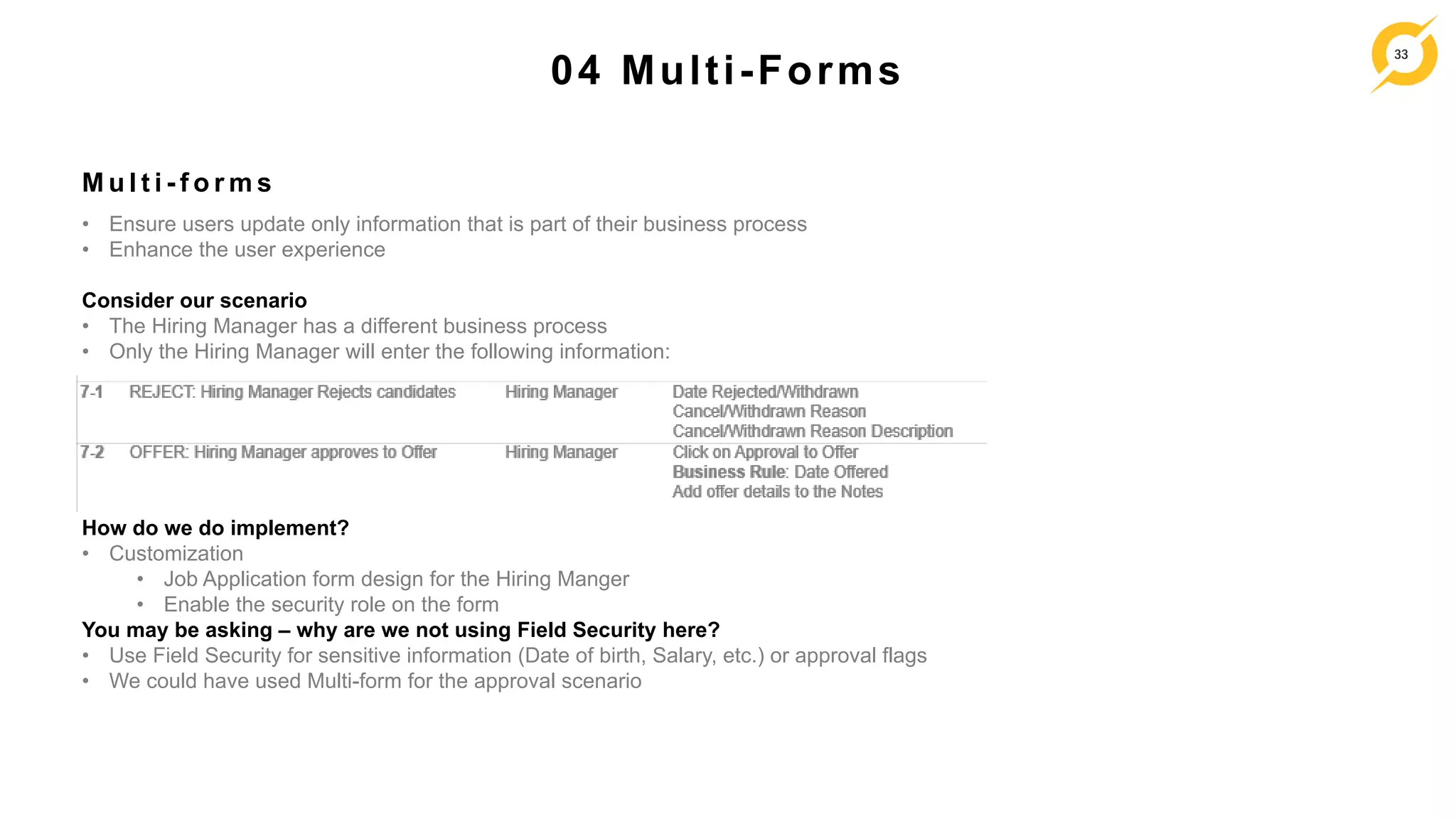
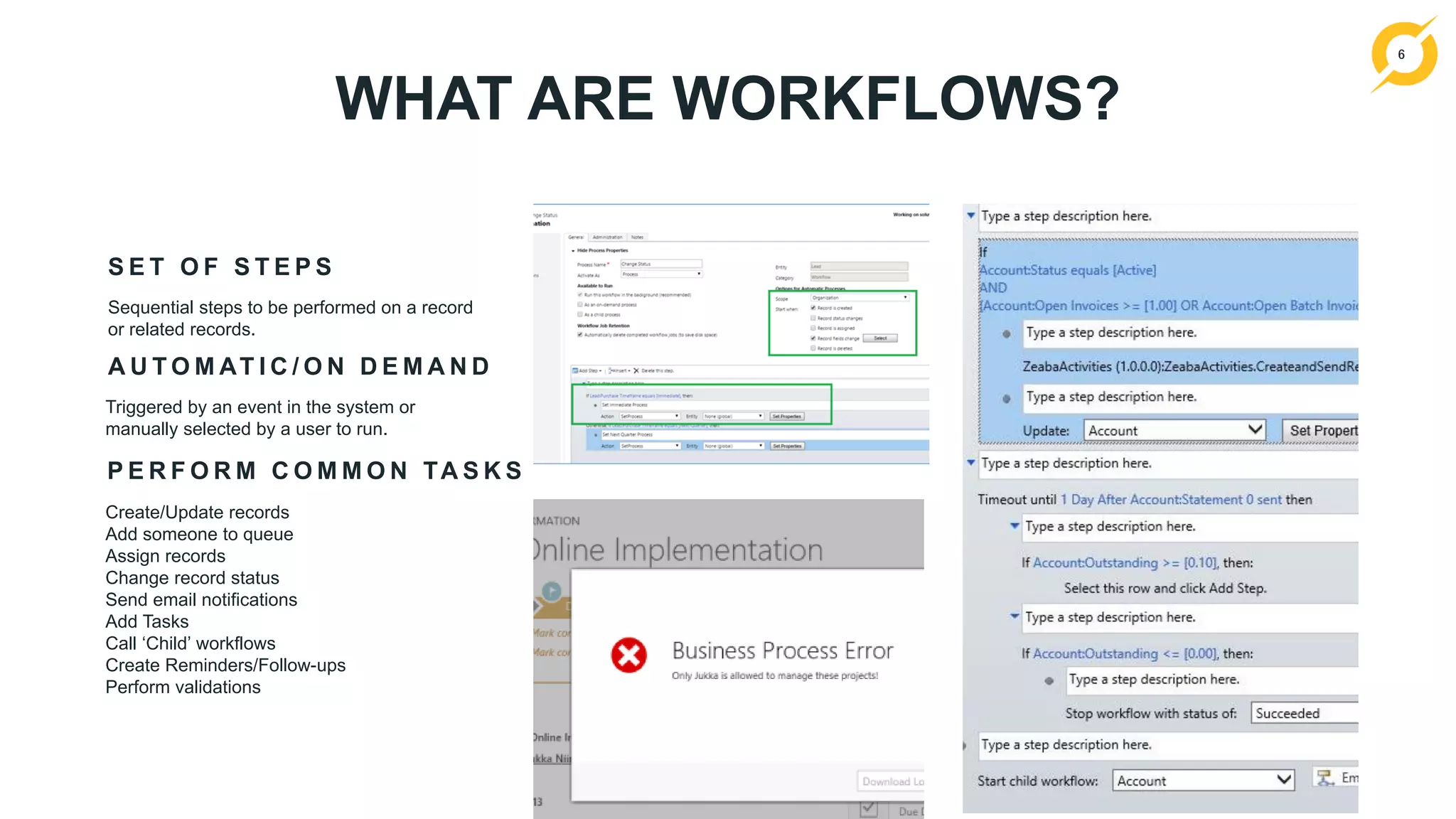
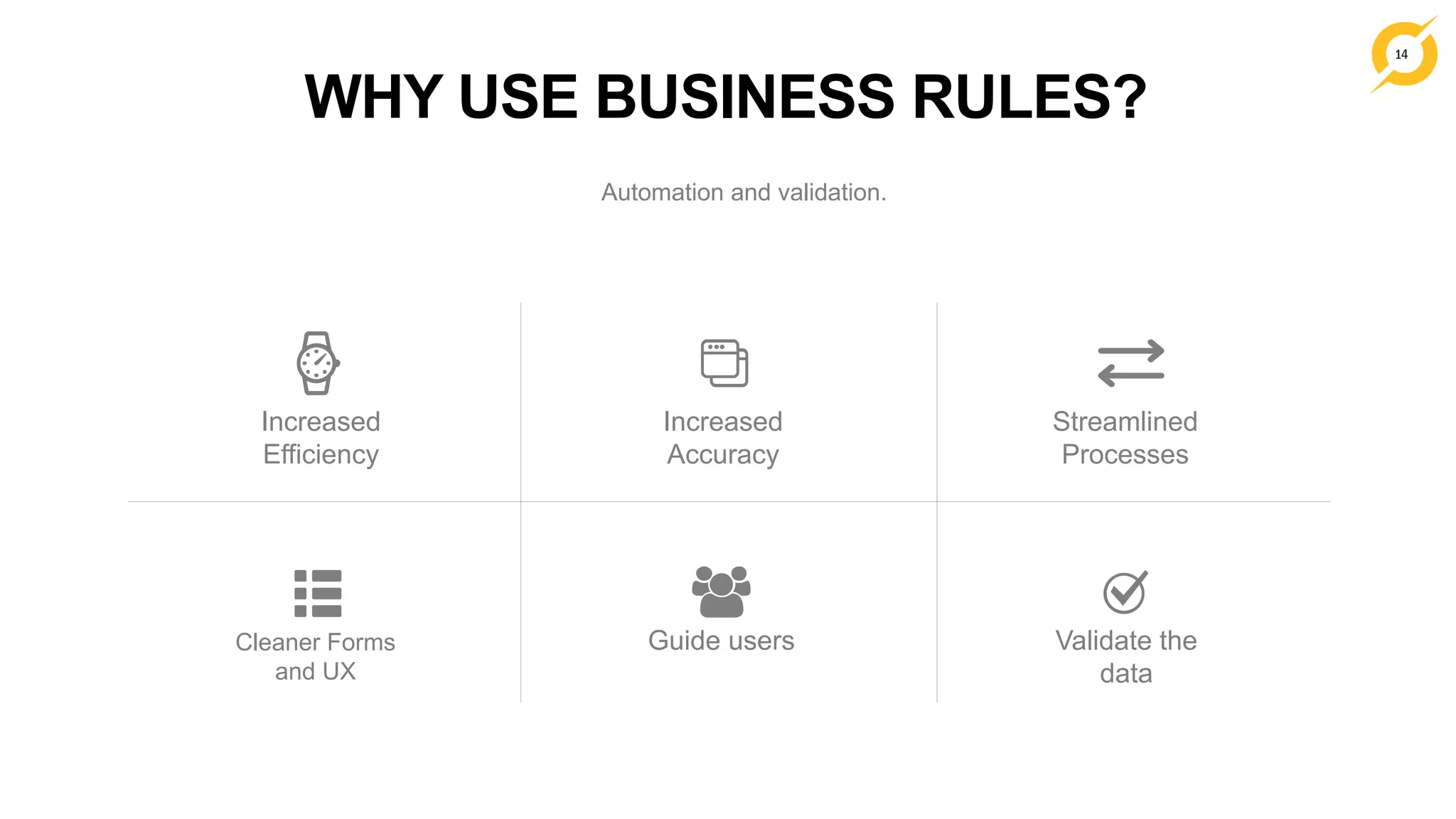
![27
• Users are assigned to a Business Units.
• Indirectly, records owned by users are
also owned by the Business Unit
B u s i n e s s U n i t s
02 BUSINESS UNITS
The Org
Dept. 2
z
IT
Human
Resources
[Bill]
[Grace]
Operations
Dept. 1
[Sally]
Marketing](https://image.slidesharecdn.com/alliance2017-crmtraining25-01-2017-170201145239/75/Alliance-2017-CRM-Deep-Dive-Workflows-Business-Rules-Security-and-Troubleshooting-27-2048.jpg)
![28
What entities can they see and/or update.
S e c u r i t y R o l e – w h a t i s i t ?
02 SECURITY ROLES
E x a m p l e : H i r i n g M a n a g e r
Entity
Create Read Write Delete Append Append To Assign Share
Contact No
[None]
All
[Organization]
Yes No All All No No
Activities All All If owner
[User]
No All All In Dept In Dept
Job Posting No Yes No No All All No No
Job Application No Yes In Dept and subordinate
[Parent: Child Business Units]
No All In Dept In Dept Yes](https://image.slidesharecdn.com/alliance2017-crmtraining25-01-2017-170201145239/75/Alliance-2017-CRM-Deep-Dive-Workflows-Business-Rules-Security-and-Troubleshooting-28-2048.jpg)