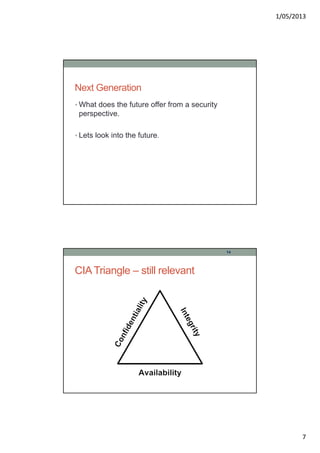
This document summarizes a presentation on the future of information security. It discusses trends that will impact security such as increased network speeds, wireless devices, cloud computing and the internet of things. It also covers issues like the decline of traditional computers, increased cyber attacks, the importance of online identity, hacktivism, and the need for improved security training and qualifications. The document concludes that the complexity of security will continue growing and attacks will have greater potential impacts, making security an even more important issue going forward.