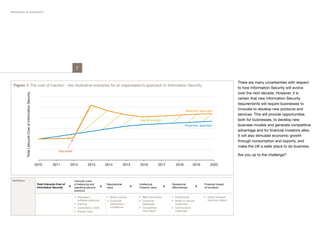
1) Information security is undergoing significant change driven by evolving technology trends and how people use technology. Key trends include the growth of cloud computing, connected devices, data sharing, and new identity and trust models.
2) Over the next decade, information security requirements will be shaped by factors like globalization, regulation, and demographics. Suppliers will need to specialize to meet diverse needs.
3) Organizations require holistic information security approaches considering technology, processes, and people to adapt to threats and remain compliant with changing rules. Proactive strategies can provide competitive advantages over reactive ones.