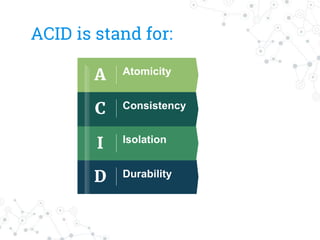
The document discusses the ACID properties that guarantee database transactions are processed reliably. ACID is an acronym that stands for atomicity, consistency, isolation, and durability. Atomicity means all or nothing transactions. Consistency means transactions can only change data in allowed ways and guarantees the committed transaction state. Isolation means transactions appear to be the only action and transactions are independent. Durability means committed data will never be lost once a transaction is successfully completed.