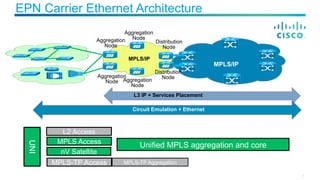
The document provides housekeeping notes for a Cisco Connect Toronto 2015 session. It reminds attendees to silence electronic devices, provides information on how to provide feedback and enter a prize drawing, and advertises the Cisco dCloud platform and Cisco Spark collaboration app. It also includes an agenda for the session on access network evolution, next generation EPN architecture, network services evolution, and SDN evolution.
![Thank you for attending Cisco Connect Toronto 2015, here are a few
housekeeping notes to ensure we all enjoy the session today.
§ Please ensure your cellphones / laptops are set on silent to ensure no
one is disturbed during the session
§ [Speaker Insert any special notes]
House Keeping Notes](https://image.slidesharecdn.com/t-sp-02-ibreton-t-sp-02-i-accessnetworkevolutionfinal-150520165828-lva1-app6892/85/Access-Network-Evolution-3-320.jpg)