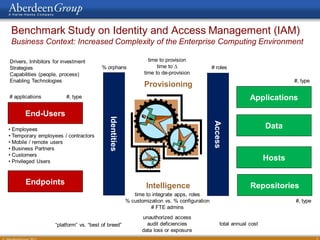
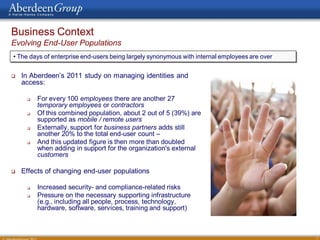
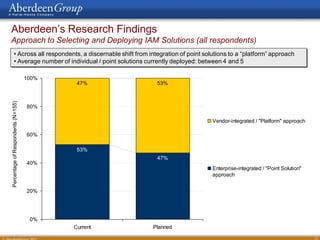
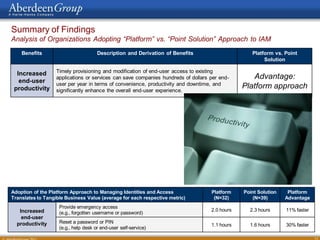
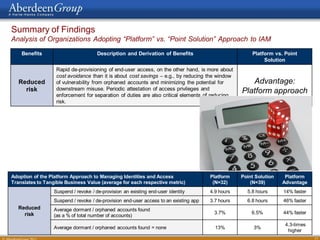
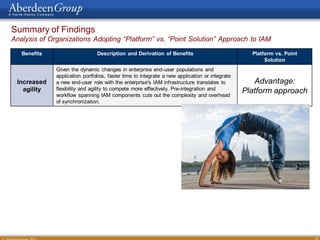
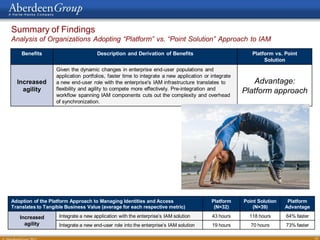
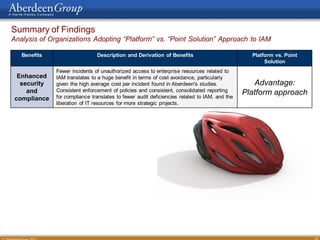
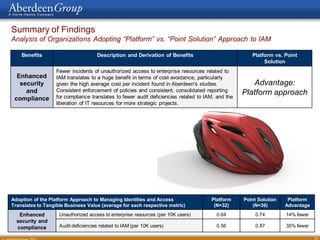
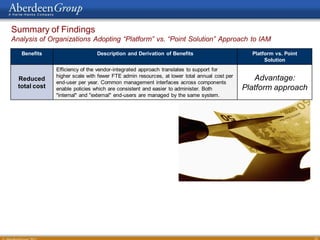
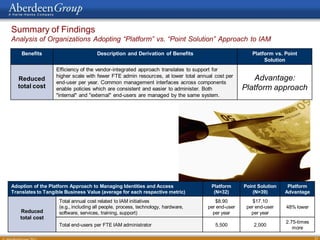
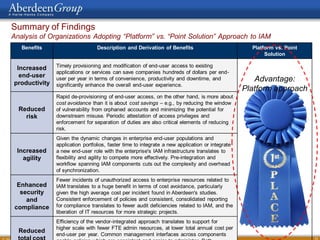
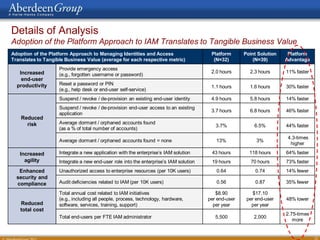
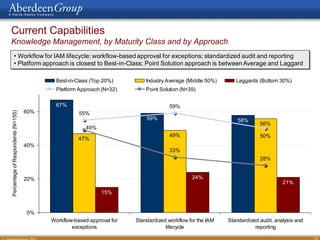
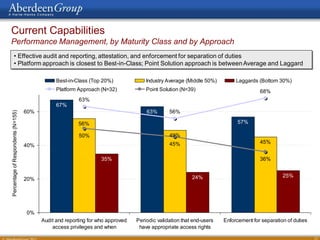
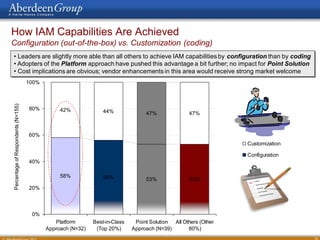
The document summarizes research findings from a study on identity and access management (IAM) solutions. The research found that organizations are shifting from a point solution approach to IAM, where individual products are integrated by the enterprise, to a platform approach where integration is handled by the vendor. The platform approach was found to provide benefits such as faster provisioning, lower risk from orphaned accounts, quicker integration of new applications and users, fewer security incidents, and lower total costs.