6 Steps of Incident Response Plan
•
0 likes•16 views
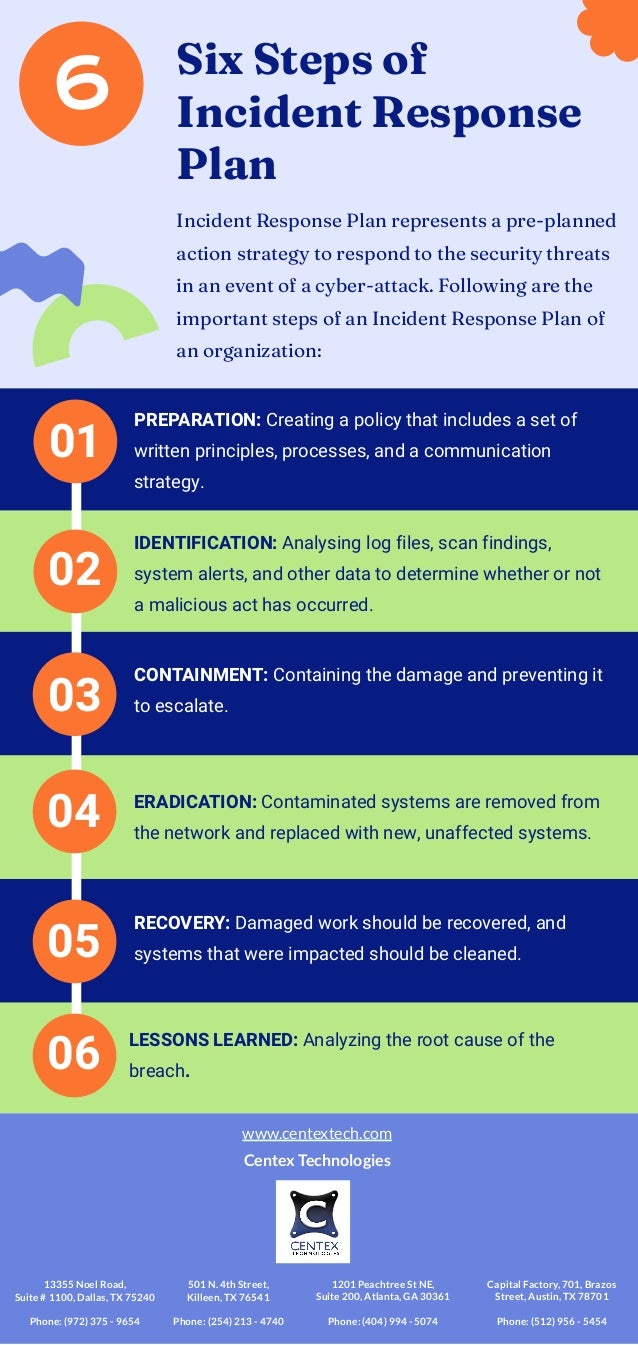
The six steps of an incident response plan are: 1) preparation through creating security policies and communication strategies, 2) identification of malicious acts by analyzing logs and data, 3) containment to limit damage and prevent escalation, 4) eradication by removing contaminated systems and replacing them, 5) recovery of damaged work and cleaning impacted systems, and 6) analyzing lessons learned including the root cause of the breach.
Report
Share
Report
Share
Download to read offline
Recommended
Steps to Consider When Conducting IT Risk Assessment

Predict360 IT Risk Assessment solution can help improve the IT risk assessment process by automating and simplifying IT risk management. This leads to a proactive, compliant, and resilient IT security environment.
Explore more features: https://bit.ly/47gyhRj
10 Ways For Mitigating Cybersecurity Risks In Project Management.docx

Each strategy discussed here will focus on a specific aspect of project management that can be vulnerable to cyber threats. From establishing strong access controls and user authentication mechanisms to ensuring regular data backups and robust incident response plans, these strategies will provide project managers with practical steps to enhance their project’s cybersecurity posture.
Take the first step today by requesting a demo of the Yoroproject, enabling you to proactively protect your business against cyber threats.
Discuss the four steps involved in the maintenance of the indicent res.docx

Discuss the four steps involved in the maintenance of the indicent response(IR) plan. For each step, discuss the main ideas and provide your comments
Solution
An incident response plan (IRP) is a set of written instructions for detecting, responding to and limiting the effects of an information security event.
Incident response plans provide instructions for responding to a number of potential scenarios, including data breaches, denial of service/distributed denial of service attacks, firewall breaches, virus or malware outbreaks or insider threats. Without an incident response plan in place, organizations may either not detect the attack in the first place, or not follow proper protocol to contain the threat and recover from it when a breach is detected.
According to the SANS Institute, there are six key phases of an incident response plan:
1. Preparation: Preparing users and IT staff to handle potential incidents should they should arise
2. Identification: Determining whether an event is indeed a security incident
3. Containment: Limiting the damage of the incident and isolating affected systems to prevent further damage
4. Eradication: Finding the root cause of the incident, removing affected systems from the production environment
5. Recovery: Permitting affected systems back into the production environment, ensuring no threat remains
6. Lessons learned: Completing incident documentation, performing analysis to ultimately learn from incident and potentially improve future response efforts
.
chapter 3 ethics: computer and internet crime

second part of the chpater .very informative and interesting slides..briefly explained
Recommended
Steps to Consider When Conducting IT Risk Assessment

Predict360 IT Risk Assessment solution can help improve the IT risk assessment process by automating and simplifying IT risk management. This leads to a proactive, compliant, and resilient IT security environment.
Explore more features: https://bit.ly/47gyhRj
10 Ways For Mitigating Cybersecurity Risks In Project Management.docx

Each strategy discussed here will focus on a specific aspect of project management that can be vulnerable to cyber threats. From establishing strong access controls and user authentication mechanisms to ensuring regular data backups and robust incident response plans, these strategies will provide project managers with practical steps to enhance their project’s cybersecurity posture.
Take the first step today by requesting a demo of the Yoroproject, enabling you to proactively protect your business against cyber threats.
Discuss the four steps involved in the maintenance of the indicent res.docx

Discuss the four steps involved in the maintenance of the indicent response(IR) plan. For each step, discuss the main ideas and provide your comments
Solution
An incident response plan (IRP) is a set of written instructions for detecting, responding to and limiting the effects of an information security event.
Incident response plans provide instructions for responding to a number of potential scenarios, including data breaches, denial of service/distributed denial of service attacks, firewall breaches, virus or malware outbreaks or insider threats. Without an incident response plan in place, organizations may either not detect the attack in the first place, or not follow proper protocol to contain the threat and recover from it when a breach is detected.
According to the SANS Institute, there are six key phases of an incident response plan:
1. Preparation: Preparing users and IT staff to handle potential incidents should they should arise
2. Identification: Determining whether an event is indeed a security incident
3. Containment: Limiting the damage of the incident and isolating affected systems to prevent further damage
4. Eradication: Finding the root cause of the incident, removing affected systems from the production environment
5. Recovery: Permitting affected systems back into the production environment, ensuring no threat remains
6. Lessons learned: Completing incident documentation, performing analysis to ultimately learn from incident and potentially improve future response efforts
.
chapter 3 ethics: computer and internet crime

second part of the chpater .very informative and interesting slides..briefly explained
New Developments in Cybersecurity and Technology for RDOs: Howland

This presentation was delivered at NADO's 2018 Annual Training Conference, held in Charlotte, NC on October 13-16. For more information, visit: https://www.nado.org/events/2018-annual-training-conference/
Reorganizing Federal IT to Address Today's Threats

New reports show U.S. government servers are faced with 1.8 billion cyber attacks every month. View this technical presentation on ‘Reorganizing Federal IT to Address Today’s Threats’ by Richard Stiennon, analyst with IT Harvest and author of Surviving Cyber War, and Paul Zimski, VP of Solution Strategy with Lumension, as they examine:
*Today’s threats targeting government IT systems
*How federal IT departments can be reorganized to improve security and operations
*What key endpoint security capabilities should be implemented
Get expert insight and recommendations on improving your approach to securing IT systems from today’s sophisticated threats.
Introduction to security

This ppt contains information about definition of computer & information security, types of attacks, services, mechanisms, controls and model for network security
3895SafeAssign Originality ReportComputer Sec.docx

%38
%9
%5
SafeAssign Originality Report
Computer Security: Foundations - 201950 - CRN163 - Zavgren • Week Eight Assignment
%51Total Score: High riskSanthosh Muthyapu
Submission UUID: febbc9ef-e6b9-70f0-6bf0-fe171274dcc9
Total Number of Reports
1
Highest Match
51 %
Santhosh Muthyapu week 8.docx
Average Match
51 %
Submitted on
08/20/19
10:16 AM EDT
Average Word Count
666
Highest: Santhosh Muthyapu week 8.docx
%51Attachment 1
Institutional database (4)
Student paper Student paper Student paper
Student paper
Global database (3)
Student paper Student paper Student paper
Internet (2)
writemyclassessay atlatszo
Top sources (3)
Excluded sources (0)
View Originality Report - Old Design
Word Count: 666
Santhosh Muthyapu week 8.docx
7 5 6
3
8 9 1
4 2
7 Student paper 5 Student paper 8 Student paper
https://blackboard.nec.edu/webapps/mdb-sa-BB5b75a0e7334a9/originalityReport?attemptId=2118e265-8842-4fba-87df-67e2234daca3&course_id=_44439_1&download=true&includeDeleted=true&print=true&force=true
Source Matches (17)
Student paper 77%
atlatszo 63%
Student paper 62%
writemyclassessay 94%
Student paper 68%
Running Head: INDUSTRIAL ESPIONAGE ALLEGED BY DAVID 1
INDUSTRIAL ESPIONAGE ALLEGED BY DAVID DOE 2
INDUSTRIAL ESPIONAGE ALLEGED BY DAVID Name: Santhosh Muthyapu Course: Computer Security: Foundations Date of Submission: 08/20//2019
The steps ought to have been taken in detecting Industrial Espionage Alleged by David Doe
David Doe was a network administrator for the ABC company. The ABC company ought to have taken various steps in detecting Industrial Espionage alleged by
David Doe. First, it should evaluate threat and risk data as well as log data from numerous sources, intending to acquire information about security that would
enhance instant response to security incidents. The manager should be in place to detect any warning signal. An instance is when David is unhappy since he is
passed over for promotion three times. The vital warning signs that a representative may have incorporates bringing home materials having a place with the
organization, being keen on things outside their duties, mainly that are related to the contender of the organization. However, David is alleged to have duplicated the
company’s research after quitting the company and starting his own consulting business (Ho & Hollister, J2015) To predict risks in the network traffic, and dangerous
malware, the company should install signature and behavior-based detection devices. Advanced Cyber Intrusion Detection enhance this. To enable immediate
response as soon as the alerts of faults, attacks, or misuse indications, there should be a correlation, analysis, and collection of server clients’ logs. For the
integrity of local systems, it is essential to ensure regular checks. It was necessary for intrusion finding (Jin & van Dijk, 2018). This involves an outline of possible
security liabilities in software and operating systems applications. Us ...
Running Head SECURITY AWARENESSSecurity Awareness .docx

Running Head: SECURITY AWARENESS
Security Awareness 2
Final Project Security Awareness
Terri Y. Hudson
Southern New Hampshire University – IT 552
December 20, 2016
Agency-wide security awareness Program Proposal
Introduction
For the organization to comply with the current PCT DSS requirement version 12,6, a security awareness program must be in place. The CISCO of the organization has an immediate requirement of creating an agency-wide security awareness program. As a means of implementing security awareness program the organization has conducted a security gap analysis which is one of the component of security awareness program which showed the 10 security findings. As one of the means of conducting the program, I will submit awareness program proposal.
Objective
This SOW (Statement of Work) is being done on behalf of the senior information officer. He has requested for the creation of an agency-wide security awareness program by handing over the security gap analysis which was done prior to this process. Hence the major aim of this document is to set a security awareness program which shows ten major key security findings. The document will also include a risk assessment of the current security awareness practices, processes and practices. By having this document, the organization will be able to have a well-organized maintenance plan. It is also important in maintaining and establishing an information-security awareness program (United States, 2000).
Background
The mission of the organization is to provide efficient IT services with the best security program in place with an aim of protecting organizations assets.
1. Technical infrastructure
The organization is engaged in short-term effort aiming at modernizing its information-processing infrastructure. These efforts have incorporated software enhancements, installation of firewalls and high end network systems for an improved communication. The senior information officer is the one who is responsible top oversee modernization effort. He has of late completed conducting a security awareness program and deployment of the organization’s LAN (Local area Network). The hardware being used is of CISCO products.
2. Computing Environment
The organization’s desktop computers are of Windows 2007/ 98 and 95. The servers are of Pentium with over 1 GB RAM. The current NOS (Network operating system) are window based.
3. Security Posture of the Organization
The organization has a basic network structure with only one router which acts as a firewall. It has several working stations and switches to this working stations. In addition the organization has installed Kasperky’s antivirus in of their desktop machines with a motive of reducing external threats. The data server is highly secured with Kaspersky’s antivirus. The organization physical sec ...
Optimizing Security Operations: 5 Keys to Success

Organizations are suffering from cyber fatigue, with too many alerts, too many technologies, and not enough people. Many security operations center (SOC) teams are underskilled and overworked, making it extremely difficult to streamline operations and decrease the time it takes to detect and remediate security incidents.
Addressing these challenges requires a shift in the tactics and strategies deployed in SOCs. But building an effective SOC is hard; many companies struggle first with implementation and then with figuring out how to take their security operations to the next level.
Read to learn:
--Advantages and disadvantages of different SOC models
--Tips for leveraging advanced analytics tools
--Best practices for incorporating automation and orchestration
--How to boost incident response capabilities, and measure your efforts
--How the NIST Cybersecurity Framework and CIS Controls can help you establish a strong foundation
Start building your roadmap to a next-generation SOC.
NIST CSF review - Essential Protections (a K12 perspective)

NIST CSF tuned for K12 (and adding K12 SIX Essential Protections under Protect)
Software Vulnerabilities Risk Remediation

ClearArmor CSRP - 01.01
SOFTWARE BASED VULNERABILITIES
CyberSecurity is a Business Issue, not a Technology Issue
CyberSecurity is not just about reacting. It includes Risk Management, Audit, Compliance, and training. It also requires continuous attention to Cyber Hygiene. CyberSecurity requires continuous measurement, monitoring, and remediation. Is your organization reactive or proactive? Move to proactive CyberSecurity.
To comply with the intent of the NIST CyberSecurity Framework (CSF), Cyber Hygiene is a requirement. To Comply with NIST 800-53, 800-171, DFARS, NY State DFS Part 500, and a plethora of other frameworks and compliance guidelines requires continuous risk reduction through vulnerability remediation. ClearArmor CyberSecurity Resource Planning (CSRP) enables your organization to meet those requirements.
Phi 235 social media security users guide presentation

PHI 235 SOCIAL MEDIA SECURITY USERS GUIDE PRESENTATION
Ethical hacking

This lecture includes detail about ethical hacking profession, there jobs description, responsibilities duties and skills required to excel in their field.
Vskills Certified Network Security Professional Sample Material

Vskills Certified Network Security Professional Sample Material
More Related Content
Similar to 6 Steps of Incident Response Plan
New Developments in Cybersecurity and Technology for RDOs: Howland

This presentation was delivered at NADO's 2018 Annual Training Conference, held in Charlotte, NC on October 13-16. For more information, visit: https://www.nado.org/events/2018-annual-training-conference/
Reorganizing Federal IT to Address Today's Threats

New reports show U.S. government servers are faced with 1.8 billion cyber attacks every month. View this technical presentation on ‘Reorganizing Federal IT to Address Today’s Threats’ by Richard Stiennon, analyst with IT Harvest and author of Surviving Cyber War, and Paul Zimski, VP of Solution Strategy with Lumension, as they examine:
*Today’s threats targeting government IT systems
*How federal IT departments can be reorganized to improve security and operations
*What key endpoint security capabilities should be implemented
Get expert insight and recommendations on improving your approach to securing IT systems from today’s sophisticated threats.
Introduction to security

This ppt contains information about definition of computer & information security, types of attacks, services, mechanisms, controls and model for network security
3895SafeAssign Originality ReportComputer Sec.docx

%38
%9
%5
SafeAssign Originality Report
Computer Security: Foundations - 201950 - CRN163 - Zavgren • Week Eight Assignment
%51Total Score: High riskSanthosh Muthyapu
Submission UUID: febbc9ef-e6b9-70f0-6bf0-fe171274dcc9
Total Number of Reports
1
Highest Match
51 %
Santhosh Muthyapu week 8.docx
Average Match
51 %
Submitted on
08/20/19
10:16 AM EDT
Average Word Count
666
Highest: Santhosh Muthyapu week 8.docx
%51Attachment 1
Institutional database (4)
Student paper Student paper Student paper
Student paper
Global database (3)
Student paper Student paper Student paper
Internet (2)
writemyclassessay atlatszo
Top sources (3)
Excluded sources (0)
View Originality Report - Old Design
Word Count: 666
Santhosh Muthyapu week 8.docx
7 5 6
3
8 9 1
4 2
7 Student paper 5 Student paper 8 Student paper
https://blackboard.nec.edu/webapps/mdb-sa-BB5b75a0e7334a9/originalityReport?attemptId=2118e265-8842-4fba-87df-67e2234daca3&course_id=_44439_1&download=true&includeDeleted=true&print=true&force=true
Source Matches (17)
Student paper 77%
atlatszo 63%
Student paper 62%
writemyclassessay 94%
Student paper 68%
Running Head: INDUSTRIAL ESPIONAGE ALLEGED BY DAVID 1
INDUSTRIAL ESPIONAGE ALLEGED BY DAVID DOE 2
INDUSTRIAL ESPIONAGE ALLEGED BY DAVID Name: Santhosh Muthyapu Course: Computer Security: Foundations Date of Submission: 08/20//2019
The steps ought to have been taken in detecting Industrial Espionage Alleged by David Doe
David Doe was a network administrator for the ABC company. The ABC company ought to have taken various steps in detecting Industrial Espionage alleged by
David Doe. First, it should evaluate threat and risk data as well as log data from numerous sources, intending to acquire information about security that would
enhance instant response to security incidents. The manager should be in place to detect any warning signal. An instance is when David is unhappy since he is
passed over for promotion three times. The vital warning signs that a representative may have incorporates bringing home materials having a place with the
organization, being keen on things outside their duties, mainly that are related to the contender of the organization. However, David is alleged to have duplicated the
company’s research after quitting the company and starting his own consulting business (Ho & Hollister, J2015) To predict risks in the network traffic, and dangerous
malware, the company should install signature and behavior-based detection devices. Advanced Cyber Intrusion Detection enhance this. To enable immediate
response as soon as the alerts of faults, attacks, or misuse indications, there should be a correlation, analysis, and collection of server clients’ logs. For the
integrity of local systems, it is essential to ensure regular checks. It was necessary for intrusion finding (Jin & van Dijk, 2018). This involves an outline of possible
security liabilities in software and operating systems applications. Us ...
Running Head SECURITY AWARENESSSecurity Awareness .docx

Running Head: SECURITY AWARENESS
Security Awareness 2
Final Project Security Awareness
Terri Y. Hudson
Southern New Hampshire University – IT 552
December 20, 2016
Agency-wide security awareness Program Proposal
Introduction
For the organization to comply with the current PCT DSS requirement version 12,6, a security awareness program must be in place. The CISCO of the organization has an immediate requirement of creating an agency-wide security awareness program. As a means of implementing security awareness program the organization has conducted a security gap analysis which is one of the component of security awareness program which showed the 10 security findings. As one of the means of conducting the program, I will submit awareness program proposal.
Objective
This SOW (Statement of Work) is being done on behalf of the senior information officer. He has requested for the creation of an agency-wide security awareness program by handing over the security gap analysis which was done prior to this process. Hence the major aim of this document is to set a security awareness program which shows ten major key security findings. The document will also include a risk assessment of the current security awareness practices, processes and practices. By having this document, the organization will be able to have a well-organized maintenance plan. It is also important in maintaining and establishing an information-security awareness program (United States, 2000).
Background
The mission of the organization is to provide efficient IT services with the best security program in place with an aim of protecting organizations assets.
1. Technical infrastructure
The organization is engaged in short-term effort aiming at modernizing its information-processing infrastructure. These efforts have incorporated software enhancements, installation of firewalls and high end network systems for an improved communication. The senior information officer is the one who is responsible top oversee modernization effort. He has of late completed conducting a security awareness program and deployment of the organization’s LAN (Local area Network). The hardware being used is of CISCO products.
2. Computing Environment
The organization’s desktop computers are of Windows 2007/ 98 and 95. The servers are of Pentium with over 1 GB RAM. The current NOS (Network operating system) are window based.
3. Security Posture of the Organization
The organization has a basic network structure with only one router which acts as a firewall. It has several working stations and switches to this working stations. In addition the organization has installed Kasperky’s antivirus in of their desktop machines with a motive of reducing external threats. The data server is highly secured with Kaspersky’s antivirus. The organization physical sec ...
Optimizing Security Operations: 5 Keys to Success

Organizations are suffering from cyber fatigue, with too many alerts, too many technologies, and not enough people. Many security operations center (SOC) teams are underskilled and overworked, making it extremely difficult to streamline operations and decrease the time it takes to detect and remediate security incidents.
Addressing these challenges requires a shift in the tactics and strategies deployed in SOCs. But building an effective SOC is hard; many companies struggle first with implementation and then with figuring out how to take their security operations to the next level.
Read to learn:
--Advantages and disadvantages of different SOC models
--Tips for leveraging advanced analytics tools
--Best practices for incorporating automation and orchestration
--How to boost incident response capabilities, and measure your efforts
--How the NIST Cybersecurity Framework and CIS Controls can help you establish a strong foundation
Start building your roadmap to a next-generation SOC.
NIST CSF review - Essential Protections (a K12 perspective)

NIST CSF tuned for K12 (and adding K12 SIX Essential Protections under Protect)
Software Vulnerabilities Risk Remediation

ClearArmor CSRP - 01.01
SOFTWARE BASED VULNERABILITIES
CyberSecurity is a Business Issue, not a Technology Issue
CyberSecurity is not just about reacting. It includes Risk Management, Audit, Compliance, and training. It also requires continuous attention to Cyber Hygiene. CyberSecurity requires continuous measurement, monitoring, and remediation. Is your organization reactive or proactive? Move to proactive CyberSecurity.
To comply with the intent of the NIST CyberSecurity Framework (CSF), Cyber Hygiene is a requirement. To Comply with NIST 800-53, 800-171, DFARS, NY State DFS Part 500, and a plethora of other frameworks and compliance guidelines requires continuous risk reduction through vulnerability remediation. ClearArmor CyberSecurity Resource Planning (CSRP) enables your organization to meet those requirements.
Phi 235 social media security users guide presentation

PHI 235 SOCIAL MEDIA SECURITY USERS GUIDE PRESENTATION
Ethical hacking

This lecture includes detail about ethical hacking profession, there jobs description, responsibilities duties and skills required to excel in their field.
Vskills Certified Network Security Professional Sample Material

Vskills Certified Network Security Professional Sample Material
Similar to 6 Steps of Incident Response Plan (20)
New Developments in Cybersecurity and Technology for RDOs: Howland

New Developments in Cybersecurity and Technology for RDOs: Howland
Reorganizing Federal IT to Address Today's Threats

Reorganizing Federal IT to Address Today's Threats
10 Essentials Of Effective Cyber Security Strategy

10 Essentials Of Effective Cyber Security Strategy
3895SafeAssign Originality ReportComputer Sec.docx

3895SafeAssign Originality ReportComputer Sec.docx
Running Head SECURITY AWARENESSSecurity Awareness .docx

Running Head SECURITY AWARENESSSecurity Awareness .docx
NIST CSF review - Essential Protections (a K12 perspective)

NIST CSF review - Essential Protections (a K12 perspective)
Phi 235 social media security users guide presentation

Phi 235 social media security users guide presentation
Vskills Certified Network Security Professional Sample Material

Vskills Certified Network Security Professional Sample Material
More from Centextech
More from Centextech (20)
Data Modeling Practices for Effective Database Design

Data Modeling Practices for Effective Database Design
Security at the Core: Unraveling Secure by Design Principles

Security at the Core: Unraveling Secure by Design Principles
Cybersecurity Incident Management for Small and Medium-sized Businesses

Cybersecurity Incident Management for Small and Medium-sized Businesses
Mobile Application Security: Safeguarding Apps in the Digital Age

Mobile Application Security: Safeguarding Apps in the Digital Age
Incident Management for Ransomware Attacks Best Practices for Response and Re...

Incident Management for Ransomware Attacks Best Practices for Response and Re...
Recently uploaded
Recruiting in the Digital Age: A Social Media Masterclass

In this masterclass, presented at the Global HR Summit on 5th June 2024, Luan Wise explored the essential features of social media platforms that support talent acquisition, including LinkedIn, Facebook, Instagram, X (formerly Twitter) and TikTok.
The Parable of the Pipeline a book every new businessman or business student ...

The-Parable of the Pipeline a book every new businessman or business student must read before diving into real world of business.
3.0 Project 2_ Developing My Brand Identity Kit.pptx

A personal brand exploration presentation summarizes an individual's unique qualities and goals, covering strengths, values, passions, and target audience. It helps individuals understand what makes them stand out, their desired image, and how they aim to achieve it.
falcon-invoice-discounting-a-premier-platform-for-investors-in-india

Falcon stands out as a top-tier P2P Invoice Discounting platform in India, bridging esteemed blue-chip companies and eager investors. Our goal is to transform the investment landscape in India by establishing a comprehensive destination for borrowers and investors with diverse profiles and needs, all while minimizing risk. What sets Falcon apart is the elimination of intermediaries such as commercial banks and depository institutions, allowing investors to enjoy higher yields.
VAT Registration Outlined In UAE: Benefits and Requirements

Vat Registration is a legal obligation for businesses meeting the threshold requirement, helping companies avoid fines and ramifications. Contact now!
https://viralsocialtrends.com/vat-registration-outlined-in-uae/
Affordable Stationery Printing Services in Jaipur | Navpack n Print

Looking for professional printing services in Jaipur? Navpack n Print offers high-quality and affordable stationery printing for all your business needs. Stand out with custom stationery designs and fast turnaround times. Contact us today for a quote!
Buy Verified PayPal Account | Buy Google 5 Star Reviews

Buy Verified PayPal Account
Looking to buy verified PayPal accounts? Discover 7 expert tips for safely purchasing a verified PayPal account in 2024. Ensure security and reliability for your transactions.
PayPal Services Features-
🟢 Email Access
🟢 Bank Added
🟢 Card Verified
🟢 Full SSN Provided
🟢 Phone Number Access
🟢 Driving License Copy
🟢 Fasted Delivery
Client Satisfaction is Our First priority. Our services is very appropriate to buy. We assume that the first-rate way to purchase our offerings is to order on the website. If you have any worry in our cooperation usually You can order us on Skype or Telegram.
24/7 Hours Reply/Please Contact
usawebmarketEmail: support@usawebmarket.com
Skype: usawebmarket
Telegram: @usawebmarket
WhatsApp: +1(218) 203-5951
USA WEB MARKET is the Best Verified PayPal, Payoneer, Cash App, Skrill, Neteller, Stripe Account and SEO, SMM Service provider.100%Satisfection granted.100% replacement Granted.
Exploring Patterns of Connection with Social Dreaming

Exploring Patterns of Connection -Introduction to Social Dreaming
#Systems Psychodynamics
#Innovation
#Creativity
#Consultancy
#Coaching
Search Disrupted Google’s Leaked Documents Rock the SEO World.pdf

The world of search engine optimization (SEO) is buzzing with discussions after Google confirmed that around 2,500 leaked internal documents related to its Search feature are indeed authentic. The revelation has sparked significant concerns within the SEO community. The leaked documents were initially reported by SEO experts Rand Fishkin and Mike King, igniting widespread analysis and discourse. For More Info:- https://news.arihantwebtech.com/search-disrupted-googles-leaked-documents-rock-the-seo-world/
Business Valuation Principles for Entrepreneurs

This insightful presentation is designed to equip entrepreneurs with the essential knowledge and tools needed to accurately value their businesses. Understanding business valuation is crucial for making informed decisions, whether you're seeking investment, planning to sell, or simply want to gauge your company's worth.
Meas_Dylan_DMBS_PB1_2024-05XX_Revised.pdf

Personal Brand Statement:
As an Army veteran dedicated to lifelong learning, I bring a disciplined, strategic mindset to my pursuits. I am constantly expanding my knowledge to innovate and lead effectively. My journey is driven by a commitment to excellence, and to make a meaningful impact in the world.
一比一原版加拿大渥太华大学毕业证(uottawa毕业证书)如何办理

一模一样【q/微:1954292140】【加拿大渥太华大学毕业证(uottawa毕业证书)成绩单Offer】【q/微:1954292140】(留信学历认证永久存档查询)采用学校原版纸张、特殊工艺完全按照原版一比一制作(包括:隐形水印,阴影底纹,钢印LOGO烫金烫银,LOGO烫金烫银复合重叠,文字图案浮雕,激光镭射,紫外荧光,温感,复印防伪)行业标杆!精益求精,诚心合作,真诚制作!多年品质 ,按需精细制作,24小时接单,全套进口原装设备,十五年致力于帮助留学生解决难题,业务范围有加拿大、英国、澳洲、韩国、美国、新加坡,新西兰等学历材料,包您满意。
【业务选择办理准则】
一、工作未确定,回国需先给父母、亲戚朋友看下文凭的情况,办理一份就读学校的毕业证【q/微:1954292140】文凭即可
二、回国进私企、外企、自己做生意的情况,这些单位是不查询毕业证真伪的,而且国内没有渠道去查询国外文凭的真假,也不需要提供真实教育部认证。鉴于此,办理一份毕业证【q/微:1954292140】即可
三、进国企,银行,事业单位,考公务员等等,这些单位是必需要提供真实教育部认证的,办理教育部认证所需资料众多且烦琐,所有材料您都必须提供原件,我们凭借丰富的经验,快捷的绿色通道帮您快速整合材料,让您少走弯路。
留信网认证的作用:
1:该专业认证可证明留学生真实身份
2:同时对留学生所学专业登记给予评定
3:国家专业人才认证中心颁发入库证书
4:这个认证书并且可以归档倒地方
5:凡事获得留信网入网的信息将会逐步更新到个人身份内,将在公安局网内查询个人身份证信息后,同步读取人才网入库信息
6:个人职称评审加20分
7:个人信誉贷款加10分
8:在国家人才网主办的国家网络招聘大会中纳入资料,供国家高端企业选择人才
→ 【关于价格问题(保证一手价格)
我们所定的价格是非常合理的,而且我们现在做得单子大多数都是代理和回头客户介绍的所以一般现在有新的单子 我给客户的都是第一手的代理价格,因为我想坦诚对待大家 不想跟大家在价格方面浪费时间
对于老客户或者被老客户介绍过来的朋友,我们都会适当给一些优惠。
选择实体注册公司办理,更放心,更安全!我们的承诺:可来公司面谈,可签订合同,会陪同客户一起到教育部认证窗口递交认证材料,客户在教育部官方认证查询网站查询到认证通过结果后付款,不成功不收费!
5 Things You Need To Know Before Hiring a Videographer

Dive into this presentation to discover the 5 things you need to know before hiring a videographer in Toronto.
Enterprise Excellence is Inclusive Excellence.pdf

Enterprise excellence and inclusive excellence are closely linked, and real-world challenges have shown that both are essential to the success of any organization. To achieve enterprise excellence, organizations must focus on improving their operations and processes while creating an inclusive environment that engages everyone. In this interactive session, the facilitator will highlight commonly established business practices and how they limit our ability to engage everyone every day. More importantly, though, participants will likely gain increased awareness of what we can do differently to maximize enterprise excellence through deliberate inclusion.
What is Enterprise Excellence?
Enterprise Excellence is a holistic approach that's aimed at achieving world-class performance across all aspects of the organization.
What might I learn?
A way to engage all in creating Inclusive Excellence. Lessons from the US military and their parallels to the story of Harry Potter. How belt systems and CI teams can destroy inclusive practices. How leadership language invites people to the party. There are three things leaders can do to engage everyone every day: maximizing psychological safety to create environments where folks learn, contribute, and challenge the status quo.
Who might benefit? Anyone and everyone leading folks from the shop floor to top floor.
Dr. William Harvey is a seasoned Operations Leader with extensive experience in chemical processing, manufacturing, and operations management. At Michelman, he currently oversees multiple sites, leading teams in strategic planning and coaching/practicing continuous improvement. William is set to start his eighth year of teaching at the University of Cincinnati where he teaches marketing, finance, and management. William holds various certifications in change management, quality, leadership, operational excellence, team building, and DiSC, among others.
LA HUG - Video Testimonials with Chynna Morgan - June 2024

Have you ever heard that user-generated content or video testimonials can take your brand to the next level? We will explore how you can effectively use video testimonials to leverage and boost your sales, content strategy, and increase your CRM data.🤯
We will dig deeper into:
1. How to capture video testimonials that convert from your audience 🎥
2. How to leverage your testimonials to boost your sales 💲
3. How you can capture more CRM data to understand your audience better through video testimonials. 📊
Recently uploaded (20)
Recruiting in the Digital Age: A Social Media Masterclass

Recruiting in the Digital Age: A Social Media Masterclass
The Parable of the Pipeline a book every new businessman or business student ...

The Parable of the Pipeline a book every new businessman or business student ...
3.0 Project 2_ Developing My Brand Identity Kit.pptx

3.0 Project 2_ Developing My Brand Identity Kit.pptx
falcon-invoice-discounting-a-premier-platform-for-investors-in-india

falcon-invoice-discounting-a-premier-platform-for-investors-in-india
VAT Registration Outlined In UAE: Benefits and Requirements

VAT Registration Outlined In UAE: Benefits and Requirements
Affordable Stationery Printing Services in Jaipur | Navpack n Print

Affordable Stationery Printing Services in Jaipur | Navpack n Print
The Influence of Marketing Strategy and Market Competition on Business Perfor...

The Influence of Marketing Strategy and Market Competition on Business Perfor...
Buy Verified PayPal Account | Buy Google 5 Star Reviews

Buy Verified PayPal Account | Buy Google 5 Star Reviews
Exploring Patterns of Connection with Social Dreaming

Exploring Patterns of Connection with Social Dreaming
Search Disrupted Google’s Leaked Documents Rock the SEO World.pdf

Search Disrupted Google’s Leaked Documents Rock the SEO World.pdf
5 Things You Need To Know Before Hiring a Videographer

5 Things You Need To Know Before Hiring a Videographer
LA HUG - Video Testimonials with Chynna Morgan - June 2024

LA HUG - Video Testimonials with Chynna Morgan - June 2024
6 Steps of Incident Response Plan
- 1. Six Steps of Incident Response Plan Incident Response Plan represents a pre-planned action strategy to respond to the security threats in an event of a cyber-attack. Following are the important steps of an Incident Response Plan of an organization: 6 PREPARATION: Creating a policy that includes a set of written principles, processes, and a communication strategy. IDENTIFICATION: Analysing log files, scan findings, system alerts, and other data to determine whether or not a malicious act has occurred. CONTAINMENT: Containing the damage and preventing it to escalate. ERADICATION: Contaminated systems are removed from the network and replaced with new, unaffected systems. RECOVERY: Damaged work should be recovered, and systems that were impacted should be cleaned. LESSONS LEARNED: Analyzing the root cause of the breach. 01 02 03 04 05 06 www.centextech.com Centex Technologies 13355 Noel Road, Suite # 1100, Dallas, TX 75240 Phone: (972) 375 - 9654 501 N. 4th Street, Killeen, TX 76541 Phone: (254) 213 - 4740 1201 Peachtree St NE, Suite 200, Atlanta, GA 30361 Phone: (404) 994 - 5074 Capital Factory, 701, Brazos Street, Austin, TX 78701 Phone: (512) 956 - 5454