What is Context Aware Security?
•
0 likes•15 views
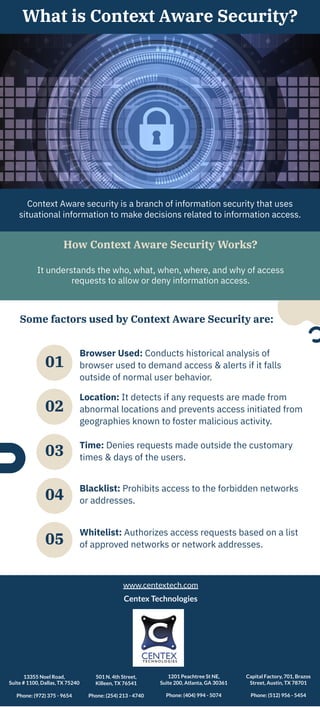
Context aware security is a branch of information security that uses situational information like location, time, browser used, and blacklist/whitelist of networks to determine whether to allow or deny access to information. It analyzes factors around an access request to understand the who, what, when, where, and why to make more informed access decisions. Context aware security conducts historical analysis of browsers used and denies requests if they are outside normal user behavior or come from abnormal locations or times.
Report
Share
Report
Share
Download to read offline
Recommended
Recommended
More Related Content
Similar to What is Context Aware Security?
Similar to What is Context Aware Security? (20)
Ethical Hacking Interview Questions and Answers.pdf

Ethical Hacking Interview Questions and Answers.pdf
Top 20 Cyber Security Interview Questions and Answers in 2023.pptx

Top 20 Cyber Security Interview Questions and Answers in 2023.pptx
Addressing Insider Threat using "Where You Are" as Fourth Factor Authentication

Addressing Insider Threat using "Where You Are" as Fourth Factor Authentication
CIA = Confidentiality of information, Integrity of information, Avai.pdf

CIA = Confidentiality of information, Integrity of information, Avai.pdf
More from Centextech
More from Centextech (20)
Data Modeling Practices for Effective Database Design

Data Modeling Practices for Effective Database Design
Security at the Core: Unraveling Secure by Design Principles

Security at the Core: Unraveling Secure by Design Principles
Cybersecurity Incident Management for Small and Medium-sized Businesses

Cybersecurity Incident Management for Small and Medium-sized Businesses
Incident Management for Ransomware Attacks Best Practices for Response and Re...

Incident Management for Ransomware Attacks Best Practices for Response and Re...
10 Essentials Of Effective Cyber Security Strategy

10 Essentials Of Effective Cyber Security Strategy
Recently uploaded
Recently uploaded (20)
Taurus Zodiac Sign_ Personality Traits and Sign Dates.pptx

Taurus Zodiac Sign_ Personality Traits and Sign Dates.pptx
RMD24 | Debunking the non-endemic revenue myth Marvin Vacquier Droop | First ...

RMD24 | Debunking the non-endemic revenue myth Marvin Vacquier Droop | First ...
What are the main advantages of using HR recruiter services.pdf

What are the main advantages of using HR recruiter services.pdf
Unlock Your TikTok Potential: Free TikTok Likes with InstBlast

Unlock Your TikTok Potential: Free TikTok Likes with InstBlast
Global Interconnection Group Joint Venture[960] (1).pdf![Global Interconnection Group Joint Venture[960] (1).pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Global Interconnection Group Joint Venture[960] (1).pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Global Interconnection Group Joint Venture[960] (1).pdf
NewBase 24 May 2024 Energy News issue - 1727 by Khaled Al Awadi_compresse...

NewBase 24 May 2024 Energy News issue - 1727 by Khaled Al Awadi_compresse...
India’s Recommended Women Surgeons to Watch in 2024.pdf

India’s Recommended Women Surgeons to Watch in 2024.pdf
Pitch Deck Teardown: RAW Dating App's $3M Angel deck

Pitch Deck Teardown: RAW Dating App's $3M Angel deck
12 Conversion Rate Optimization Strategies for Ecommerce Websites.pdf

12 Conversion Rate Optimization Strategies for Ecommerce Websites.pdf
8 Questions B2B Commercial Teams Can Ask To Help Product Discovery

8 Questions B2B Commercial Teams Can Ask To Help Product Discovery
Luxury Artificial Plants Dubai | Plants in KSA, UAE | Shajara

Luxury Artificial Plants Dubai | Plants in KSA, UAE | Shajara
RMD24 | Retail media: hoe zet je dit in als je geen AH of Unilever bent? Heid...

RMD24 | Retail media: hoe zet je dit in als je geen AH of Unilever bent? Heid...
Understanding UAE Labour Law: Key Points for Employers and Employees

Understanding UAE Labour Law: Key Points for Employers and Employees
What is Context Aware Security?
- 1. What is Context Aware Security? Context Aware security is a branch of information security that uses situational information to make decisions related to information access. How Context Aware Security Works? It understands the who, what, when, where, and why of access requests to allow or deny information access. Some factors used by Context Aware Security are: Browser Used: Conducts historical analysis of browser used to demand access & alerts if it falls outside of normal user behavior. Location: It detects if any requests are made from abnormal locations and prevents access initiated from geographies known to foster malicious activity. Time: Denies requests made outside the customary times & days of the users. Blacklist: Prohibits access to the forbidden networks or addresses. Whitelist: Authorizes access requests based on a list of approved networks or network addresses. 05 01 02 03 04 www.centextech.com Centex Technologies 13355 Noel Road, Suite # 1100, Dallas, TX 75240 Phone: (972) 375 - 9654 501 N. 4th Street, Killeen, TX 76541 Phone: (254) 213 - 4740 1201 Peachtree St NE, Suite 200, Atlanta, GA 30361 Phone: (404) 994 - 5074 Capital Factory, 701, Brazos Street, Austin, TX 78701 Phone: (512) 956 - 5454