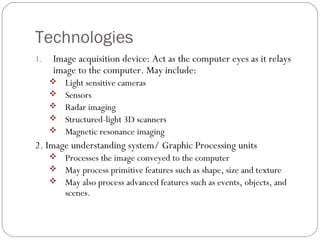
Computer Vision Based Interfaces (CVBI) is an emerging technology that enables computers to acquire and process images and gestures for human-computer interaction. It involves image acquisition devices and graphic processing units to interpret visual information, with applications in consumer electronics, security, and industrial automation. Key benefits include enabling distance communication and assisting users with physical disabilities, while challenges include interpretation accuracy and costs.