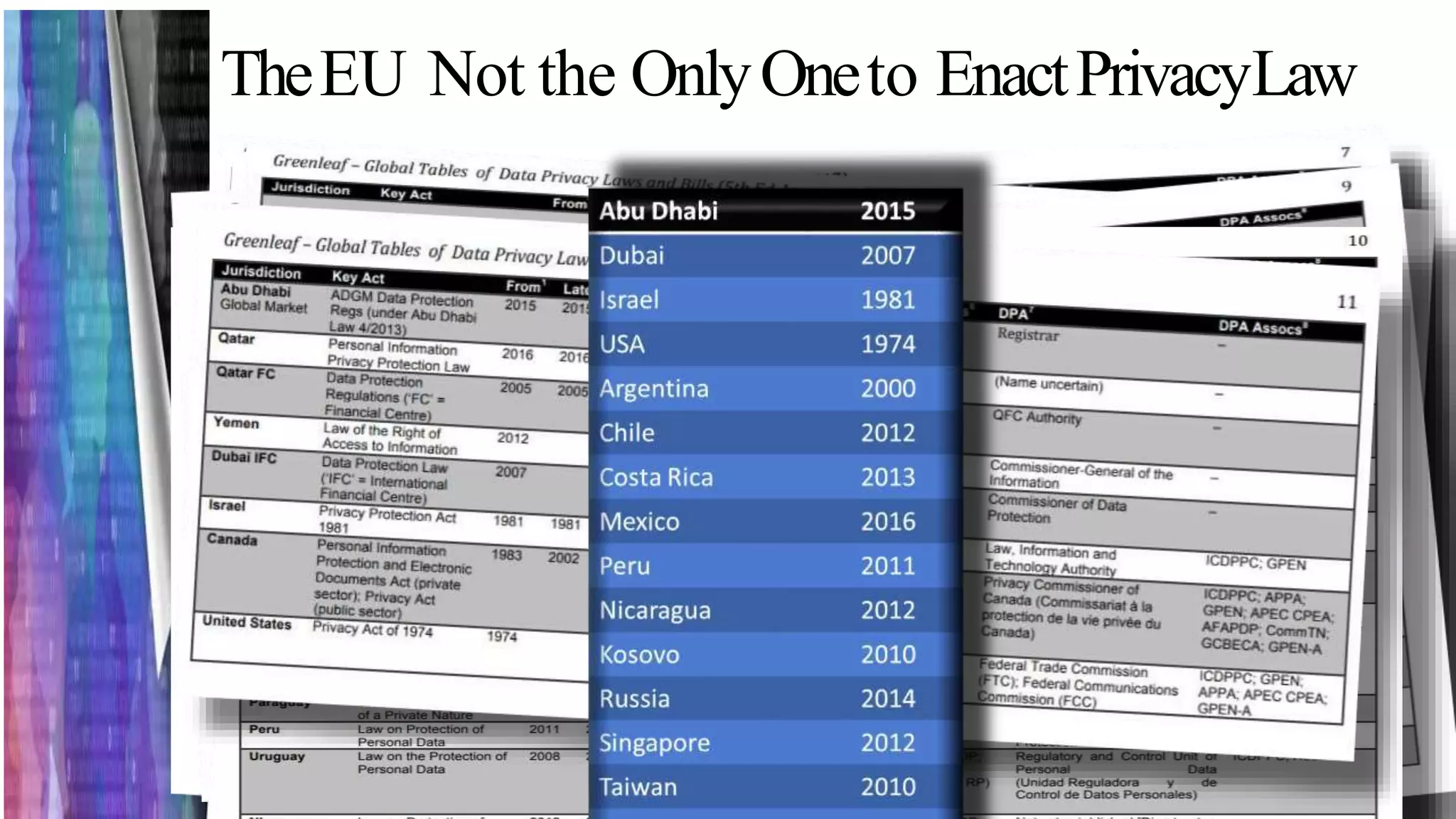
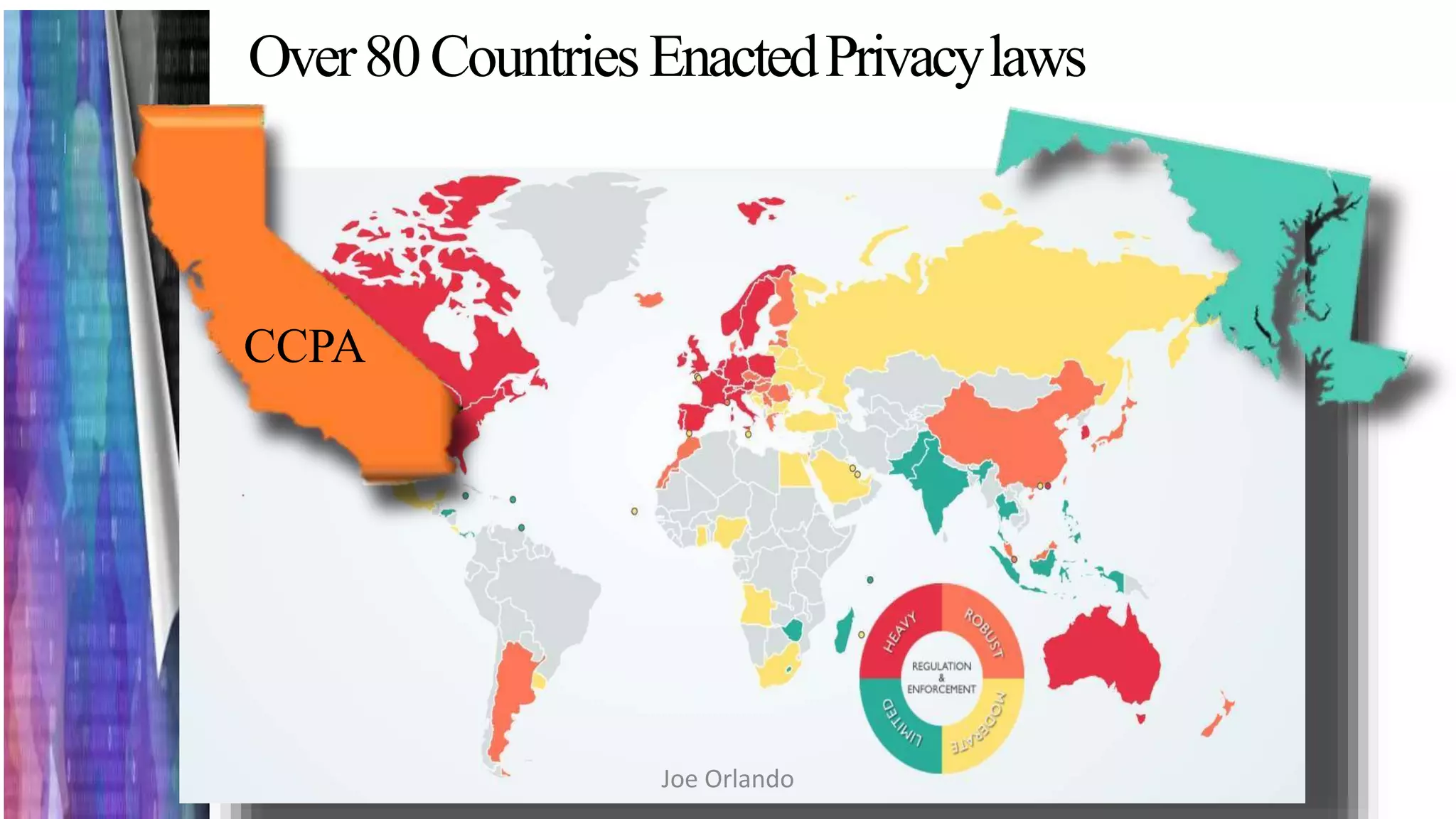
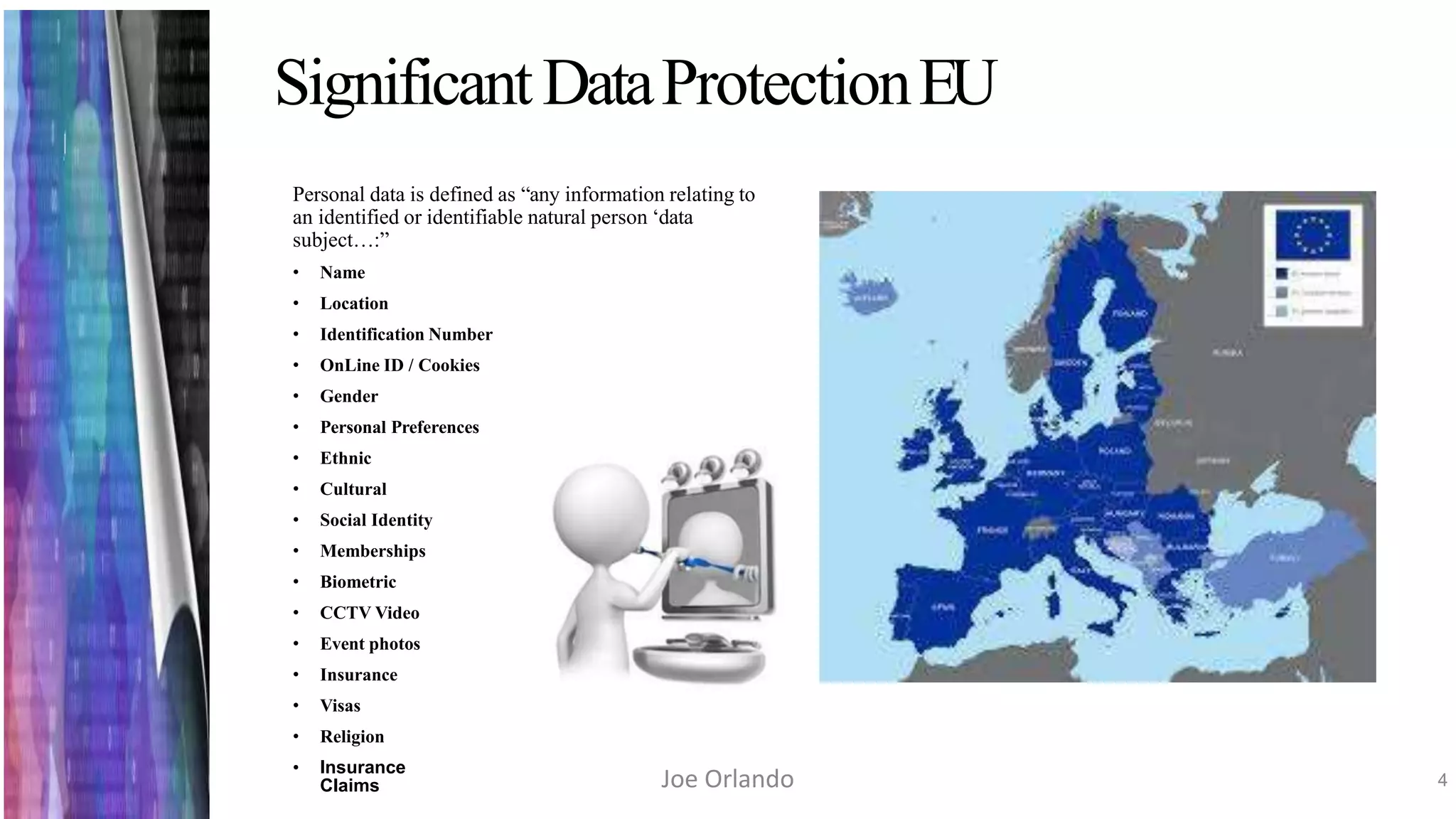
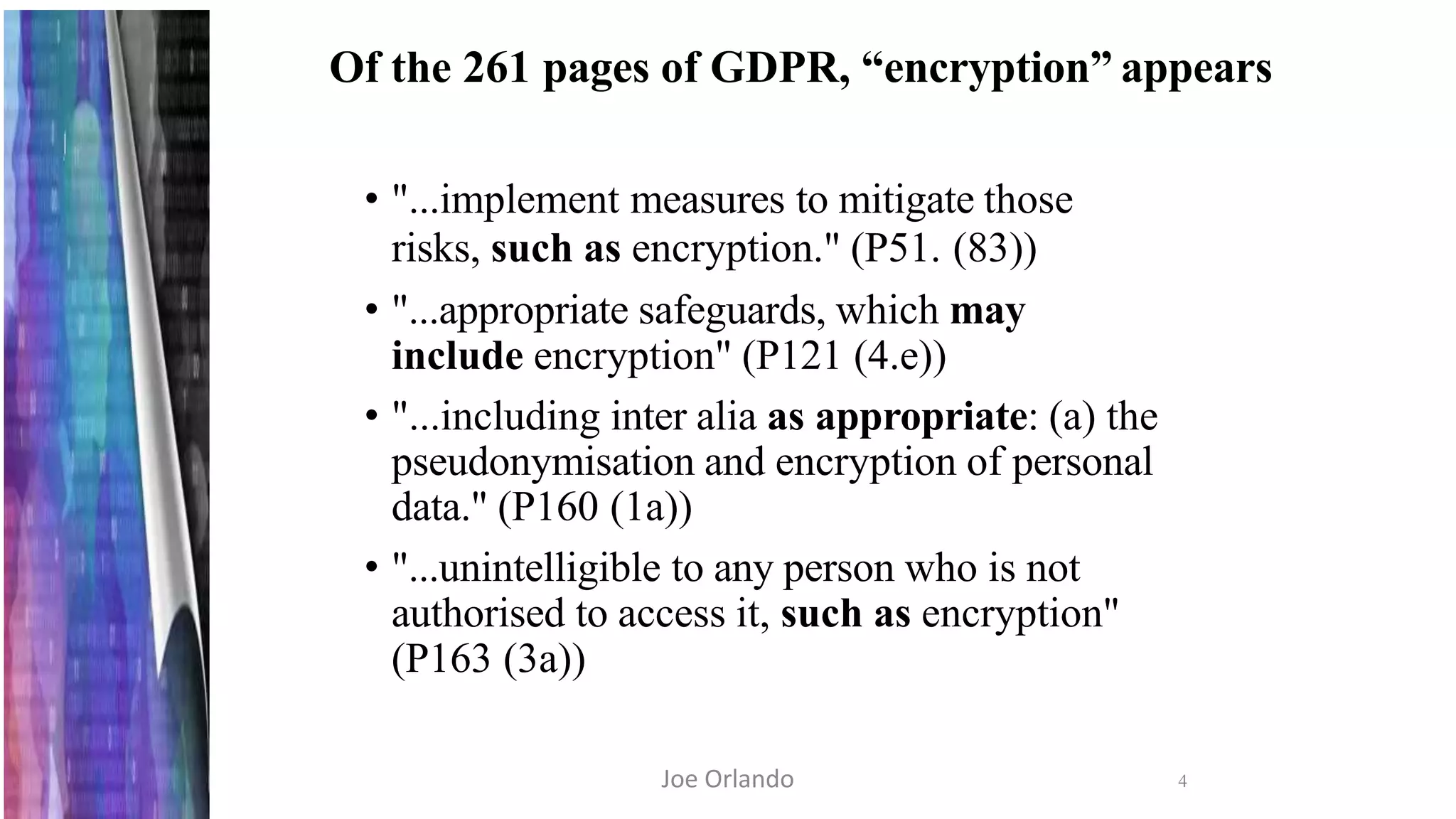
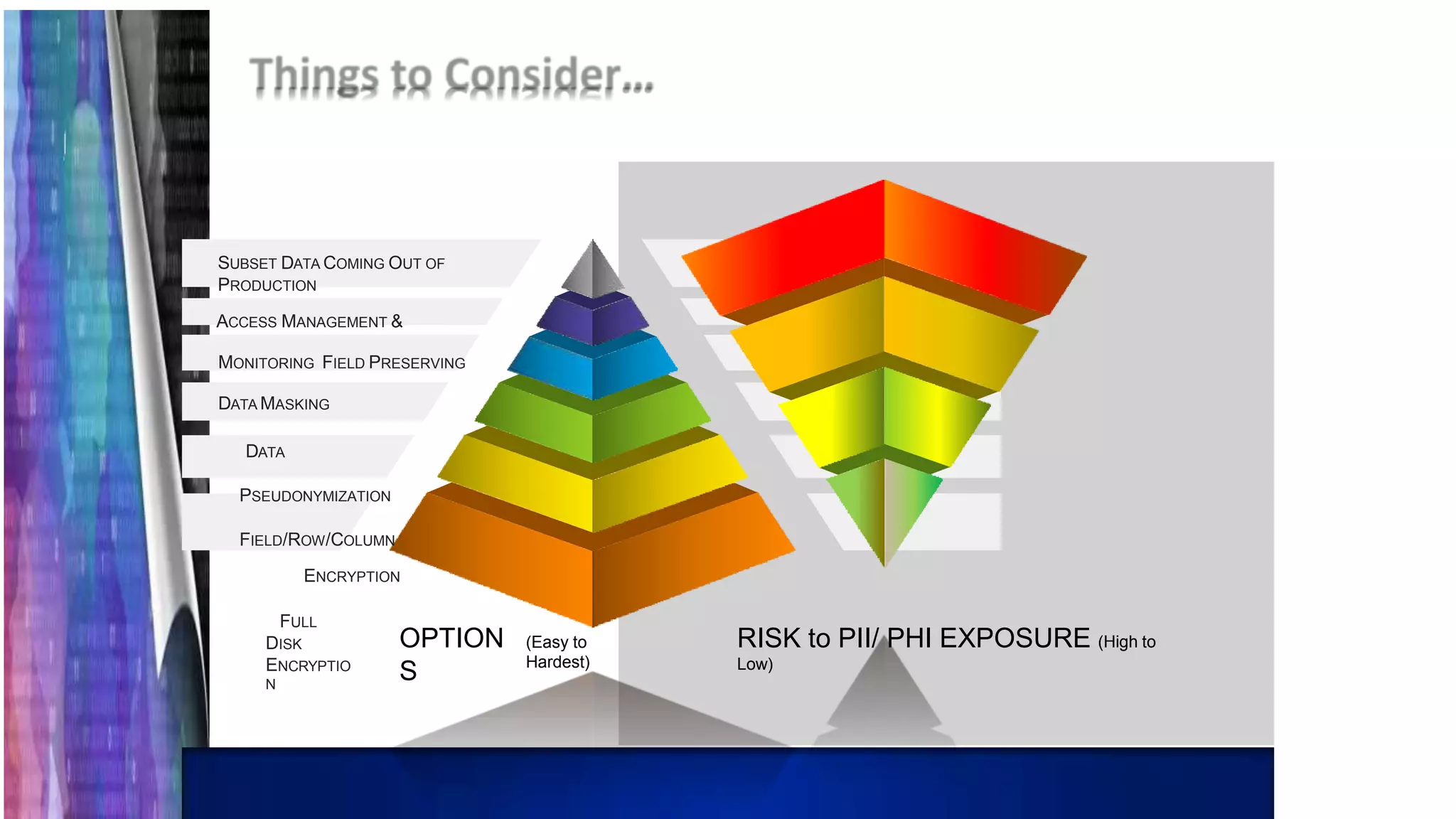
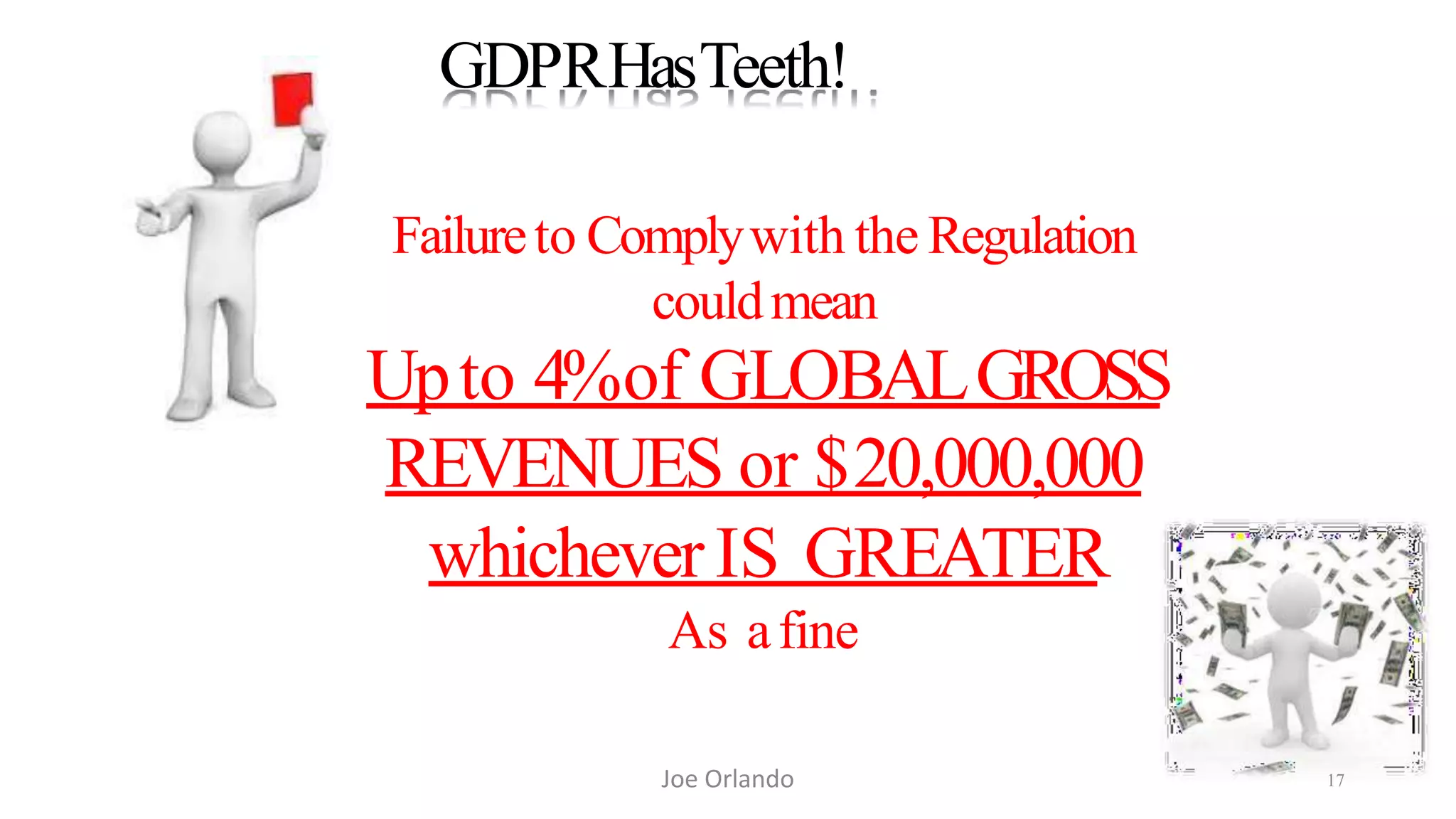
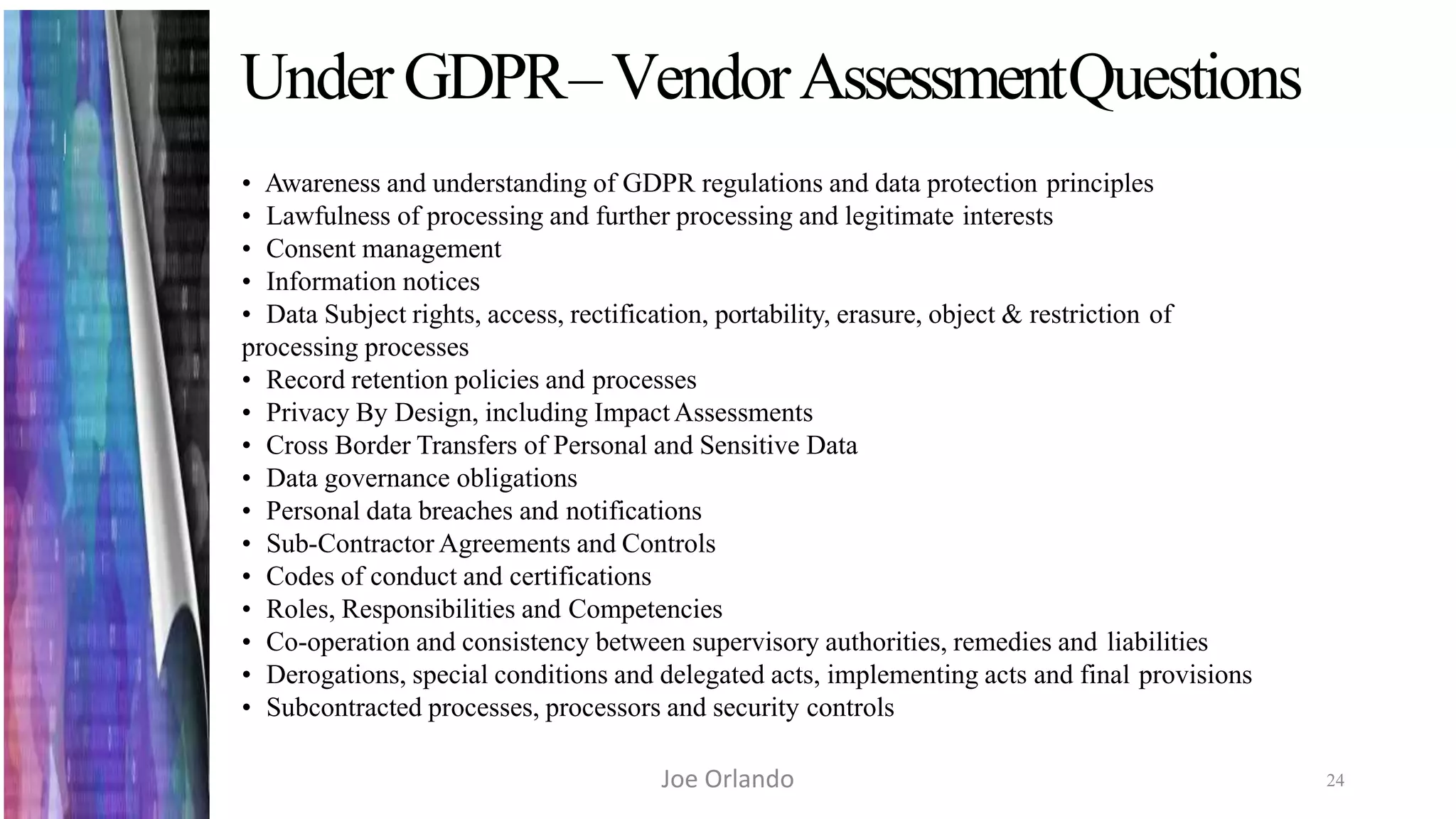
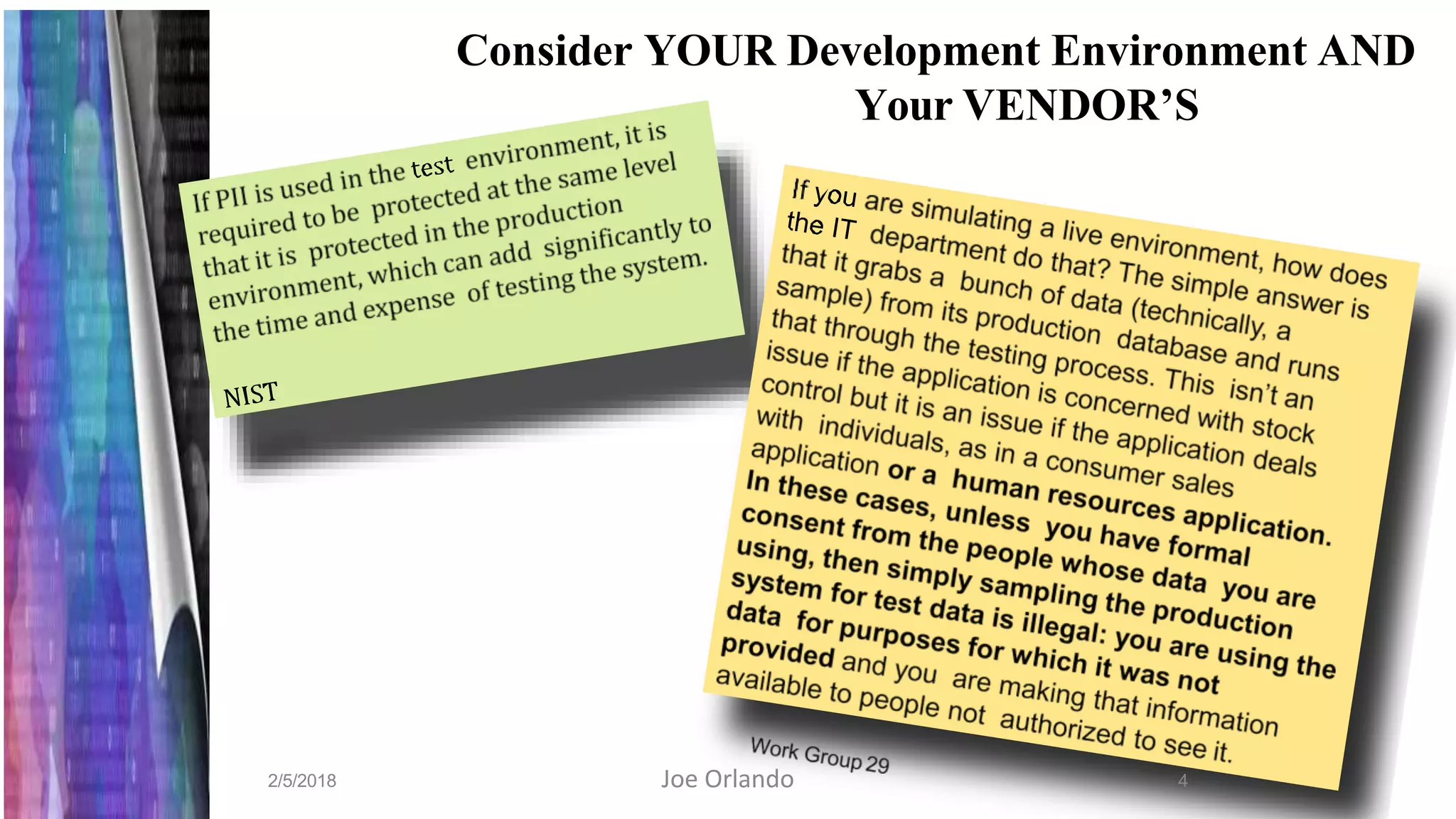
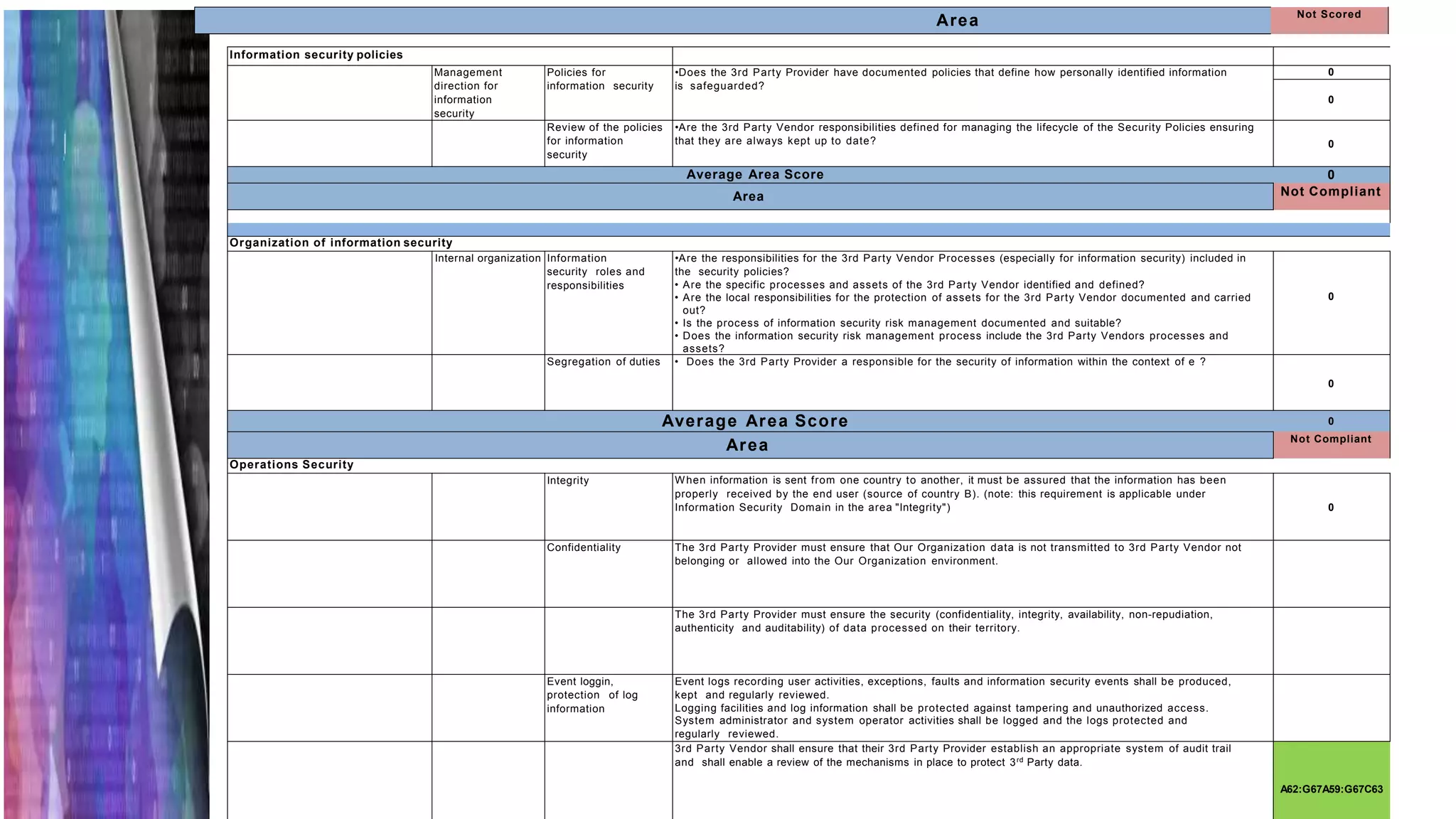
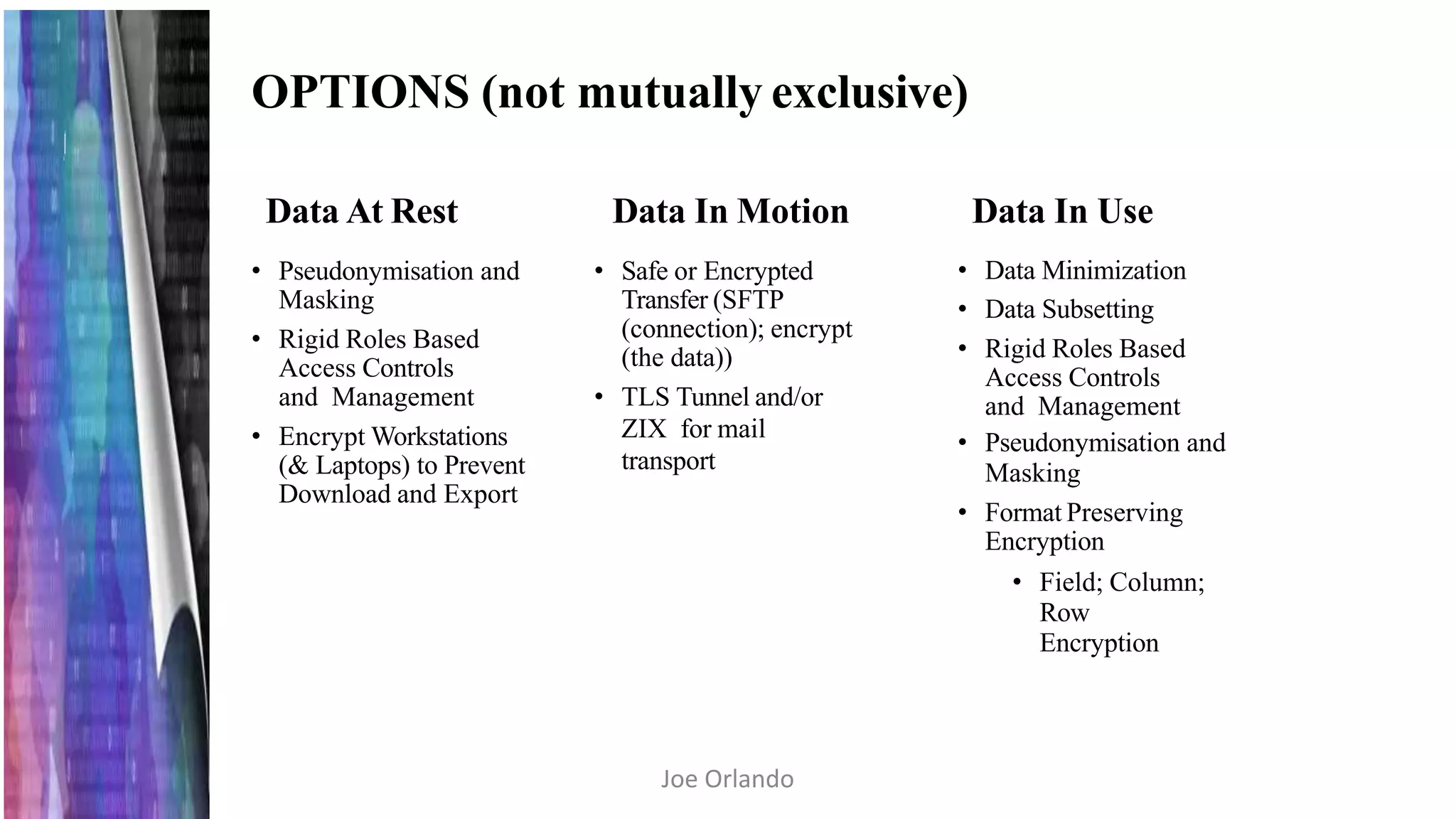
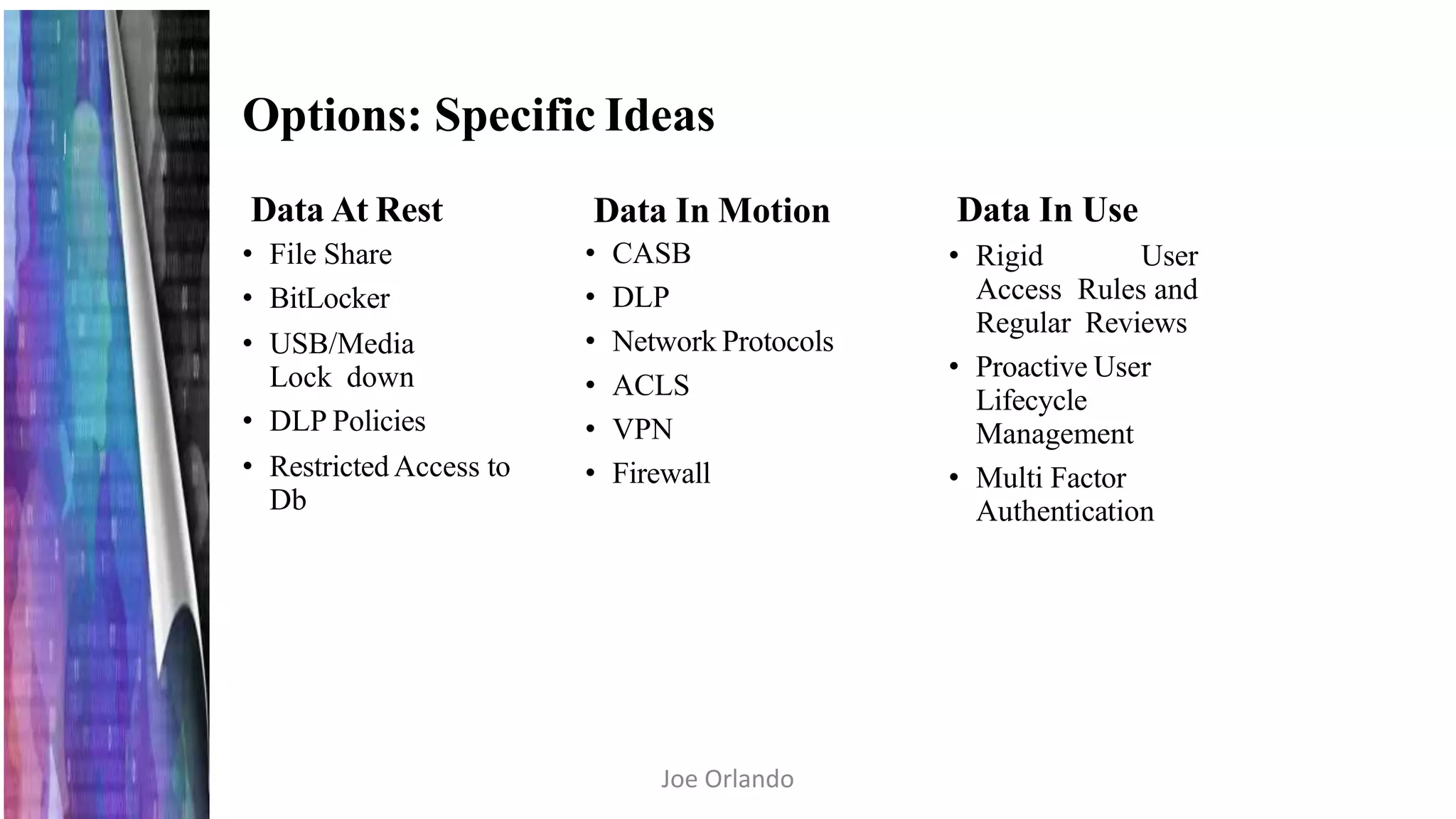
The document outlines the General Data Protection Regulation (GDPR) and its implications for businesses, particularly regarding data protection and compliance responsibilities when working with third-party partners. It details the types of personal data covered, individual rights under the GDPR, and the requirements for implementing security measures such as encryption to safeguard this data. The document emphasizes that data controllers remain responsible for data security regardless of the involvement of third-party processors.