2020 midterm prof.docxIT 240 Midterm Proficiency Exam .docx
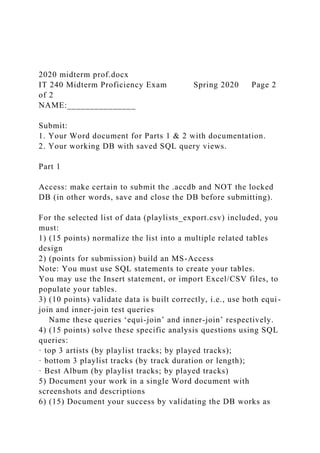
- 1. 2020 midterm prof.docx IT 240 Midterm Proficiency Exam Spring 2020 Page 2 of 2 NAME:_______________ Submit: 1. Your Word document for Parts 1 & 2 with documentation. 2. Your working DB with saved SQL query views. Part 1 Access: make certain to submit the .accdb and NOT the locked DB (in other words, save and close the DB before submitting). For the selected list of data (playlists_export.csv) included, you must: 1) (15 points) normalize the list into a multiple related tables design 2) (points for submission) build an MS-Access Note: You must use SQL statements to create your tables. You may use the Insert statement, or import Excel/CSV files, to populate your tables. 3) (10 points) validate data is built correctly, i.e., use both equi- join and inner-join test queries Name these queries ‘equi-join’ and inner-join’ respectively. 4) (15 points) solve these specific analysis questions using SQL queries: · top 3 artists (by playlist tracks; by played tracks); · bottom 3 playlist tracks (by track duration or length); · Best Album (by playlist tracks; by played tracks) 5) Document your work in a single Word document with screenshots and descriptions 6) (15) Document your success by validating the DB works as
- 2. intended, i.e. run (3) additional queries. Provide an explanation of the query (what you were attempting to accomplish), the code, and the results. Make certain you SAVE the query in the DB. 7) Do not encrypt or lock the database with username/password. 8) (25 points) Submit working database (including the saved sql queries) AND the Word document Part 2 Queen Anne DB (use the DB provided) T. (5 points) Given your assumptions about cascading deletions in your answer to part B of the Queen Anne case study, write the fewest number of DELETE statements possible to remove all the data in your database, but leave the table structures intact. Do not run these statements if you are using an actual database! If you decide to run the code, make a copy of the DB and use it to test your SQL statements. U. (15 points) Chapter 2 discussed multivalued dependencies and the associated multivalue, multicolumn problem and how to resolve it (pages 96-98). Does the VENDOR table have the multivalue, multicolumn problem? If so, use the discussion on pages 114-118 as the basis for solving it for the QACS database. Create a new table named PHONE_NUMBER, link it to the VENDOR table, populate the PHONE_NUMBER table, and finally alter the VENDOR table to remove any unneeded columns. Hint: Read the additional discussion of the SQL ALTER TABLE statement in online Extension B, “Advanced SQL”. Use the ALTER statement.
- 3. Do not run these SQL statements if you are using an actual database! If you decide to run the code, make a copy of the DB and use it. Write your SQL code here: playlists_export.csv.xlsx playlists_export (1) MidTermtitleartistalbumtrackdurationididtypeplaycountratingye argenrenotesplaylistThey Call the Wind MariaSam CookeSwing Low3177000Taghhvg3vcgqvpi75kyweitw3v473null1961Classic SoulLibraryGrandfather's ClockSam CookeSwing Low7192000T7gx26h2ex7ord3fffatkkqvpji72null1961Classic SoulLibraryGoin' HomeSam CookeSwing Low12188000Tjvz5mtuamkd5vxdiwpd77bge2m70null1961Class ic SoulLibraryIf I Had You (I'd Be Happy)Sam CookeSwing Low5138000Ts7yeb5d7jn5kbtcssumpiukfme72null1961Classic SoulLibraryI'm Just a Country BoySam CookeSwing Low2248000Tm5wfclmto6pbqe2vrh3ahorwki74null1961Classic SoulLibraryJeanie with the Light Brown HairSam CookeSwing Low8226000Tauaedgdd5v2f2xo2qryrxoy73i72null1961Classic SoulLibraryChain Gang (Remastered)Sam CookeSwing Low6155000T6z5yef6xgdsaw56dud23tifyuq72null1961Classic SoulLibraryPraySam CookeSwing Low10132000Tfutisrpxdi4pmhkzrabs7fjoke71null1961Classic SoulLibraryLong, Long AgoSam CookeSwing Low9179000Takrxk5fzwploxzc7mspqjhzkxi71null1961Classic SoulLibraryYou Belong o MeSam CookeSwing Low11165000Ta2vq2ztzixaxfv7vlzn742at2a71null1961Classic SoulLibraryTwilight on the TrailSam CookeSwing Low4192000Tkxfto5kfo63x37euhn6ckjjrya72null1961Classic SoulLibrarySwing Low, Sweet ChariotSam CookeSwing Low1187000Tlvhmqjazejf3lecf2j4lt25ksa75null1961Classic SoulLibraryGreat White SharkPeter GarrettA Version of
- 4. Now6229000Tkdhduoikplfeja6vnbnpnl5a2a73null2016RockLibr aryDie A Happy ManThomas RhettTangled Up4227000Ttjtbrpoftpgveiqkac2zeku54y70null2016CountryLibr aryRitual / Nous Sommes Du SoleilYesTales From Topographic Oceans21292000Triq4tvewfs32ql5z6kvr26zse470null1973Progr essive/Art RockLibraryBlackDierks BentleyBlack1211000Tjm2yc3aldyhod2v5fn6azfo7uq73null201 6nullLibraryThe Only Way Is Up80s Chartstarz1980's Best Tunes32232000Tvrllfue4frddppot7mruvumhky70null2015PopLi braryI Want Candy80s Chartstarz1980's Best Tunes27159000Tyqu7kcuzxsja7wodxqiqyqiv5m70null2015PopL ibraryHazy Shade of Winter80s Chartstarz1980's Best Tunes29161000Tfy4vwzkxgmdljlvjj7d4no6tn470null2015PopLi braryRock Me Amadeus80s Chartstarz1980's Best Tunes6191000Trmmrfgtdudsq62kjt2mqiukziy70null2015PopLib raryBette Davis Eyes80s Chartstarz1980's Best Tunes19226000Tayp4cjap3goxsw4dsvs37vlidu70null2015PopLi braryShe Works Hard for the Money80s Chartstarz1980's Best Tunes11250000Tpilit7d6saq3hapvvhopfi7ieu70null2015PopLibr aryListen to Your Heart80s Chartstarz1980's Best Tunes23339000Txgbzrk2kgmuarnemb2g7u6zdeq70null2015Pop LibraryI Just Called to Say I Love You80s Chartstarz1980's Best Tunes14263000Tgq2qmy2woq7nofjnrrmmjup2qq70null2015Pop LibraryI Still Haven't Found What I'm Looking For80s Chartstarz1980's Best Tunes26272000Tkoxzjl6xrfau5bcvozzbfpt65m70null2015PopLi braryAy Ay Ay Ay Moosey80s Chartstarz1980's Best Tunes4171000Tsuw5c2ncvprcr6tplyx7yzzegy70null2015PopLib raryJump80s Chartstarz1980's Best Tunes7240000Tlxrmfx3uwbwqm6y3j3b7zdqcua70null2015PopL ibraryFight the Power80s Chartstarz1980's Best Tunes3257000Tr3w3ge6c56ag77cqkjkbbp5rvi70null2015PopLib raryStraight Up80s Chartstarz1980's Best Tunes17235000Tx5d34coxtilzqrpnixd2jlsfz470null2015PopLibr aryAll of My Heart80s Chartstarz1980's Best
- 5. Tunes20226000T454o66tpbawe66lr5tycofcjki70null2015PopLib raryYou Came80s Chartstarz1980's Best Tunes12198000Tzce6k3t2fttkmzsm4oapbu5xeq70null2015PopLi braryBelfast Child80s Chartstarz1980's Best Tunes28353000T4gdbt2psynrv5dmefhek2fwiiy70null2015PopLi braryInvisible80s Chartstarz1980's Best Tunes31223000Thcd4sjhvcoeapii5izj6qqchji70null2015PopLibr aryStop Draggin' My Heart Around80s Chartstarz1980's Best Tunes30244000T3whrfkrwzu3lzf4ezuwt6kp7zu70null2015PopLi braryWe Are the World80s Chartstarz1980's Best Tunes25351000Tgyonnnfqlfjywjli3piak2257470null2015PopLib raryWhenever You Need Somebody80s Chartstarz1980's Best Tunes24215000Tcyhj6iwpfkbucxjygyvbv7arbi70null2015PopLi brarySing Our Own Song80s Chartstarz1980's Best Tunes16212000T2dk4ikp3cxodfbet5dmyvdyxa470null2015PopL ibraryMony Mony80s Chartstarz1980's Best Tunes21254000Tdlkya4dotldijxpils5f6dor5m70null2015PopLibr aryBrass in Pocket (I'm Special)80s Chartstarz1980's Best Tunes10188000Tzy2owqsqg57qili6qw2uv7t6pu70null2015PopL ibraryI'm Still Standing80s Chartstarz1980's Best Tunes9176000T7fit2iliiapcl7peaaeyiip2cy70null2015PopLibrary Out of Touch80s Chartstarz1980's Best Tunes18204000Tor6xlqd7qjsjxnc3bxr3tkbpgy70null2015PopLib raryAnother Day in Paradise80s Chartstarz1980's Best Tunes8294000Tlynqs4r2pd7nhhcw6jhriqpqnq70null2015PopLib rarySimply Irresistible80s Chartstarz1980's Best Tunes2254000Tjvyam7pgt6edpgm5ya2bfurgny71null2015PopLi braryI Found Someone80s Chartstarz1980's Best Tunes13233000Tfgzwfwhuyttrhjtuhxkapo45fy70null2015PopLib raryDanger Zone80s Chartstarz1980's Best Tunes1212000Txm677sxryryagzkvjxdbbpk72q71null2015PopLi braryThe Captain of Her Heart80s Chartstarz1980's Best Tunes5239000T7yngn6ybpza3yzqoahbj3dcbna70null2015PopLi braryJack & Diane80s Chartstarz1980's Best Tunes22250000Tz72lsacseojt7uj2onsgm3va4i70null2015PopLib raryRhythm Is Gonna Get You80s Chartstarz1980's Best
- 6. Tunes15237000Trguw7s6vcdvv3chddux6czohtu70null2015PopL ibraryNight And DayJimmy BrunoSolo12239000Tzcbnbyogxgn6v37itwmg4q5bpa70null2004 JazzLibraryLash OutAlice MertonNo Roots EP2194000Tvkpbmzydjweqvmrzpcpmfatifu70null2017Alternati ve/IndieLibraryBody Like A Back RoadSam HuntBody Like A Back Road1165000T74fdrq3trpmdivax7ghfz5lxha75null2017Country LibraryFire At Midnight (2003 Remastered Version)Jethro TullSongs From The Wood9147000Te7qfvgf75ej25i5xqj22mblsii74null1977Progressi ve/Art RockLibraryHigh Noon NeonJason AldeanRearview Town15175000Tfgzmqqrfgafhu6tbm3dxmkwkwu5252018Countr ycountryWalk, Don't RunThe VenturesWalk Don't Run6122000Tblpjrwwcfzuebbz3mjflekpt7u55null1960RockSurfi n' MikeTequilaThe ChampsTequila1135000Tqo5ixyvqswkgiwp636lup4ogu454null2 009PopSurfin' MikePipelineThe VenturesGold12143000T6g6hiuqxpwatu35pkf437o3biy53null20 06RockSurfin' MikeWipeoutBeach BoysBeach Boys3136000Tje3a4z77clrwassqt7dz5axodm53null2014'60s PopSurfin' MikeSurfer GirlBeach BoysBeach Boys6138000Tzicgozv7pldsw4gkesteg3g2pi53null2014'60s PopSurfin' MikeSurfin' SafariBeach BoysBeach Boys1119000Ts5uhic64vvhffwtfc2uhv5tda452null2014'60s PopSurfin' MikeSurfinBeach BoysBeach Boys8133000T5jb2cxzo6hukh7krjvjdczywqe52null2014'60s PopSurfin' MikeI Get AroundBeach BoysBeach Boys15131000Tjdgtq42ut4qn3ilt3xwdptebpi52null2014'60s PopSurfin' MikeMeant to Be (feat. Florida Georgia Line)Bebe RexhaAll Your Fault: Pt. 26163000T3nxypw72ewkt3nr4ub2pb4id5m51252017PopThumbs UpHigh Noon NeonJason AldeanRearview Town15175000Tfgzmqqrfgafhu6tbm3dxmkwkwu5252018Countr yThumbs UpMeant to Be (feat. Florida Georgia Line)Bebe RexhaAll Your Fault: Pt.
- 7. 26163000T3nxypw72ewkt3nr4ub2pb4id5m51252017PopAugust 31, 2018 QueueIssues (Alan Walker Remix)Julia MichaelsIssues (Alan Walker Remix)1181000Tigeilxwbqketwpmurwmrnu6vhu51null2017Dan ce/ElectronicAugust 31, 2018 QueueThe WaveR3HAB, Lia Marie JohnsonThe Wave2158000T35b3caqbvmmvnxlfsgtglckl7u51null2018PopAu gust 31, 2018 QueueNo Promises (feat. Demi Lovato)Cheat CodesNo Promises (feat. Demi Lovato)1222000Tovudjlv2i2qaptv2e6uio6ajuy51null2017PopAu gust 31, 2018 QueueLights Down LowMAXHell's Kitchen Angel5223000Tsmwhvgvorgirpowjnbgfot24bi51null2016PopAu gust 31, 2018 QueueGoldKiiaraGold1225000Tjn6f7feql3t4jpjx53jd7jppde51nu ll2015PopAugust 31, 2018 QueueNow Or NeverHalseyhopeless fountain kingdom (Deluxe)6214000Tk3nzcvded7yxseifn7wgy6fcs451null2017Elec tropopAugust 31, 2018 QueueI Got TimeBebe RexhaAll Your Fault: Pt. 22230000Tg4x7xbljx5sa5pmkfncir3o3vi53null2017PopAugust 31, 2018 QueueHide AwayDayaSit Still, Look Pretty6192000Tlvfrrrrckcvl4ovvup4f7f3vee51null2016PopAugu st 31, 2018 QueueSolo (feat. Demi Lovato)Clean BanditSolo (feat. Demi Lovato)1222000Tqwwn7xrqxobxbiumq743t6wmgu51null2018D ance/ElectronicAugust 31, 2018 QueueGirls Like You (feat. Cardi B)Maroon 5Red Pill Blues11235000Tbjnigbhufbsor4u3ls2fegjeoq54null2017PopAug ust 31, 2018 QueueTip Toe (feat. French Montana)Jason DeruloTip Toe (feat. French Montana)1187000T3g2zzrfixiupdagq22okn6tzxu51null2017Pop August 31, 2018 QueueRise (feat. Jack & Jack)Jonas BlueRise1194000Tdmxuabsnst4vy3cq4p5tb343sy51null2018Dan ce/ElectronicAugust 31, 2018 QueueMama SaidLukas GrahamLukas Graham3206000Telcjy4kpr4aosim5gp4s5pjrb451null2015PopAu
- 8. gust 31, 2018 QueueMercy (Loote Remix)Shawn MendesMercy (Loote Remix)1203000Tkykzdwev6qobdel76f4fykbqpu53null2016PopA ugust 31, 2018 QueueAttention (Acoustic)Charlie PuthAttention (Acoustic)1206000Tvnf7mblieuxfk2zy6devt4lz6454null2017Pop August 31, 2018 QueueDancerFlo RidaDancer1182000Twyqignxeu2r3a7rbqg2d4zy36451null2018 Hip-Hop/RapAugust 31, 2018 QueueGateway DrugBebe RexhaAll Your Fault: Pt. 15212000Te4frlkxkppjxrdsqcbvuaa7isu53null2017Contemporar y R&BAugust 31, 2018 QueueTG4MZara LarssonSo Good5172000T76h4dwcgz5q3zbrcn3rqtap6pi51null2017PopAug ust 31, 2018 QueueDon't LeaveSnakehips & MØDon't Leave1214000T3srnlbpmywaqpwbdnndaoff5wa52null2017PopA ugust 31, 2018 QueueYour Song (Acoustic)Rita OraYour Song (Acoustic)1181000Tjyeff5rml2jvunyxekr2dpfwtm51null2017Po pAugust 31, 2018 QueueHunterGalantisHunter1183000T72fnnnefn2i2d5ttrgwbqpit se51null2017Dance/ElectronicAugust 31, 2018 QueueOverdoseAlessia CaraKnow-It-All (Deluxe)8208000Twjzqhdbbo57jpwggtckmt545ty52null2015Con temporary R&BAugust 31, 2018 QueueKnow No Better (feat. Camila Cabello, Travis Scott & Quavo)Major LazerKnow No Better1225000Tuqmq5xap36zpmtvmbspdfftxym51null2017Worl dAugust 31, 2018 QueueI'll Be ThereJess GlynneI'll Be There1193000Tolomkcdqro7her3zpwgztodurq50null2018PopAu gust 31, 2018 QueueLove LiesKhalid & NormaniLove Lies1201000Titldrdny22pkcw7re7fawnfgku50null2018R&B/Sou lAugust 31, 2018 QueueLove MyselfHailee SteinfeldHow To Be Single: Original Motion Picture Soundtrack11217000Tkegig55zeeqkg4x5ke4icxwka450null2016 PopAugust 31, 2018 QueueKeep It Mello (feat. Omar LinX)Marshmello & Omar LinXJoytime10243000T3lvsqmnvvezvsnnep5edkqpknq50null20 16HouseAugust 31, 2018 QueueHappierEd Sheeran÷ (Deluxe)7207000Tvojp5xcrfhrgzvjudwivdz7wfq50null2017Pop
- 9. August 31, 2018 QueueBad At LoveHalseyhopeless fountain kingdom (Deluxe)11181000Twimc4ymgil5kzri5gyjuberz6u52null2017Ele ctropopAugust 31, 2018 QueueFirst Love (feat. Sabrina Carpenter)Lost KingsFirst Love1207000T73wkc6xlvn6dffptk3g3ofqor450null2017Dance/E lectronicAugust 31, 2018 QueueI'm a MessBebe RexhaExpectations2195000T7kzpul4pmhmpuzeg2llcaxoy3q55n ull2018PopAugust 31, 2018 QueueBad TogetherDua LipaDua Lipa (Deluxe)16238000Tt7pgcxmodaihnccny4zji7jddu50null2017Pop August 31, 2018 Queuerockstar (feat. 21 Savage)Post MaloneCrowd Pleasers (Vol. II)24218000Tq6dyp5qiywncim2d6h4b33lpae50null2018Hip- Hop/RapAugust 31, 2018 QueueConfidentDemi LovatoConfident (Deluxe Edition)1205000Tozrhnsqopnd5727nb3pu5yggmq50null2015Po pAugust 31, 2018 QueueFamiliarLiam PayneFamiliar1196000Trexknxckxx5ifspp73snksjmg450null201 8PopAugust 31, 2018 QueueScared To Be Lonely (DubVision Remix)Martin GarrixScared To Be Lonely Remixes Vol. 12190000Tqbyqoyedt3iug4mrzsjuo4adau50null2017Dance/Elect ronicAugust 31, 2018 QueueThunder / Young Dumb & Broke (Medley)Imagine DragonsThunder / Young Dumb & Broke (Medley)1251000Tzgpmgpij2sxn3xrezykspoyk7a51null2017Alte rnative/IndieAugust 31, 2018 QueueDANCEDNCEDANCE1179000Tkjtmvyg22p6us6sxzpxcnl 3rbq50null2018PopAugust 31, 2018 QueueCloser (R3hab Remix) (feat. Halsey)The ChainsmokersCloser (Remixes)1161000Tp2bqjdkctpazdi65bklbli2kbm54null2016Dan ce/ElectronicAugust 31, 2018 Queue2002Anne-MarieSpeak Your Mind (Deluxe)10187000T7eqmc5em5jgcg6soledbozx6le50null2018Po pAugust 31, 2018 QueueInside OutCamila CabelloCamila5182000Tjj32hmxf4peie3uucjtgngjpjm50null201 8PopAugust 31, 2018
- 10. QueueNewDayaNew1230000Ttmykv6jghxr7luellum5esu3xm50n ull2017PopAugust 31, 2018 QueueGoneBebe RexhaGone1227000Tkwv2lghd4v3xbtvdvgc2qd7vku52null2014 PopAugust 31, 2018 QueueSymphony (feat. Zara Larsson) [Alternative Version]Clean BanditSymphony (feat. Zara Larsson) [Alternative Version]1212000Titpebf5hunyssm7sr3etcmnfau50null2017Danc e/ElectronicAugust 31, 2018 QueueStand By YouRachel PlattenWildfire1219000T56f73wcyfmuawsrdkc5gsdnbhm50null 2016PopAugust 31, 2018 QueueFuneralZara LarssonSo Good13215000Tcud4lre2khftdf6qztisvtezbu50null2017PopAugu st 31, 2018 QueueI Don’t Wanna Live Forever (Fifty Shades Darker)ZAYN & Taylor SwiftFifty Shades Darker (Original Motion Picture Soundtrack)1245000Tdmbigeaqkedngvs2qdauwn5qca51null2017 SoundtracksAugust 31, 2018 QueueBorn To Be YoursKygoBorn To Be Yours1193000Tjylul6lautfumtl4snfea4rurm50null2018Dance/El ectronicAugust 31, 2018 QueueDessert (Remix) (feat. Silentó)DawinDessert2211000Tjyvioj62pcrpybamyjy2m6wd6q 50null2015PopAugust 31, 2018 Queue answers a3_4 DBC-e08-QACS (MIDTERM).accdbCustomerIDLastNameFirstNameAddressCity StateZIPPhoneEmailAddressReferredBy1Shire Robert 6225 Evanston Ave N Seattle WA98103 206-524-2433[email protected]2Goodyear Katherine 7335 11th Ave NE Seattle WA98105 206-524-3544[email protected]13Bancroft Chris 12605 NE 6th Street Bellevue WA98005 425-635-9788[email protected]4Griffith John 335 Aloha Street Seattle WA98109 206-524-4655[email protected]25Tierney Doris 14510 NE 4th Street Bellevue WA98005 425-635-8677[email protected]36Anderson Donna 1410 Hillcrest Parkway Mt. Vernon
- 11. WA98273 360-538-7566[email protected]7Svane Jack 3211 42nd Street Seattle WA98115 206-524-5766[email protected]48Walsh Denesha 6712 24th Avenue NE Redmond WA98053 425-635-7566[email protected]59Enquist Craig 534 15th Street Bellingham WA98225 360-538-6455[email protected]610Anderson Rose 6823 17th Ave NE Seattle WA98105 206-524- 6877[email protected]7EmployeeIDLastNameFirstNamePhoneE mailAddressSupervisorTraining1Stuart Anne 206-527-0010[email protected]Completed2Stuart George 206-527- 0011[email protected]1Completed3Stuart Mary 206-527-0012[email protected]1Completed4Orange William 206-527-0013[email protected]3In process5Griffith John 206-527- 0014[email protected]3In processItemIDItemDescriptionPurchaseDateItemCostItemPriceV endorID1Antique Desk11/7/161800.03000.022Antique Desk Chair11/10/16300.0500.043Dining Table Linens11/14/16600.01000.014Candles11/14/1630.050.015Candl es11/14/1627.045.016Desk Lamp11/14/16150.0250.037Dining Table Linens11/14/16450.0750.018Book Shelf11/21/16150.0250.059Antique Chair11/21/16750.01250.0610Antique Chair11/21/161050.01750.0611Antique Candle Holders11/28/16210.0350.0212Antique Desk1/5/171920.03200.0213Antique Desk1/5/172100.03500.0214Antique Desk Chair1/6/17285.0475.0915Antique Desk Chair1/6/17339.0565.0916Desk Lamp1/6/17150.0250.01017Desk Lamp1/6/17150.0250.01018Desk Lamp1/6/17144.0240.0319Antique Dining Table1/10/173000.05000.0720Antique
- 12. Sideboard1/11/172700.04500.0821Dining Table Chairs1/11/175100.08500.0922Dining Table Linens1/12/17450.0750.0123Dining Table Linens1/12/17480.0800.0124Candles1/17/1730.050.0125Candle s1/17/1736.060.01VendorIDPhonePhoneType1206-325- 67551206-329-9675Fax 2206-325-78662206-329- 9786Fax 3206-325-89773206-329-9897Fax 4425-746-54335425-746-43226206-325-90886206-329-9908Fax 7425-635-75668425-635-97888425-639-9978Fax 9415-422-21219415-423-5212Fax 10415-422- 323210415-429-9323Fax SaleIDCustomerIDEmployeeIDSaleDateSubTotalTaxTotal11112 /14/163500.0290.53790.522112/15/161000.083.01083.033112/1 5/1650.04.1554.1544312/23/1645.03.7448.745151/5/17250.020. 75270.756551/10/17750.062.25812.257641/12/17250.020.75270 .758211/15/173000.0249.03249.09551/25/17350.029.05379.051 0712/4/1714250.01182.7515432.7511852/4/17250.020.75270.75 12542/7/1750.04.1554.1513922/7/174500.0373.54873.5141032/ 11/173675.0305.033980.0315222/11/17800.066.4866.4SaleIDSa leItemIDItemIDItemPrice1113000.0122500.02131000.031450.0 41545.0516250.0617750.0718250.08191250.082101750.091113 50.0101195000.0102218500.010322750.011117250.01212450.0 131204500.0141123200.014214475.015123800.0VendorIDCom panyNameContactLastNameContactFirstNameAddressCityState ZIPPhoneFaxEmailAddress1Lamps and Lighting Huntington Anne 1515 NW Market Street Seattle WA98107 206-325- 6755206-329-9675[email protected]2European Specialties Tadema Ken 6123 15th Avenue NW Seattle WA98107 206-325-7866206-329- 9786[email protected]3Lamps and Lighting Swanson Sally 506 Prospect Street Seattle WA98109 206-325-8977206-329- 9897[email protected]4Lee Andrew 1102 3rd Street Kirkland WA98033 425-746-5433[email protected]5Harrison
- 13. Denise 533 10th Avenue Kirkland WA98033 425-746-4322[email protected]6New York Brokerage Smith Mark 621 Roy Street Seattle WA98109 206-325-9088206-329- 9908[email protected]7Walsh Denesha 6712 24th Avenue NE Redmond WA98053 425-635-7566[email protected]8Bancroft Chris 12605 NE 6th Street Bellevue WA98005 425-635-9788425-639- 9978[email protected]9Specialty Antiques Nelson Fred 2512 Lucky Street San Francisco CA94110 415-422-2121415-423- 5212[email protected]10General Antiques Garner Patty 2515 Lucky Street San Francisco CA94110 415-422-3232415-429- 9323[email protected] SELECT * FROM CUSTOMER; SELECT * FROM EMPLOYEE; SELECT * FROM VENDOR; SELECT * FROM ITEM; SELECT * FROM SALE_ITEM; SELECT ItemID, ItemDescription FROM ITEM WHERE ItemPrice >= 1000; SELECT ItemID, ItemDescription FROM ITEM, VENDOR WHERE ItemPrice >= 1000 ANDCompanyName LIKE 'New*'
- 14. ANDITEM.VendorID = VENDOR.VendorID; SELECT LastName, FirstName, Phone FROM CUSTOMER WHERE CustomerID IN (SELECT CustomerID FROM SALE WHERE SaleID = 1); SELECT LastName, FirstName, Phone FROM CUSTOMER AS C INNER JOIN SALE AS S ON C.CustomerID = S.CustomerID WHERE SaleID = 1; SELECT LastName, FirstName, Phone FROM CUSTOMER WHERE CustomerID IN (SELECT CustomerID FROM SALE WHERE SaleID IN (1, 2, 3)); SELECT LastName, FirstName, Phone FROM CUSTOMER AS C INNER JOIN SALE AS S ON C.CustomerID = S.CustomerID WHERE SaleID IN (1, 2, 3); SELECT LastName, FirstName, Phone FROM CUSTOMER WHERE CustomerID IN (SELECT CustomerID FROM SALE WHERE SubTotal > 500);
- 15. SELECT DISTINCT LastName, FirstName, Phone FROM CUSTOMER AS C INNER JOIN SALE AS S ON C.CustomerID = S.CustomerID WHERE SubTotal > 500; SELECT LastName, FirstName, Phone FROM CUSTOMER WHERE CustomerID IN (SELECT CustomerID FROM SALE WHERE SaleID IN (SELECT SaleID FROM SALE_ITEM WHERE ItemPrice > 500)); SELECT DISTINCT LastName, FirstName, Phone FROM (CUSTOMER AS C INNER JOIN SALE AS S ON C.CustomerID = S.CustomerID) INNER JOIN SALE_ITEM AS SI ON S.SaleID = SI.SaleID WHERE ItemPrice > 500; SELECT LastName, FirstName, Phone FROM CUSTOMER WHERE CustomerID IN (SELECT CustomerID FROM SALE WHERE SaleID IN
- 16. (SELECT SaleID FROM SALE_ITEM WHERE ItemID IN (SELECT ItemID FROM ITEM WHERE VendorID IN (SELECT VendorID FROM VENDOR …