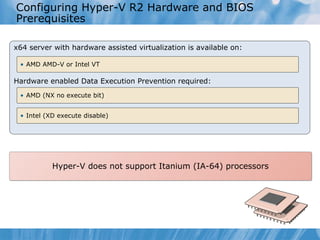
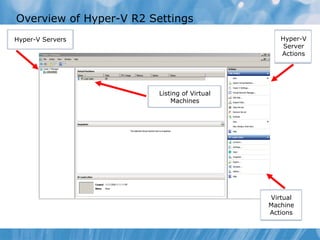
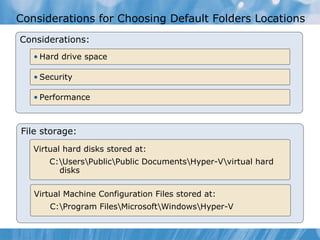
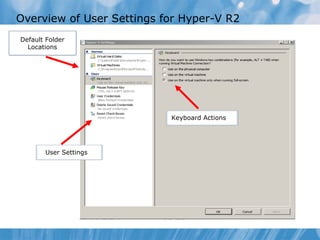
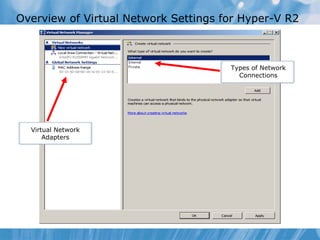
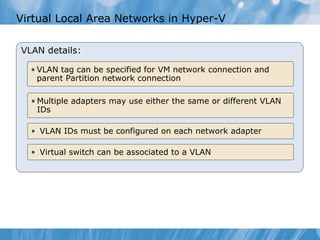
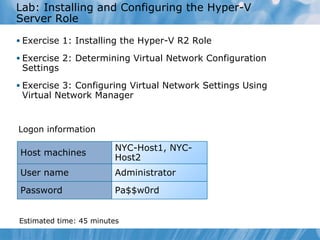
This document provides an overview of installing and configuring the Hyper-V R2 server role. It discusses installing Hyper-V on Windows Server 2008, configuring virtual networks, and considerations for virtual network types and VLAN configurations. Hands-on demonstrations are provided for installing Hyper-V, configuring user settings, virtual networks, and VLAN support.