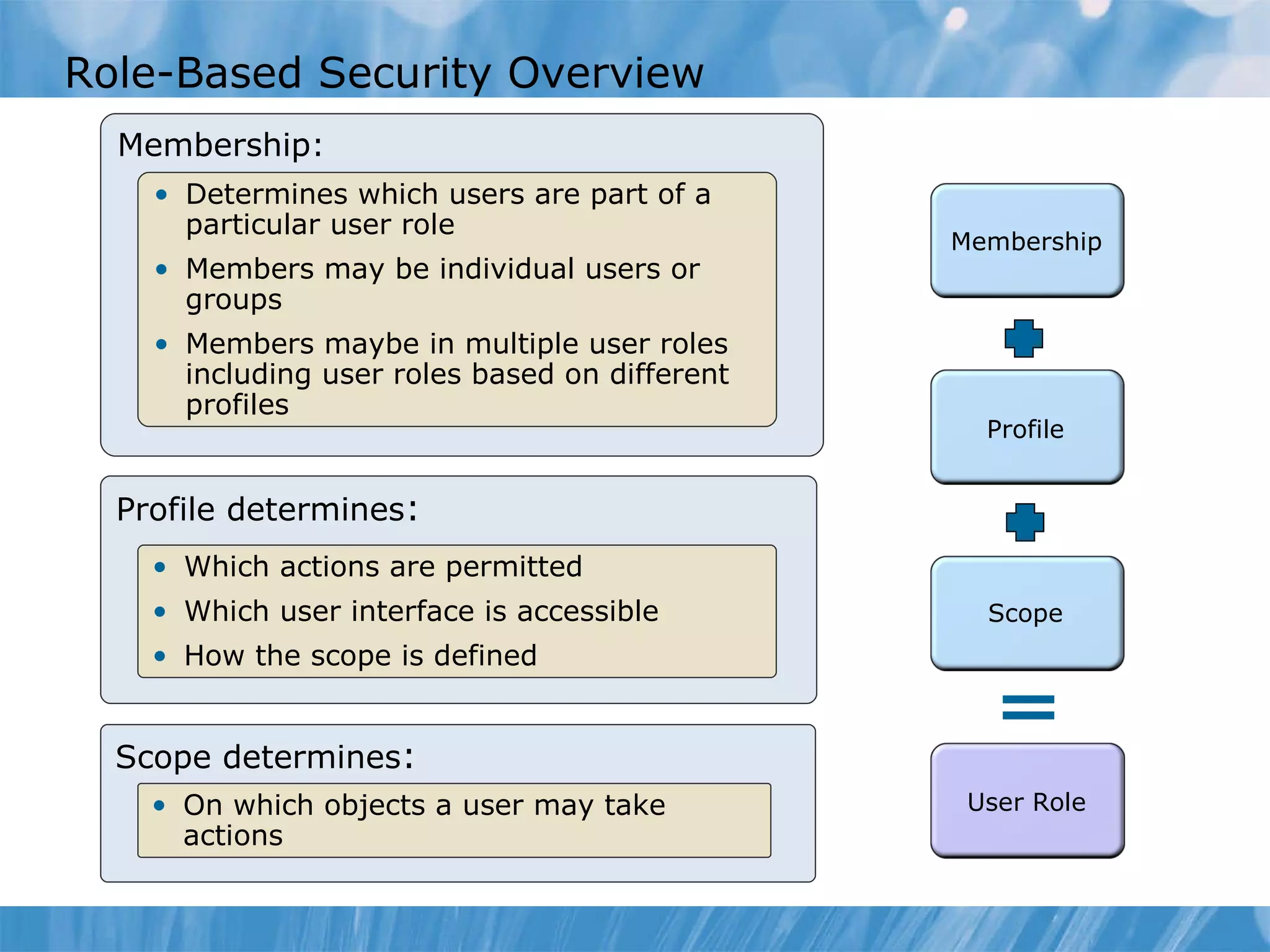
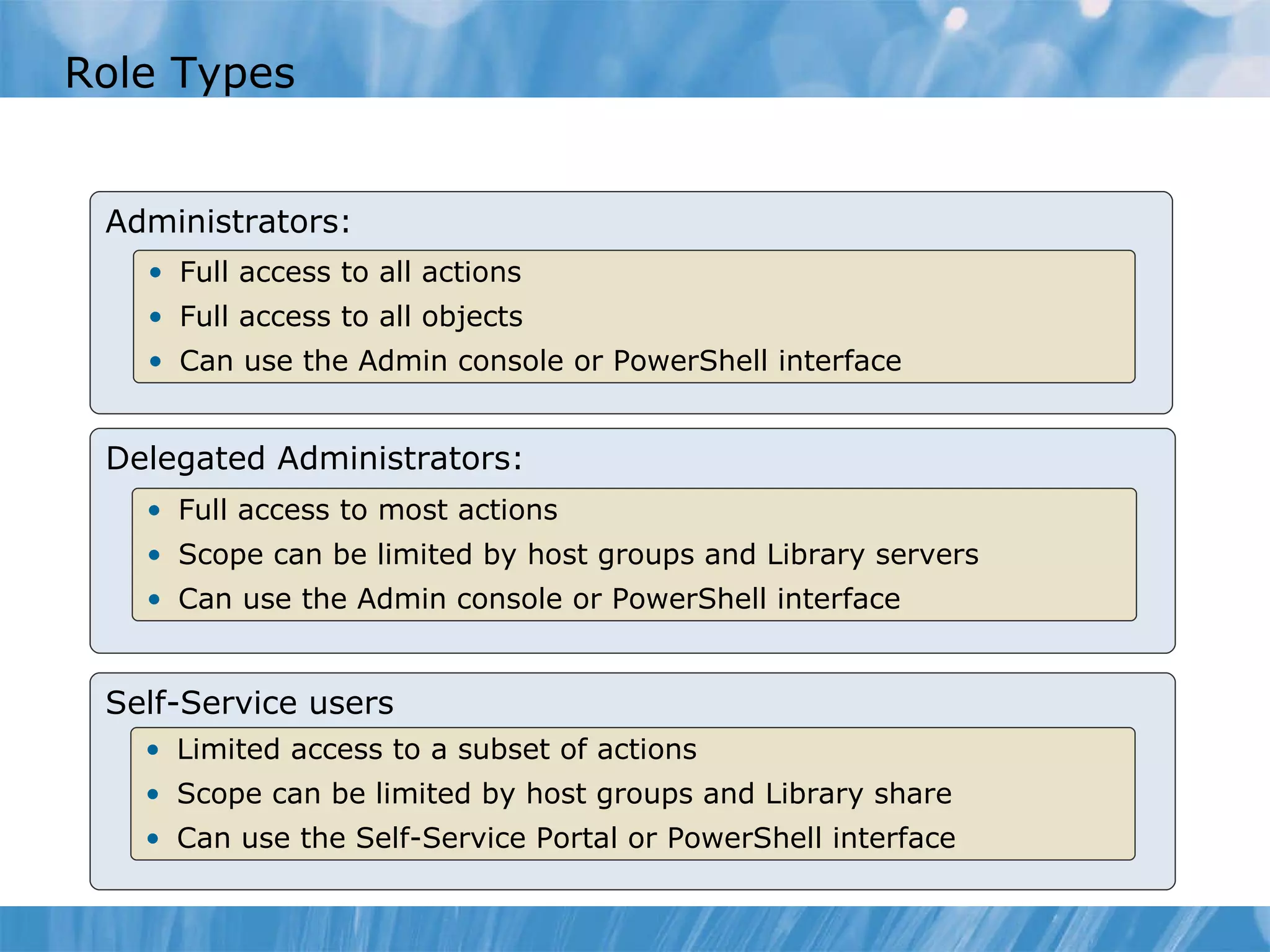
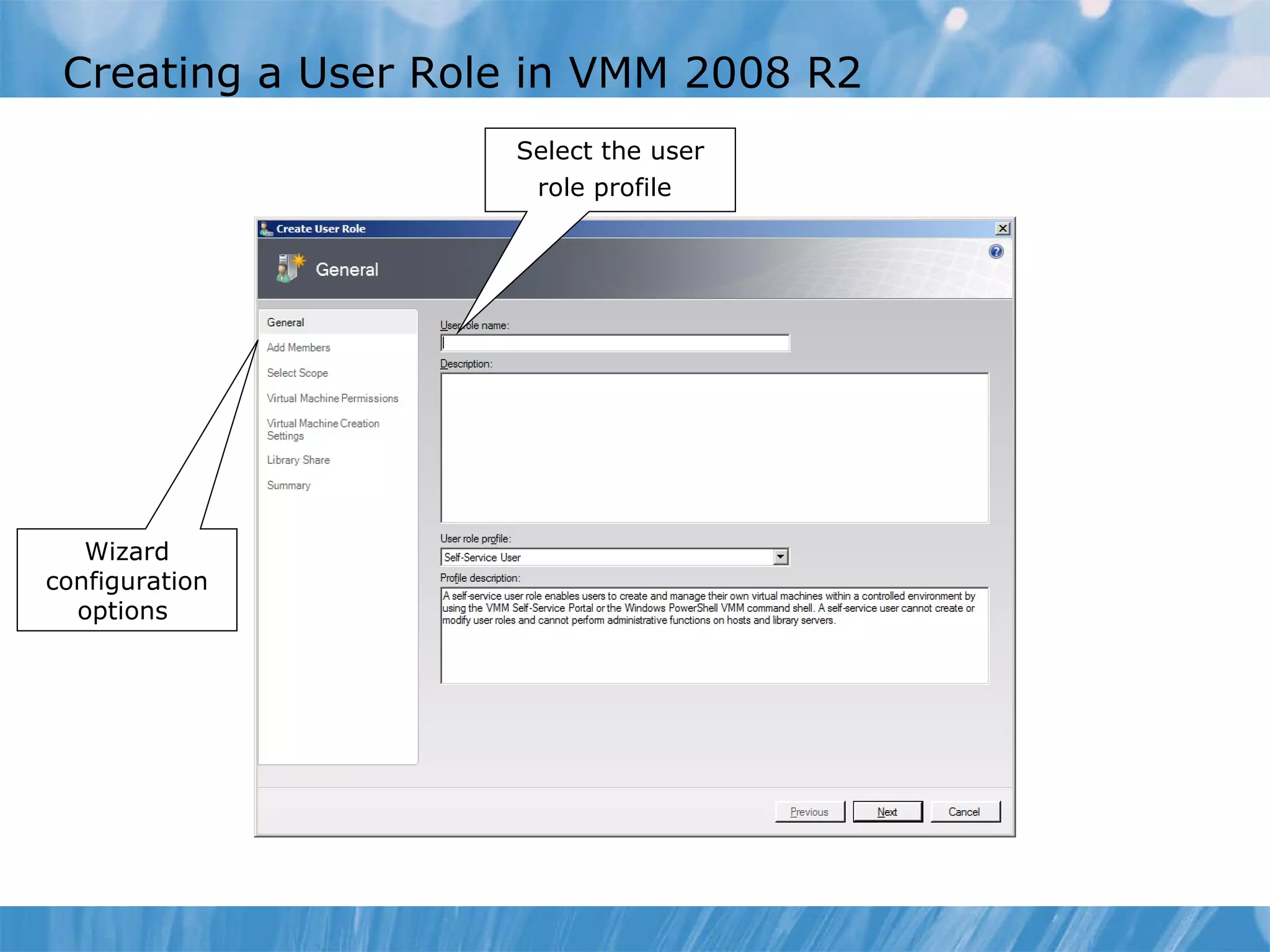
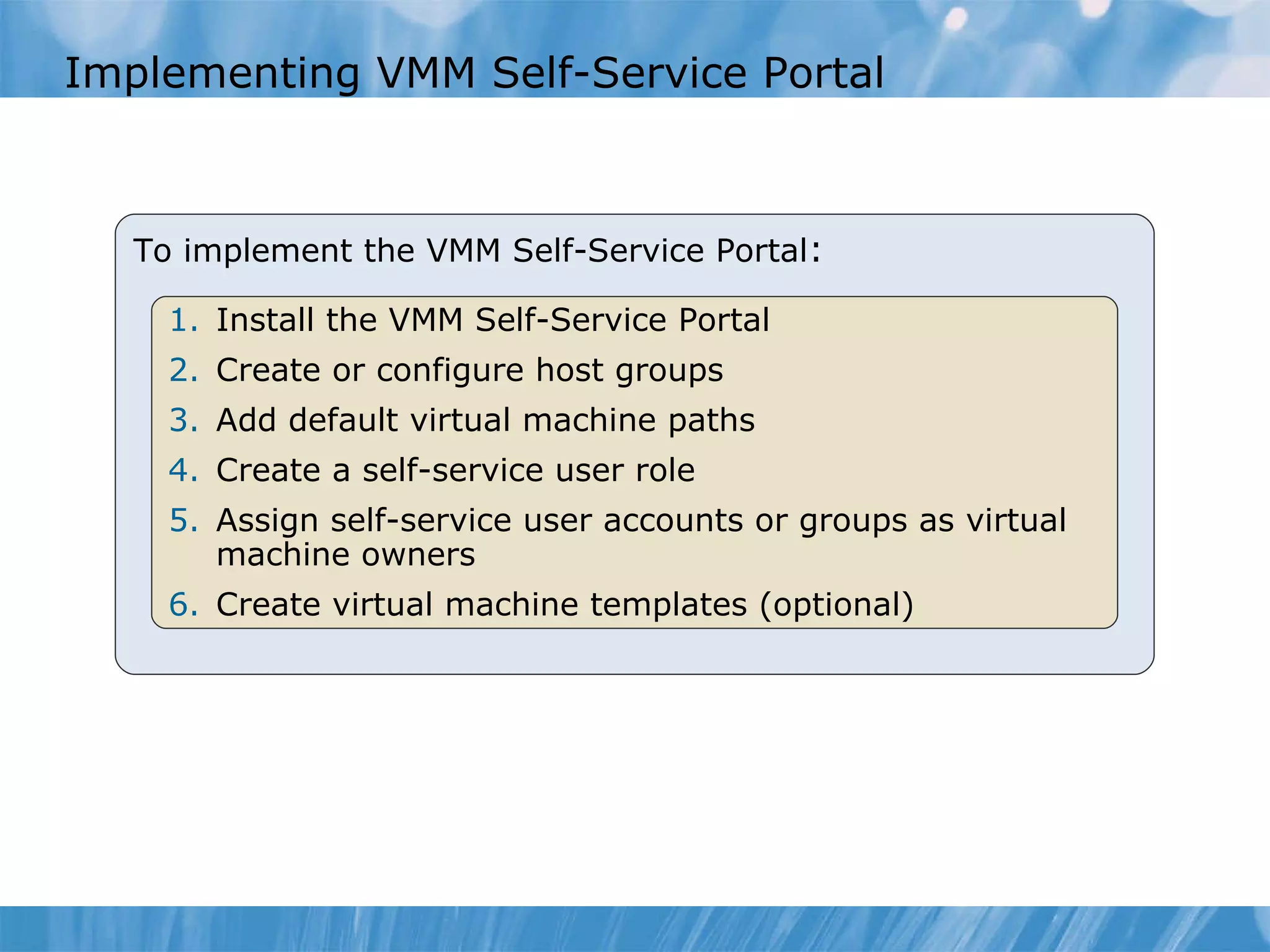
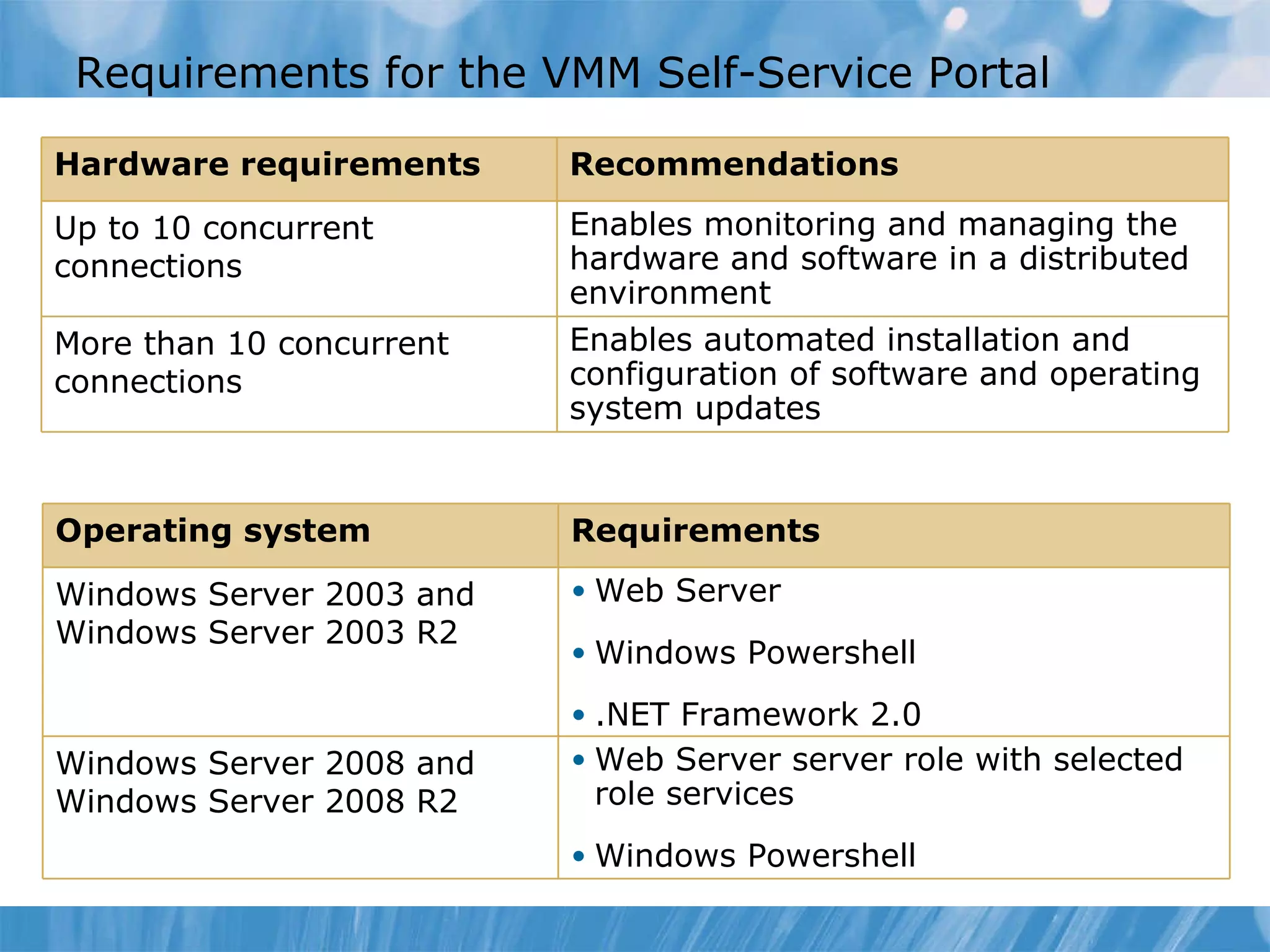
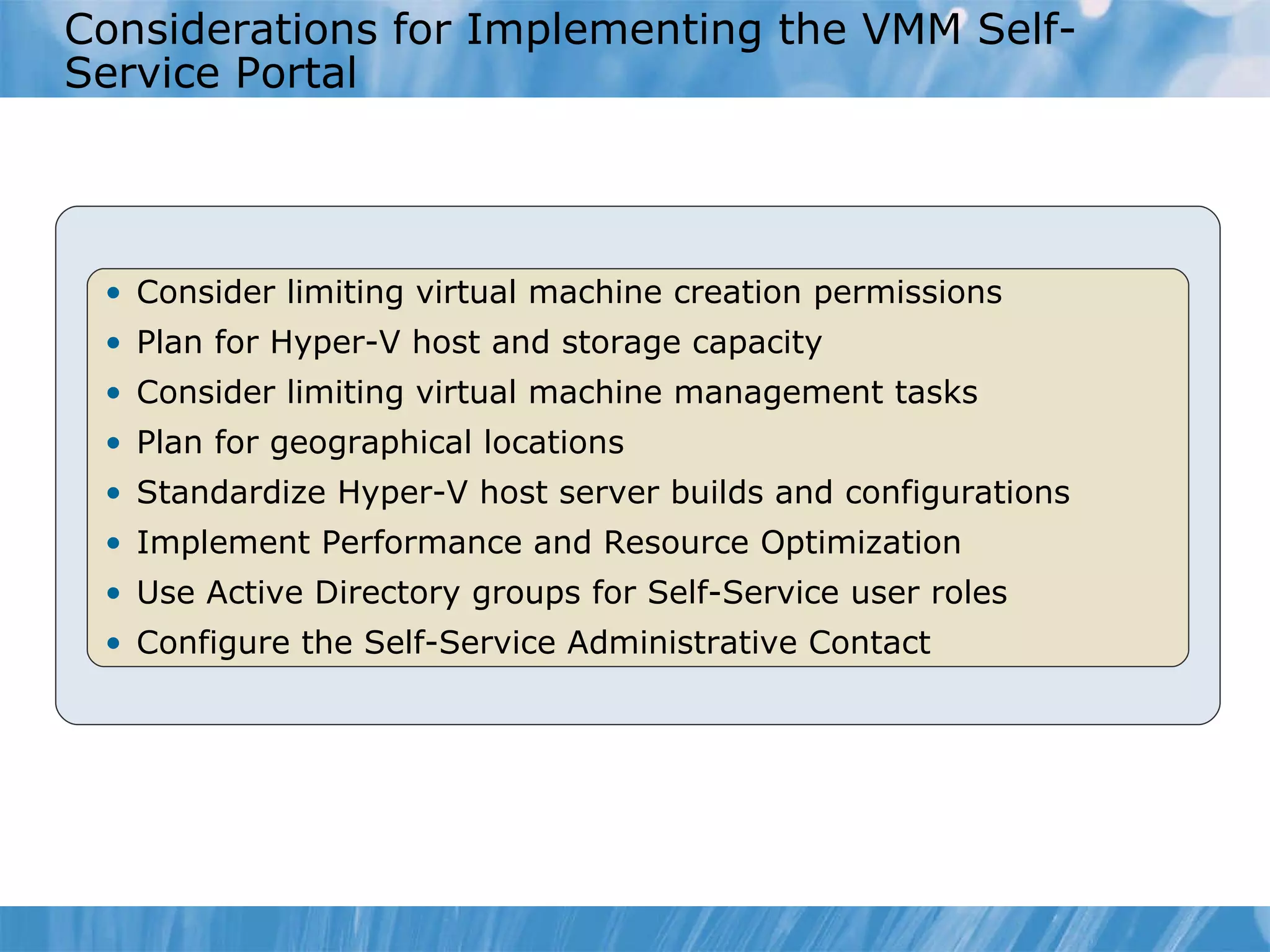
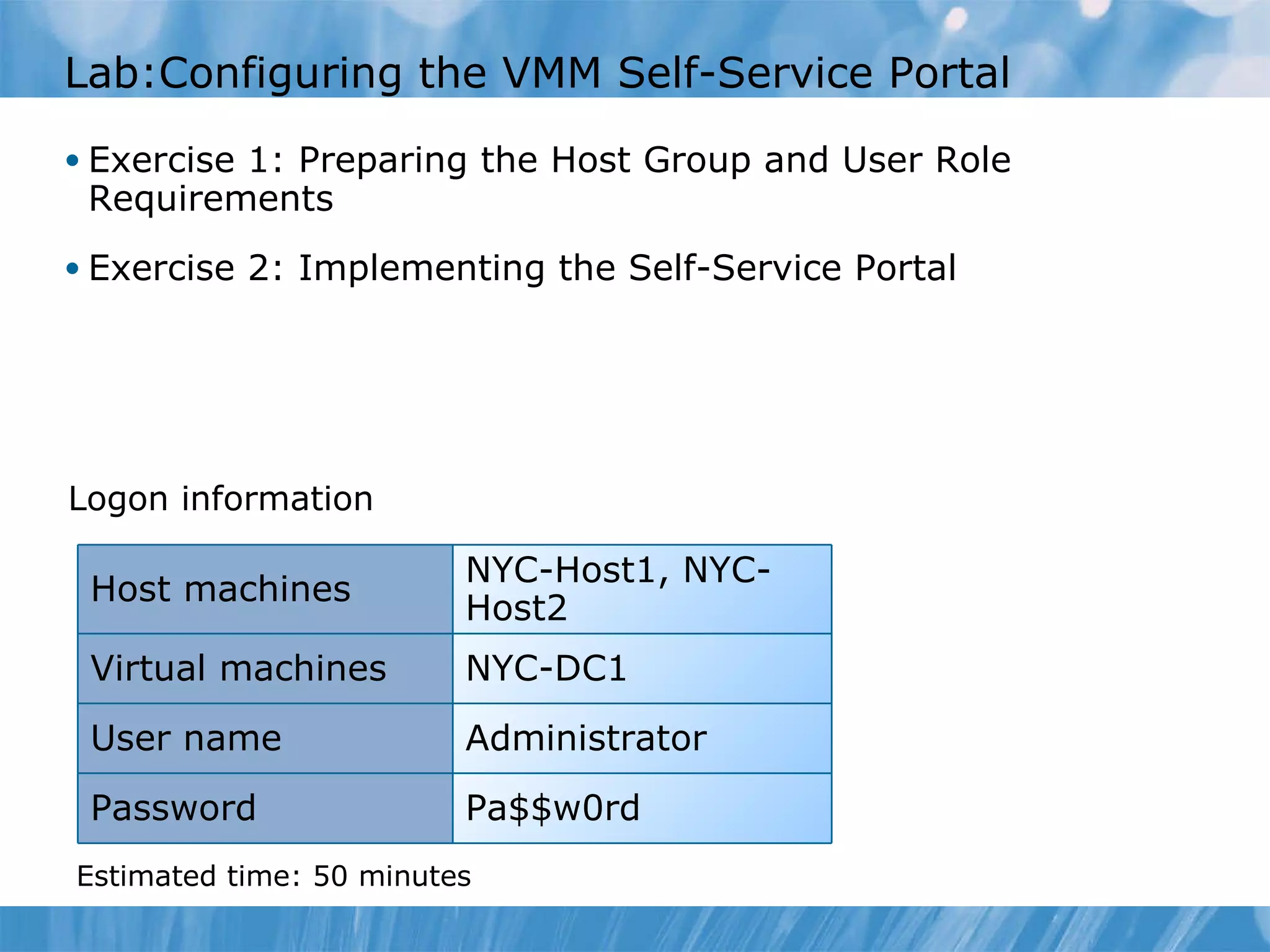
This document discusses configuring user roles and the VMM self-service portal. It covers creating user roles in VMM 2008 R2, installing and configuring the self-service portal, and considerations for implementing it. A demonstration shows how to create a user role and configure access to the portal. The goal is to allow specific groups like a research department to deploy and manage their own virtual machines.