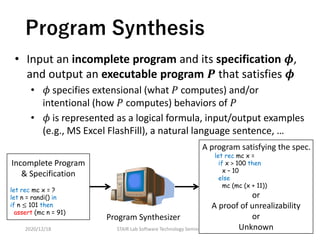
This document presents a tutorial on program verification and synthesis using constraint solving and machine learning, highlighting the importance of reliability in safety-critical systems. It discusses methodologies for both proving program correctness and synthesizing programs from specifications, focusing on constrained horn clauses and predicate constraint satisfaction. Ongoing research includes exploiting AI techniques for formal specification, program synthesis, and verification techniques relevant to the era of AI.









![Program Verification via
Constrained Horn Clauses (CHCs)
2020/12/18 STAIR Lab Software Technology Seminar
Constraint
Generation
𝓒 is Sat (𝑷 satisfies 𝝍),
𝓒 is Unsat (𝑷 violates 𝝍),
or Unknown
Constraint
Solving
Target Program 𝑷 & Specification 𝝍
CHCs Constraints 𝓒 on Predicate Variables
JayHorn for Java [Kahsai+ ’16]
SeaHorn for C [Gurfinkel+ ’15]
RCaml for OCaml [Unno+ ’09]
SPACER [Komuravelli+ ’14]
Hoice [Champion+ ’18]
Eldarica [Hojjat+ ’18]
12](https://image.slidesharecdn.com/20201218stair-201218052800/85/1-12-320.jpg)
![CHCs: Constrained Horn Clauses
(see e.g., [Bjørner+ ’15] )
• A finite set 𝓒 of Horn-clauses of either form:
where 𝑋0, 𝑋1 … , 𝑋 𝑚 are predicate variables,
𝑡0, … , 𝑡 𝑚 are sequences of terms of a 1st-order theory 𝑇,
𝜙 is a formula of 𝑇 without predicate variables.
• 𝓒 is satisfiable (modulo 𝑇) if there is an interpretation 𝜌 of
predicate variables such that 𝜌 ⊨ ⋀𝓒
2020/12/18 STAIR Lab Software Technology Seminar
𝑋0 𝑡0 ⟸ 𝑋1 𝑡1 ∧ ⋯ ∧ 𝑋 𝑚 𝑡 𝑚 ∧ 𝜙
13
⊥ ⟸ 𝑋1 𝑡1 ∧ ⋯ ∧ 𝑋 𝑚 𝑡 𝑚 ∧ 𝜙or](https://image.slidesharecdn.com/20201218stair-201218052800/85/1-13-320.jpg)



![pCSP Constraints 𝓒 on Predicate Variables
Target Program 𝑷 & Specification 𝝍
Program Verification via Predicate
Constraint Satisfaction [Satake+ ’20]
2020/12/18 STAIR Lab Software Technology Seminar
Constraint
Generation
𝓒 is Sat (𝑷 satisfies 𝝍),
𝓒 is Unsat (𝑷 violates 𝝍),
or Unknown
Constraint
Solving
Applicable to (Finitely-)
Branching-Time Safety
Verification
17
PCSat [Satake+ ’20, Unno+ ’20]](https://image.slidesharecdn.com/20201218stair-201218052800/85/1-17-320.jpg)

![pCSP: Predicate Constraint
Satisfaction Problem[Satake+ ’20]
• A finite set 𝓒 of clauses of the form:
where 𝑋1, … , 𝑋 𝑚 are predicate variables,
𝑡1, … , 𝑡 𝑚 are sequences of terms of a 1st-order theory 𝑇,
𝜙 is a formula of 𝑇 without predicate variables.
• 𝓒 is satisfiable (modulo 𝑇) if there is an interpretation 𝜌 of
predicate variables such that 𝜌 ⊨ ⋀𝓒
• 𝓒 is CHCs if ℓ ≤ 1 for all clause in 𝓒
2020/12/18 STAIR Lab Software Technology Seminar
𝑋1 𝑡1 ∨ ⋯ ∨ 𝑋ℓ 𝑡ℓ ⟸
𝑋ℓ+1 𝑡ℓ+1 ∧ ⋯ ∧ 𝑋 𝑚 𝑡 𝑚 ∧ 𝜙
19](https://image.slidesharecdn.com/20201218stair-201218052800/85/1-19-320.jpg)



![pfwCSP Constraints 𝓒 on Predicate Variables
Target Program 𝑷 & Specification 𝝍
Program Verification via Extended
Predicate Constraint Satisfaction [Unno+ ’20]
2020/12/18 STAIR Lab Software Technology Seminar
Constraint
Generation
𝓒 is Sat (𝑷 satisfies 𝝍),
𝓒 is Unsat (𝑷 violates 𝝍),
or Unknown
Constraint
Solving
Applicable to (Infinitely-)
Branching-Time Safety &
Liveness Verification
23
PCSat [Satake+ ’20, Unno+ ’20]](https://image.slidesharecdn.com/20201218stair-201218052800/85/1-23-320.jpg)

![pfwCSP: Extension of pCSP with Functional
and Well-founded Predicates [Unno+ ’20]
(cf. ∀∃CHCs with dwf [Beyene+ ’13])
• A finite set 𝓒 of pCSP clauses equipped with
a map 𝓚 from predicate variable 𝑋 in 𝓒 to ⋆, 𝜆, ⇓
• 𝑋 is ordinary predicate if 𝓚 𝑋 = ⋆
• 𝑋 is functional predicate if 𝓚 𝑋 = 𝜆
• 𝑋 is well-founded predicate if 𝓚 𝑋 = ⇓
• 𝓒 is satisfiable (modulo 𝑇) if there is an interpretation
𝜌 of predicate variables such that
• 𝜌 ⊨ ⋀𝓒
• ∀𝑋. 𝓚 𝑋 = 𝜆 ⟹ 𝜌 𝑋 characterizes a total function
• ∀𝑋. 𝓚 𝑋 = ⇓ ⟹ 𝜌 𝑋 represents a well-founded relation
2020/12/18 STAIR Lab Software Technology Seminar 25](https://image.slidesharecdn.com/20201218stair-201218052800/85/1-25-320.jpg)




![Further Applications of pfwCSP
• Refinement type inference [Unno+ ’09,’13,’18, Nanjo’18, Katsura+ ’20]
• Validity checking of fixpoint logic formulas
• LTL, CTL, CTL*, modal-mu calculus model checking
• Infinite-state infinite-duration game solving
• Bisimulation and bisimilarity verification
• Hyperproperties verification
• Program synthesis
• …
2020/12/18 STAIR Lab Software Technology Seminar 31
(see [Unno+ ’20] and upcoming papers)](https://image.slidesharecdn.com/20201218stair-201218052800/85/1-31-320.jpg)

![Program Synthesis via
Syntax-Guided Synthesis (SyGuS)
2020/12/18 STAIR Lab Software Technology Seminar
Constraint
Generation
𝓒 is Sat (some 𝑷 ∈ 𝓛 satisfies 𝝍),
𝓒 is Unsat (all 𝑷 ∈ 𝓛 violates 𝝍),
or Unknown
Constraint
Solving
SyGuS Constraints 𝓒 on Function Variables
Language 𝓛 & Specification 𝝍
33
CVC4 [Reynolds+ ’15,’19]
DryadSynth [Huang+ ’20]
PCSat [Satake+ ’20, Unno+ ’20]](https://image.slidesharecdn.com/20201218stair-201218052800/85/1-33-320.jpg)
![SyGuS: Syntax-Guided
Synthesis [Alur+ ’15]
• Fix a first-order background theory 𝑇 such as:
• Linear integer arithmetic (LIA)
• Strings (for FlashFill benchmarks)
• Bit-vectors (for Hackers' Delight benchmarks)
• Given
• Specification: 𝑇-formula 𝜙 over a function variable 𝑓
• Language: context-free grammar 𝐺 characterizing the
set ℒ 𝐺 of allowed 𝑇-terms
• Find a term 𝑡 ∈ ℒ 𝐺 such that ⊨ 𝑡/𝑓 𝜙
2020/12/18 STAIR Lab Software Technology Seminar 34](https://image.slidesharecdn.com/20201218stair-201218052800/85/1-34-320.jpg)



![Challenges in Constraint Solving
• Undecidable in general even for decidable theories
• The search space of solutions is often very large
(or unbounded), high-dimensional, and non-smooth
2020/12/18 STAIR Lab Software Technology Seminar
To address these challenges, researchers are
integrating deductive & inductive reasoning
techniques within the framework of
CounterExample Guided Inductive Synthesis
(CEGIS) [Solar-Lezama+ ’06]
38](https://image.slidesharecdn.com/20201218stair-201218052800/85/1-38-320.jpg)










![Machine Learning for CEGIS
• Adapt ML models and algorithms to implement Learner
• Piecewise linear classifiers [Sharma+ ’13a, Garg+ ’14, Unno+ ’20]
• Decision trees [Krishna+ ’15, Garg+ ’16, Champion+ ’18, Ezudheen+ ’18, Zhu+ ’18]
• Neural networks [Chang+ ’19, Zhao+ ’20, Abate+ ’21]
• Greedy set covering w/ logic minimization [Padhi+ ’16, Sharma+ ’13b]
• Metropolis Hastings MCMC sampler [Sharma+ ’14]
• Probabilistic inference, survey propagation [Satake+ ’20]
• Ensemble learning [Padhi+ ’20]
• Learning to learn
• Reinforcement learning of NNs to generate candidates [Si ’18]
• Reinforcement learning of strategy to adjust classification models used
by Learner (joint work w/ Tsukada, Sekiyama, Suenaga)
2020/12/18 STAIR Lab Software Technology Seminar 49](https://image.slidesharecdn.com/20201218stair-201218052800/85/1-49-320.jpg)




