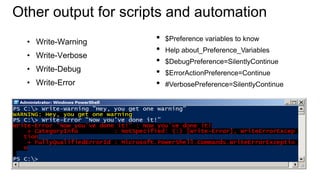
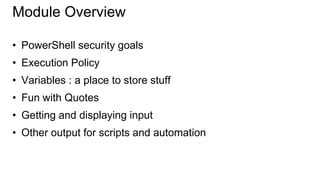
This document discusses getting prepared for automation in PowerShell. It covers PowerShell security goals of being secured by default to prevent mistakes while allowing script execution. It also discusses execution policies for controlling script execution and using variables to store information in scripts. The document provides examples of using variables, quotes, getting input, and different output types in scripts and automation.




![Variables: A place to store stuff
• Use $ to create and use
variables
• Can contain letters, numbers,
spaces and underscores
• Don’t persist after Shell exits
• New-Variable
• Set-Variable
• Get-Variable
• Clear-Variable
• Remove-Variable
• Can force a type – [int]$var
Note: The $ is not part of the variable
name, it’s a cue to access the contents
of the variable](https://image.slidesharecdn.com/08-gettingpreparedforautomation-131218075036-phpapp01/85/08-getting-prepared-for-automation-6-320.jpg)