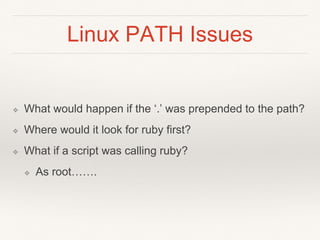
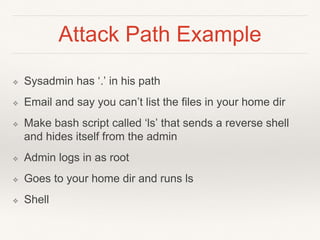
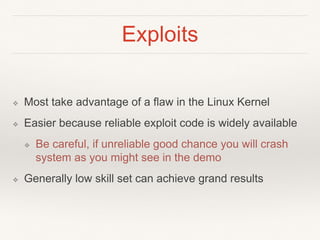
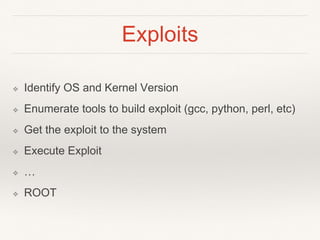
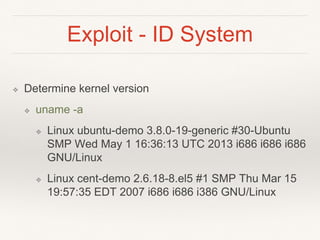
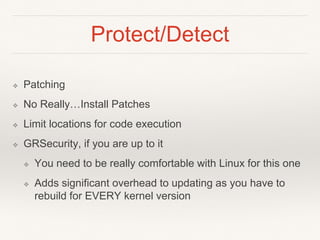
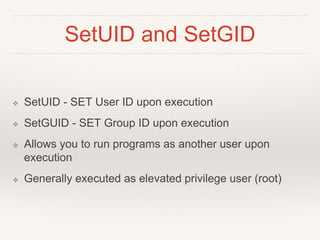
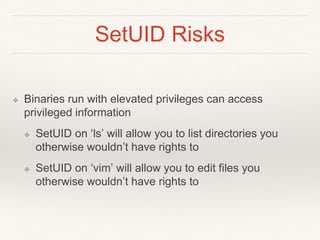
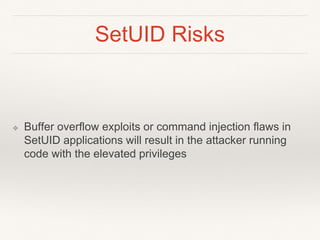
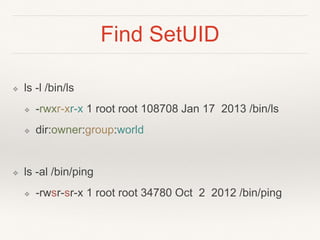
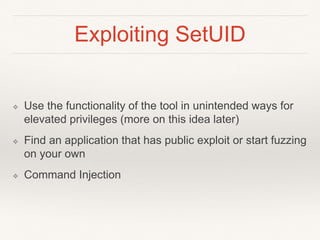
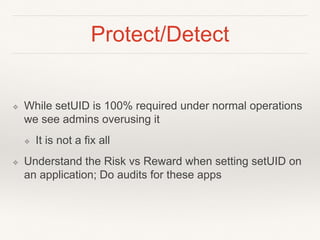
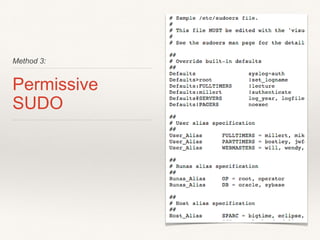
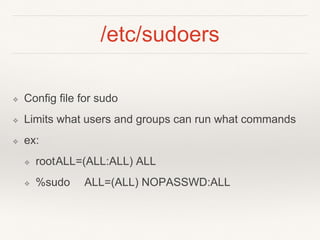
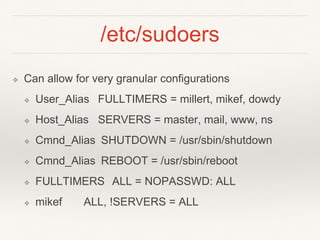
This document provides an introduction to techniques for Linux privilege escalation. It discusses exploiting vulnerabilities like kernel exploits, taking advantage of permissive file permissions like world-readable/writable files and SetUID programs, exploiting overly permissive sudo configurations, and issues that can arise from improper PATH variable configuration like executing a Trojan program. The document demonstrates finding and using exploits, identifying vulnerable configurations, and how an attacker could leverage each technique to escalate privileges on a target Linux system. It also provides recommendations for how to protect against these methods through patching, auditing permissions and configurations, and restricting what programs can be executed with elevated privileges.


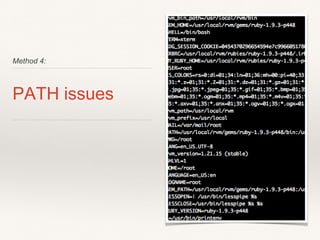
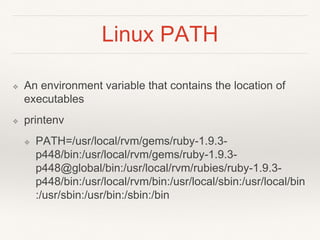
![Linux PATH
❖ ruby -v
❖ ruby 1.9.3p448 (2013-06-27 revision 41675) [i686-
linux]
❖ which ruby
❖ /usr/local/rvm/rubies/ruby-1.9.3-p448/bin/ruby](https://image.slidesharecdn.com/0fsjnkiqyaw0fnpl3k4i-signature-50e925eb952b3ca00f24fe9f84de304493eb270f605d31687c51579037624a72-poli-140730142214-phpapp01/85/Fundamentals-of-Linux-Privilege-Escalation-39-320.jpg)