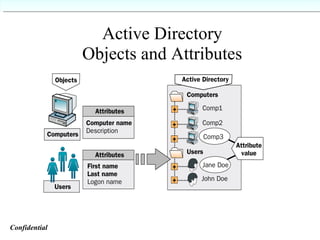
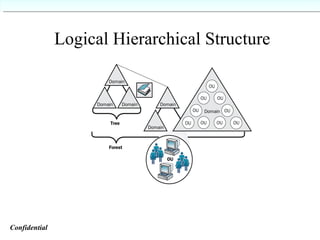
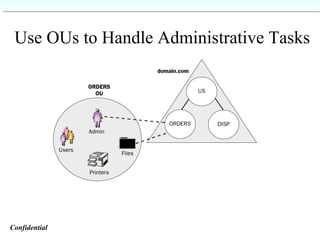
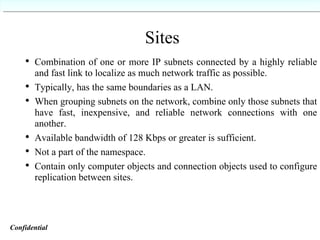
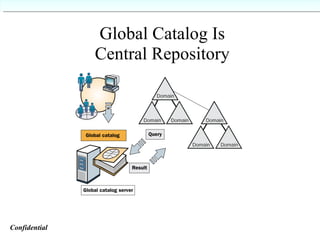
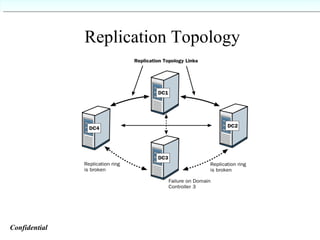
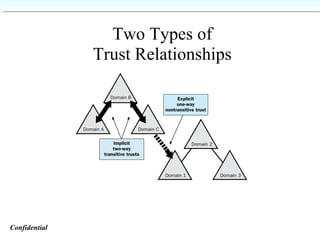
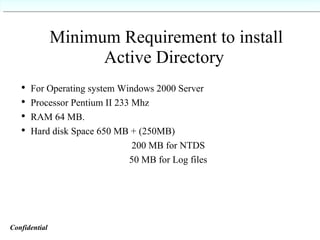
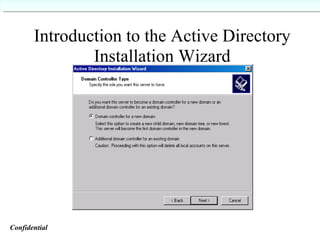
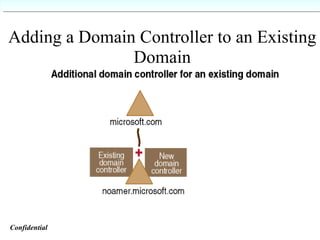
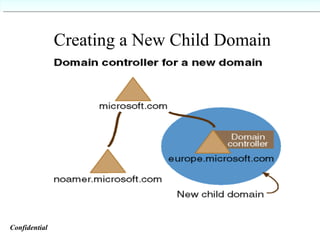
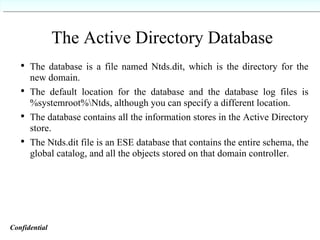
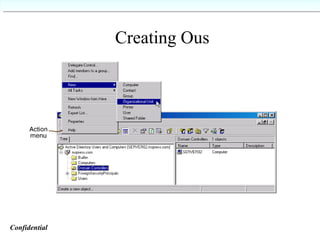
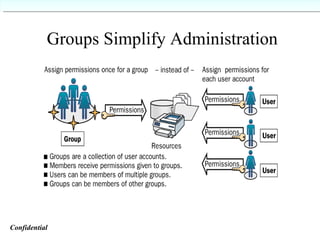
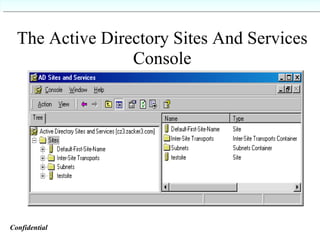
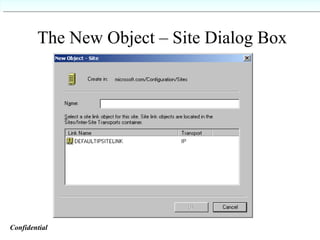
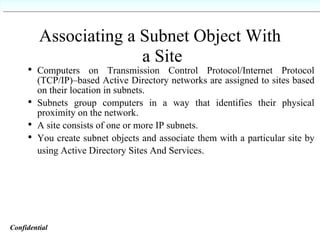
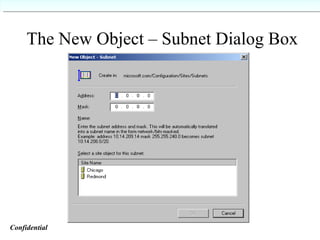
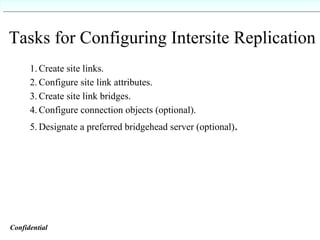
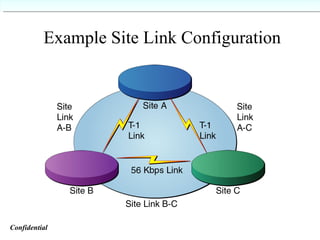
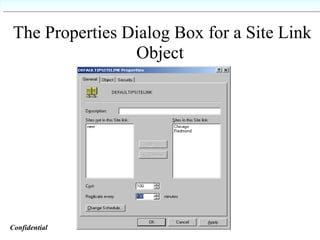
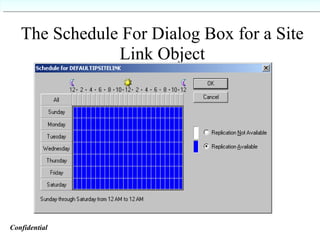
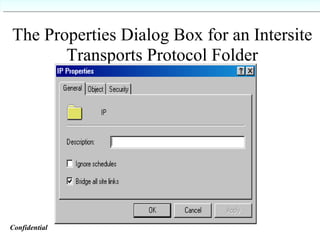
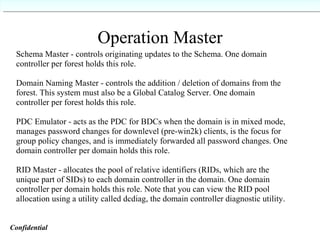
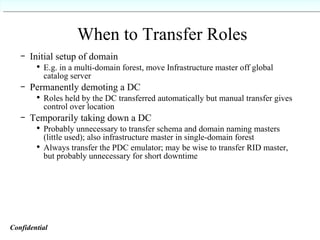
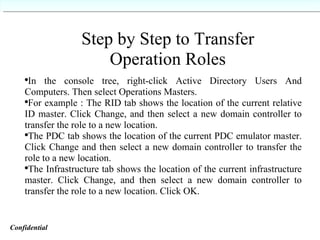
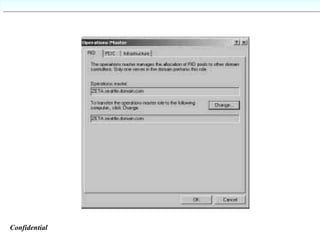
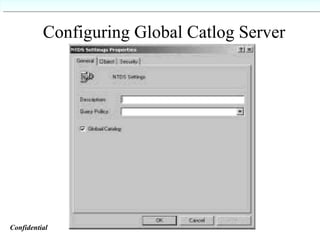
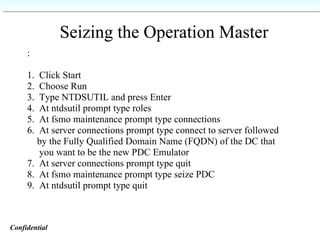
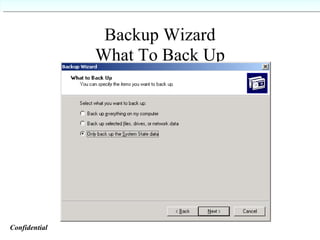
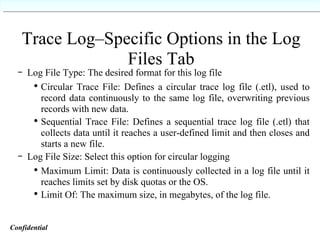
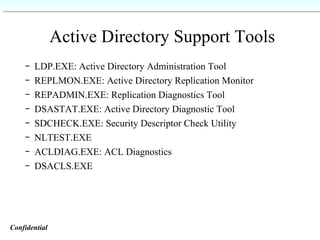
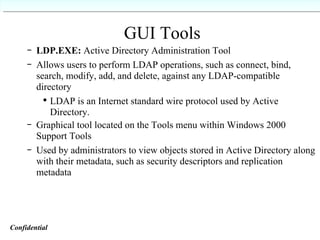
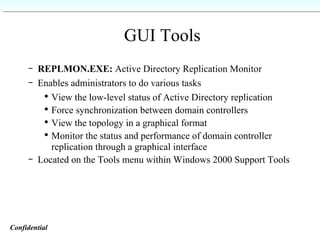
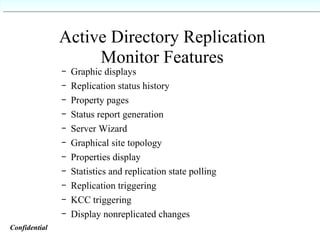
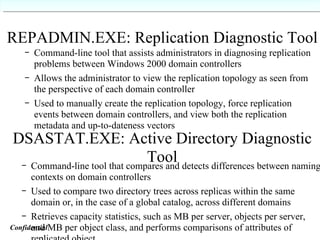
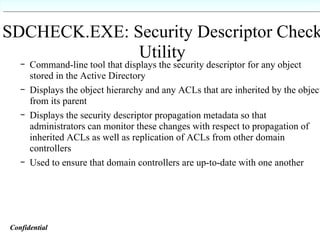
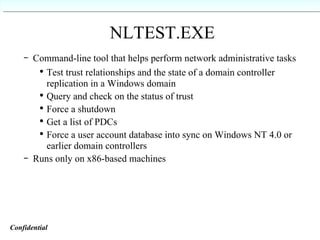
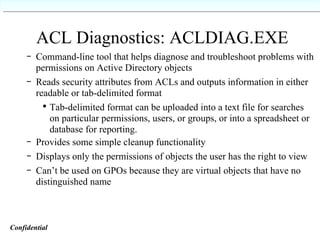
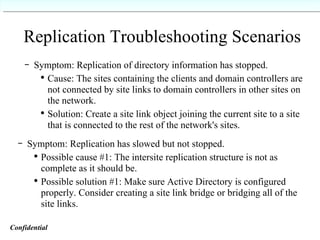
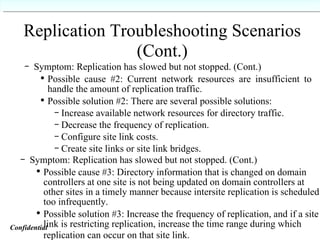
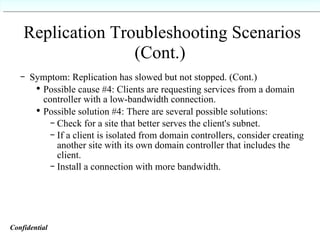
This document provides an overview of Active Directory, detailing its components, logical and physical structures, and administrative tasks. It explains the significance of objects, groups, and sites within Active Directory, along with the procedures for replication, installation, and role management. Additionally, it covers key concepts such as group types, site links, and operational roles critical for domain controllers.