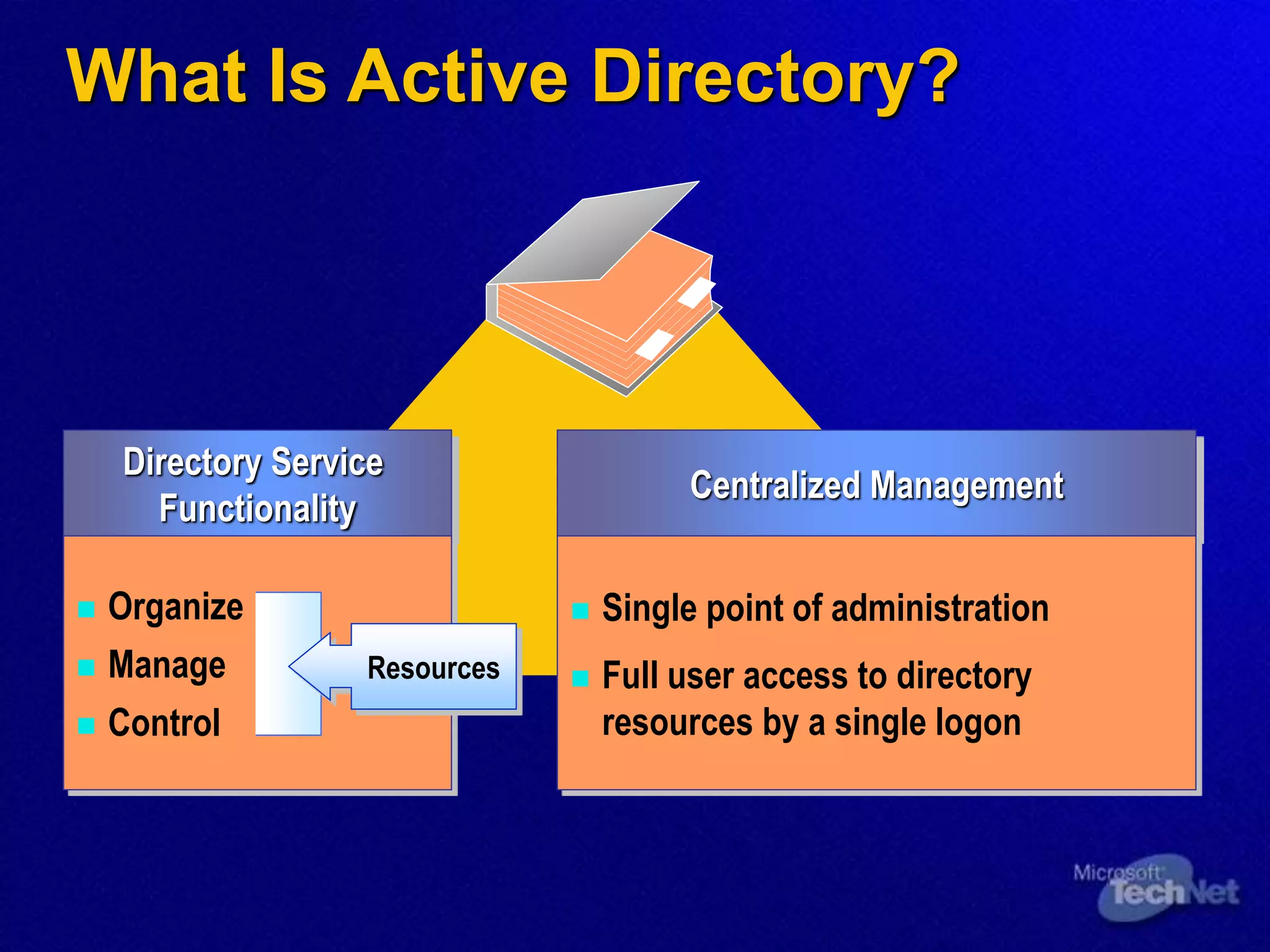
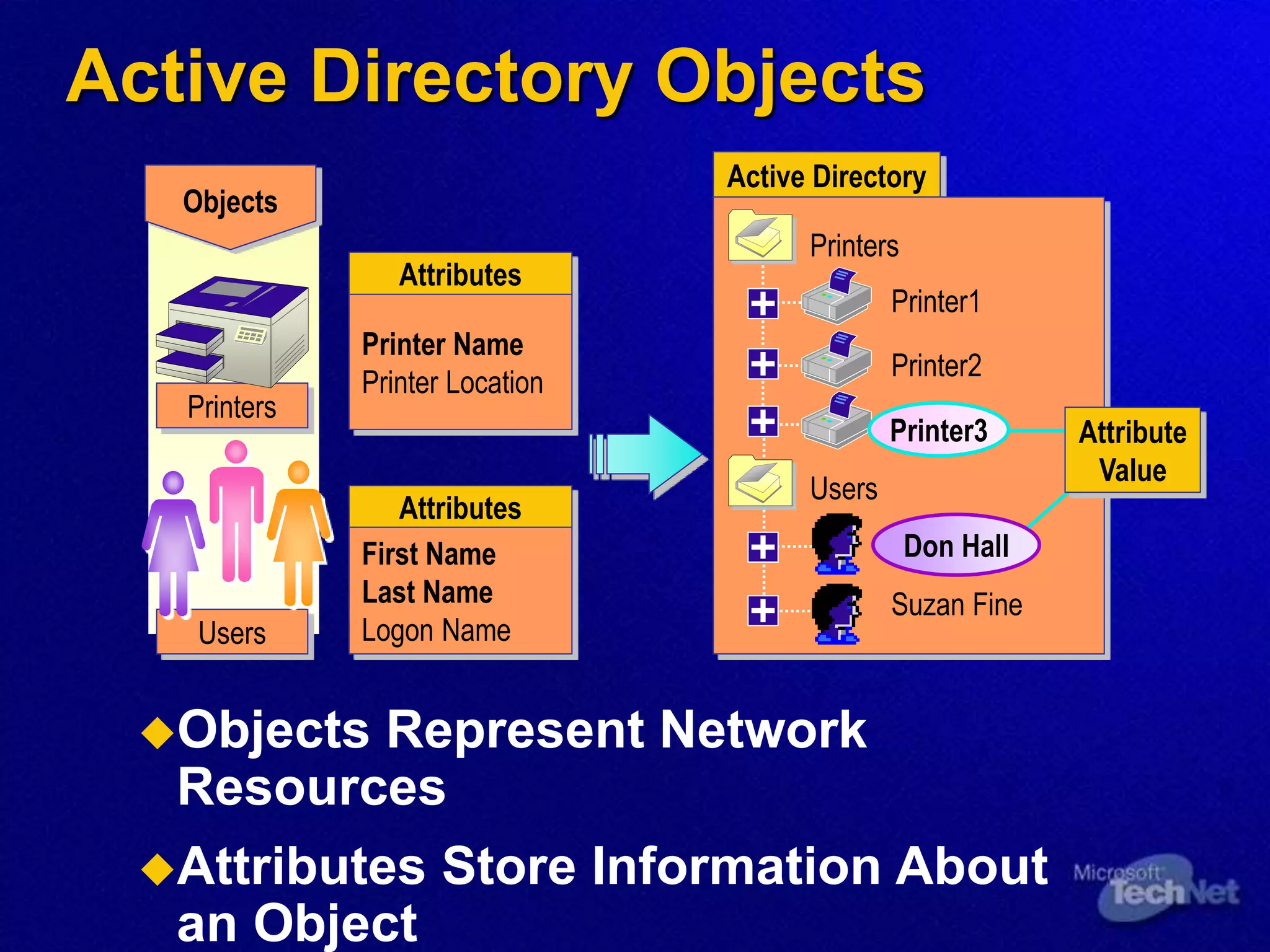
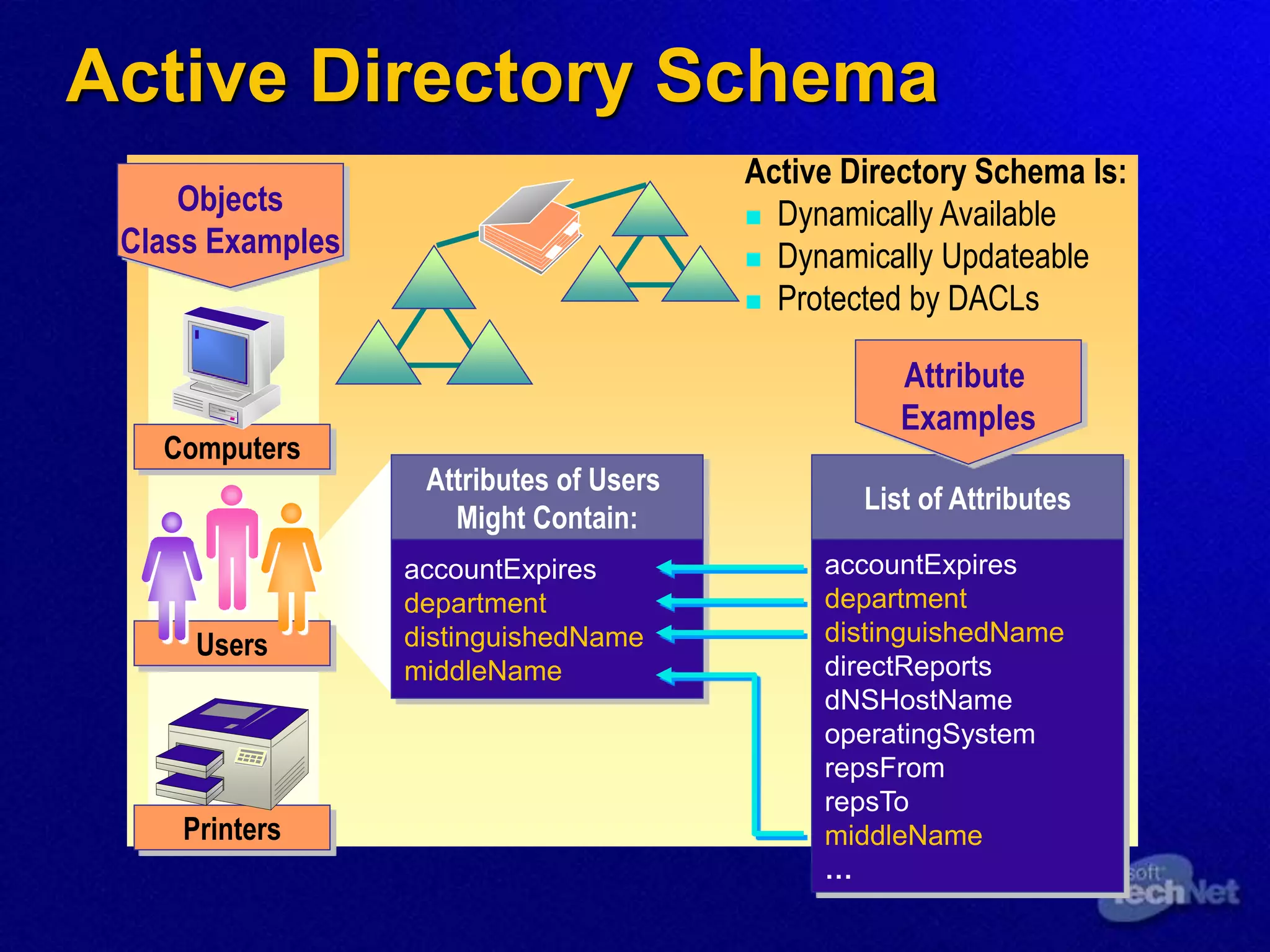
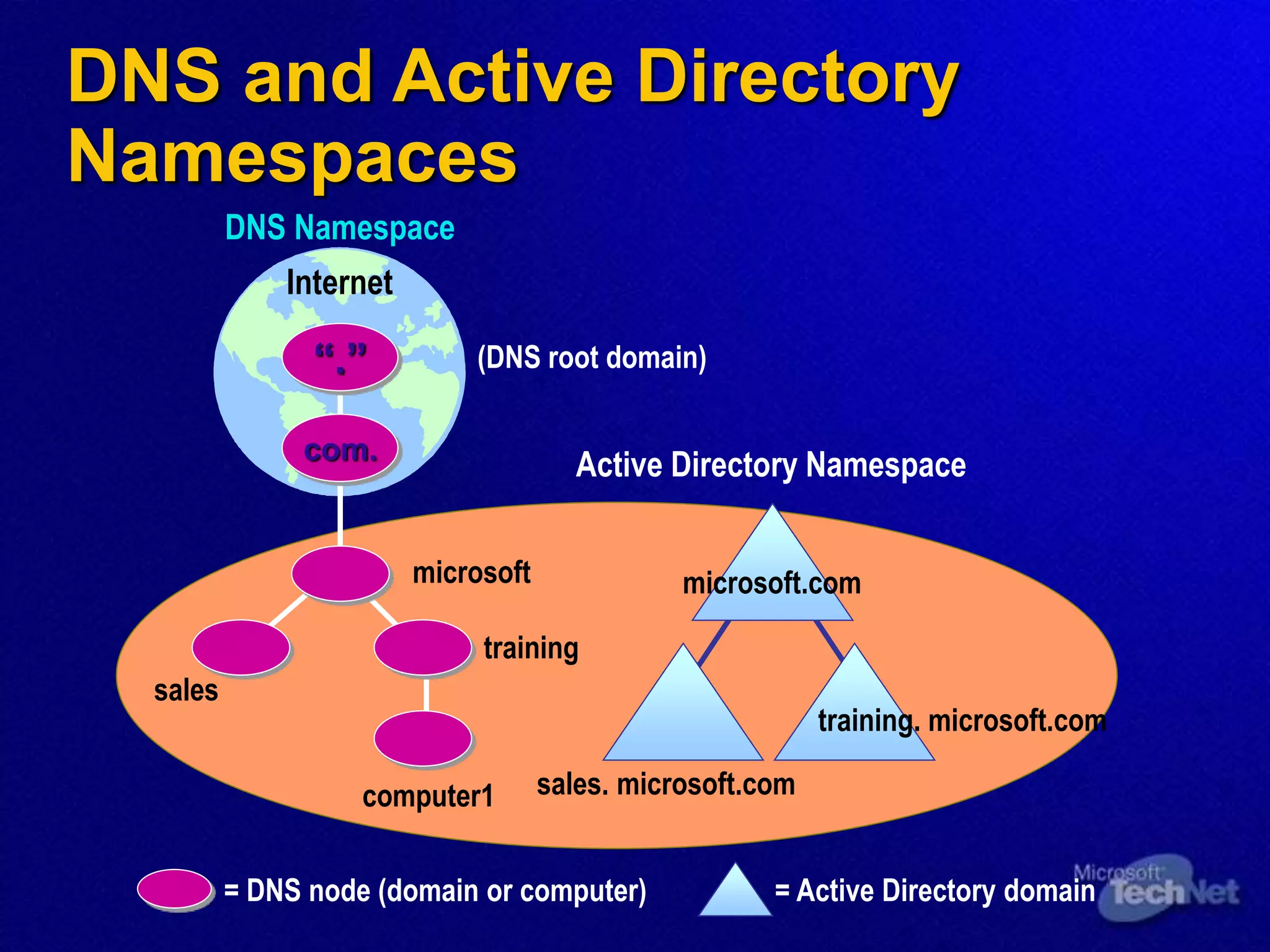
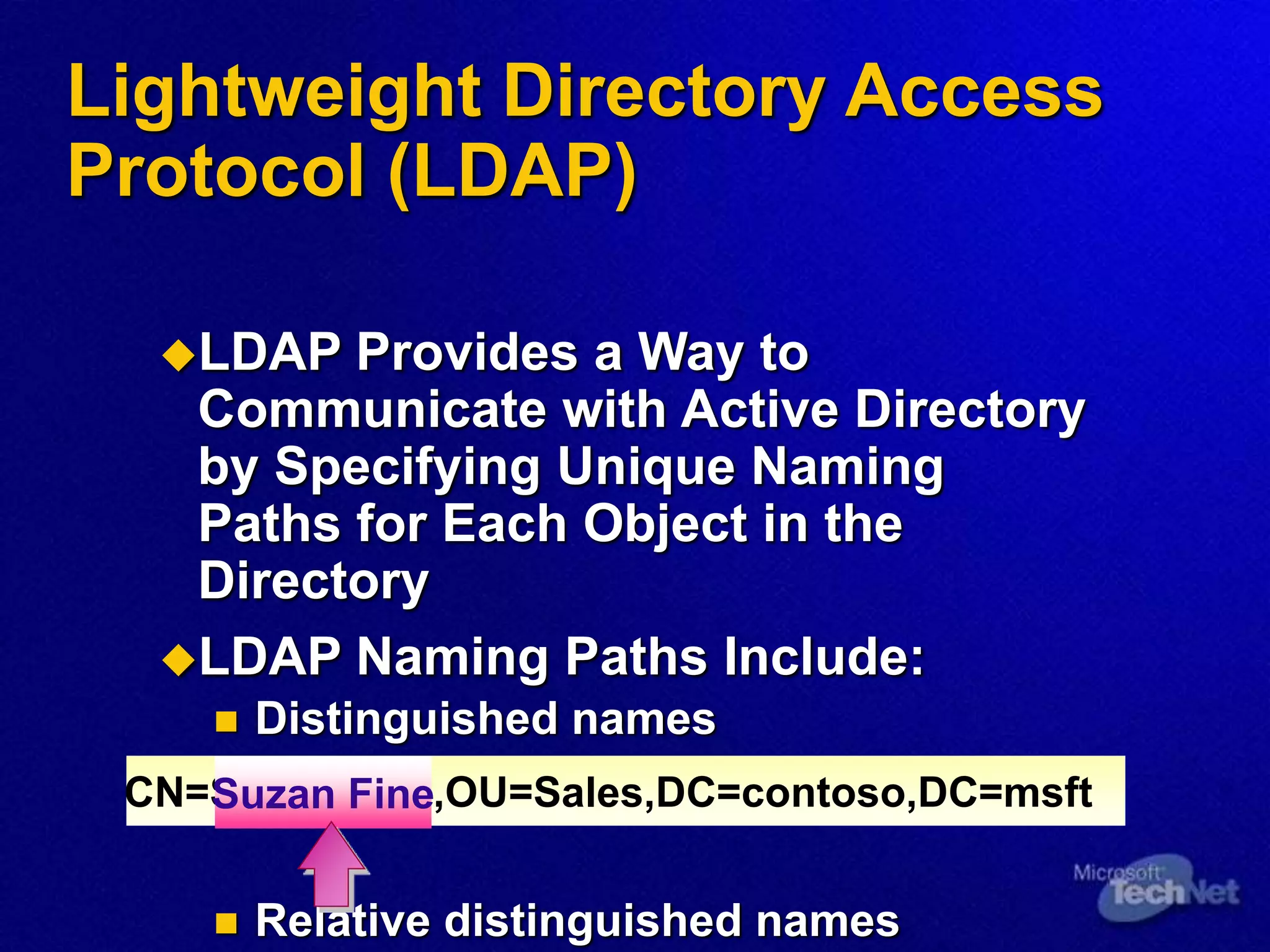
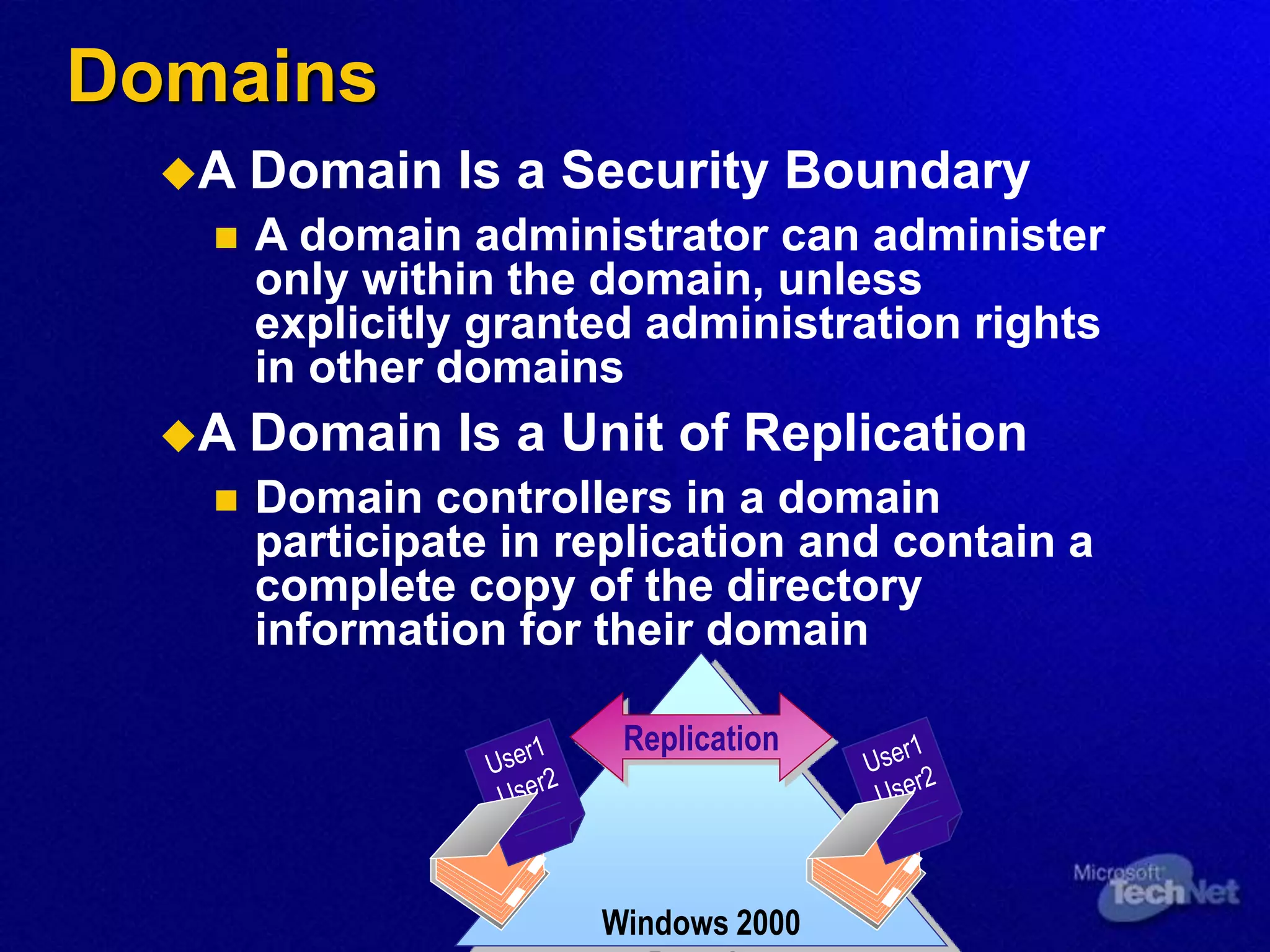
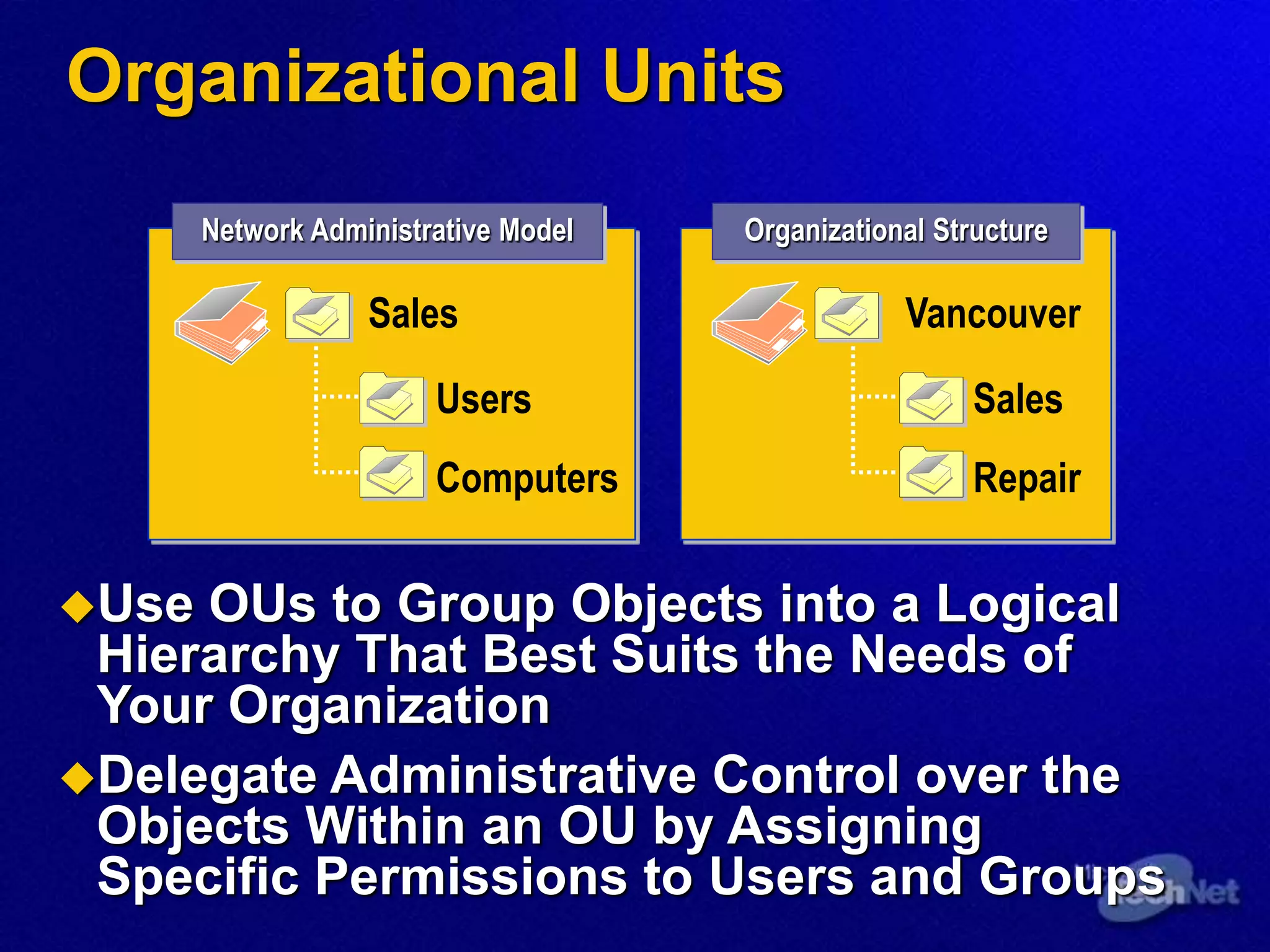
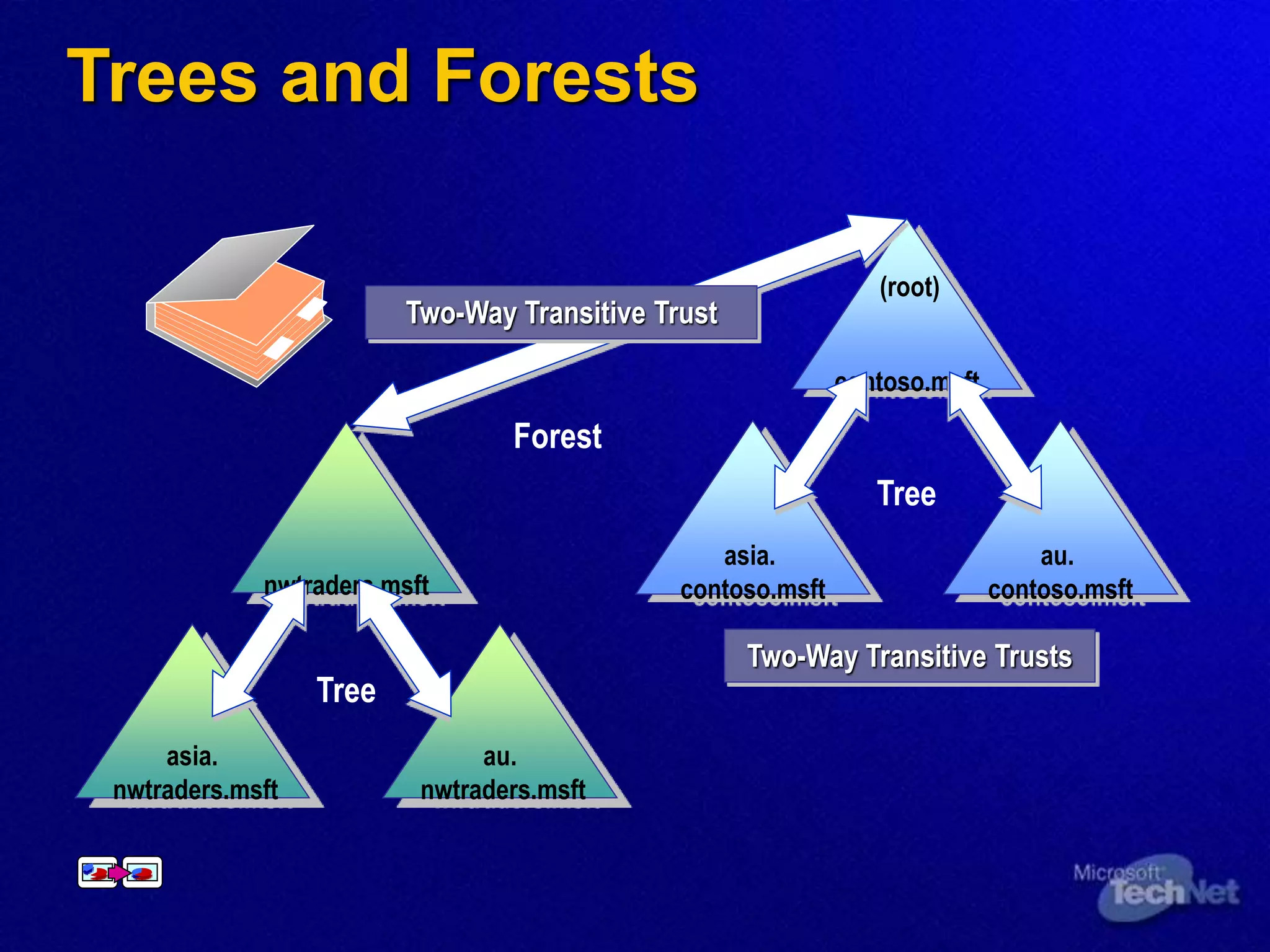
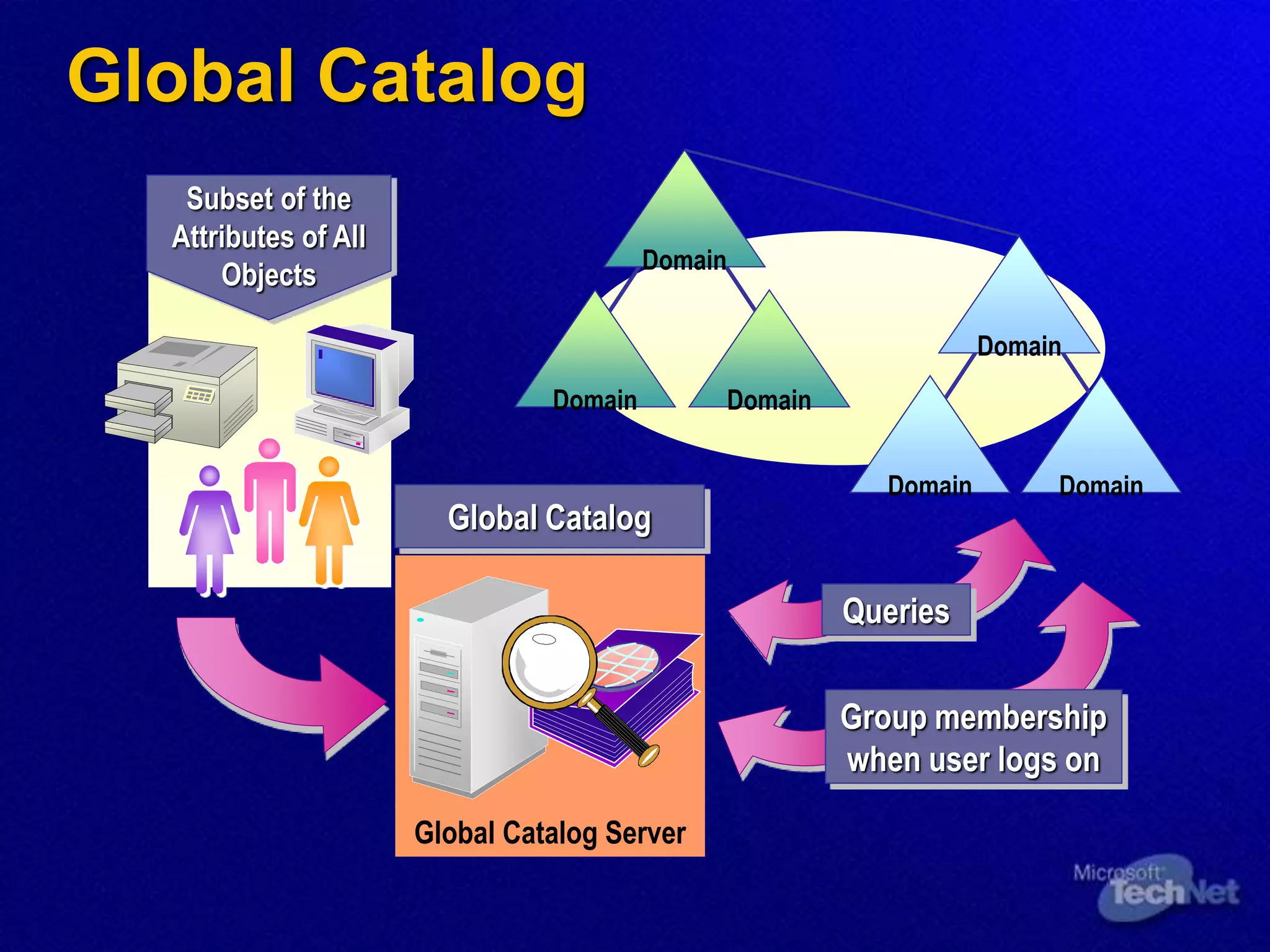
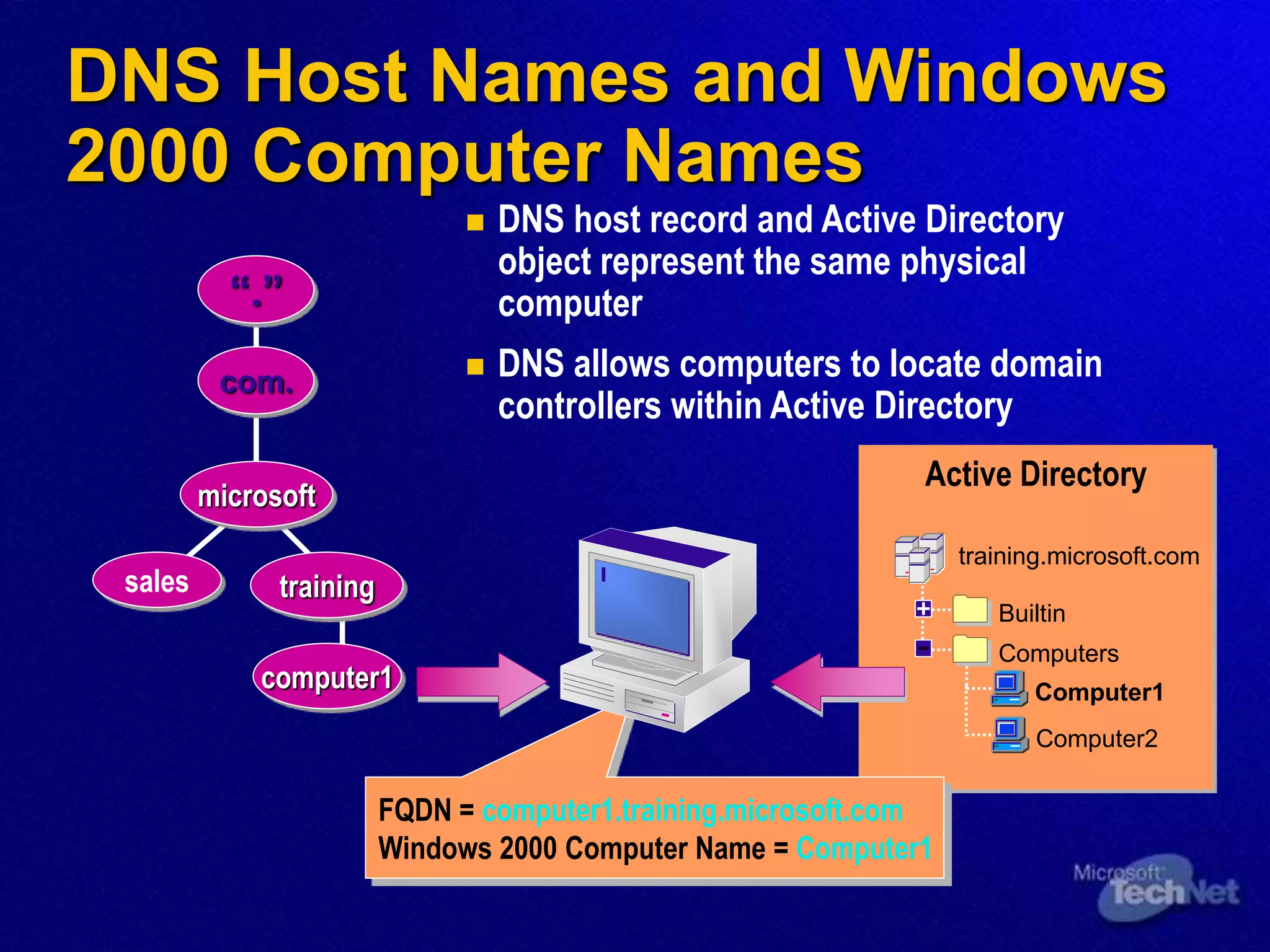
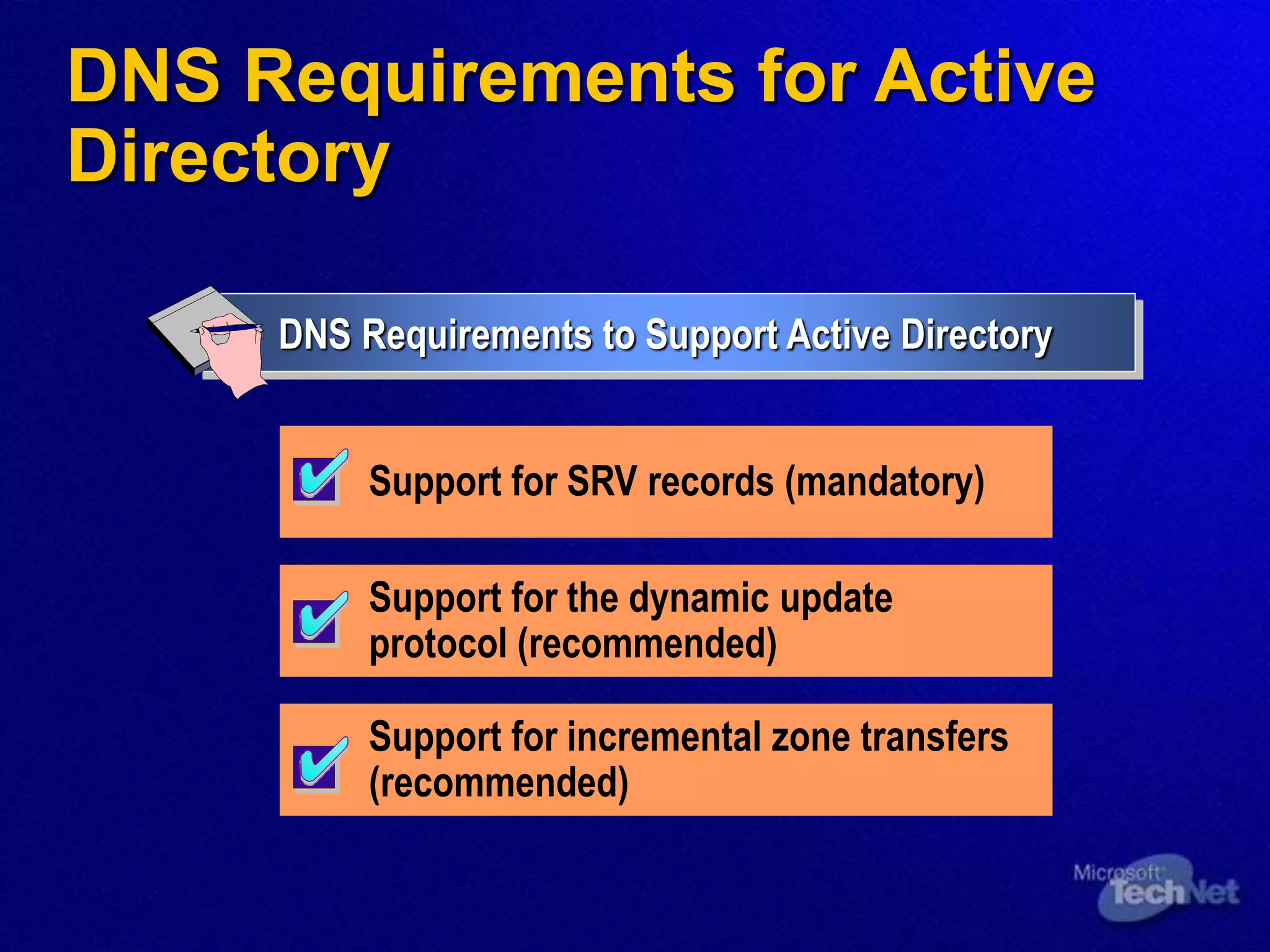
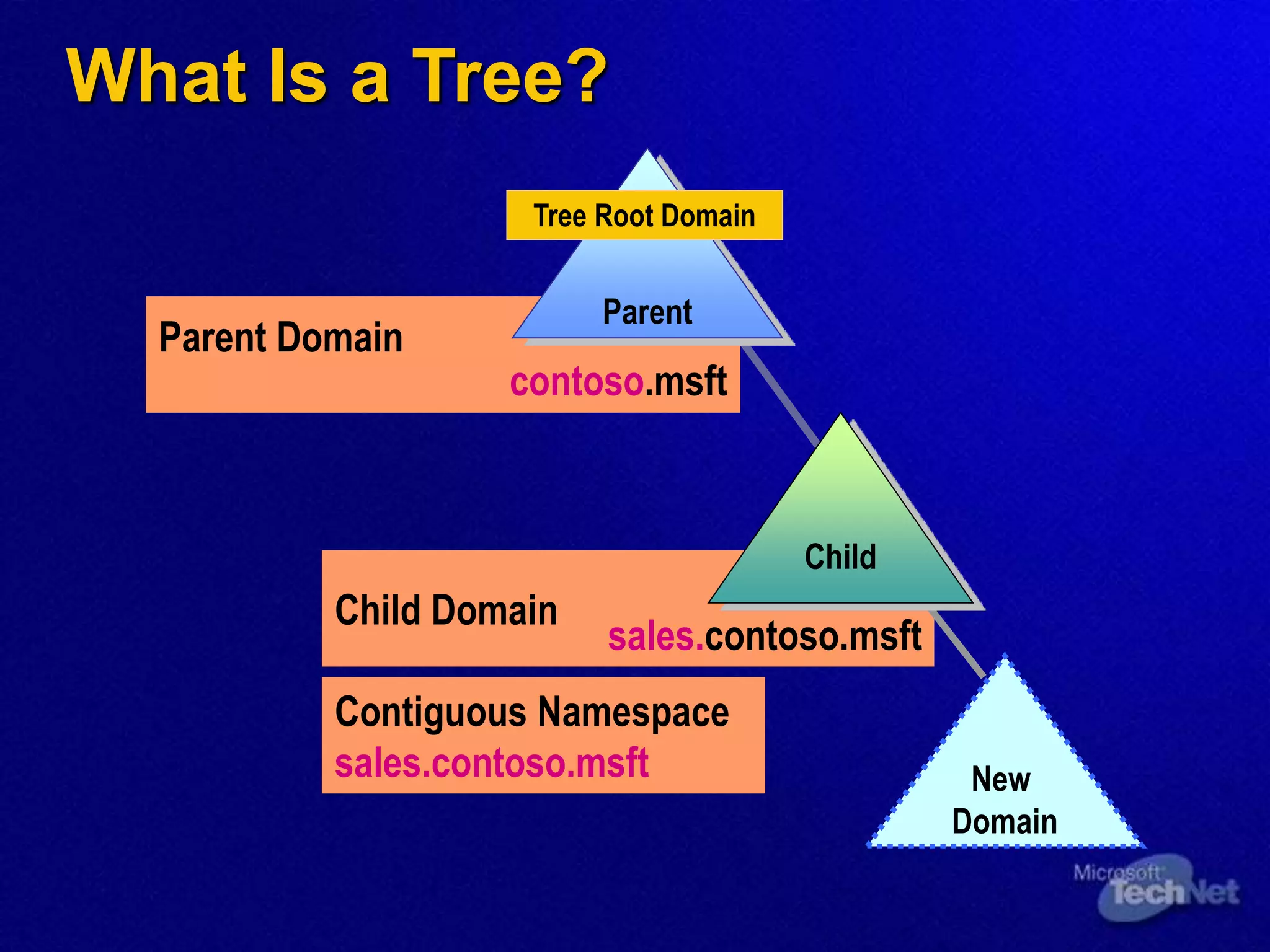
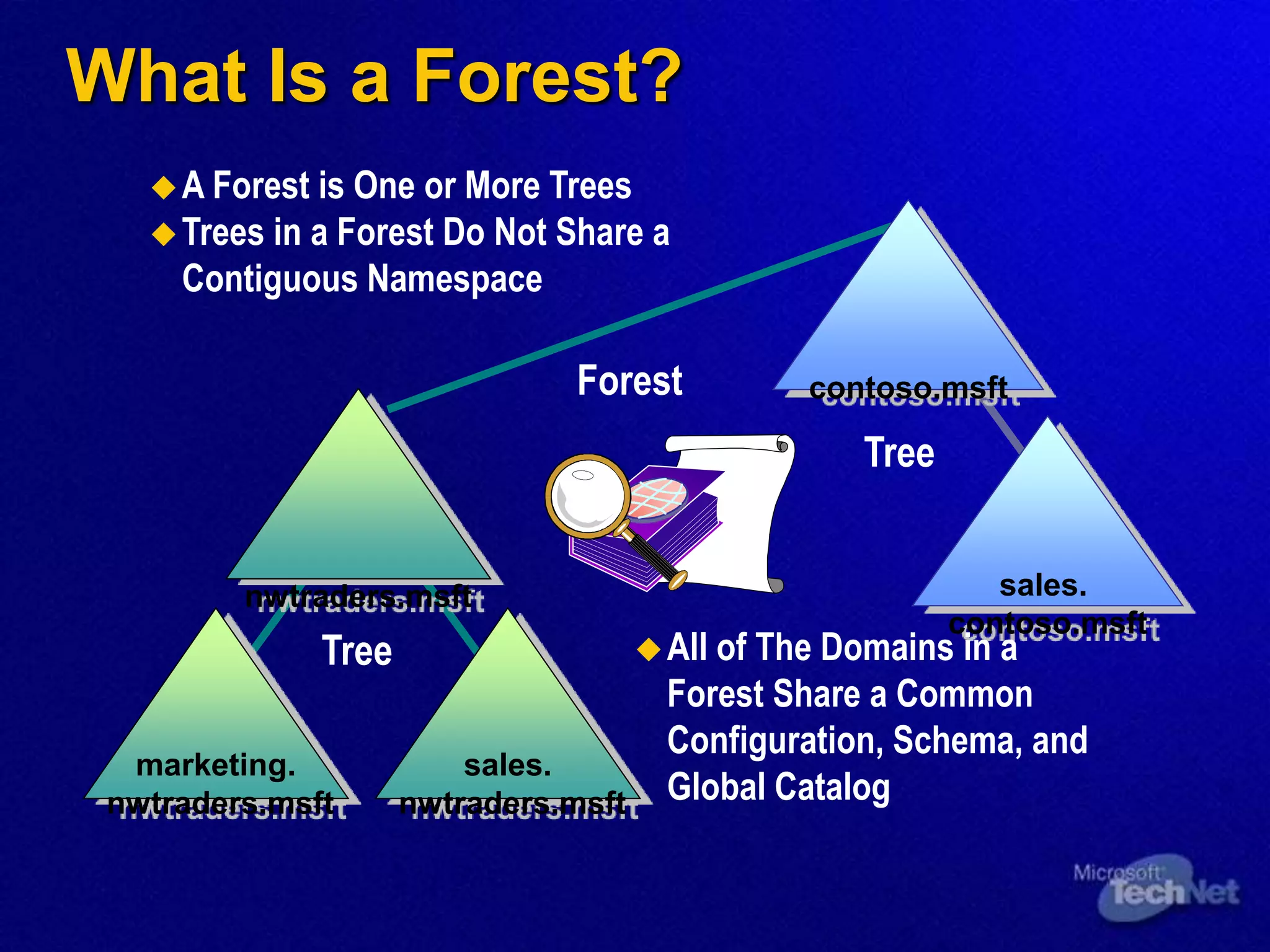
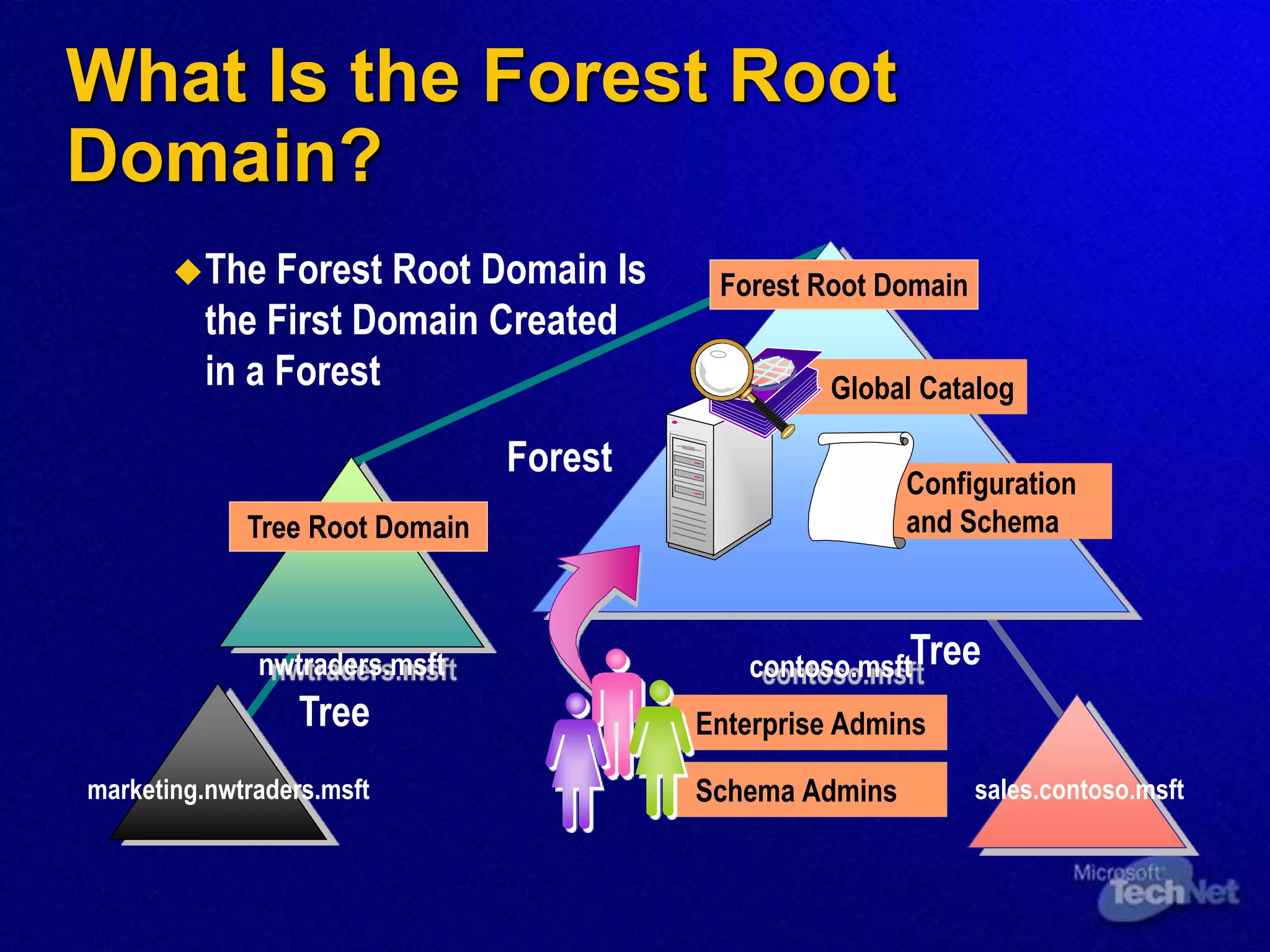
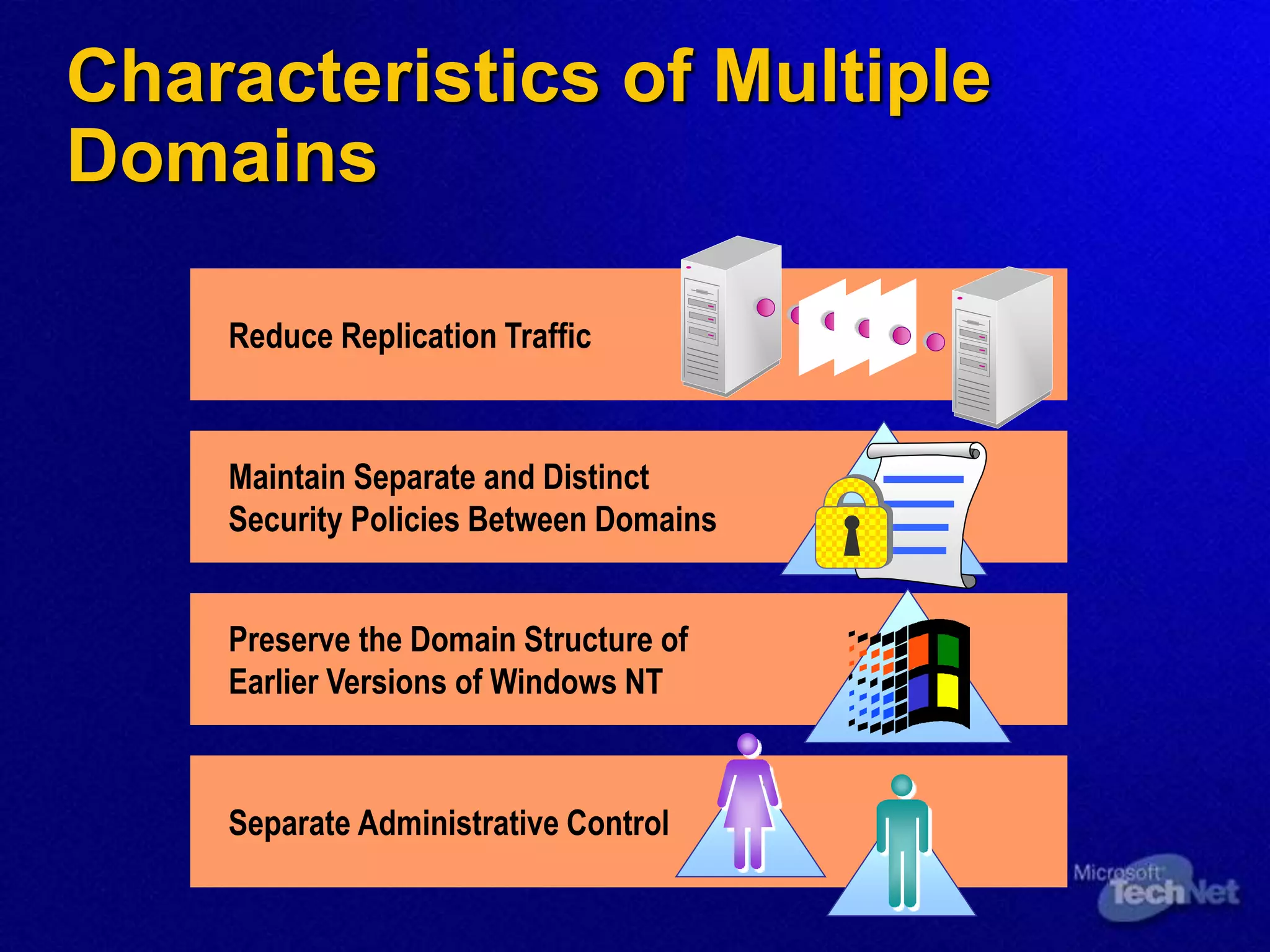
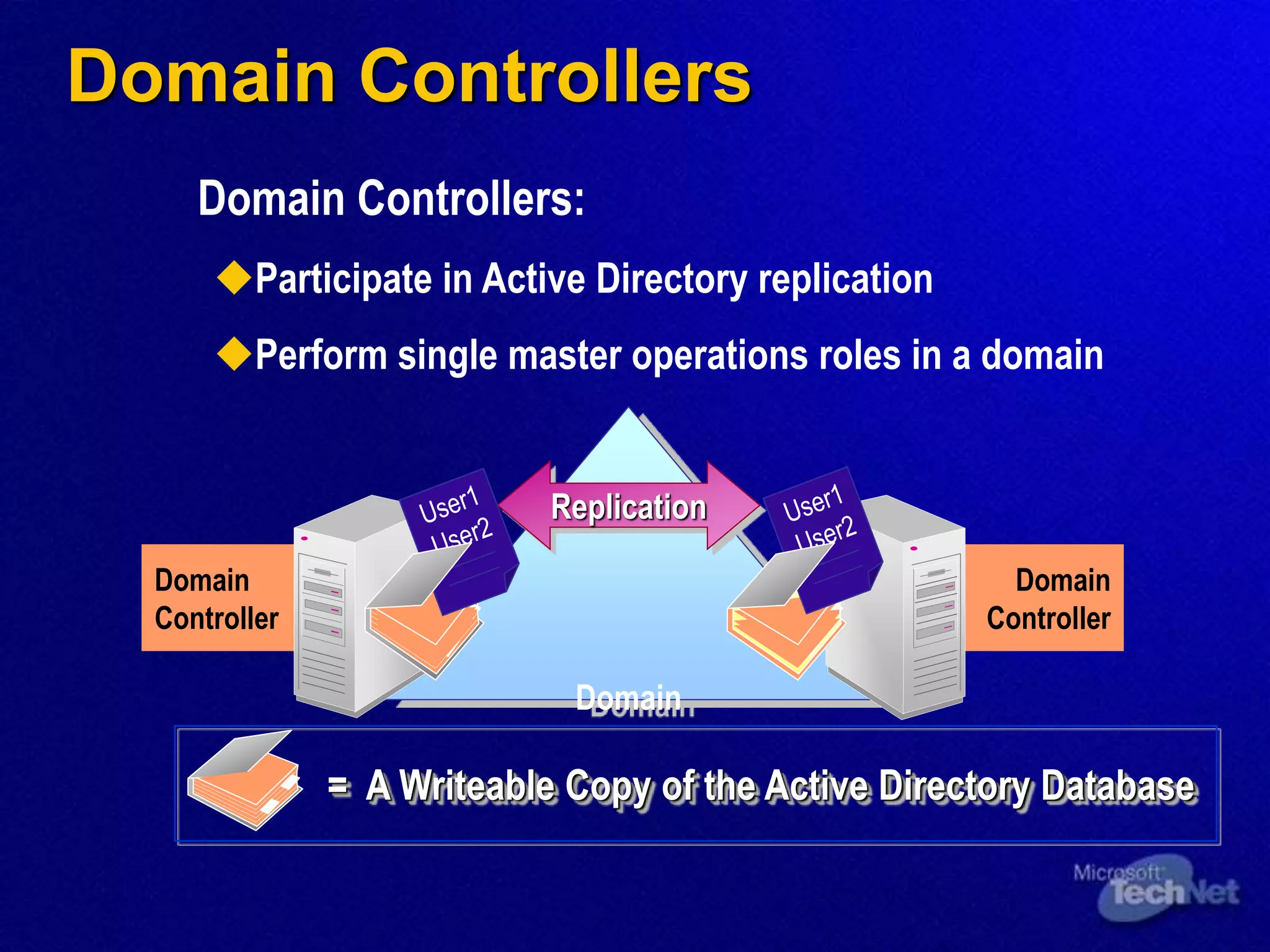
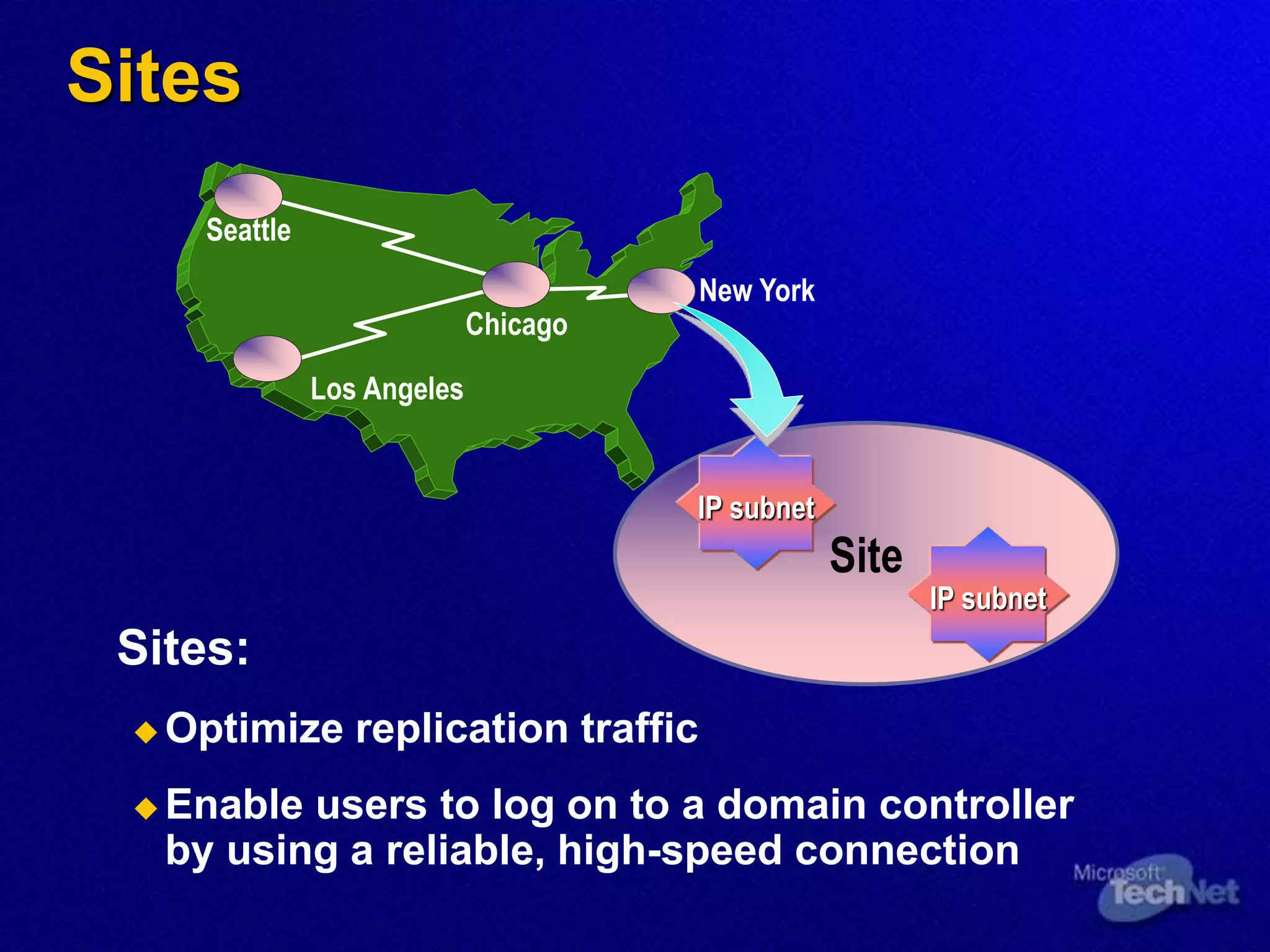
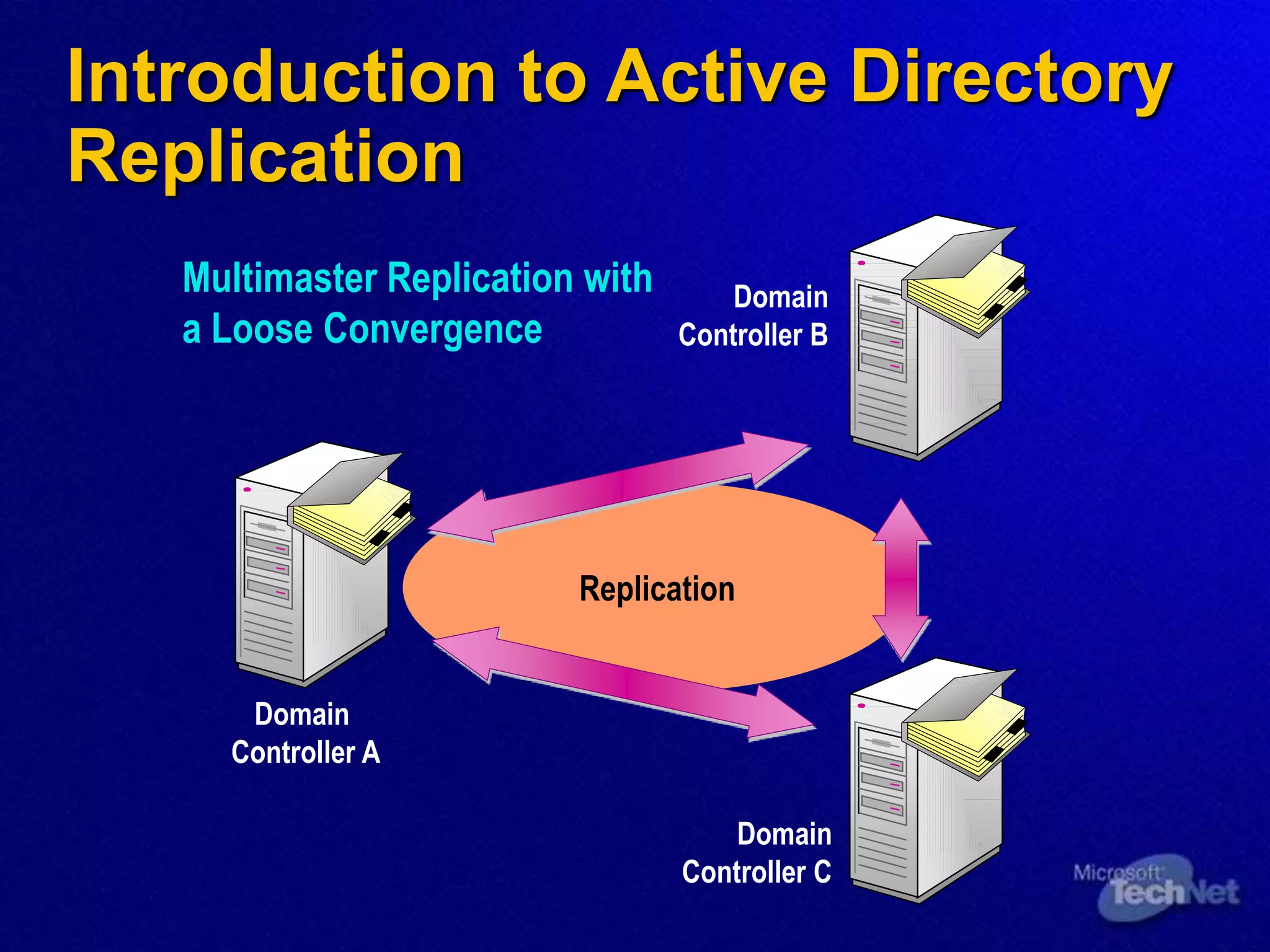
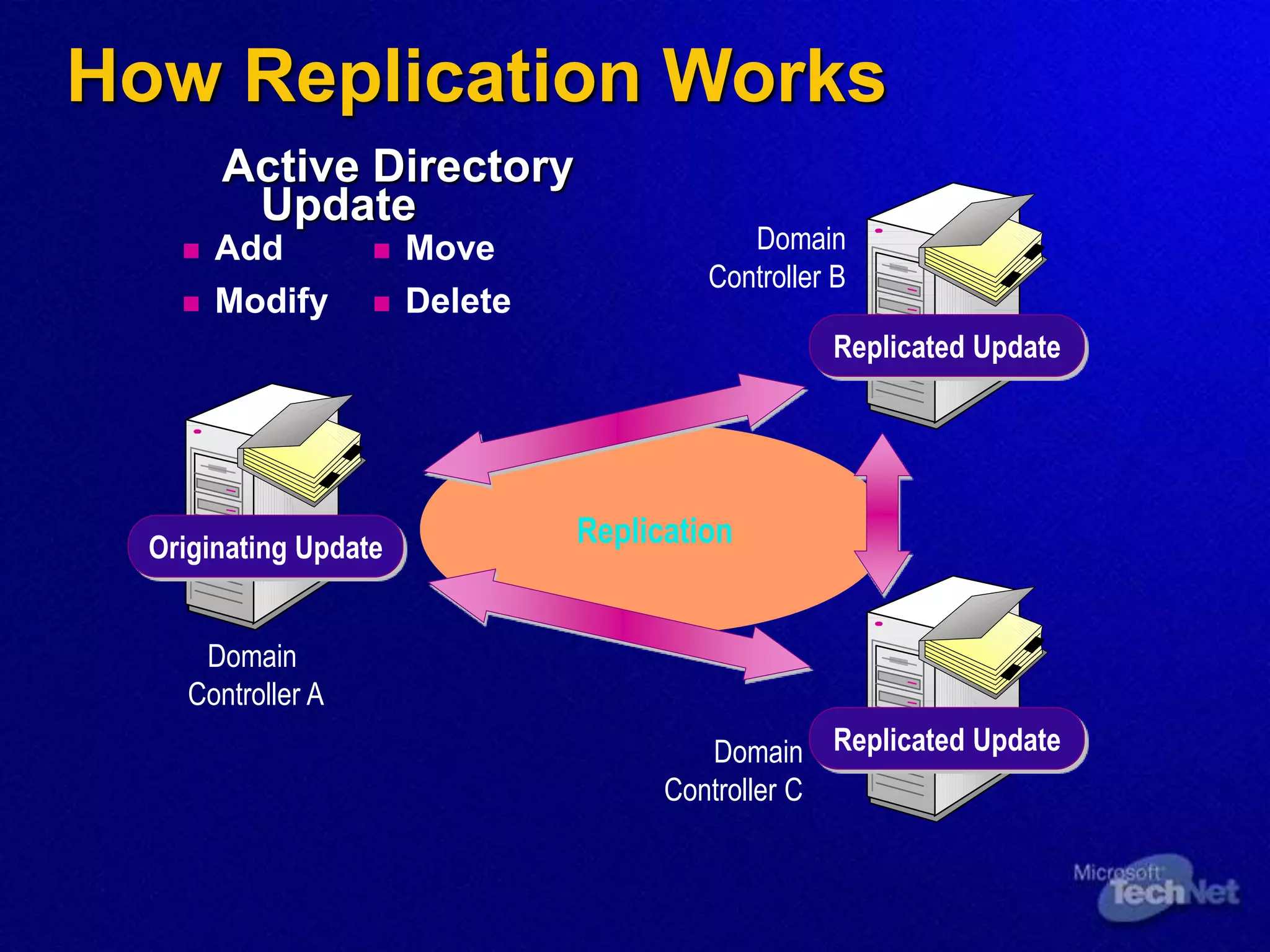
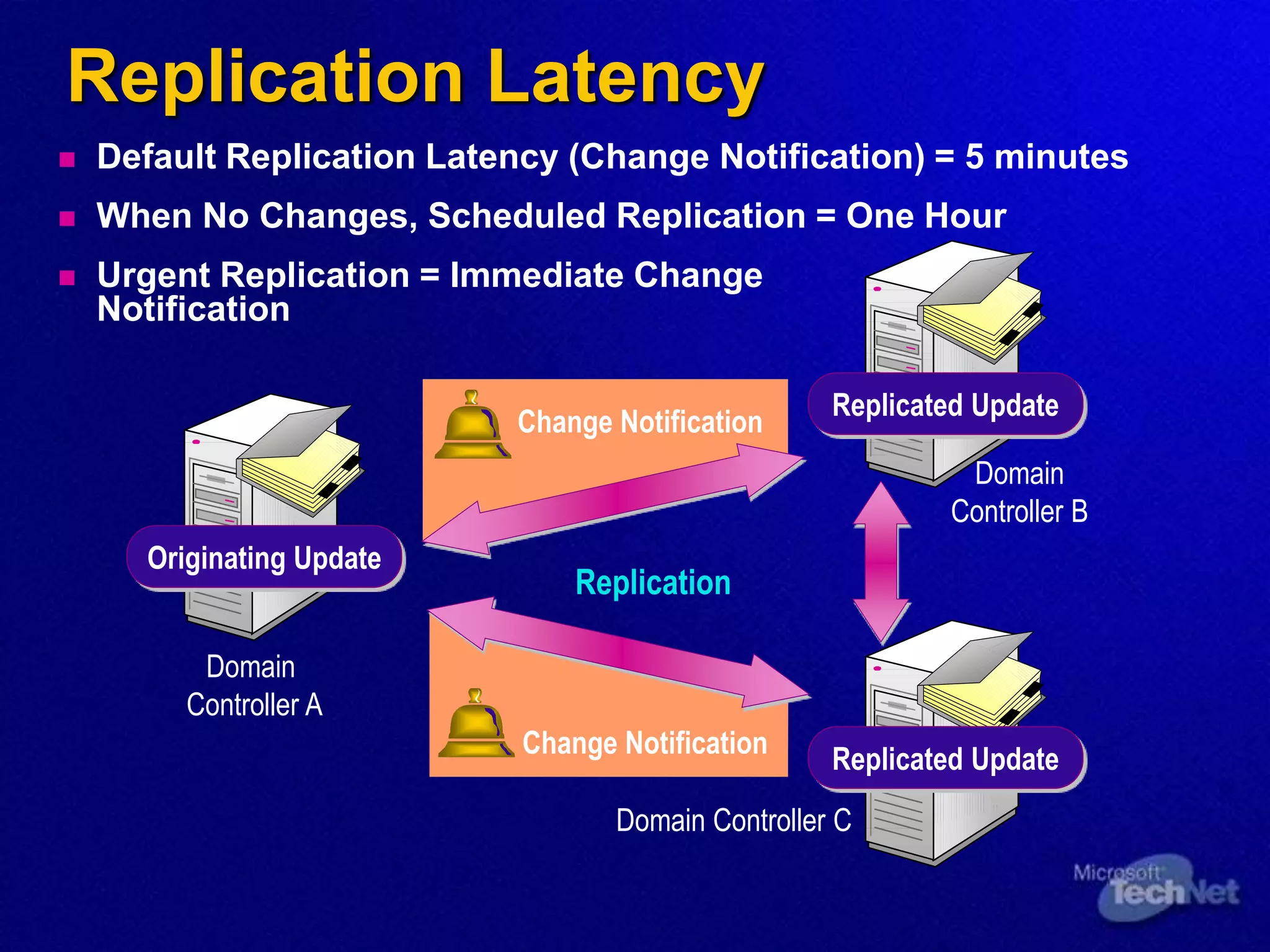
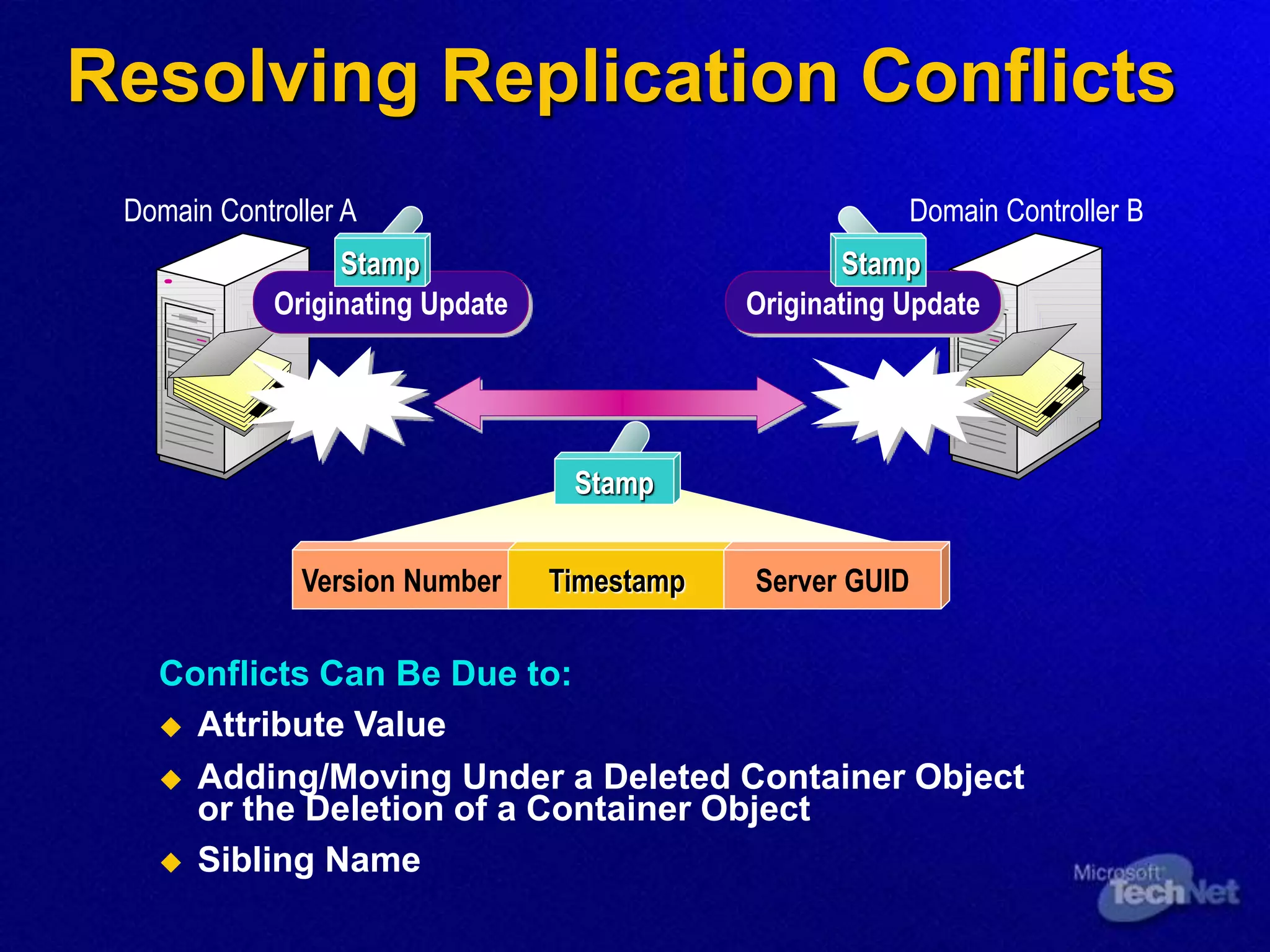
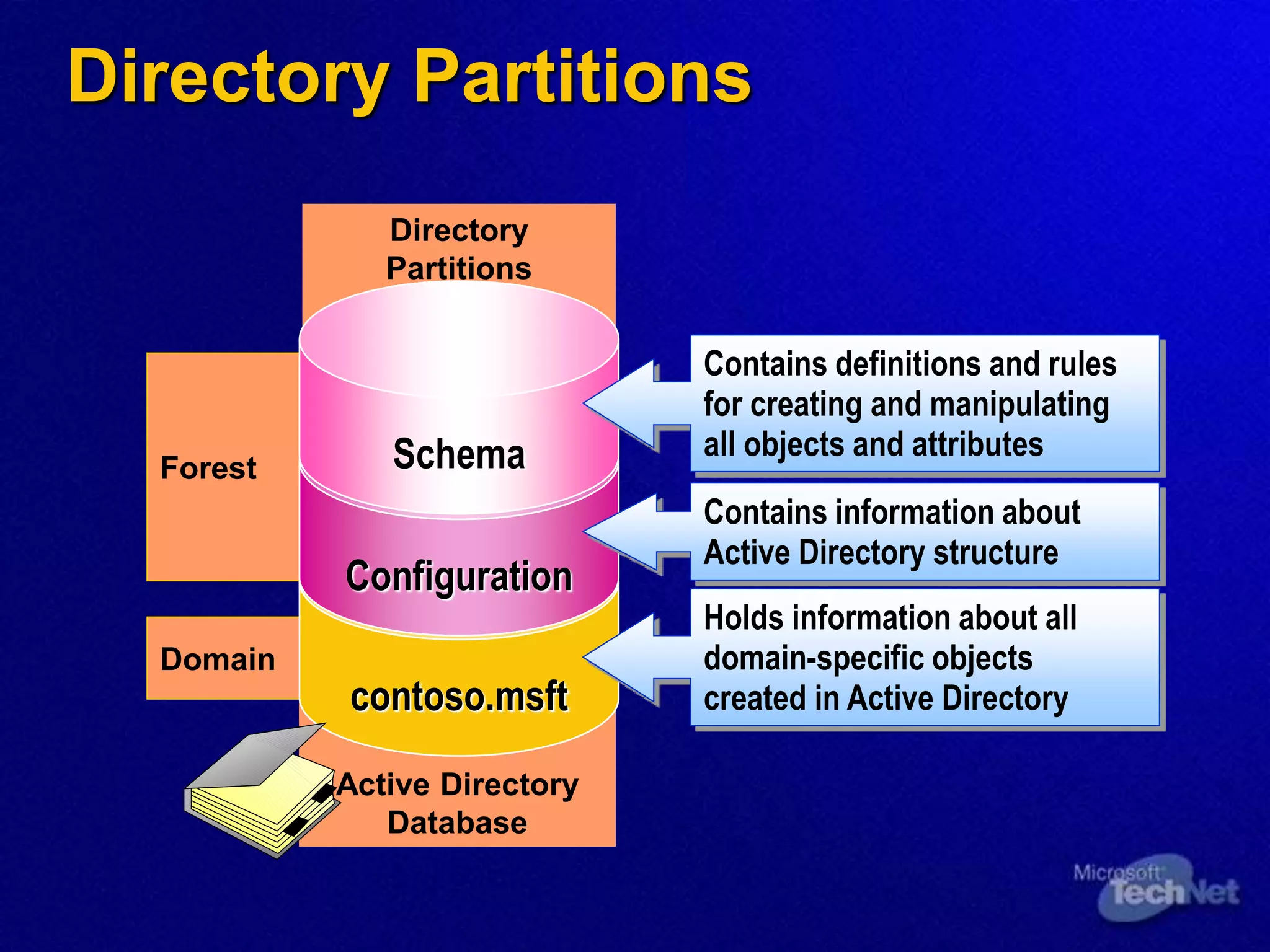
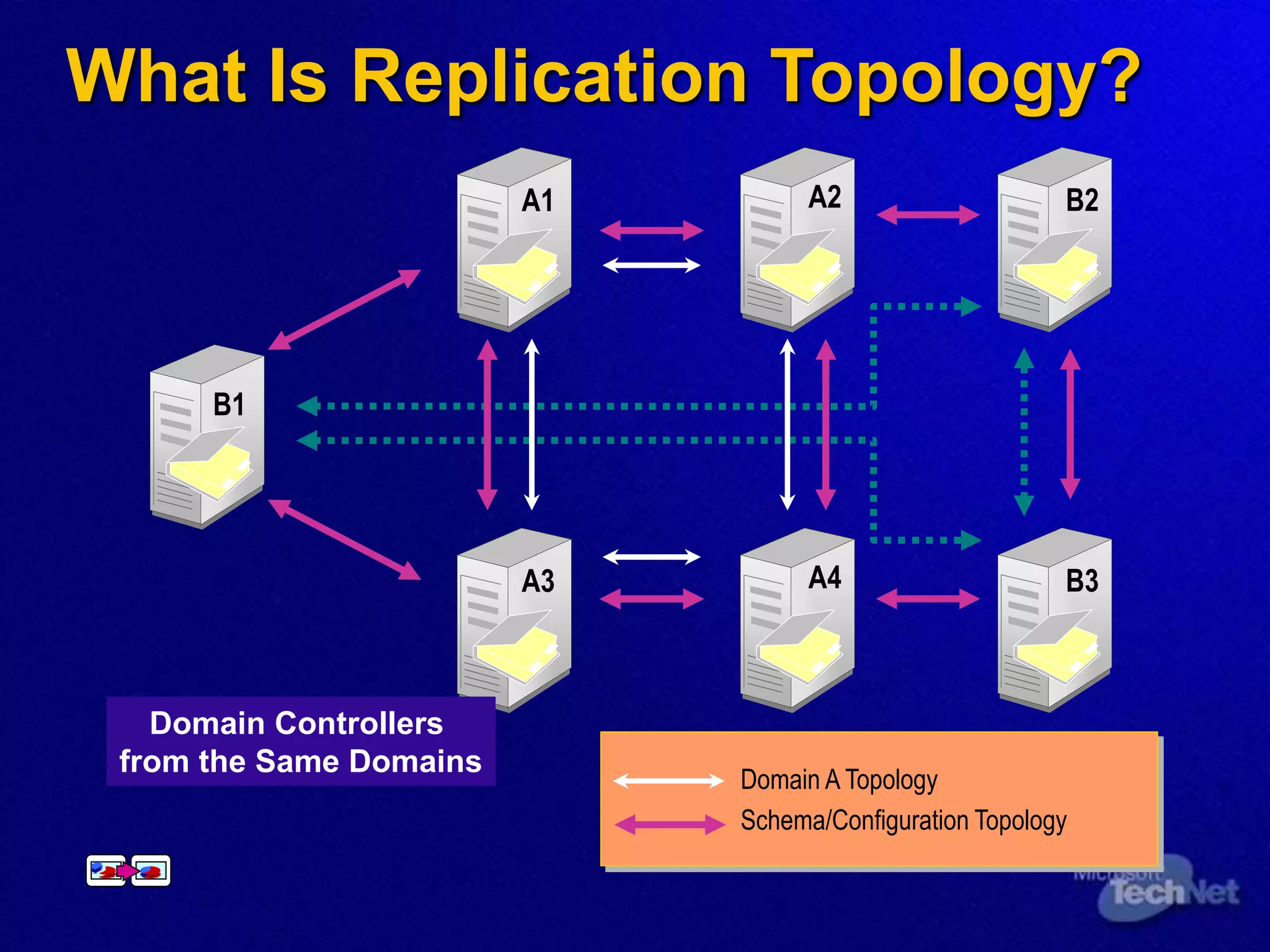
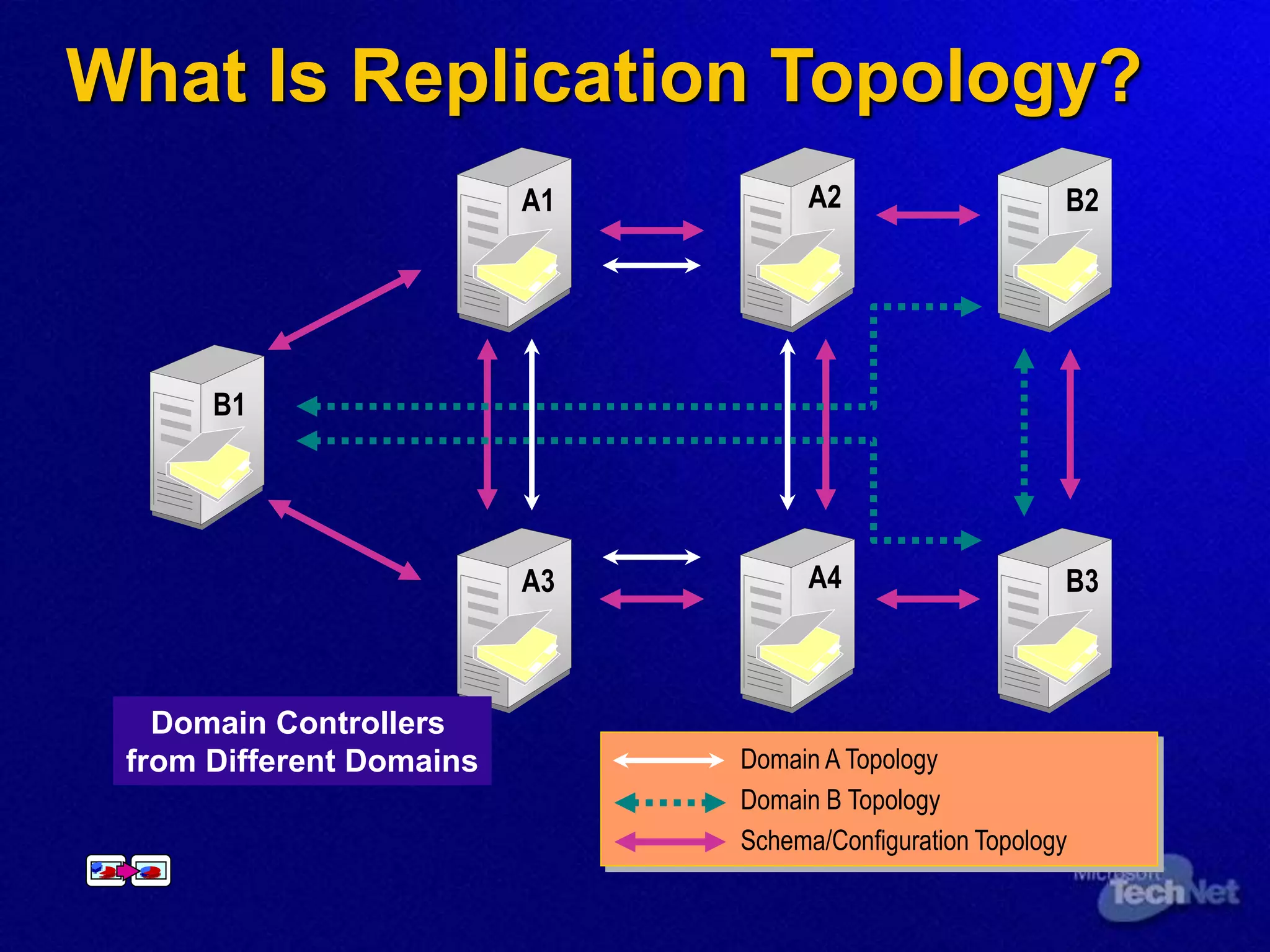
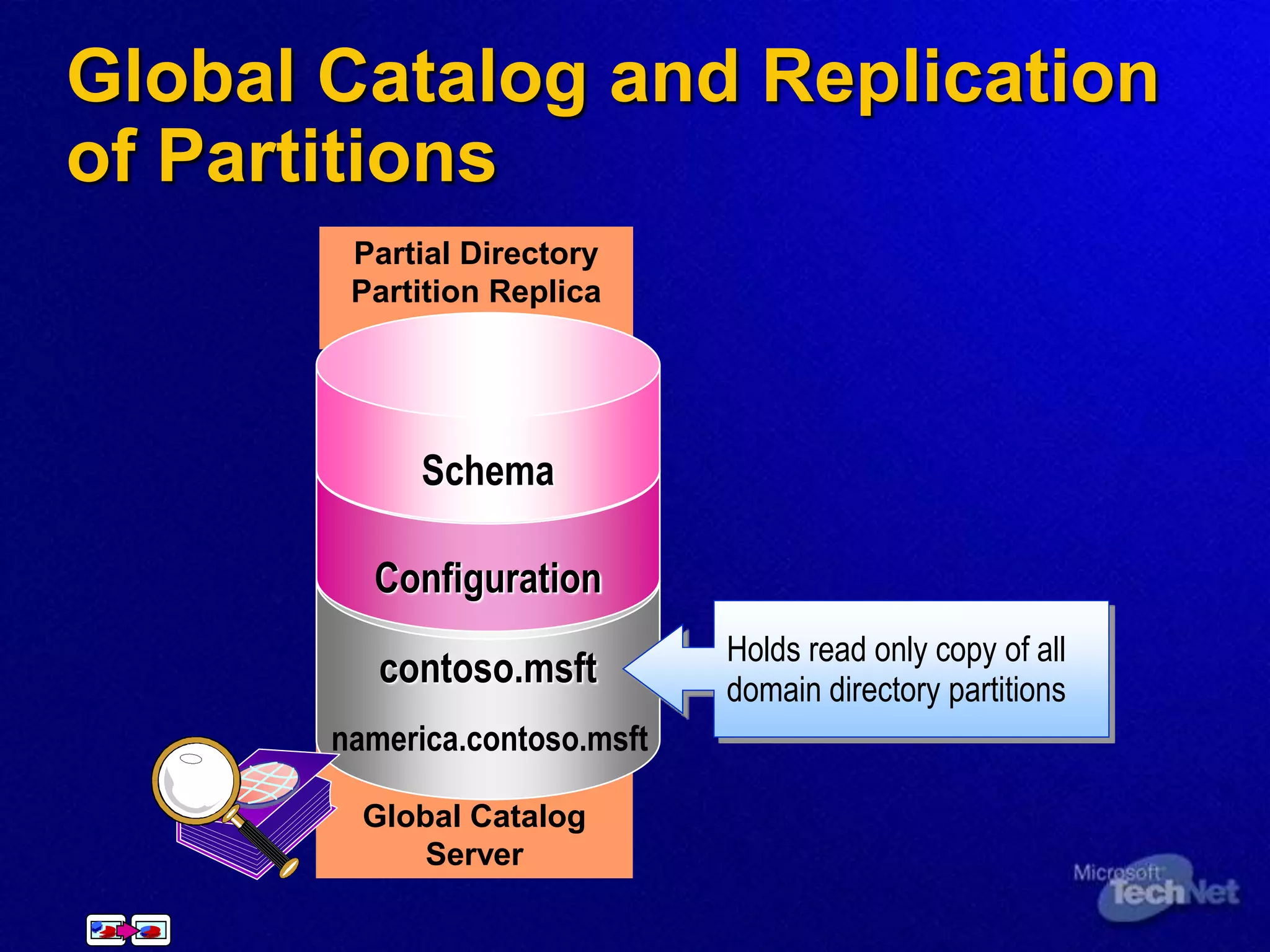
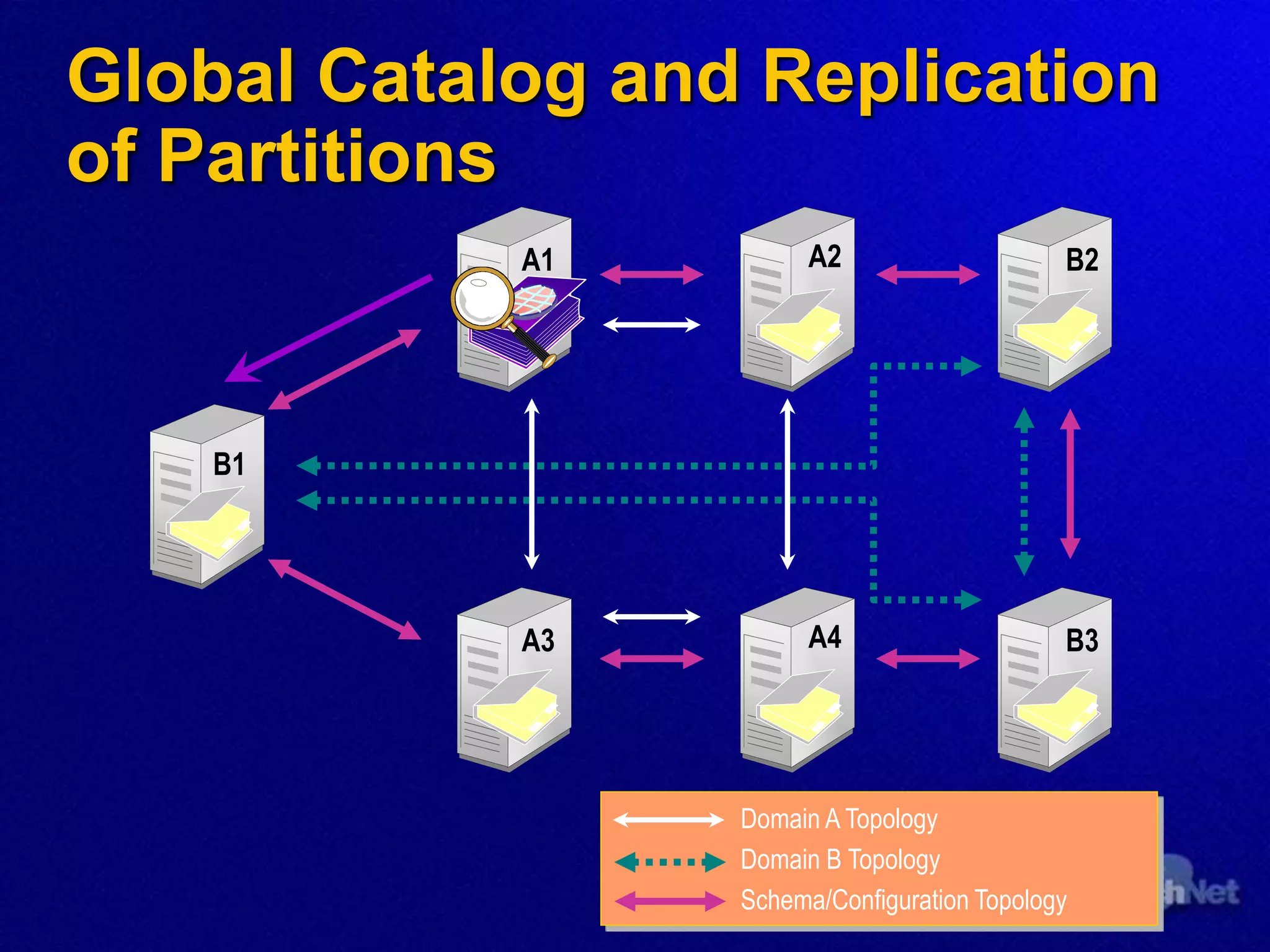
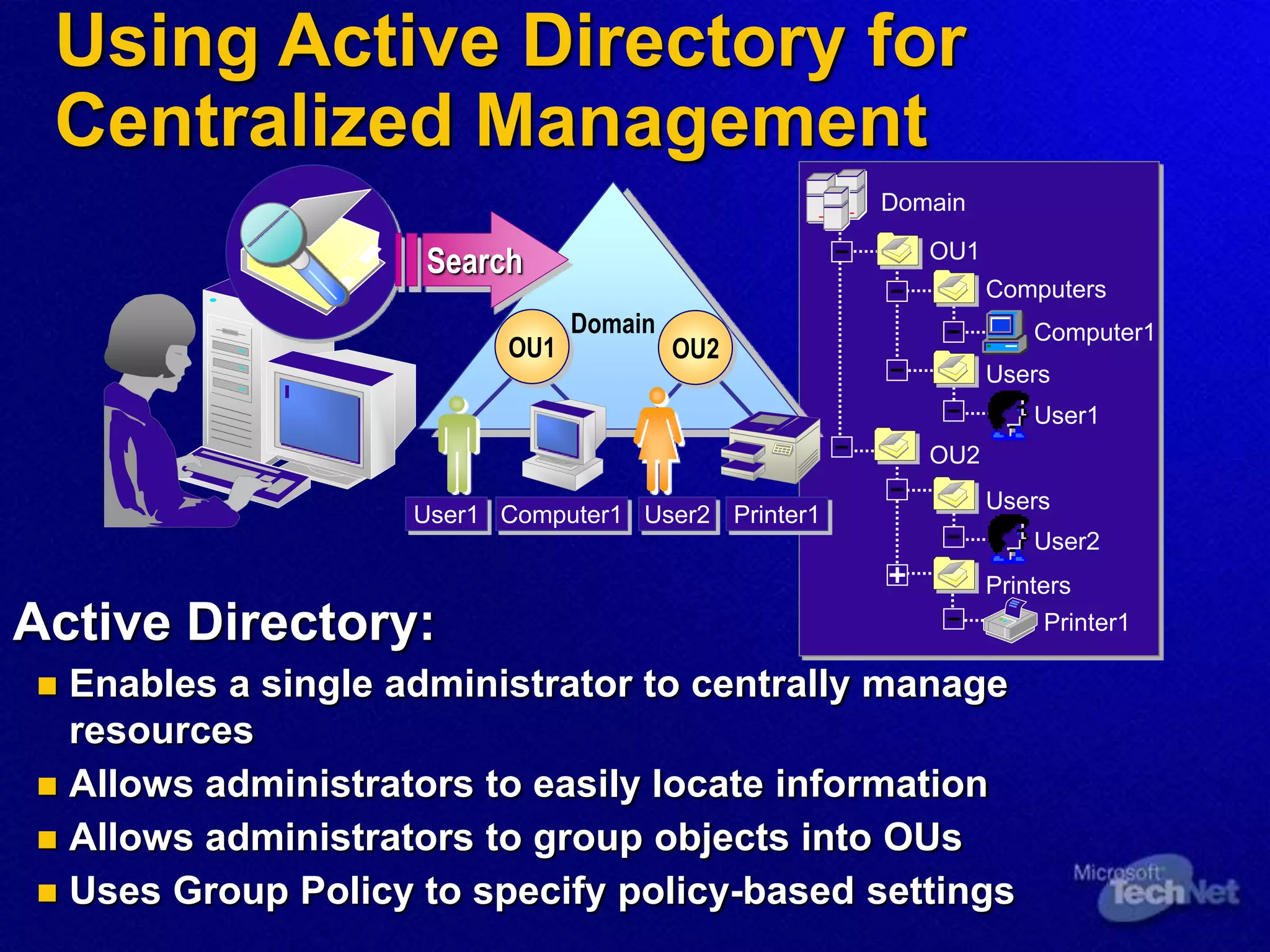
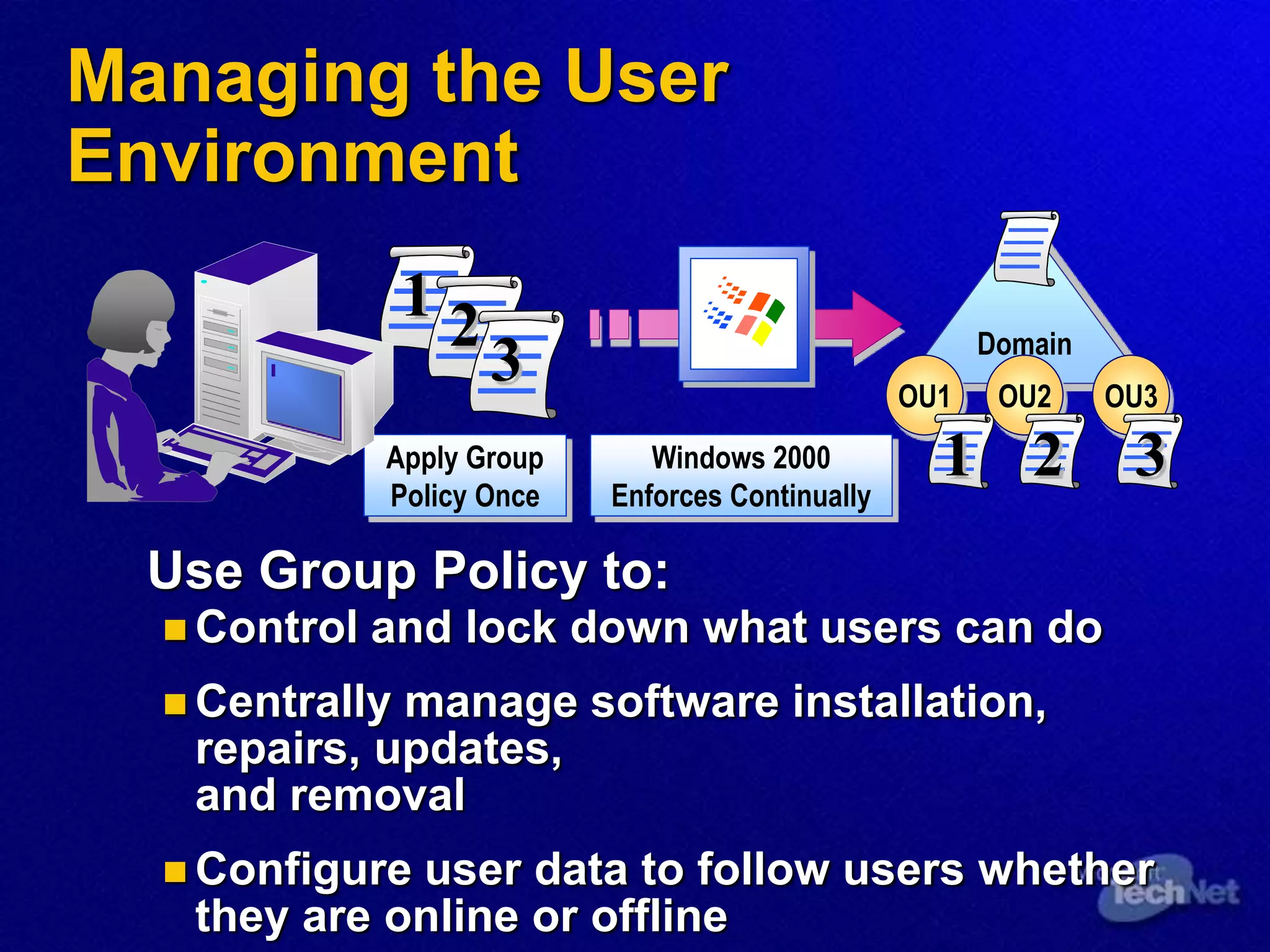
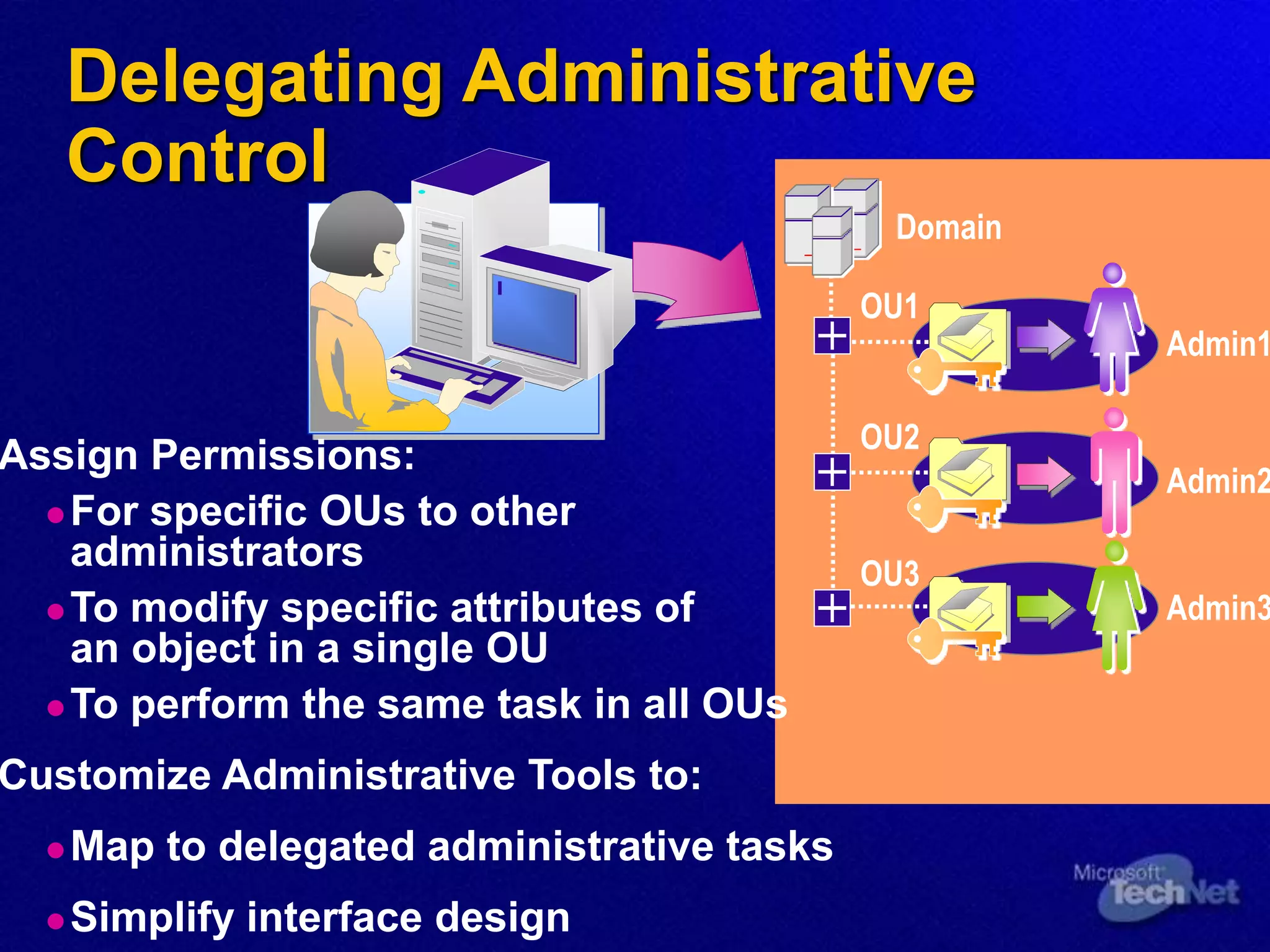
This document provides an overview of Active Directory, including its logical and physical structures, the role of DNS, and methods for administration. It describes how Active Directory organizes, manages and controls network resources through a centralized directory. Key components include domains, organizational units, replication between domain controllers, and use of Group Policy for centralized management of users and computers.