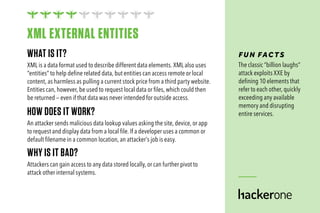
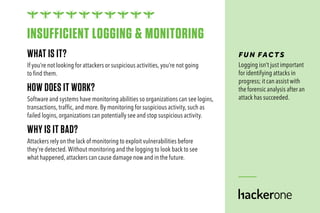
The document provides a reference guide to the OWASP Top 10 web security risks of 2017, detailing vulnerabilities such as injection flaws, broken authentication, sensitive data exposure, and more. It explains how attackers exploit these vulnerabilities and the potential consequences for affected systems. This serves as a crucial reminder for organizations to regularly assess and improve their security measures.