Troubleshooting vocab
•Download as PPTX, PDF•
1 like•361 views
dt vocab words
Report
Share
Report
Share
More Related Content
Similar to Troubleshooting vocab
Similar to Troubleshooting vocab (20)
Comparison of android and black berry forensic techniques

Comparison of android and black berry forensic techniques
More from Frya Lora
More from Frya Lora (20)
Recently uploaded
Model Call Girl in Bikash Puri Delhi reach out to us at 🔝9953056974🔝

Model Call Girl in Bikash Puri Delhi reach out to us at 🔝9953056974🔝9953056974 Low Rate Call Girls In Saket, Delhi NCR
“Oh GOSH! Reflecting on Hackteria's Collaborative Practices in a Global Do-It...

“Oh GOSH! Reflecting on Hackteria's Collaborative Practices in a Global Do-It...Marc Dusseiller Dusjagr
KSHARA STURA .pptx---KSHARA KARMA THERAPY (CAUSTIC THERAPY)————IMP.OF KSHARA ...

KSHARA STURA .pptx---KSHARA KARMA THERAPY (CAUSTIC THERAPY)————IMP.OF KSHARA ...M56BOOKSTORE PRODUCT/SERVICE
Organic Name Reactions for the students and aspirants of Chemistry12th.pptx

Organic Name Reactions for the students and aspirants of Chemistry12th.pptxVS Mahajan Coaching Centre
9953330565 Low Rate Call Girls In Rohini Delhi NCR

9953330565 Low Rate Call Girls In Rohini Delhi NCR9953056974 Low Rate Call Girls In Saket, Delhi NCR
Recently uploaded (20)
Introduction to ArtificiaI Intelligence in Higher Education

Introduction to ArtificiaI Intelligence in Higher Education
Incoming and Outgoing Shipments in 1 STEP Using Odoo 17

Incoming and Outgoing Shipments in 1 STEP Using Odoo 17
Model Call Girl in Bikash Puri Delhi reach out to us at 🔝9953056974🔝

Model Call Girl in Bikash Puri Delhi reach out to us at 🔝9953056974🔝
“Oh GOSH! Reflecting on Hackteria's Collaborative Practices in a Global Do-It...

“Oh GOSH! Reflecting on Hackteria's Collaborative Practices in a Global Do-It...
KSHARA STURA .pptx---KSHARA KARMA THERAPY (CAUSTIC THERAPY)————IMP.OF KSHARA ...

KSHARA STURA .pptx---KSHARA KARMA THERAPY (CAUSTIC THERAPY)————IMP.OF KSHARA ...
Organic Name Reactions for the students and aspirants of Chemistry12th.pptx

Organic Name Reactions for the students and aspirants of Chemistry12th.pptx
Enzyme, Pharmaceutical Aids, Miscellaneous Last Part of Chapter no 5th.pdf

Enzyme, Pharmaceutical Aids, Miscellaneous Last Part of Chapter no 5th.pdf
Framing an Appropriate Research Question 6b9b26d93da94caf993c038d9efcdedb.pdf

Framing an Appropriate Research Question 6b9b26d93da94caf993c038d9efcdedb.pdf
Hierarchy of management that covers different levels of management

Hierarchy of management that covers different levels of management
9953330565 Low Rate Call Girls In Rohini Delhi NCR

9953330565 Low Rate Call Girls In Rohini Delhi NCR
Troubleshooting vocab
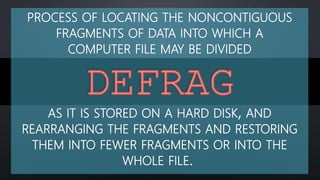
- 1. PROCESS OF LOCATING THE NONCONTIGUOUS FRAGMENTS OF DATA INTO WHICH A COMPUTER FILE MAY BE DIVIDED AS IT IS STORED ON A HARD DISK, AND REARRANGING THE FRAGMENTS AND RESTORING THEM INTO FEWER FRAGMENTS OR INTO THE WHOLE FILE.
- 2. DETERIORATION OF COMPUTER DATA AS A RESULT OF SOME EXTERNAL AGENT
- 3. TO REQUEST CONFIDENTIAL INFORMATION OVER THE INTERNET OR BY TELEPHONE UNDER FALSE PRETENSES IN ORDER TO FRAUDULENTLY OBTAIN CREDIT CARD NUMBERS, PASSWORDS, OR OTHER PERSONAL DATA.
- 4. REFERS TO THE COPYING AND ARCHIVING OF COMPUTER DATA SO IT MAY BE USED TO RESTORE THE ORIGINAL AFTER A DATA LOSS EVENT.
- 5. AN INDIVIDUAL WHO USES COMPUTER, NETWORKING OR OTHER SKILLS TO OVERCOME A TECHNICAL PROBLEM.
- 6. TYPE OF UTILITY USED FOR SCANNING AND REMOVING VIRUSES FROM YOUR COMPUTER.
- 7. TO PREPARE THE CHOSEN PARTITION ON THE DRIVE TO BE USED BY AN OPERATING SYSTEM BY DELETING ALL OF THE DATA1 AND SETTING UP A FILE SYSTEM.
- 8. MALICIOUS LITTLE PROGRAMS CAN CREATE FILES, MOVE FILES, ERASE FILES, CONSUME YOUR COMPUTER'S MEMORY, AND CAUSE YOUR COMPUTER NOT TO FUNCTION CORRECTLY.
- 9. RELATIVELY MINOR RELEASE OR VERSION UPGRADE TO AN EXISTING SOFTWARE PRODUCT THAT ADDS MINOR FEATURES OR CORRECTS BUGS.
- 10. ILLEGAL COPYING, DISTRIBUTION, OR USE OF SOFTWARE
- 11. A SOFTWARE THAT IS INSTALLED ON A COMPUTING DEVICE WITHOUT THE USER'S KNOWLEDGE OR PERMISSION.
Editor's Notes
- BOOST
- clever or expert programmer
- clever or expert programmer
- clever or expert programmer
- clever or expert programmer
- Spyware can capture information like Web browsing habits, e-mail messages, usernames and passwords, and credit card information. If left unchecked, the software can transmit this data to another person's computer over the Internet.
