Report
Share
Download to read offline
Recommended
More Related Content
What's hot
What's hot (20)
RRB JE Stage 2 Computer and Applications Questions Part 5

RRB JE Stage 2 Computer and Applications Questions Part 5
Security & control in management information system

Security & control in management information system
Information Security- Threats and Attacks presentation by DHEERAJ KATARIA

Information Security- Threats and Attacks presentation by DHEERAJ KATARIA
SECURITY & CONTROL OF INFORMATION SYSTEM (Management Information System)

SECURITY & CONTROL OF INFORMATION SYSTEM (Management Information System)
Viewers also liked
Viewers also liked (8)
Similar to legalworkspace-infographic 0116
Similar to legalworkspace-infographic 0116 (20)
Final Project – Incident Response Exercise SAMPLE.docx

Final Project – Incident Response Exercise SAMPLE.docx
Manage Risk By Protecting the Apps and Data Infographic

Manage Risk By Protecting the Apps and Data Infographic
Manage Risk By Protecting the Apps and Data That Drive Business Productivity

Manage Risk By Protecting the Apps and Data That Drive Business Productivity
Typical system servicesProgram executionIO operationsFile Sy.pdf

Typical system servicesProgram executionIO operationsFile Sy.pdf
legalworkspace-infographic 0116
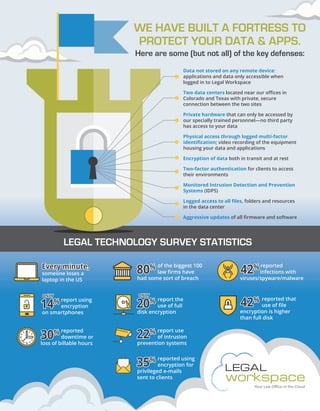
- 1. WE HAVE BUILT A FORTRESS TO PROTECT YOUR DATA & APPS. Here are some (but not all) of the key defenses: Data not stored on any remote device: applications and data only accessible when logged in to Legal Workspace Two data centers located near our offices in Colorado and Texas with private, secure connection between the two sites Private hardware that can only be accessed by our specially trained personnel—no third party has access to your data Physical access through logged multi-factor identification; video recording of the equipment housing your data and applications Encryption of data both in transit and at rest Two-factor authentication for clients to access their environments Monitored Intrusion Detection and Prevention Systems (IDPS) Logged access to all files, folders and resources in the data center Aggressive updates of all firmware and software reported downtime or loss of billable hours of the biggest 100 law firms have had some sort of breach someone loses a laptop in the US report using encryption on smartphones reported infections with viruses/spyware/malware reported using encryption for privileged e-mails sent to clients report the use of full disk encryption report use of intrusion prevention systems reported that use of file encryption is higher than full disk LEGAL TECHNOLOGY SURVEY STATISTICS 42% Every minute,Every minute, 30% 30% 80% 80% 42% 42% 42% 22% 22% 35% 35% 14% ONLY 14% ONLY 20% ONLY 20% ONLY