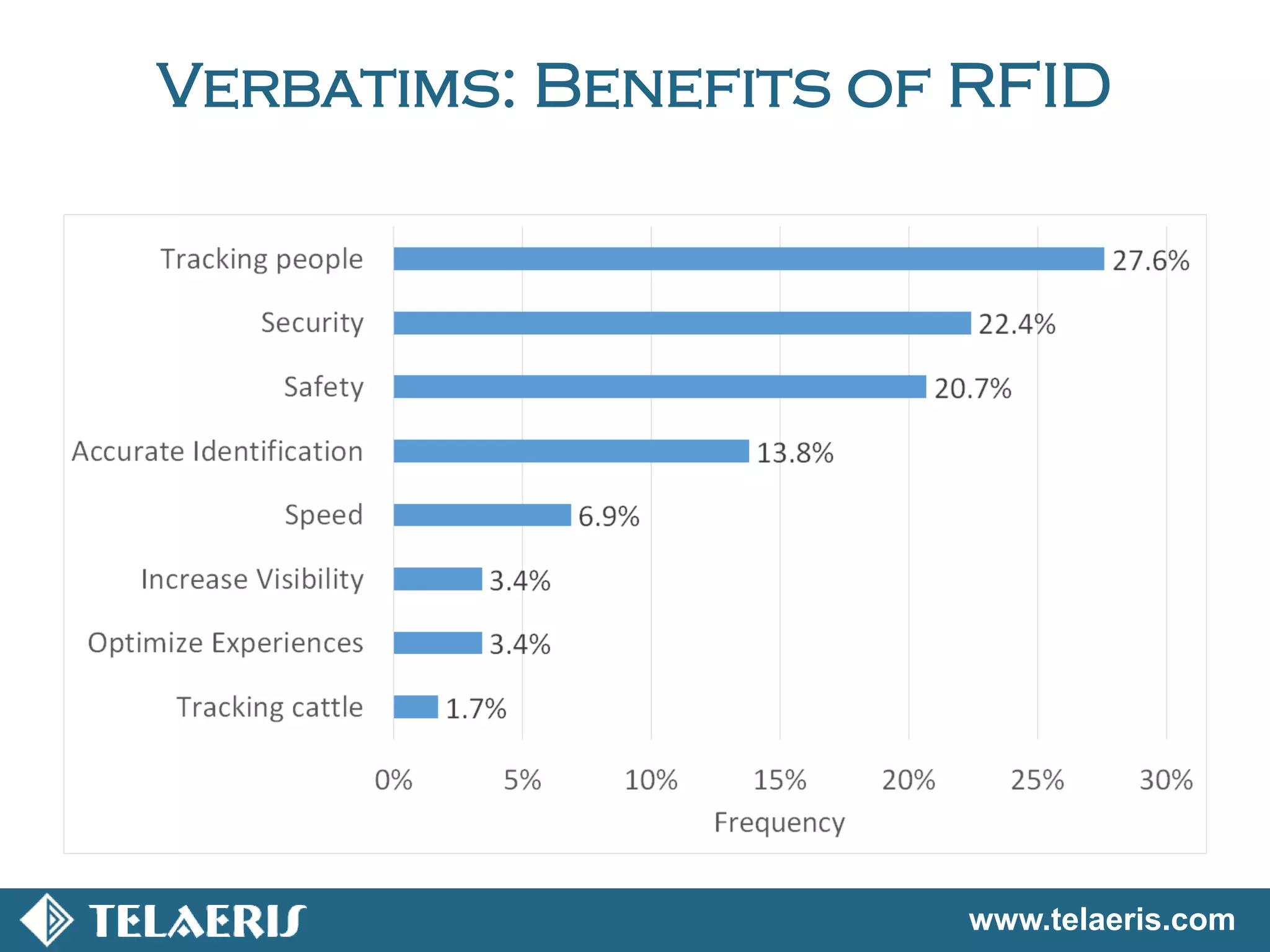
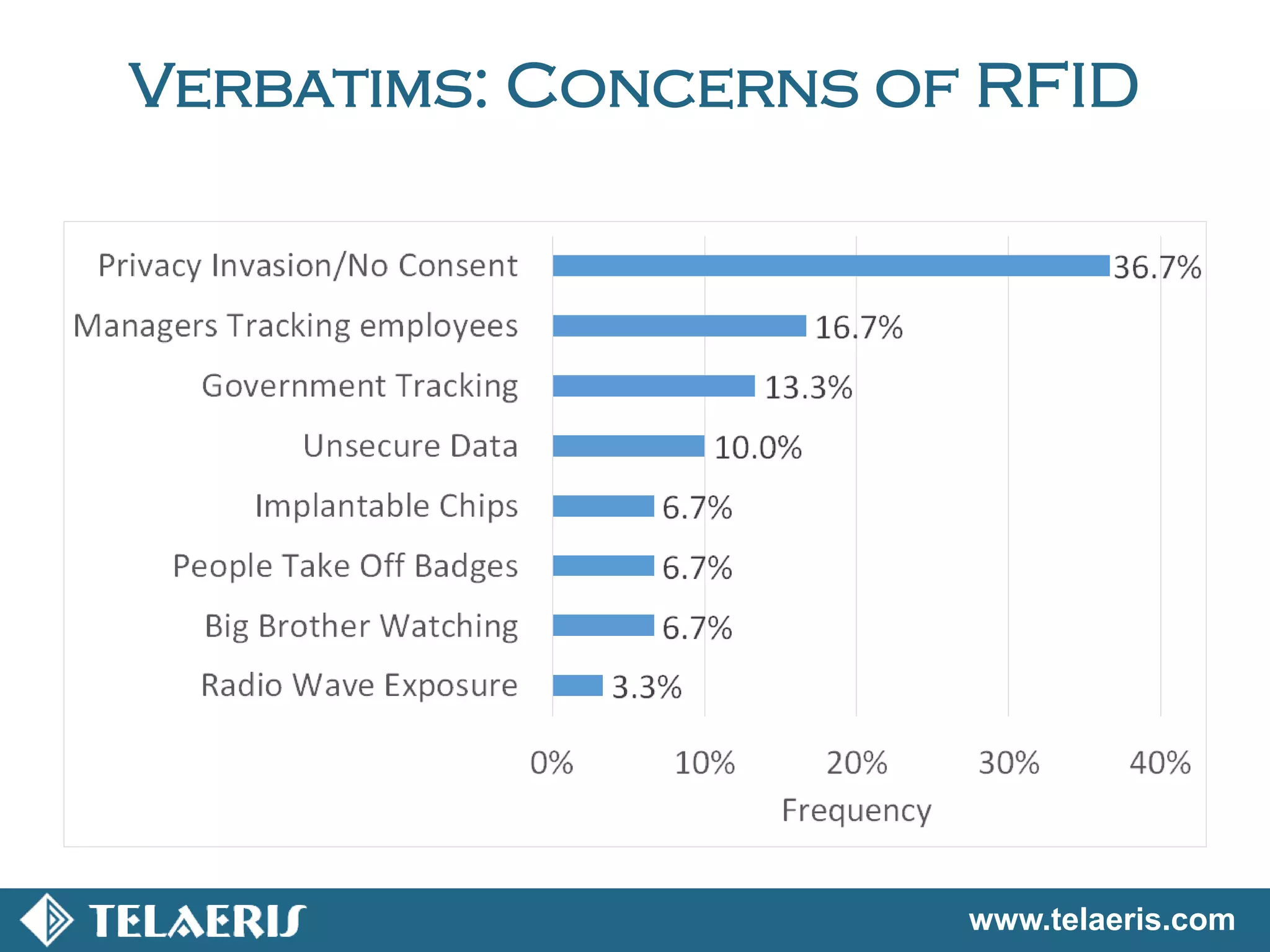
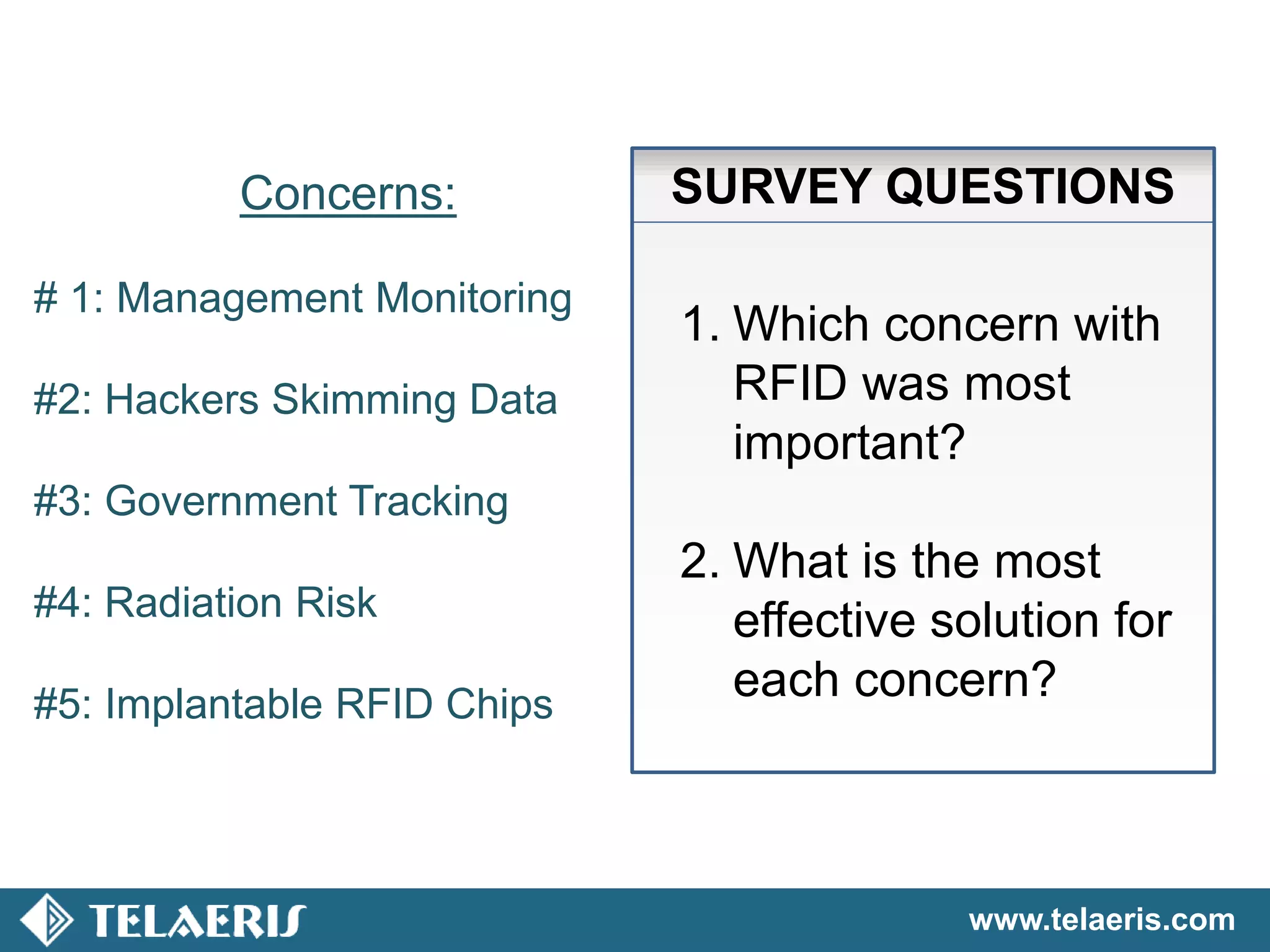
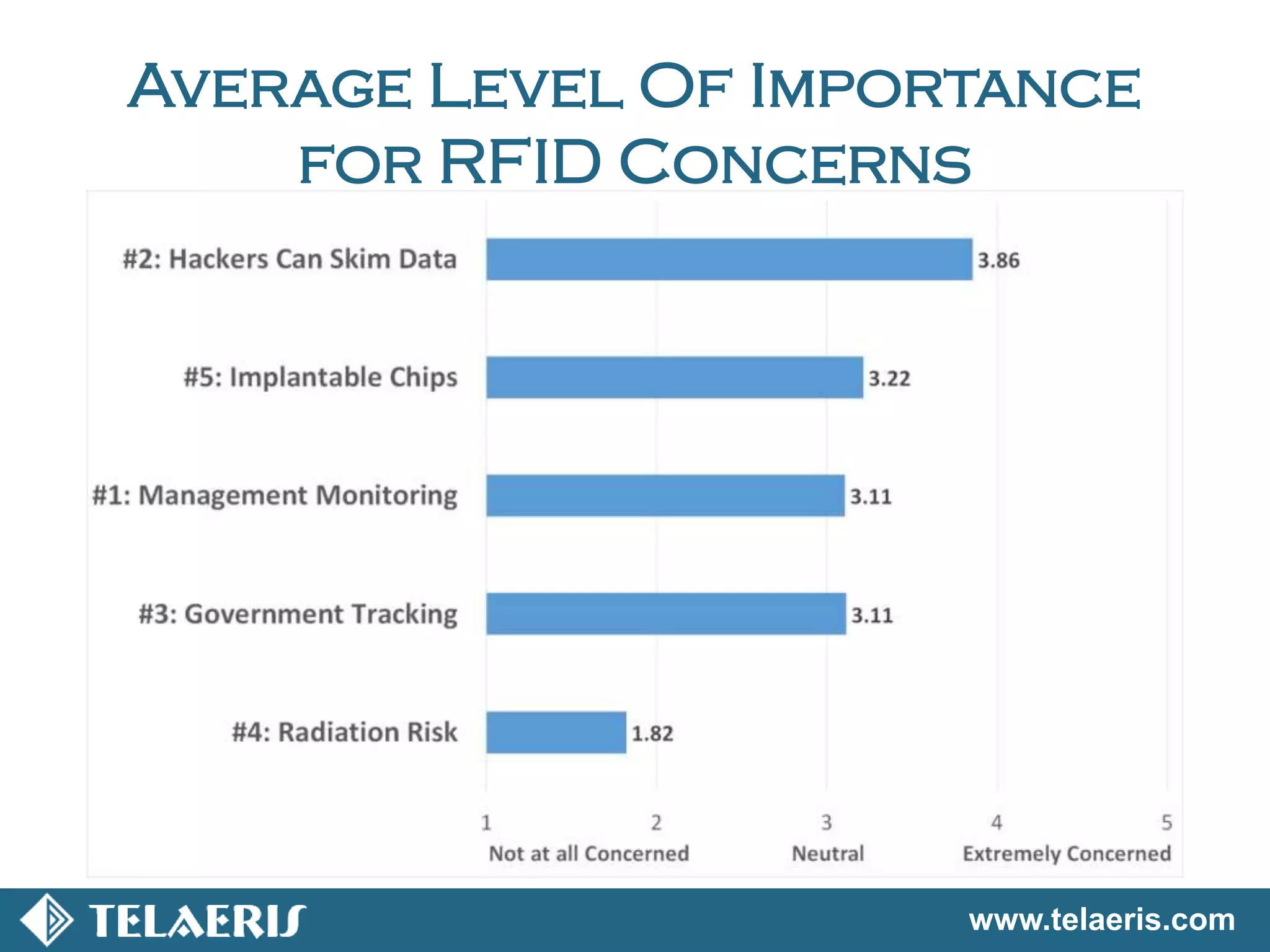
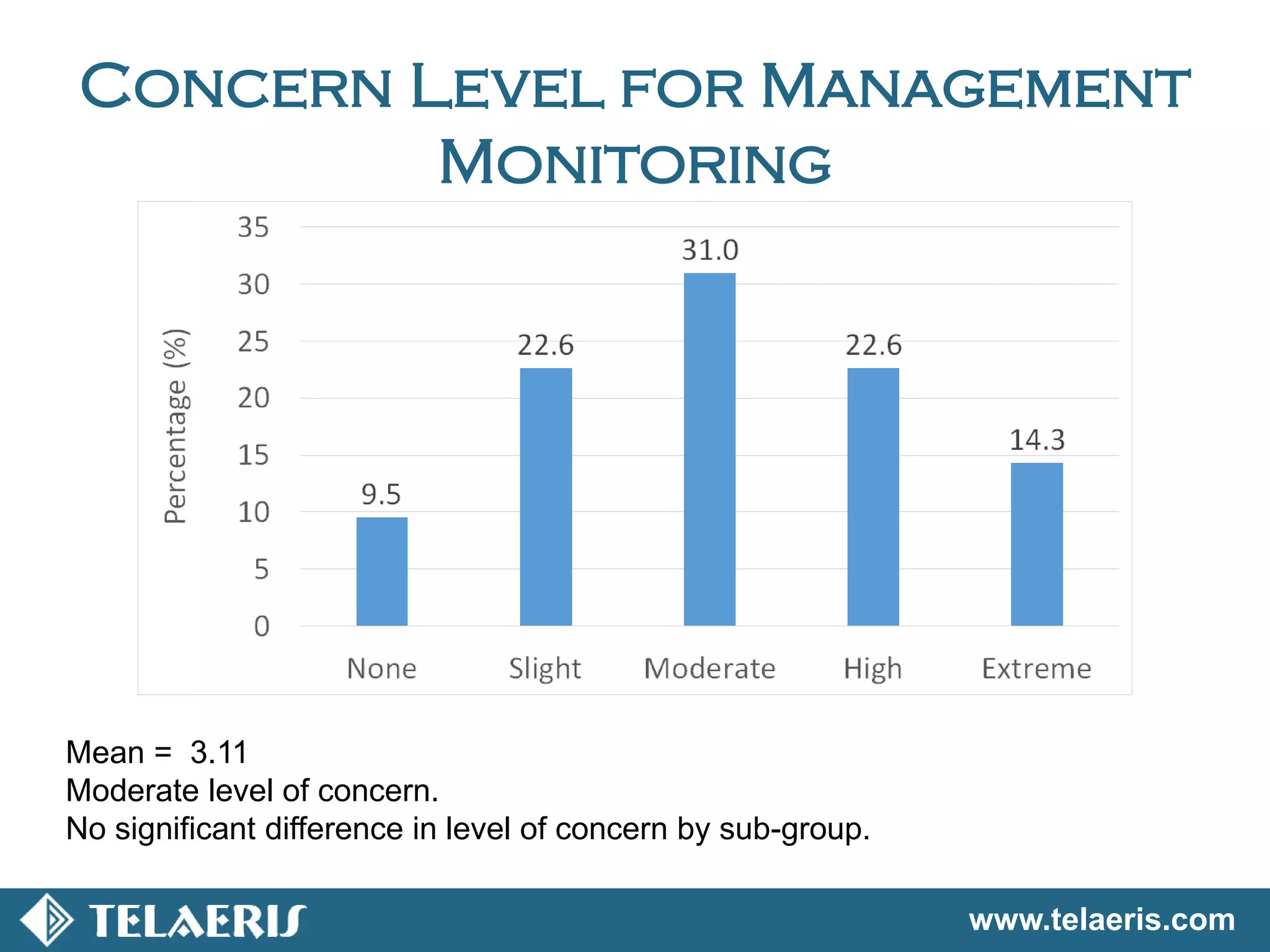
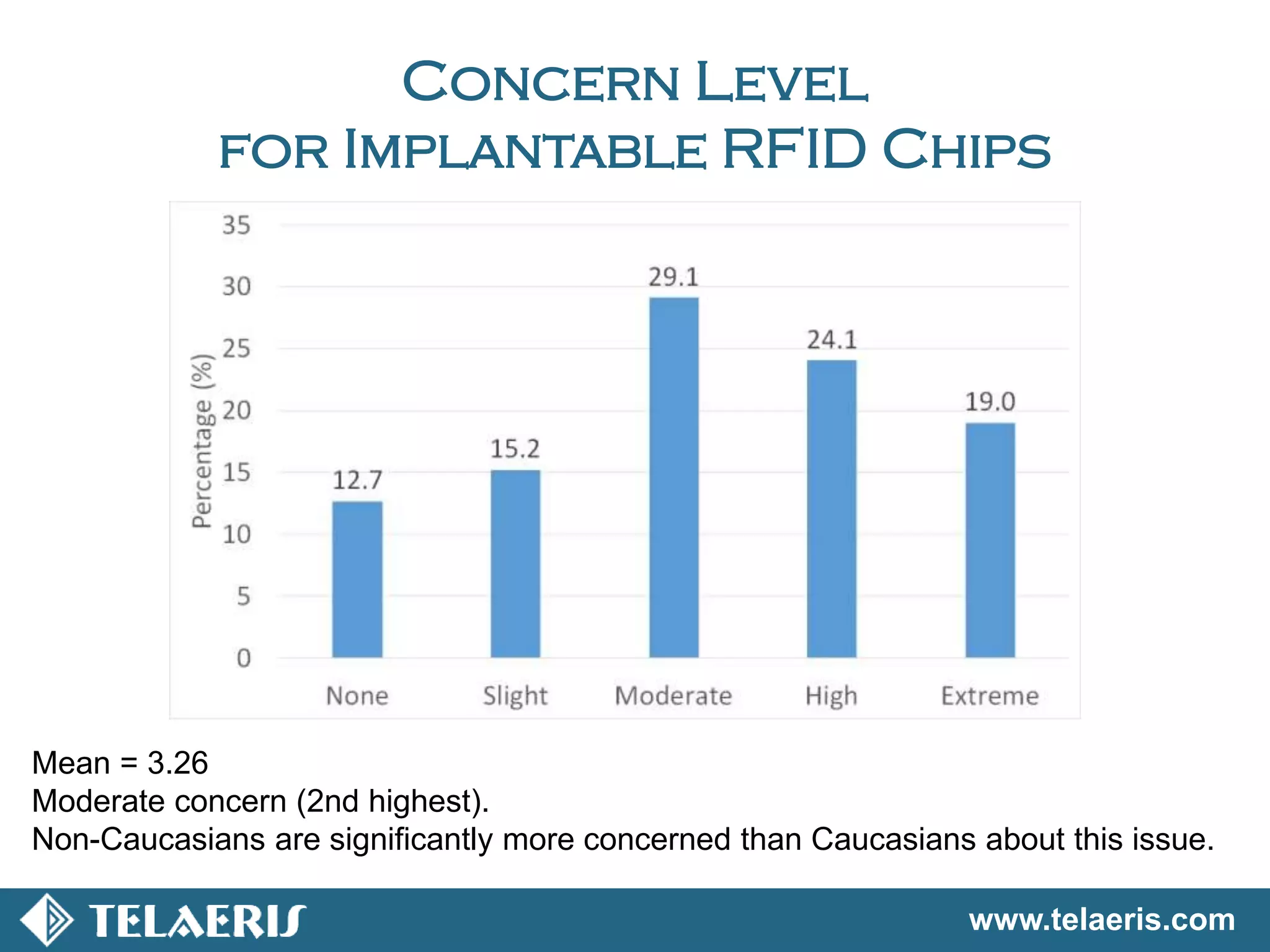
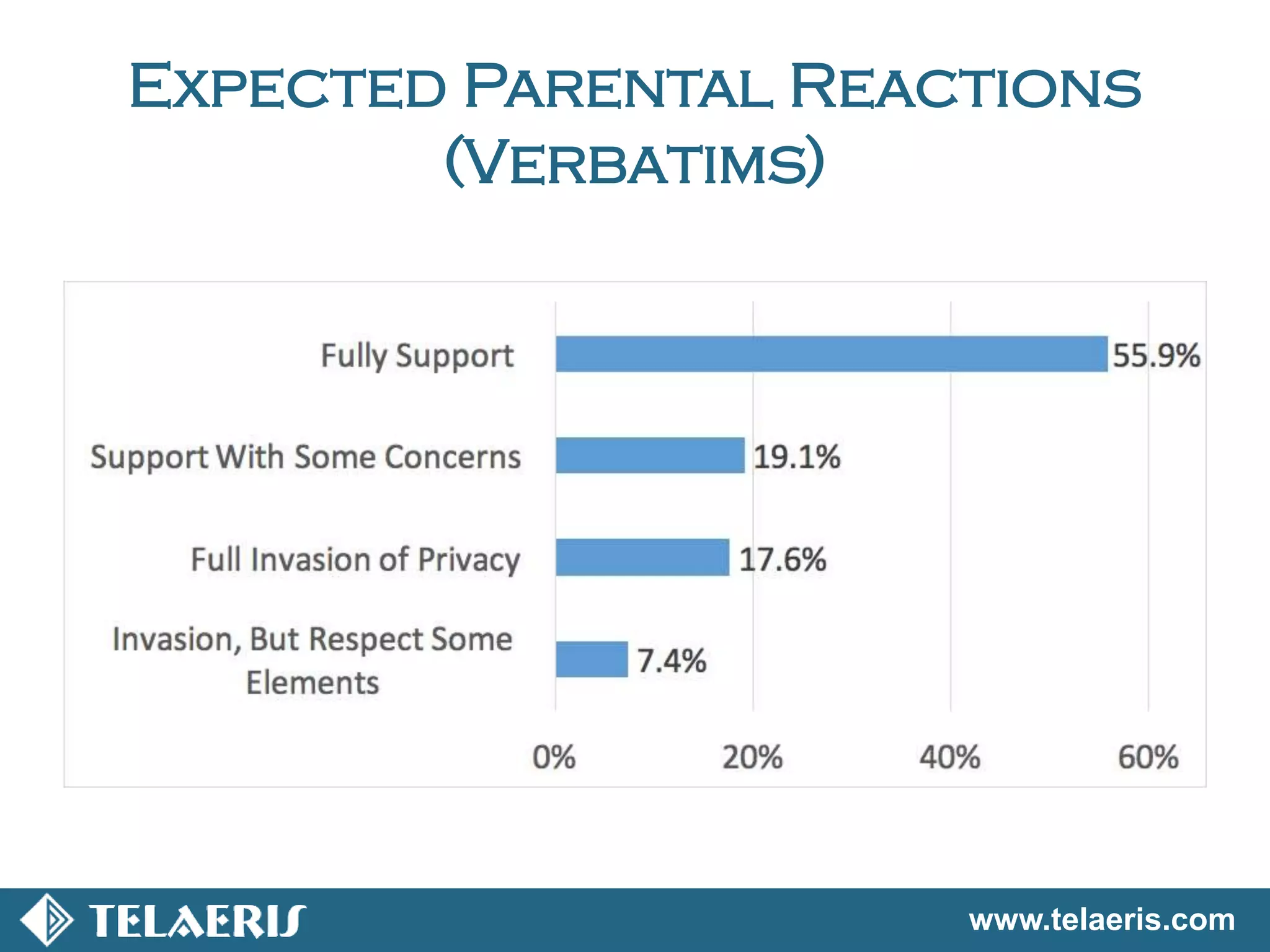
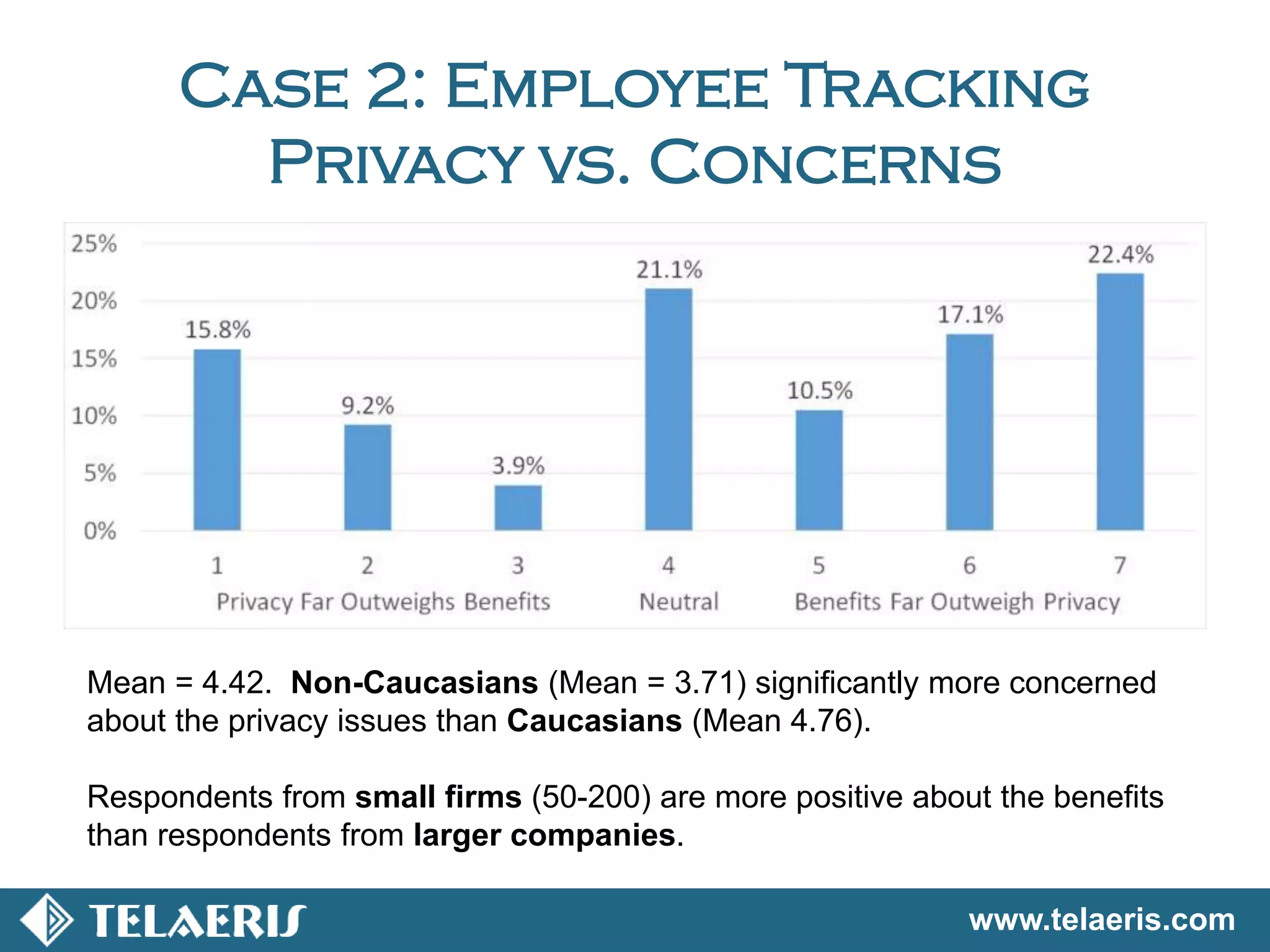
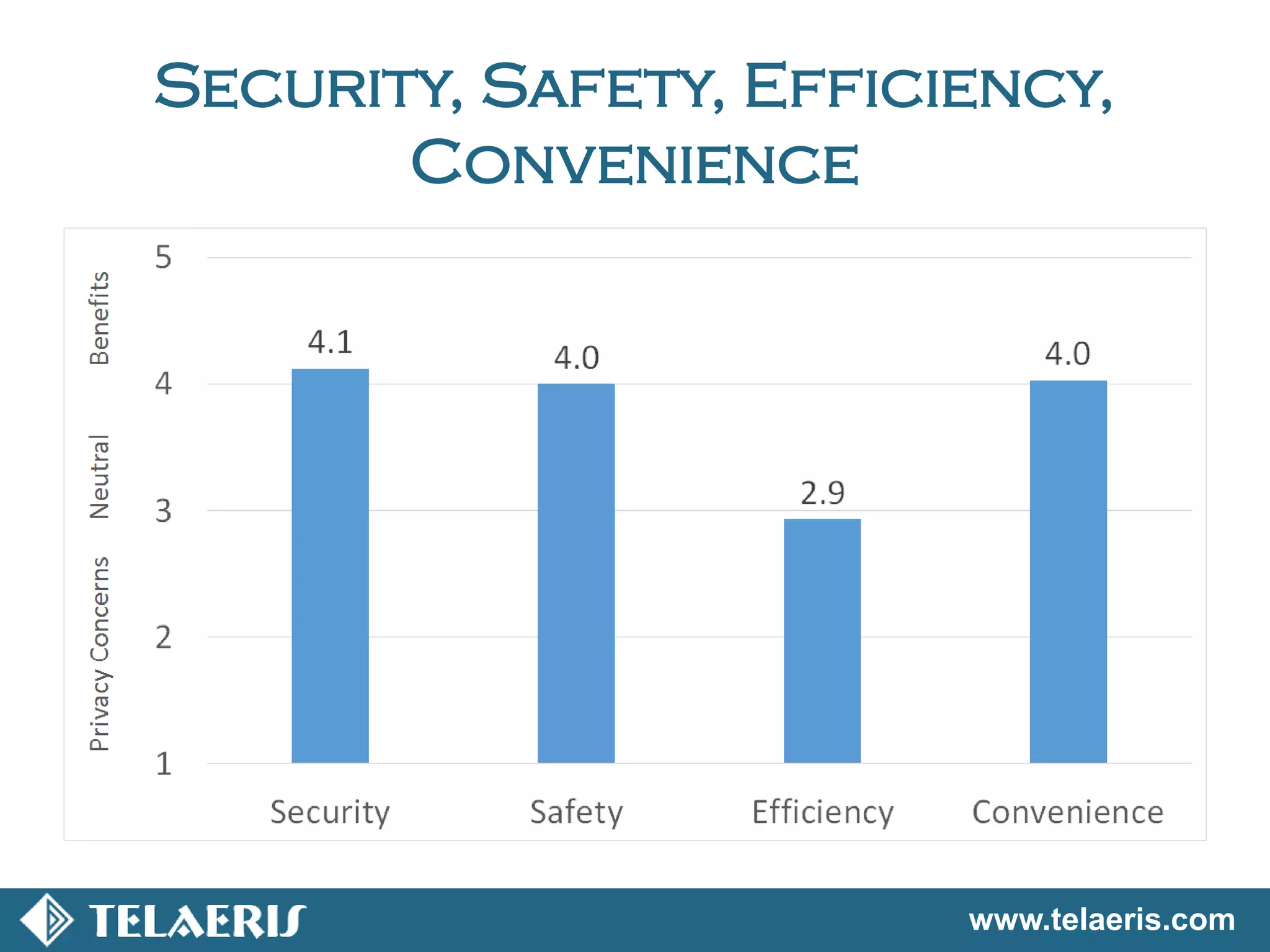
A joint study by Telaeris and Point Loma Nazarene University evaluated public perception of RFID tracking technology, focusing on privacy concerns vs. benefits. Key findings indicated that concerns over data hacking were the highest among respondents, with demographic differences influencing attitudes toward the technology. Recommendations include broadening the sample frame for future research to enhance understanding of diverse opinions on RFID applications.