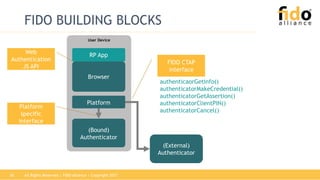
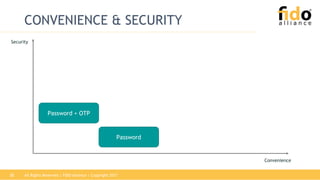
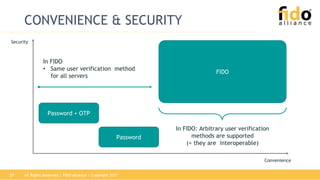
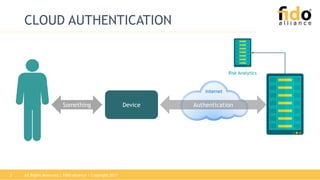
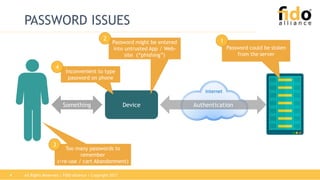
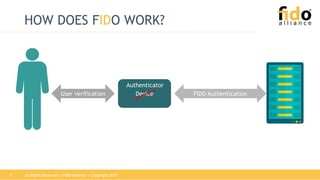
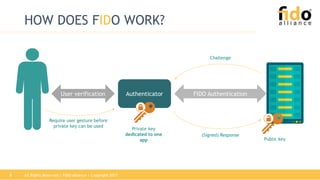
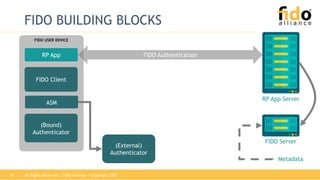
The document discusses technical specifications for device authentication provided by FIDO. It describes issues with traditional password authentication and how FIDO addresses these through standards that separate user verification from authentication. FIDO uses public key cryptography and relies on authenticators that can be integrated into devices to enable strong, passwordless authentication across multiple websites and applications.




![All Rights Reserved | FIDO Alliance | Copyright 201717
FIDO REGISTRATION
accountInfo, challenge, [cOpts]
rpId, ai, hash(clientData), cryptoP, [exts]
verify user
generate:
key kpub
key kpriv
credential c
c,kpub,clientData,ac,cdh,rpId,cntr,AAGUID[,exts],
signature(tbs)
c,kpub,clientData,ac,tbs, s
store:
key kpub
c
s
Authenticator
select Authenticator according to cOpts;
determine rpId, get tlsData;
clientData := {challenge, origin, rpId, hAlg, tlsData}
cOpts: crypto params, credential black list,
extensions
cdh
ai
tbs
ac: attestation certificate chain](https://image.slidesharecdn.com/fidotechnicalspecificationsoverviewsept2017-171005170823/85/FIDO-Technical-Specifications-Overview-17-320.jpg)
![All Rights Reserved | FIDO Alliance | Copyright 201718
FIDO AUTHENTICATION
Authenticator Relying Party
rpId, [c,] hash(clientData)
select Authenticator according to policy;
check rpId, get tlsData (i.e. channel id, etc.);
lookup key handle h;
clientData := {challenge, rpId, tlsData}
clientData,cntr,[exts],signature(cdh,cntr,exts)
clientData, cntr, exts, s
lookup kpub
from DB
check:
exts +
signature
using
key kpub
s
cdh
challenge, [aOpts]
verify user
find
key kpriv
cntr++;
process exts](https://image.slidesharecdn.com/fidotechnicalspecificationsoverviewsept2017-171005170823/85/FIDO-Technical-Specifications-Overview-18-320.jpg)

![All Rights Reserved | FIDO Alliance | Copyright 201722
RELYING PARTY APPLICATION
Browser “Application”:
A normal website - HTML, CSS,
JavaScript
Website, Inc. [US] https://www.acme.com
acme.com X](https://image.slidesharecdn.com/fidotechnicalspecificationsoverviewsept2017-171005170823/85/FIDO-Technical-Specifications-Overview-22-320.jpg)
![All Rights Reserved | FIDO Alliance | Copyright 201724
WEBAUTHN APIs: Create
User Device
Browser
Authenticator
Platform
RP AppWeb
Authentication
JS API
publicKeyCred = {
challenge, rp: {name=“Acme”},
user: { name=“john.smith@example.com”,
displayName = “John’s personal account”,
id: “1098237235409872”,
icon: "https://pics.acme.com/00/apqPb.png"
},
parameters: [ {
type: "public-key", algorithm: "ES256" }],
}
navigator.credentials.create( {publicKeyCred})
.then(function (newCredInfo) {
// Send new credential info to server for checking
// contains AuthenticatorAttestationResponse
})
);
John](https://image.slidesharecdn.com/fidotechnicalspecificationsoverviewsept2017-171005170823/85/FIDO-Technical-Specifications-Overview-24-320.jpg)
![All Rights Reserved | FIDO Alliance | Copyright 201725
WEBAUTHN APIs: Get
User Device
Browser
Authenticator
Platform
RP AppWeb
Authentication
JS API
var options = {
challenge: ValueFromServer,
timeout: 60000, // 1 minute
allowList: [{ type: "public-key" }]
};
navigator.credentials.get({ "publicKey": options })
.then(function (assertion) {
// Send assertion to server for verification
})
John](https://image.slidesharecdn.com/fidotechnicalspecificationsoverviewsept2017-171005170823/85/FIDO-Technical-Specifications-Overview-25-320.jpg)