Cyber Forensics
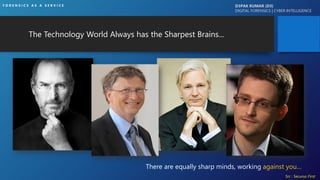
- 1. The Technology World Always has the Sharpest Brains... There are equally sharp minds, working against you… Src : Securus First F O R E N S I C S A S A S E R V I C E D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE
- 2. EVERY CRIME LEAVES A TRAIL OF EVIDENCE D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE
- 3. F O R E N S I C S A S A S E R V I C E D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE
- 4. DISCLAIMER Different organisations are subject to different laws and regulations. This resource is for educational and research purposes only. Do not attempt to violate the law with anything contained here. Neither the author of this material, nor anyone else affiliated in any way, is liable for your actions. Some information from the internet and some of personal experience; doesn’t want to hurt anybody D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE
- 5. ONCE THE DOCUMENTS HAVE BEEN POSTED ONLINE, THE GENIE IS OUT OF THE BOTTLE D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 6. D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 7. SOME CASE STUDIES • STUXNET, APT (MALWARE) 2010 • SONY PICTURE (IP THEFT) 2014 • BANGLADESH BANK HACK, COSMOS BANK(BFSI SECTOR) 2016 • MIRAI DYN BOTNET (IOT) 2016 • MP VYAPAM, SUNANDA PUSHKAR, HRITHIK ROSHAN KANGANA, AARUSHI TALWAR, MOVIE LEAKED PIRACY, HBO GOP, ATM BANKING, IRCTC DATA BREACH, WANNACRY, PETYA, BAD RABBIT… • STILL IN JURIS D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 8. SO WHAT IS 4N6 ? D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E A B
- 9. OR YOU MEAN • VAPT Skills • Almost Just Doing Data Recovery • Working On Tools & Technology • Malware Analysis • Password Cracking • Running Certain Script Programming • Rooting / Jailbreak Mobile Phones • Anything else? D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 10. Science for the examination and analysis of digital trace evidence. D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 11. D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 12. STANDARDS + TOOLS + ? = FORENSICS D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 13. STANDARDS + TOOLS + INTELLIGENCE = FORENSICS D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 14. D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 15. D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 16. DIGITAL FORENSICS STANDARDS & GUIDELINES • NIST: National Institute of Standard Technology (CFTT, NSRL, CFReDS) • ISO/IEC 27037: Guidelines for identification, collection, acquisition & preservation of digital evidence • ISO/IEC 17025: General requirements for the competence of testing and calibration laboratories • NIJ: National Institute of Justice (Several Standards, National Criminal Justice Reference Service) • IOCE: International Organization on Computer Evidence • ASCLD/LAB: American Society of Crime Laboratory Directors/Laboratory Accreditation Board • ASTM: E2678 standard; Guide for Education & Training • AES: Audio Engineering Society (Authentication of Analog tape) • SWGDE & SWGIT: Scientific Working Group on Digital Evidence & Scientific Working Group on Imaging Technology • ACPO: Association of Chief Police Officers • DSCI Manual India (Not specific standards but Manual) D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 17. Section 79 A of IT act : Central Government to notify Examiner of Electronic Evidence • The Central Government may for the purposes of providing expert opinion on electronic form evidence before any court or other authority specify by notification in the Official Gazette any Department body or agency of the Central Government or a State Government as an Examiner of Electronic Evidence. • The Lab has to follow competence of testing and calibration laboratories as per ISO/ IEC 17025:2005 and best practices as stated in ISO/IEC 27037:2012, guidelines for identification collection acquisition and preservation of digital evidence D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E 1. CFL, Army Cyber Group, DGMO, Signals 2. SFSL-DFS, Madiwala-Bangalore 3. CFSL, Hyderabad 4. DFS, Gandhinagar, Gujarat 5. CF-Data Mining Lab, SFIO-MCA, Delhi 6. FSL, Rohini, Delhi
- 18. D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE CHAIN OF CUSTODY Lack of integrity in the process of custody and, absence of appropriate documentation in this regard, will not only be detrimental to the cyber crime investigation, during trial but also, expose the IOs to criminal liability under Section 72 of the ITAA2008 F O R E N S I C S A S A S E R V I C E
- 19. SOME BEST TOOLS Commercial/Proprietary • Mobile Forensics : UFED, Oxygen, Santoku • Composite: EnCase, FTK, NUIX, Belkasoft, CyberCheck, Magnet Axiom, OSForensics • Writeblocker/Imager : Tableau, Ad Triage, FTK Imager, Encase Imager, DD Opensource/GPL • Volatility, Nirsoft, GRR, DFF, Autopsy TSK, Regripper, Caine Distro, Wireshark, JTR, Xplico, Networkminer, Splunk, Arsenal image mounter, HashMyFiles, SysInternal, Mimikatz, Metasploit, Redline, MobSF, Github (Tools), OS (DEFT, SIFT, KALI, CAINE) For more list : https://d3pakblog.wordpress.com/2016/12/27/computer-forensic-tools/ Career: https://d3pakblog.wordpress.com/2017/07/16/forensics-as-career/ D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 20. D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE CAREER F O R E N S I C S A S A S E R V I C E
- 21. So What Required D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E Where to Start Which degree is Important Is Programming required Which Certification What job Profile ? What to Study But I am L33T
- 22. D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 23. STEPS TO FOLLOW D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE 4. Web Application /Network (VAPT) 3. Networking Skills 7. Cyber Crime/Cyber Law 9. Certifications – Add Value F O R E N S I C S A S A S E R V I C E 5. Foreniscs (CHFI,SANS,Tools Whitepapers/Webinars) 6. Basic Idea of Risk/Compliance/Audit/ Standards 1. DEGREE 2. Mentor + Dedication 8. Hands-On Practices/ Case Studies 10. LinkedIn/ Dream Job
- 24. GOOD THINGS OF TECHNOLOGY D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE DEEP-WEB / REDDITLEAD (SOCIAL NETWORKING) MOBILE IOT IOT / Sync COOKIES INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 25. GOOD THINGS OF TECHNOLOGY (Cont.) D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE CTI COMMUNITIES OPEN-SOURCE INTELLIGENCE / GIT GOOGLE F O R E N S I C S A S A S E R V I C E And The best : Social Engineering
- 26. D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE USE CASE F O R E N S I C S A S A S E R V I C E
- 27. USE CASE : IP Theft o Employee Resigned o Joined New Company o Data theft o Type of data (pdf, xlsx) o Browser history cleared o No data in Recycle bin o Formatted USB Forensics Imaging (Physical If required) Timeline Machine (Laptop/Desktop) : User info (SID) Data Recovery (Specific data formats) Mail Check (pst,ost, lotus etc) SIEM/DLP logs (Data copied) Firewall (3rd party URL data uploaded) D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE Q U E S T I O N AN S W E R F O R E N S I C S A S A S E R V I C E
- 28. D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE Cyber Kill Chain MITRE ATT&CK MATRIX Recon Weaponise Delivery Exploitation Installation C2 Actions & Objectives Task: Identify the Attackers’ Step by Step Process Goal: Disrupting Attackers’ operations Motivation Preparation SE OSINT Configuration Packaging Powershell Add Mechanism of Delivery Infection Vector Phishing Technical or human? Applications affected Method & Characteristics Persistence Characteristic s of change Self0signed Driver Communication between victim & adversary VPN What the adversary does when they have control of the system Data Exfil APT MITRE ATT&CK: Active Scanning Passive Scanning Determine Domain & IP Address Space Analyze Third-Party IT Footprint MITRE ATT&CK: Malware Scripting Service Execution MITRE ATT&CK: Spearphishing Attachment/Link Exploit Public- Facing Application Supply Chain Compromise MITRE ATT&CK: Local Job Scheduling Scripting Rundll32 MITRE ATT&CK: Application Shimming Hooking Login Items MITRE ATT&CK: Data Obfuscation Domain Fronting Web Service MITRE ATT&CK: Email Collection Data from Local System/Network Share Surveillance F O R E N S I C S A S A S E R V I C E
- 29. FORENSIC CHALLENGES D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 30. Don’t believe marketing hype "oh, we spent $$$ in $Vendor product, so we are safe" Any "tool", regardless of the price, is still a "tool" D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 31. D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE DEMOGRAPHIC F O R E N S I C S A S A S E R V I C E
- 32. IMAGE FORENSICS D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE F O R E N S I C S A S A S E R V I C E
- 33. D3pak@Protonmail.com Resources : D3pakblog.wordpress.com D3PAK KUMAR (D3) DIGITAL FORENSICS | CYBER INTELLIGENCE Thank You F O R E N S I C S A S A S E R V I C E
