Hacking wireless networks
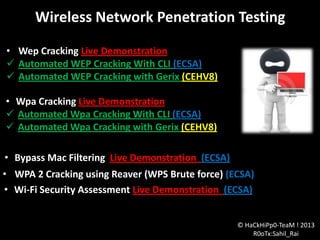
- 1. Wireless Network Penetration Testing • Wep Cracking Live Demonstration Automated WEP Cracking With CLI (ECSA) Automated WEP Cracking with Gerix (CEHV8) • Wpa Cracking Live Demonstration Automated Wpa Cracking With CLI (ECSA) Automated Wpa Cracking with Gerix (CEHV8) • Bypass Mac Filtering Live Demonstration (ECSA) • WPA 2 Cracking using Reaver (WPS Brute force) (ECSA) • Wi-Fi Security Assessment Live Demonstration (ECSA) © HaCkHiPp0-TeaM ! 2013 R0oTx:Sahil_Rai
- 2. List of WLAN channels Amendments Freq-(GHz) Speed (Mbps) Range (Ft) 802.11a 5 54 24-75 802.11b 2.4 11 150-150 802.11g 2.4 54 150-150 802.11i Define WPA Enterprise /WPA Personal for Wi-Fi 802.11n 2.4,5 54 100 802.11( Wimax) 10-66 70-100 30 miles Bluetooth 2.4 1-3 25 Each ranges divided into multiple channels Every Country has allowed channels, users and maximum Frequency levels. © HaCkHiPp0-TeaM ! 2013 R0oTx:Sahil_Rai
- 3. IEEE 802.11b/g/n Channel © HaCkHiPp0-TeaM ! 2013 R0oTx:Sahil_Rai
- 4. Encryption & Authentication used in IEEE 802.11 Environment: Wired Equivalent Privacy (WEP) – WEP uses RC4 encryption algorithm which has several weaknesses. WEP relies on secret key “shared” between a wireless device and the AP Wi-Fi Protected Access (WPA) – WPA protocol implements majority of IEE 802.11i standard requirements. WPA makes use of Temporal Key Integrity Protocol (TKIP) instead of RC4 used in its predecessor WEP. To offer greater security WPA Personal – Commonly referred as WPA – Pre shared key (PSK). The clients authenticate with the AP’s using the 256 bit keys. WPA Enterprise – Mainly designed for Enterprise networks and requires authentication using RADIUS server. Extensible Authentication Protocol (EAP) is used for authentication, which comes in different flavors (EAP-TLS, EAP-TTLS). RADIUS protocol inherently only allows for password based authentication i.e. the password is sent as MD5 Hash or response to a challenge, (EAP) is an authentication framework included in Windows Client and Windows Server operating systems
- 5. Wi-Fi authentication mode Probe Request Probe Response ( Security Parameters ) Open System Authentication Request Open System Authentication Response Association Request ( Security Parameters ) Association Response Handshake Completed open system authentication (ssid beaconing)
- 6. Wi-Fi authentication mode Authentication Request sent to AP AP Sends Challenge txt Client encrypt challenge txt and sends it back to AP AP decrypts challenge text , and if correct authenticates client Handshake Completed Shared key authentication process
- 7. 1. Authentication Request ( Encrypted Challenge ) 2. Authentication Response ( Challenge ) 0 0 0 Sniffing packets (packet capture) Sniffing packets (packet capture) © HaCkHiPp0-TeaM R0oTx:Sahil_Rai
- 8. Wi-Fi vulnerability assessment checklist • Vulnerability assessments can help you find and fix WLAN weaknesses before attackers take advantage of them Wireless Sniffing • Wireless Card can be only on one channel at a time • Can not sniff on all channels and band at the same time • Wireless card needs to be capable of operate a/b/g/n/h ? For each discovered 802.11 access point, document: Media Access Control (MAC) address (BSSID) Extended service set identifier (ESSID) Channel Number Average/Peak signal-to-noise ratio (SNR) Beaconed security parameters (i.e., WEP, Wpa, wpa2 security)
- 9. Wep Cracking: Lab Test Requirement • • • • Airmon-ng Airodump-ng Aireplay-ng Aircrack-ng • Tp-link wlan card supporting only Seamlessly compatible with 802.11b/g . © HaCkHiPp0-TeaM ! 2013 R0oTx:Sahil_Rai
- 10. Wpa Cracking: Lab Test Requirement • • • • • Airmon-ng Airodump-ng Aireplay-ng Aircrack-ng Dictionary File • Tp-link wlan card supporting only Seamlessly compatible with 802.11b/g. © HaCkHiPp0-TeaM ! 2013 R0oTx:Sahil_Rai
- 11. WPA 2 Cracking Using Reaver (WPS Brute force) Penetration-Testing Tool (Reaver) Cracking WPA/Wpa2 using reaver, it uses a brute force attack on the access point's WPS (Wi-Fi Protected Setup) and may be able to recover the WPA/WPA2 passphrase in 4-10 hours but it also depends on the AP. there is no need to get a handshake. © HaCkHiPp0-TeaM ! 2013 R0oTx:Sahil_Rai
- 12. Bypass Mac address binding
- 13. Wi-Fi Security Assessment Wi-Fi authentication process using centralized authentication server Client Request Connection AP send the EAP request to determine identity EAP response with identity Forward the identity to the radius . Send a request to the wireless client via AP specifying the authentication mechanism to be used The wireless client responds to the RADIUS server with its credential via the Ap Sends an encrypted authentication key Global authentications key to the AP if the credentials are encrypted with per station unicast acceptable session key
- 14. Wi-Fi cracking commands details Where: Wep/ Wpa Cracking -c 5 is the channel for the wireless network --bssid 00:14:6C:7E:40:80 is the access point MAC address. This eliminate extraneous traffic. -w capture is file name prefix for the file which will contain the IVs. wlan0 is the interface name. -1 means fake authentication 0 reassociation timing in seconds -e teddy is the wireless network name -a 00:14:6C:7E:40:80 is the access point MAC address -h 00:09:5B:EC:EE:F2 is our card MAC address wlan0 is the wireless interface name Where: Wep/ Wpa Cracking -1 means fake authentication 0 reassociation timing in seconds -e hhippo is the wireless network name -a 00:14:6C:7E:40:80 is the access point MAC address -h 00:0F:B5:88:AC:82 is our card MAC address Wlan0 is the wireless interface name
- 15. Where: -5 means the fragmentation attack -b 00:14:6C:7E:40:80 is the access point MAC address -h 00:09:5B:EC:EE:F2 is the MAC address of our card and must match the MAC used in the fake authentication wlan0is the wireless interface name Where: -2 means use interactive frame selection -r arp-request defines the file name from which to read the arp packet wlan0 defines the interface to use Where: -0 means generate an arp packet -a 00:14:6C:7E:40:80 is the access point MAC address -h 00:09:5B:EC:EE:F2 is MAC address of our card -k 255.255.255.255 is the destination IP (most APs respond to 255.255.255.255) -l 255.255.255.255 is the source IP (most APs respond to 255.255.255.255) -y fragment-0203-180343.xor is file to read the PRGA from (NOTE: Change the file name to the actual file name out in step 4 above) -w arp-request is name of file to write the arp packet to
- 16. Thank You © HaCkHiPp0-TeaM ! 2013 R0oTx:Sahil_Rai http://hackhippo.blogspot.com
Editor's Notes
- RC4 was designed by Ron Rivest of RSA Security in 1987 Transport Layer Security (TLS)
