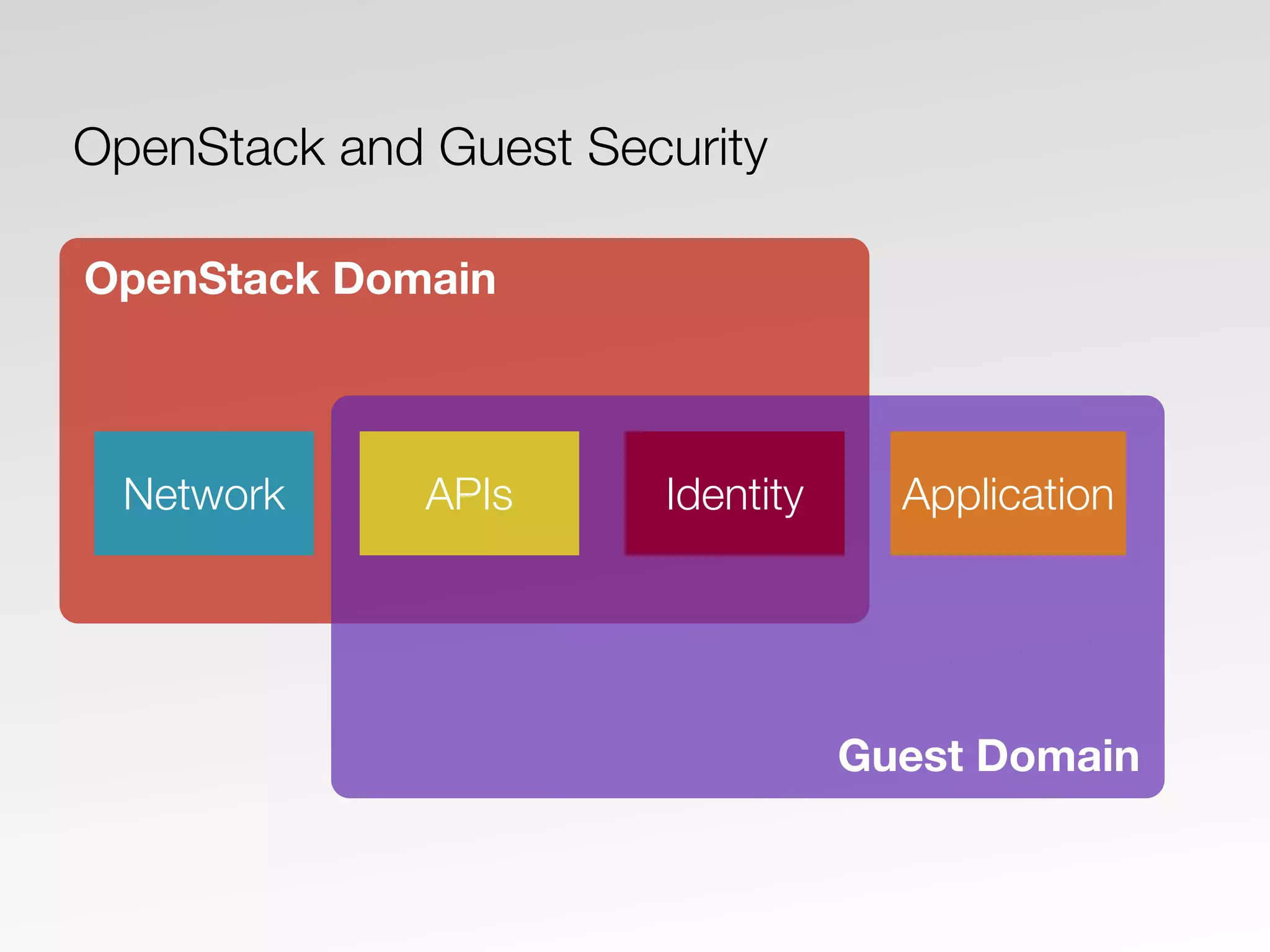
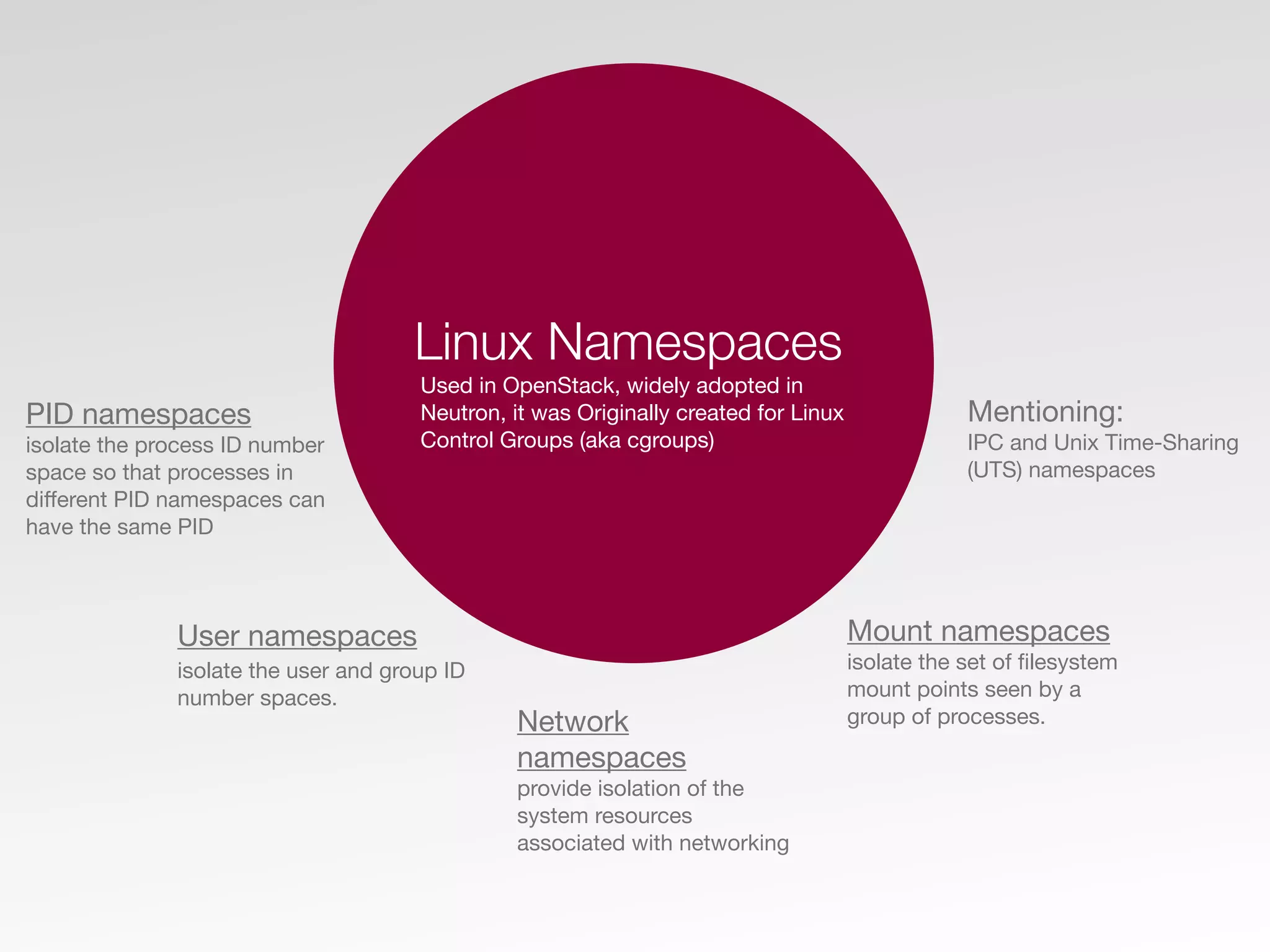
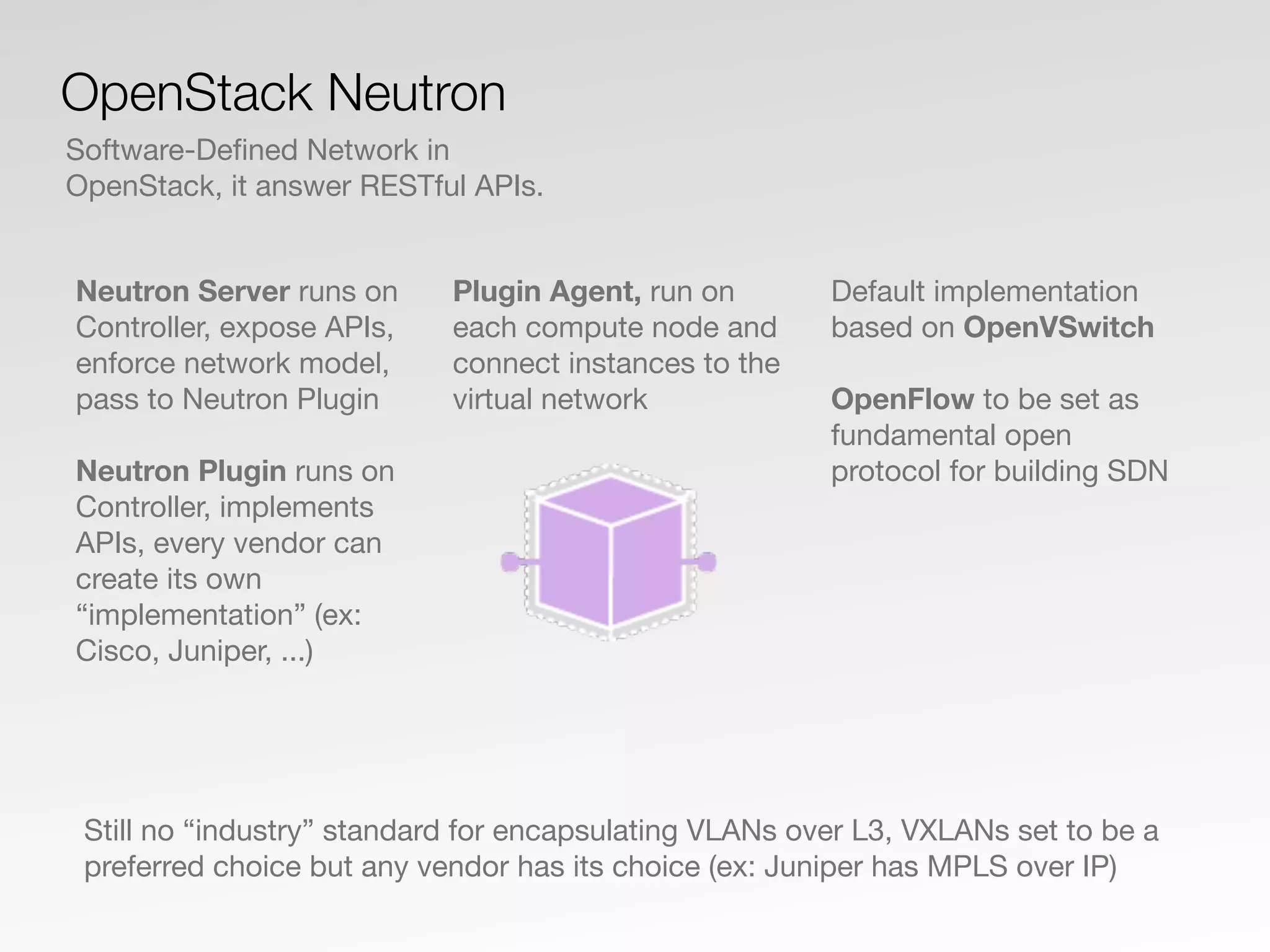
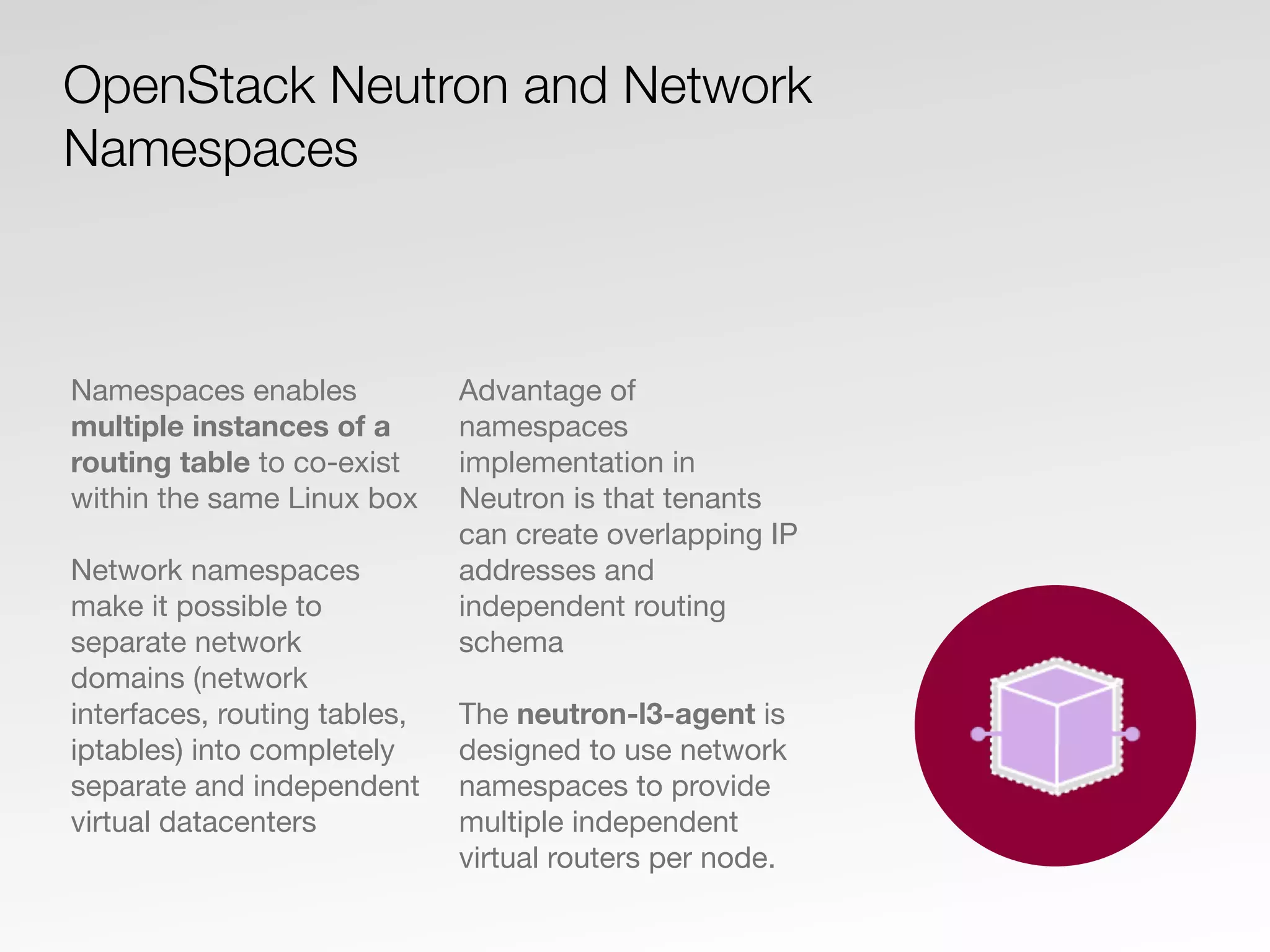
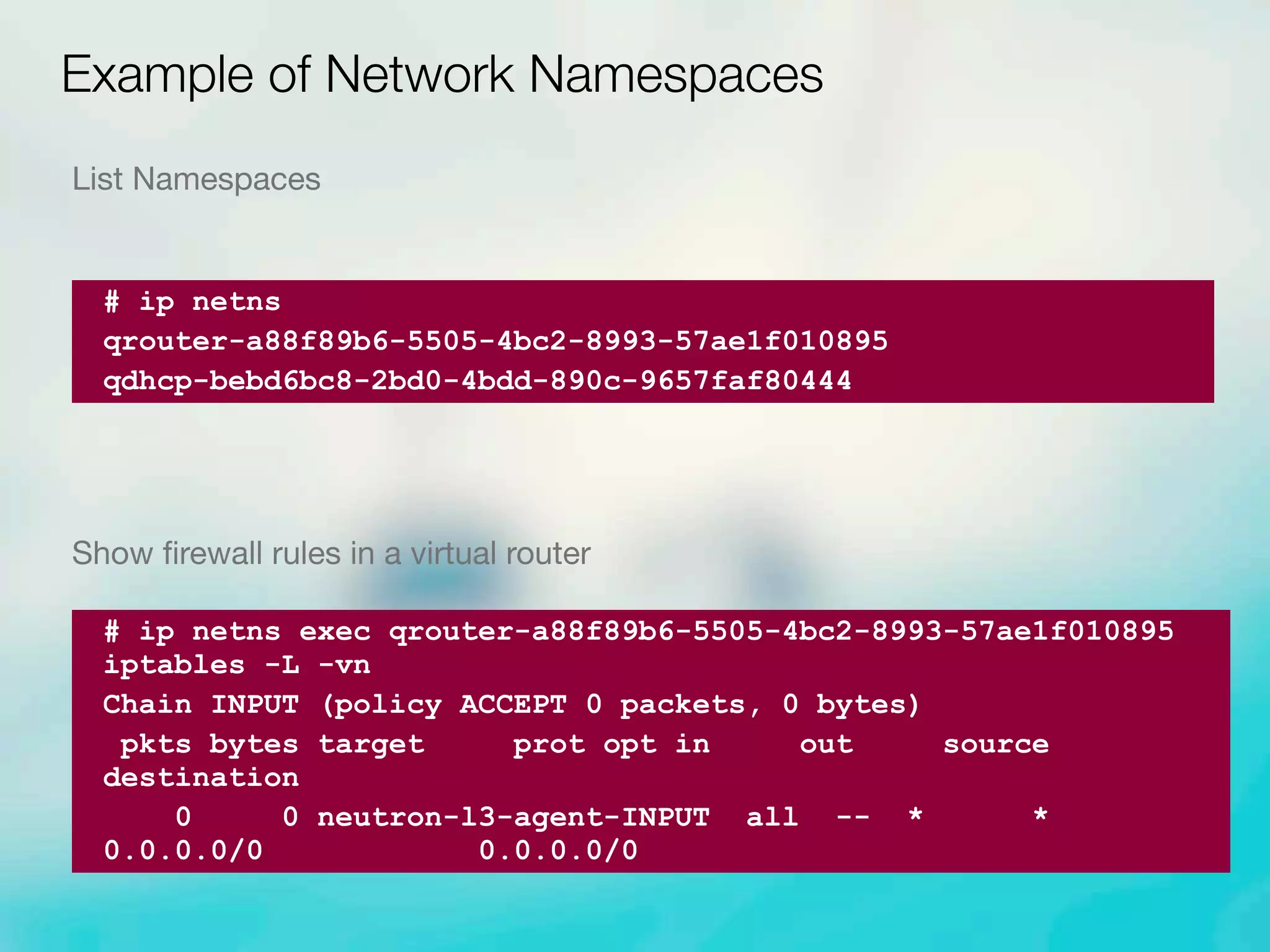
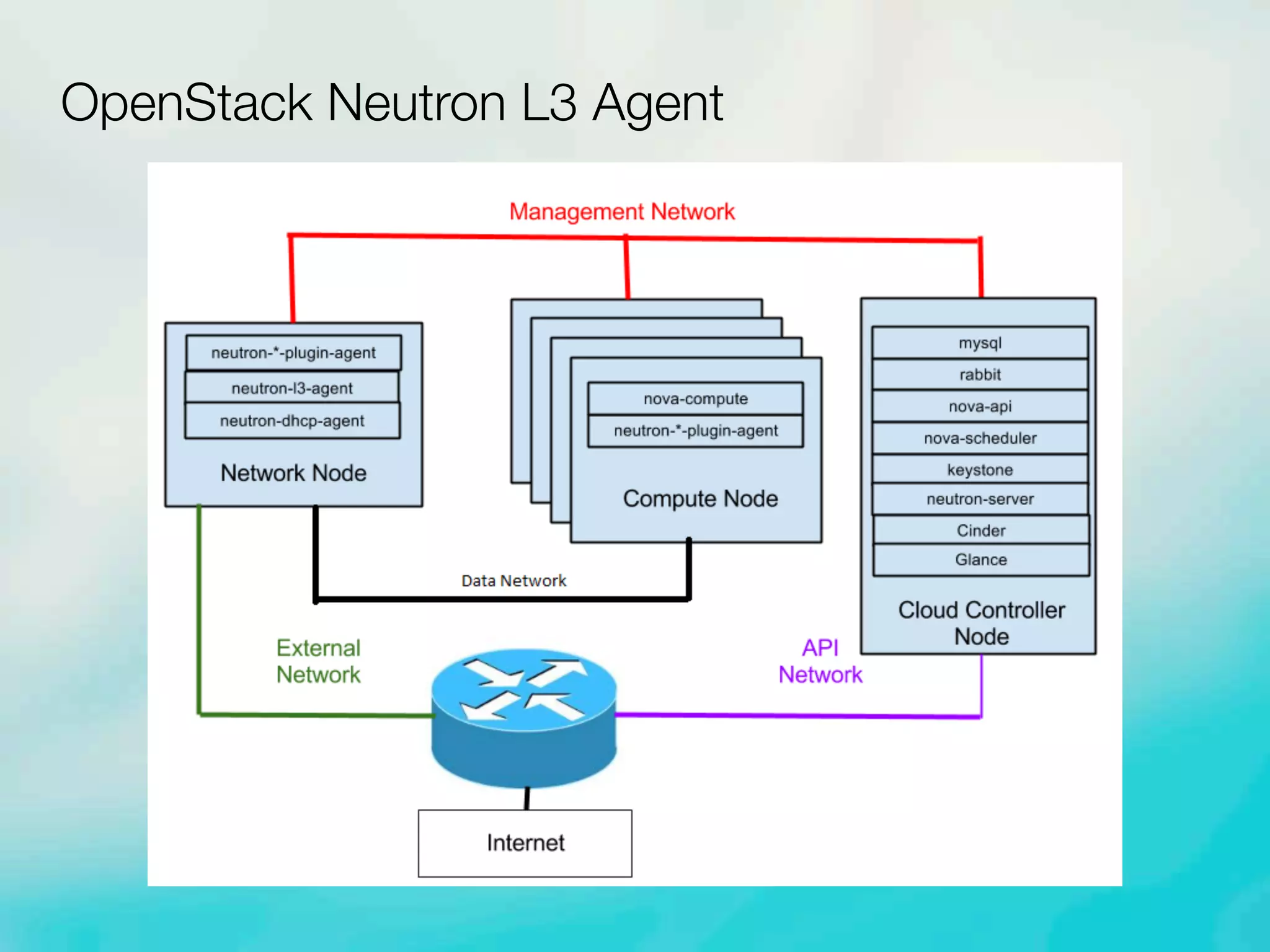
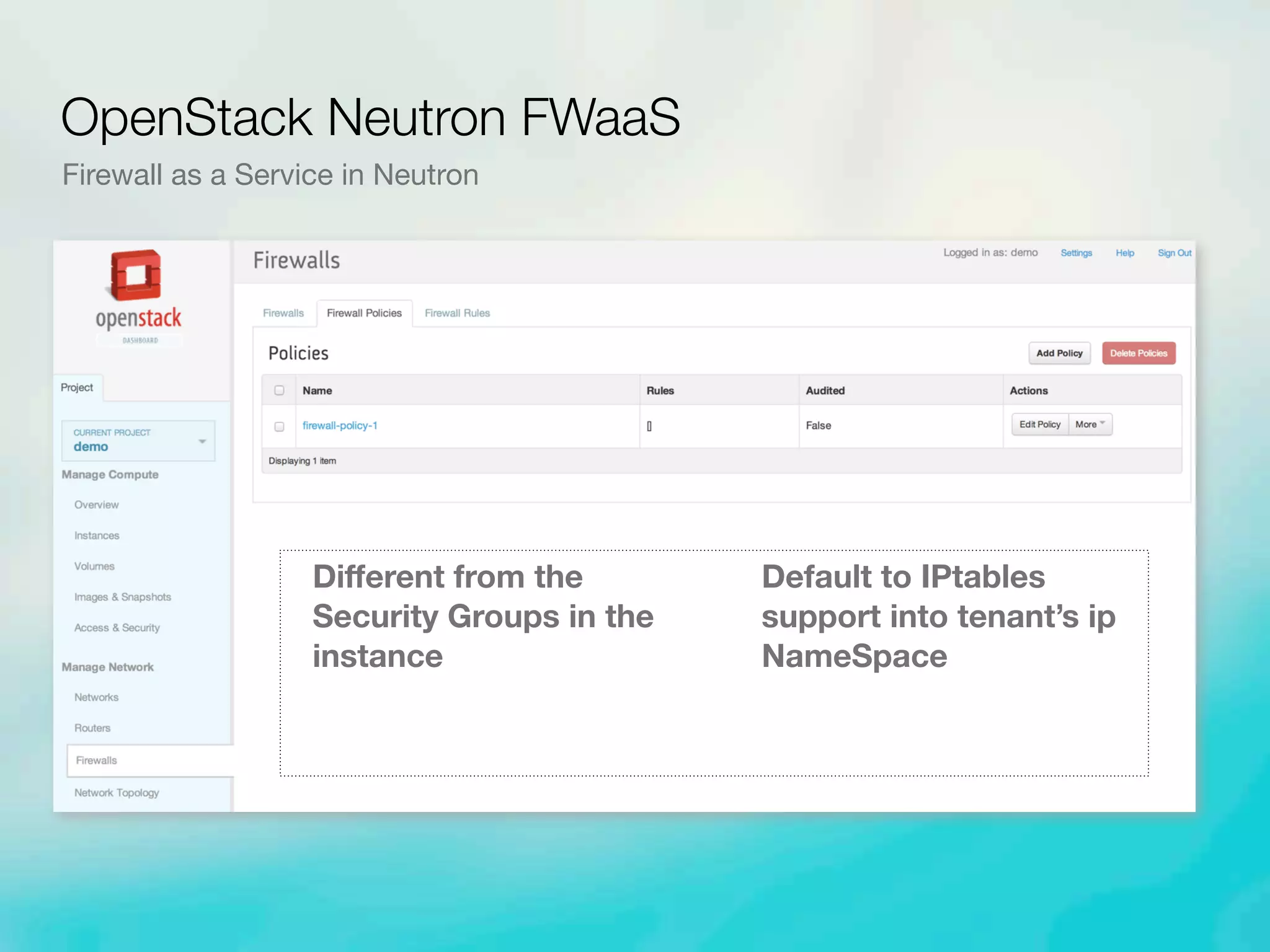
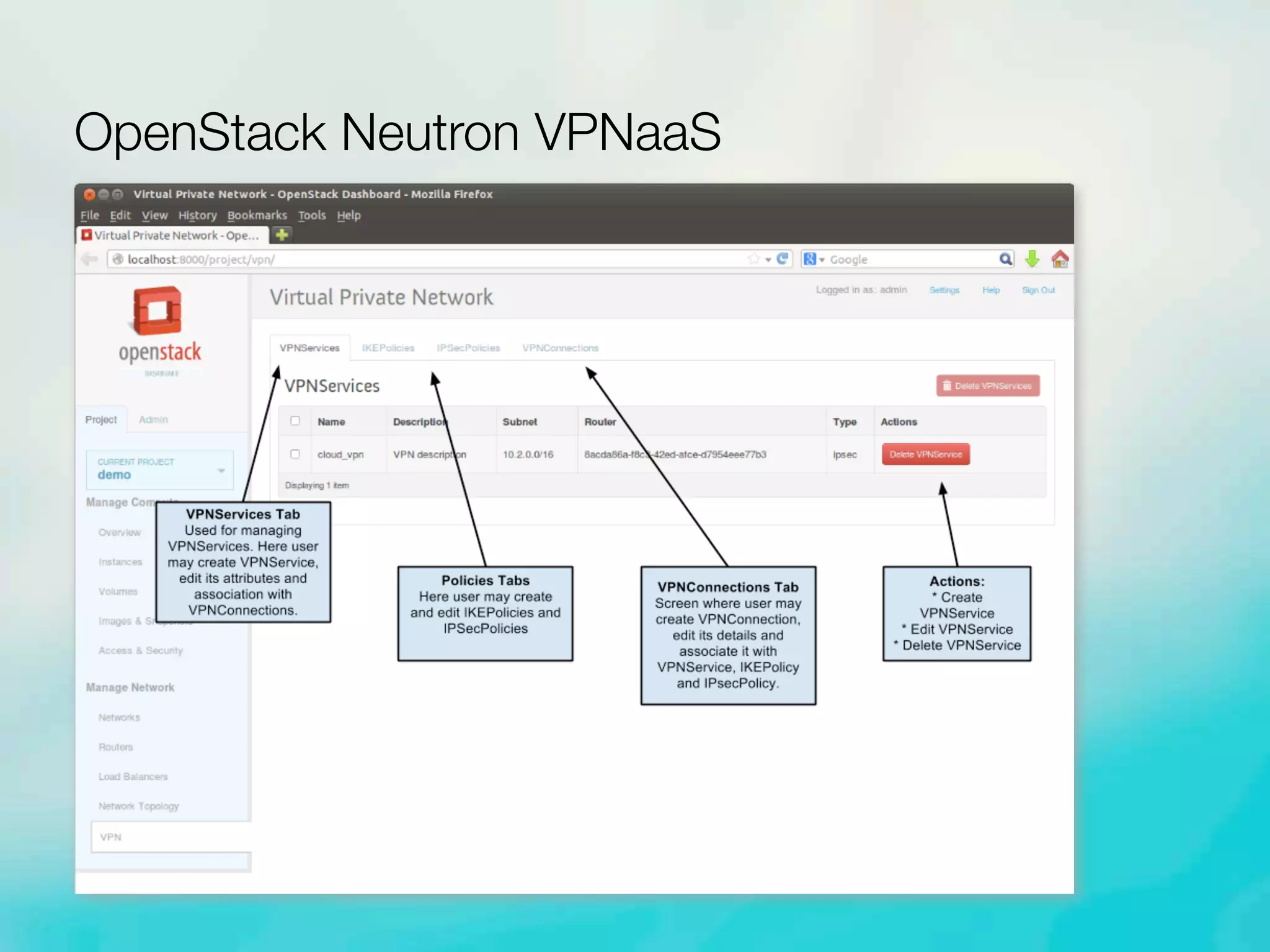
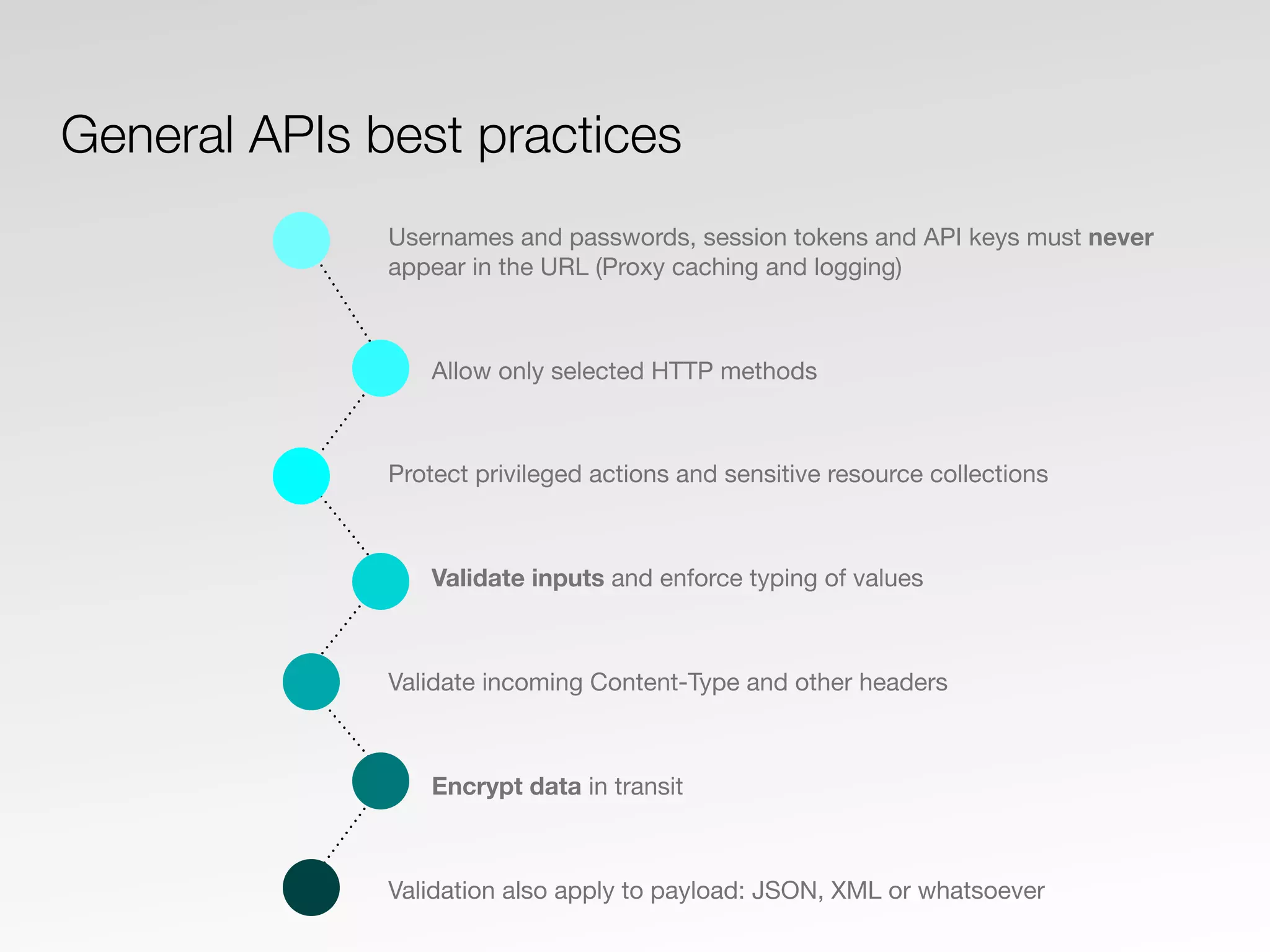
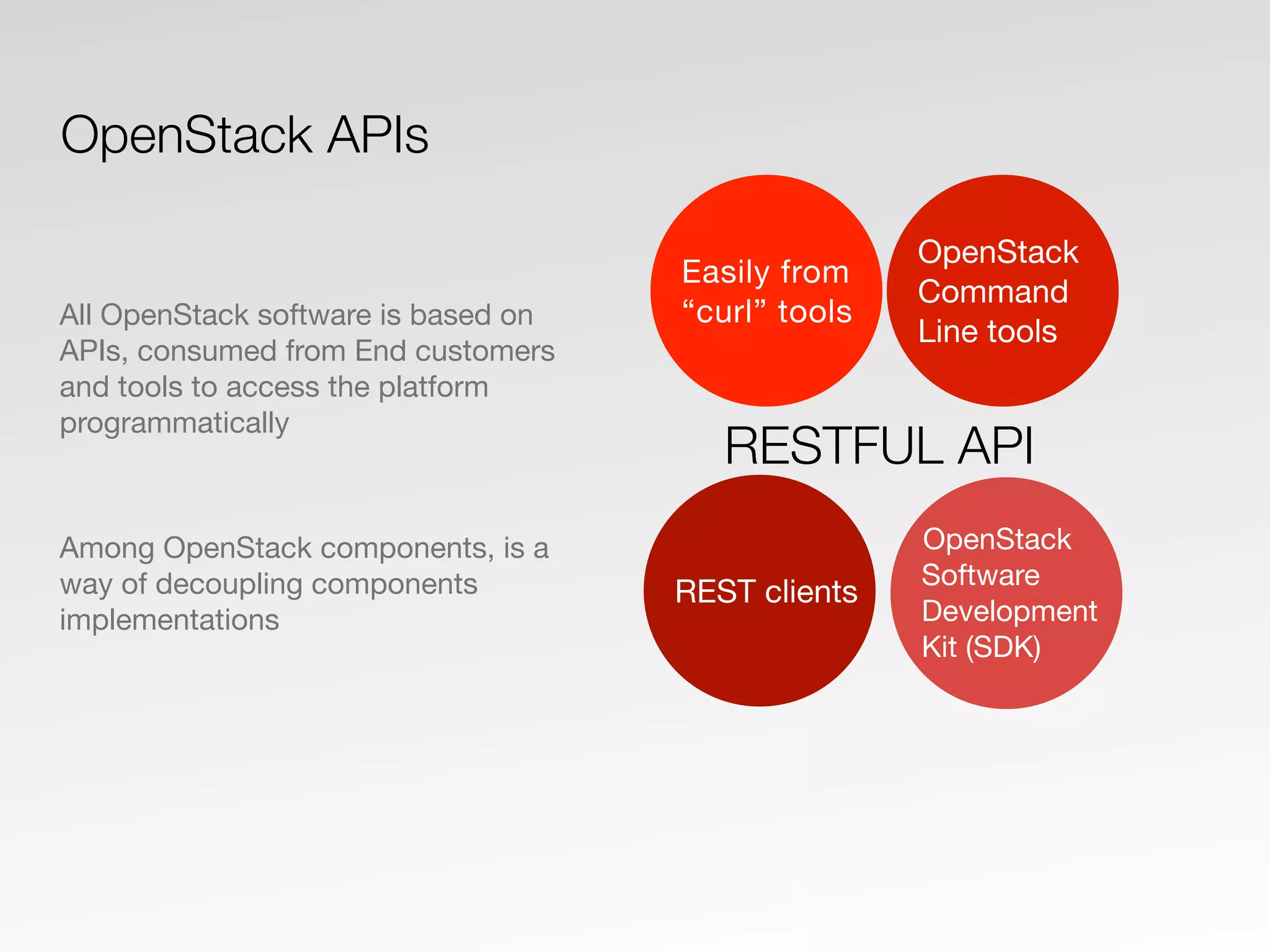
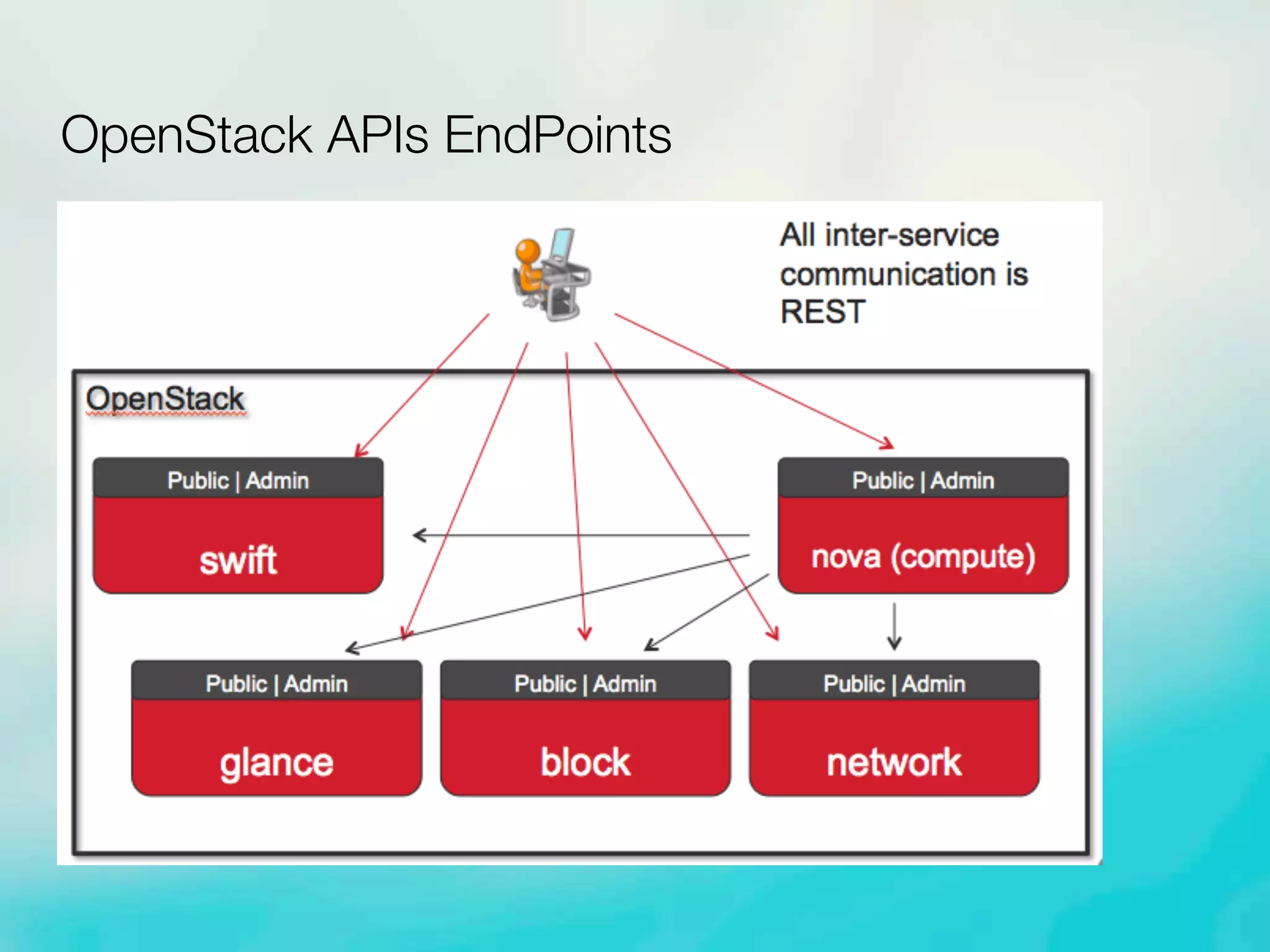
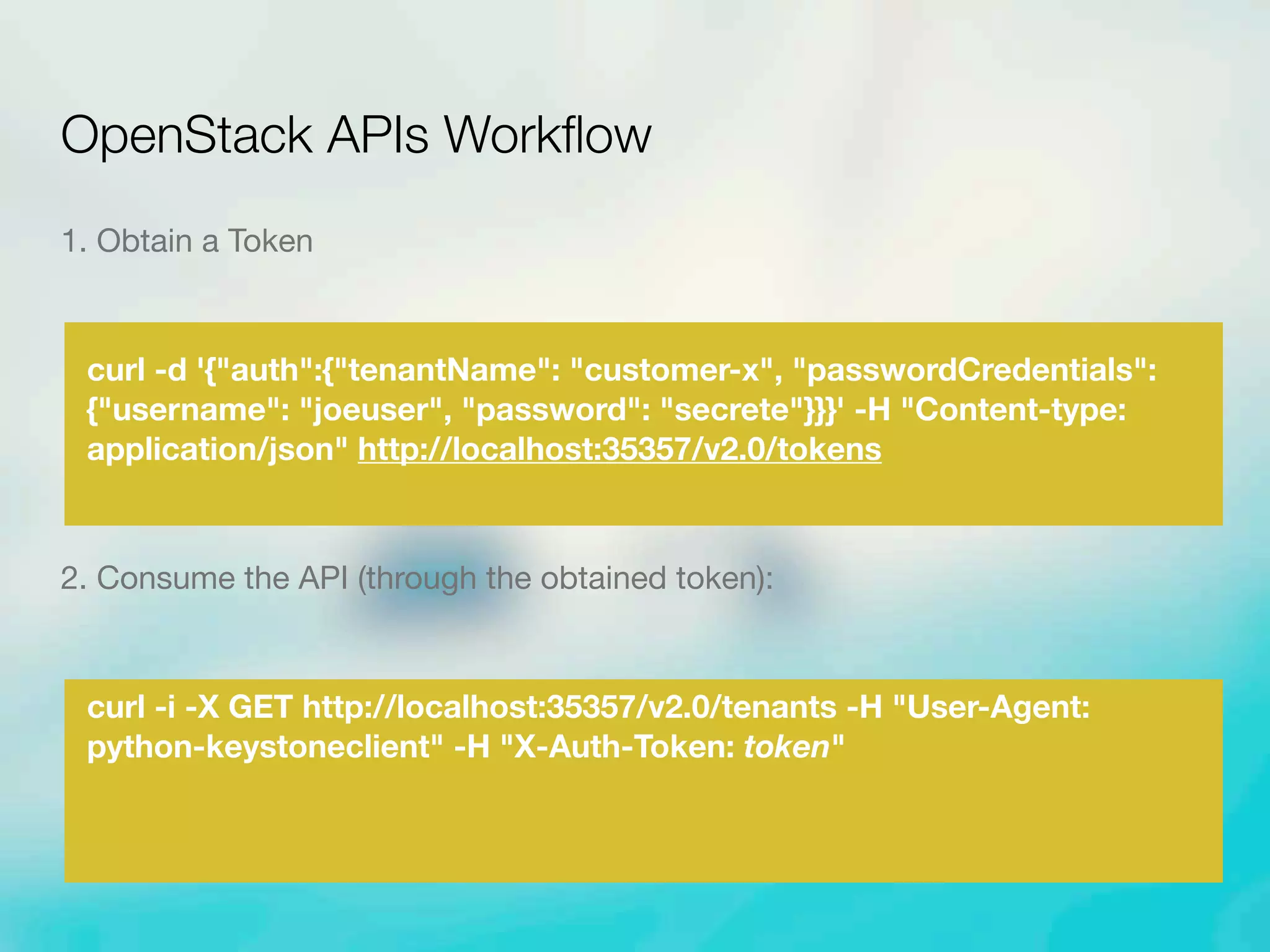
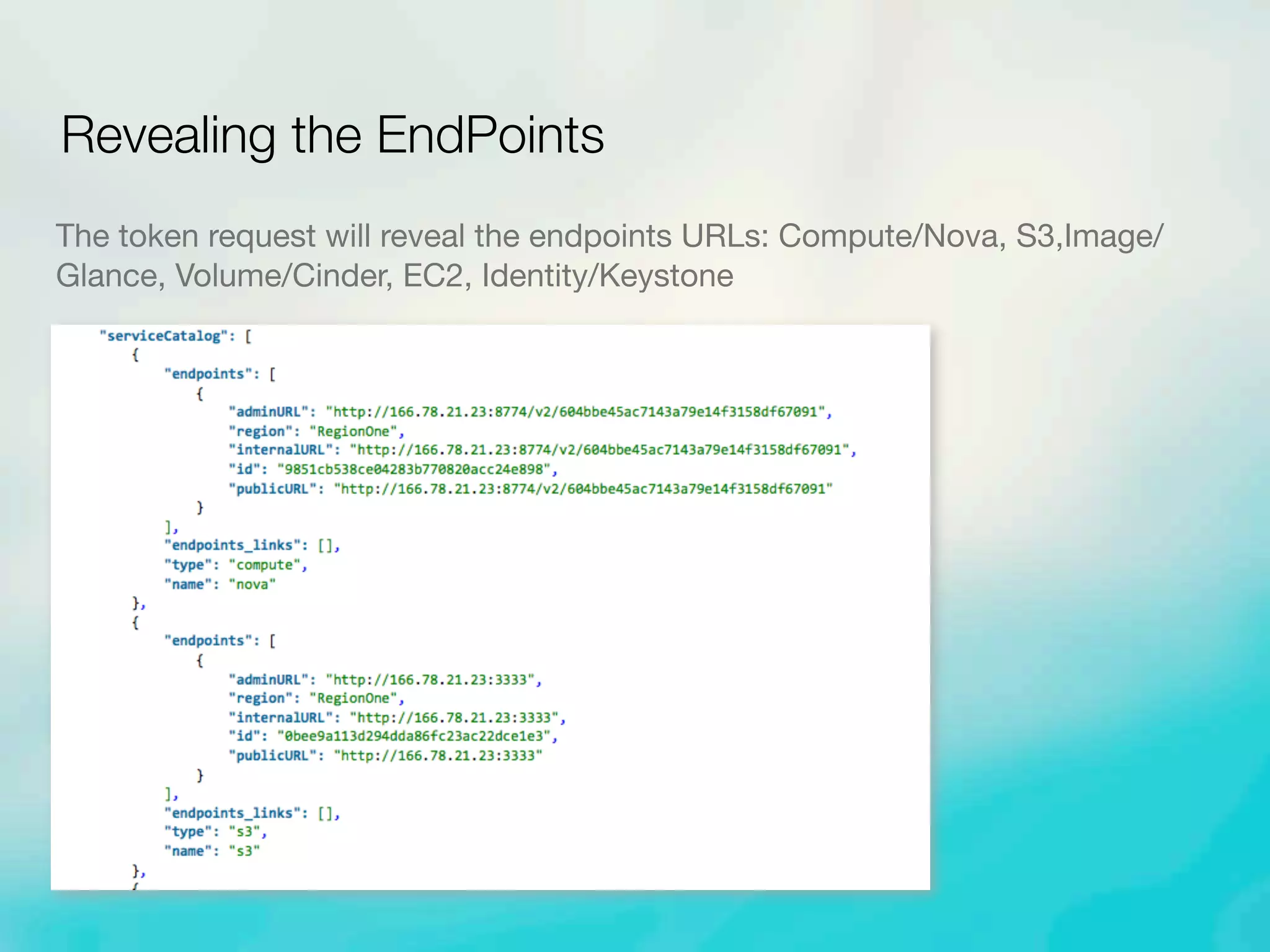
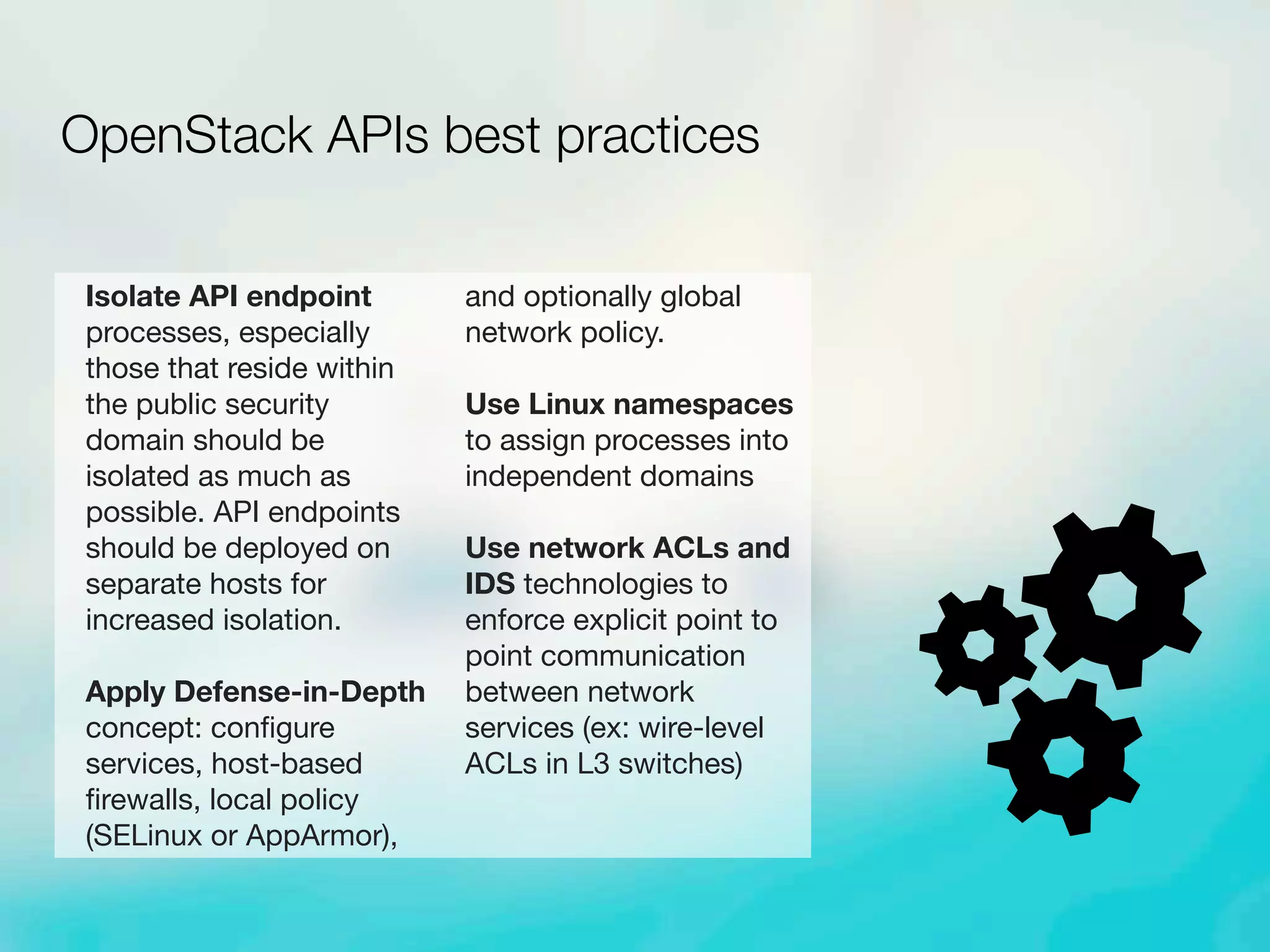
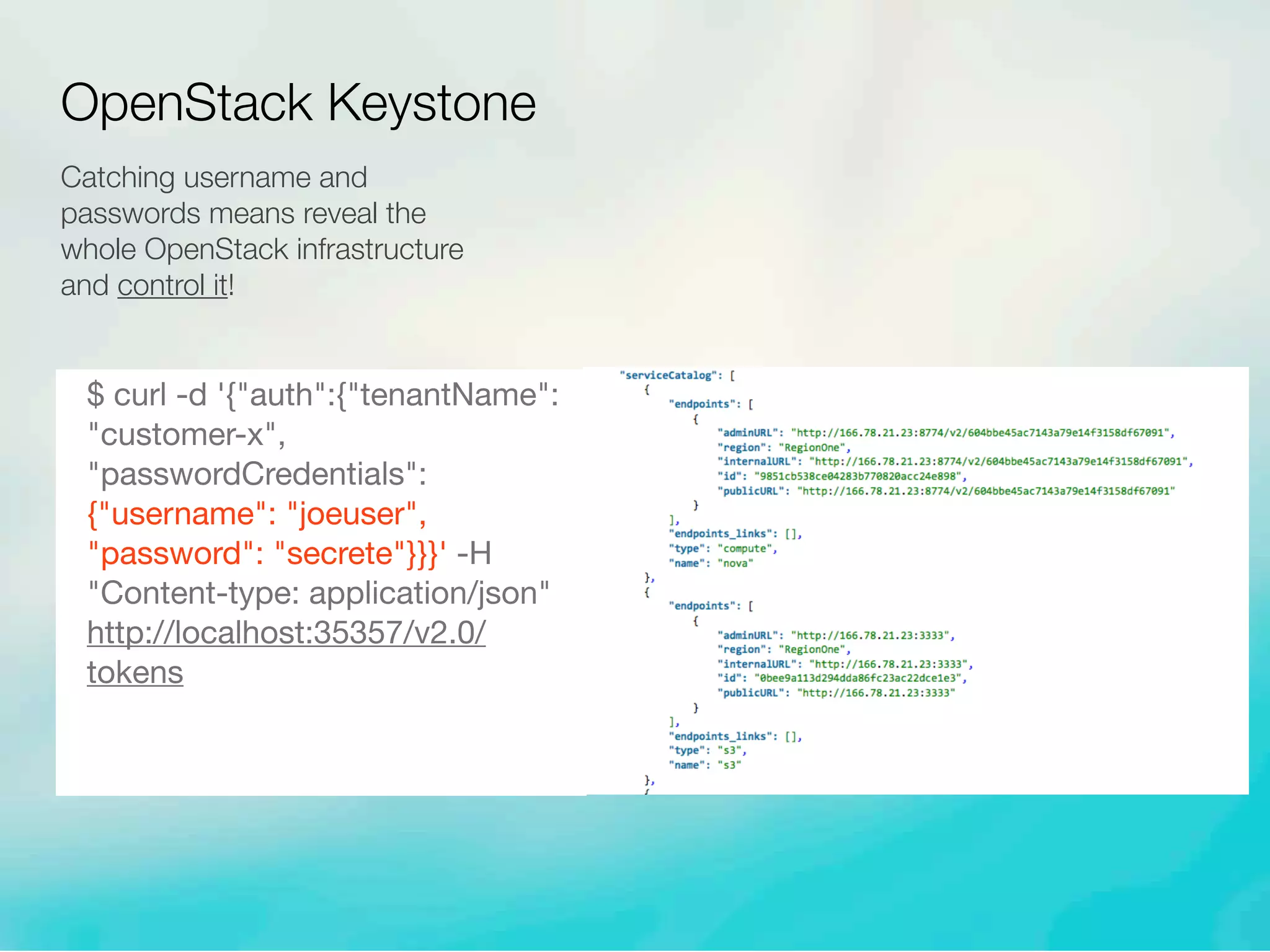
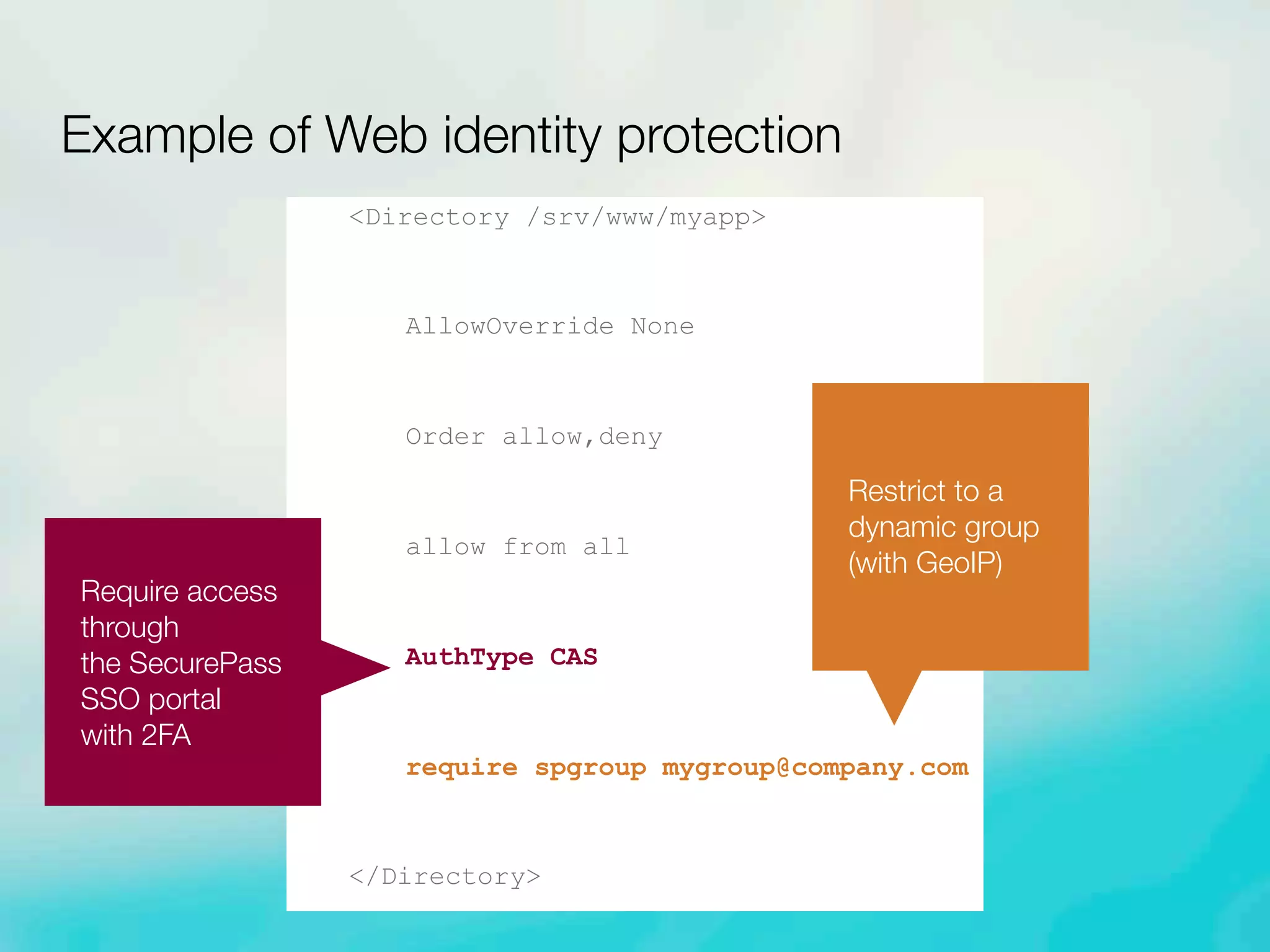
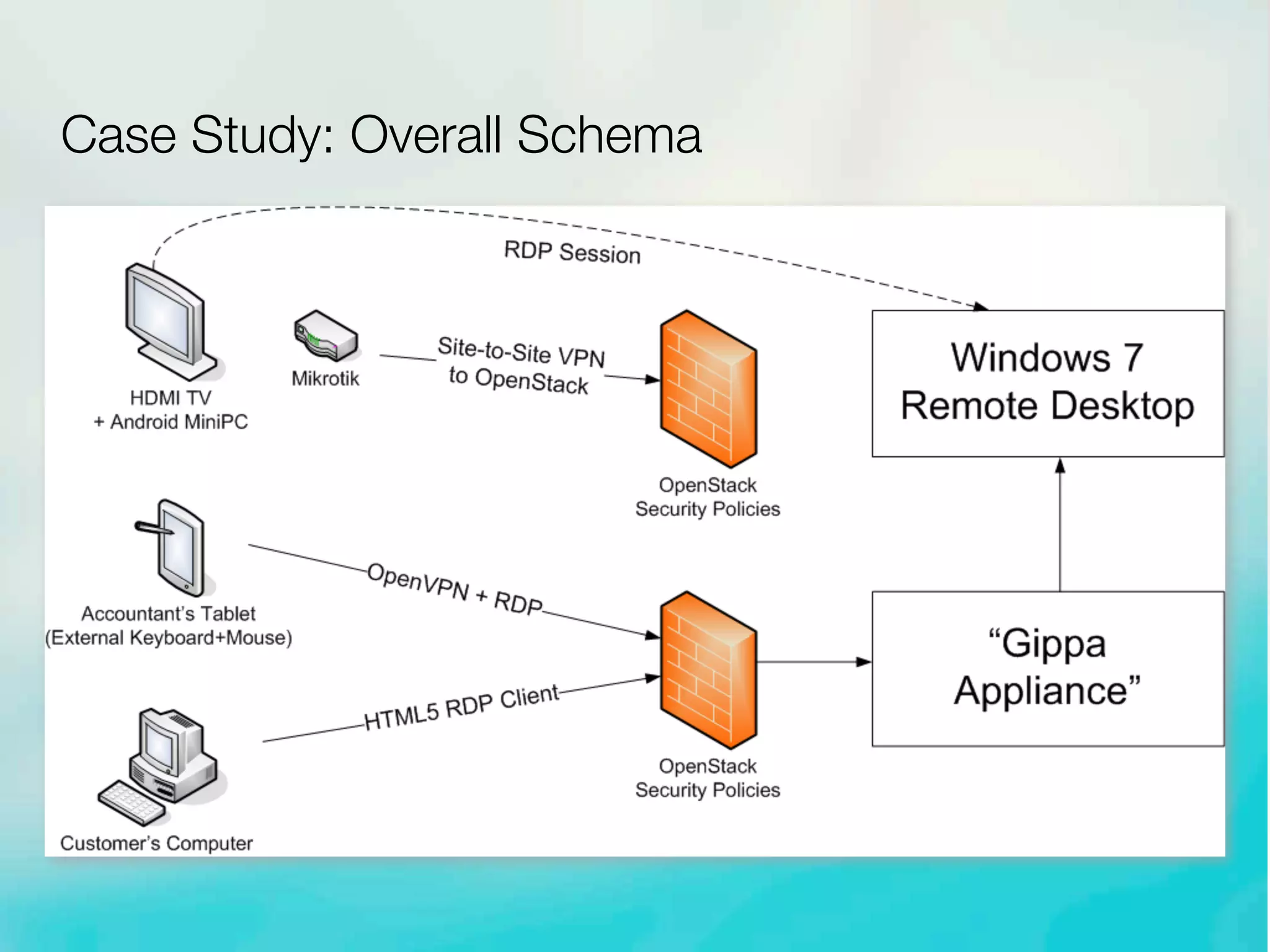
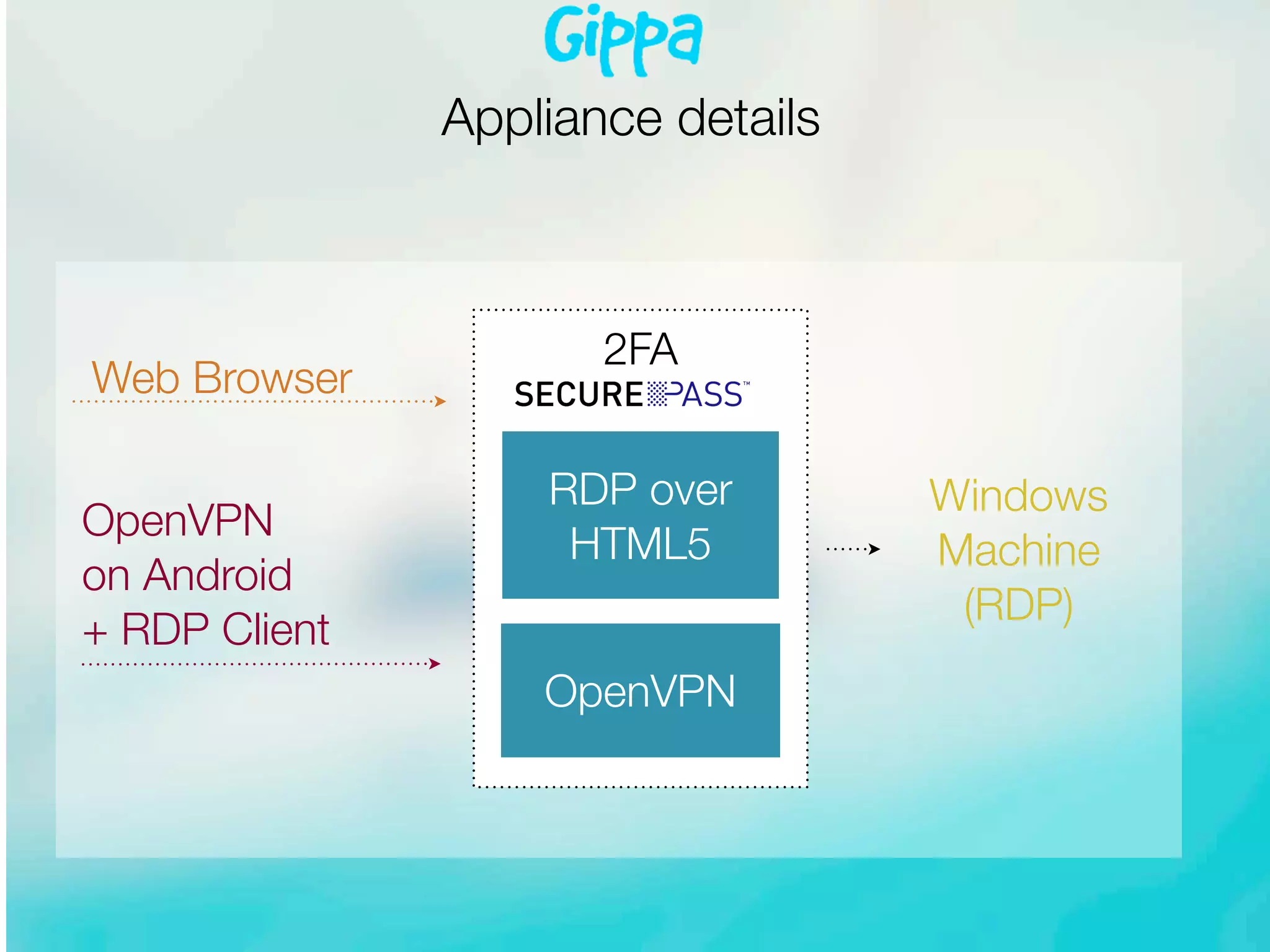
The document discusses enhancing cloud security in OpenStack environments, emphasizing that user identity has become the ultimate perimeter in distributed models. It details various security mechanisms, such as network namespaces and identity management through OpenStack Keystone, while showcasing best practices for API security and identity protection. Additionally, it provides a case study demonstrating a secure virtual desktop solution for remote access, highlighting the importance of multi-factor authentication and VPNs.