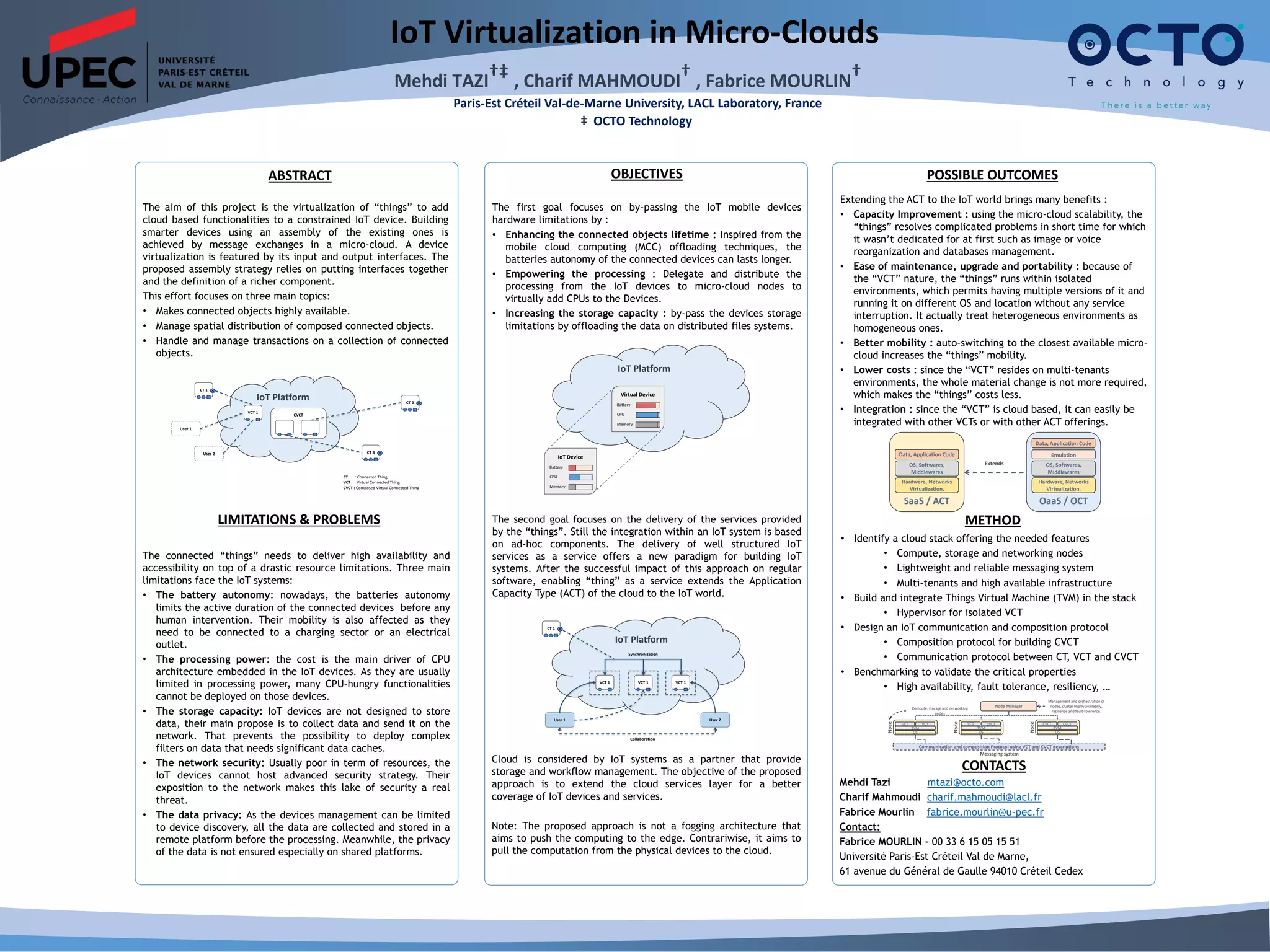
This document proposes a method for virtualizing IoT devices to overcome their limitations in battery life, processing power, storage capacity, and security. It involves assembling existing devices into a "micro-cloud" where their inputs and outputs are connected. This allows offloading processing and storage to the micro-cloud to extend battery life and add capabilities. It aims to deliver high availability and accessibility for constrained IoT devices by managing compositions of virtualized connected things in the micro-cloud.