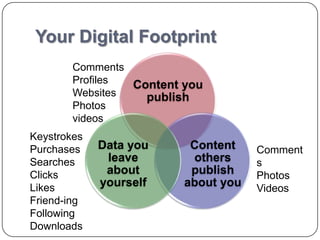
This document provides an overview of digital footprints and how to manage your online privacy. It defines a digital footprint as the collection of information people leave online through activities like social media use, comments, photos and purchases. The presentation discusses how to discover your own digital trail, clean up your online presence by removing unused accounts and content, and conduct privacy audits. It also offers tips for building a positive digital identity through blogs, profiles and online content creation. Sample student activities are provided to help teach these digital citizenship concepts.