Embed presentation









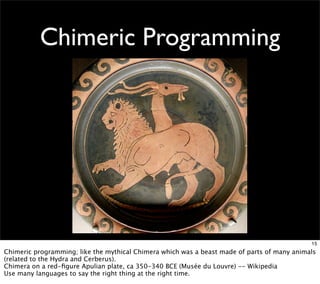
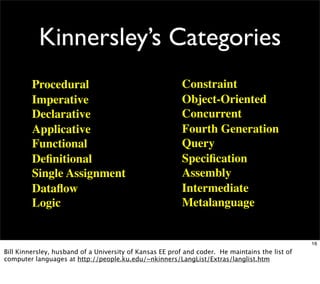
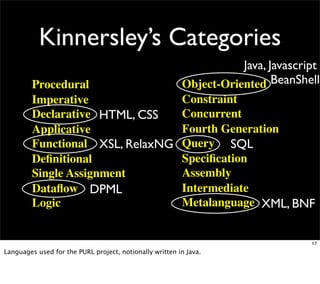



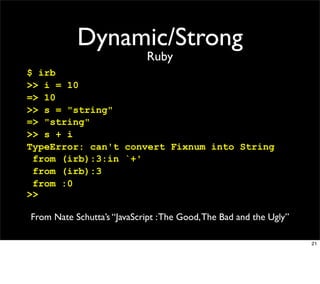


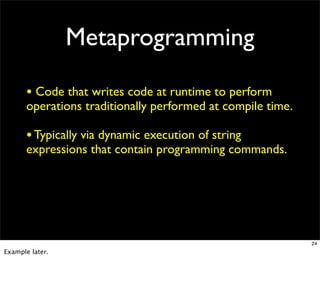
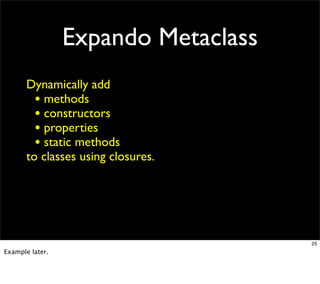
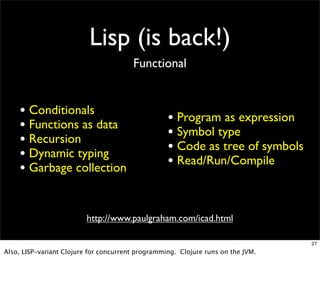
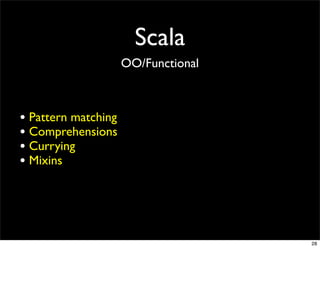


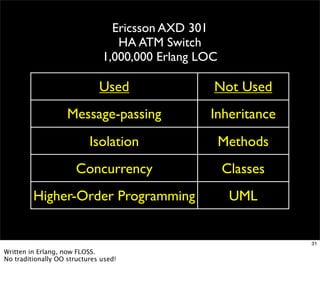










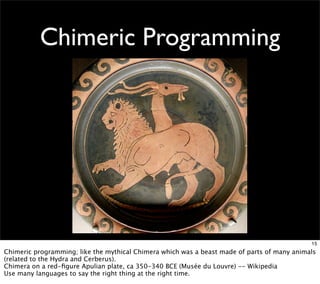
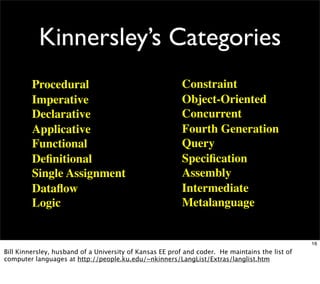
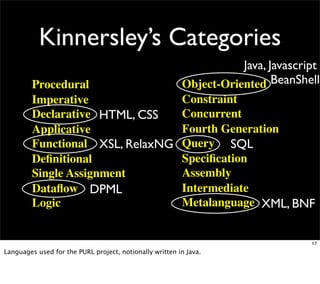
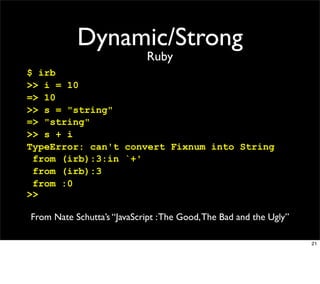
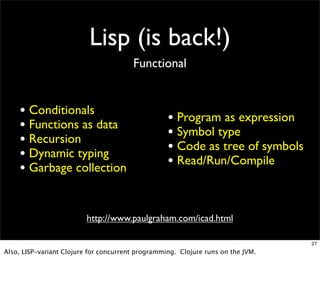
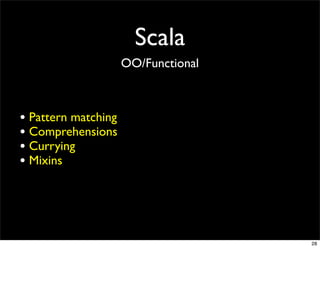
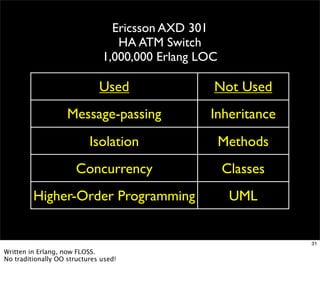
This document discusses various programming languages and concepts. It begins by looking at the popularity of languages like Java, C/C++, and Python. It then examines different language features and paradigms, including dynamic vs static typing, closures, metaprogramming, and more. The document also profiles several important languages such as Lisp, Scala, Haskell, Erlang, JavaScript, Ruby, and Groovy. It emphasizes that no single language can satisfy all needs and that the appropriate language depends on the task.