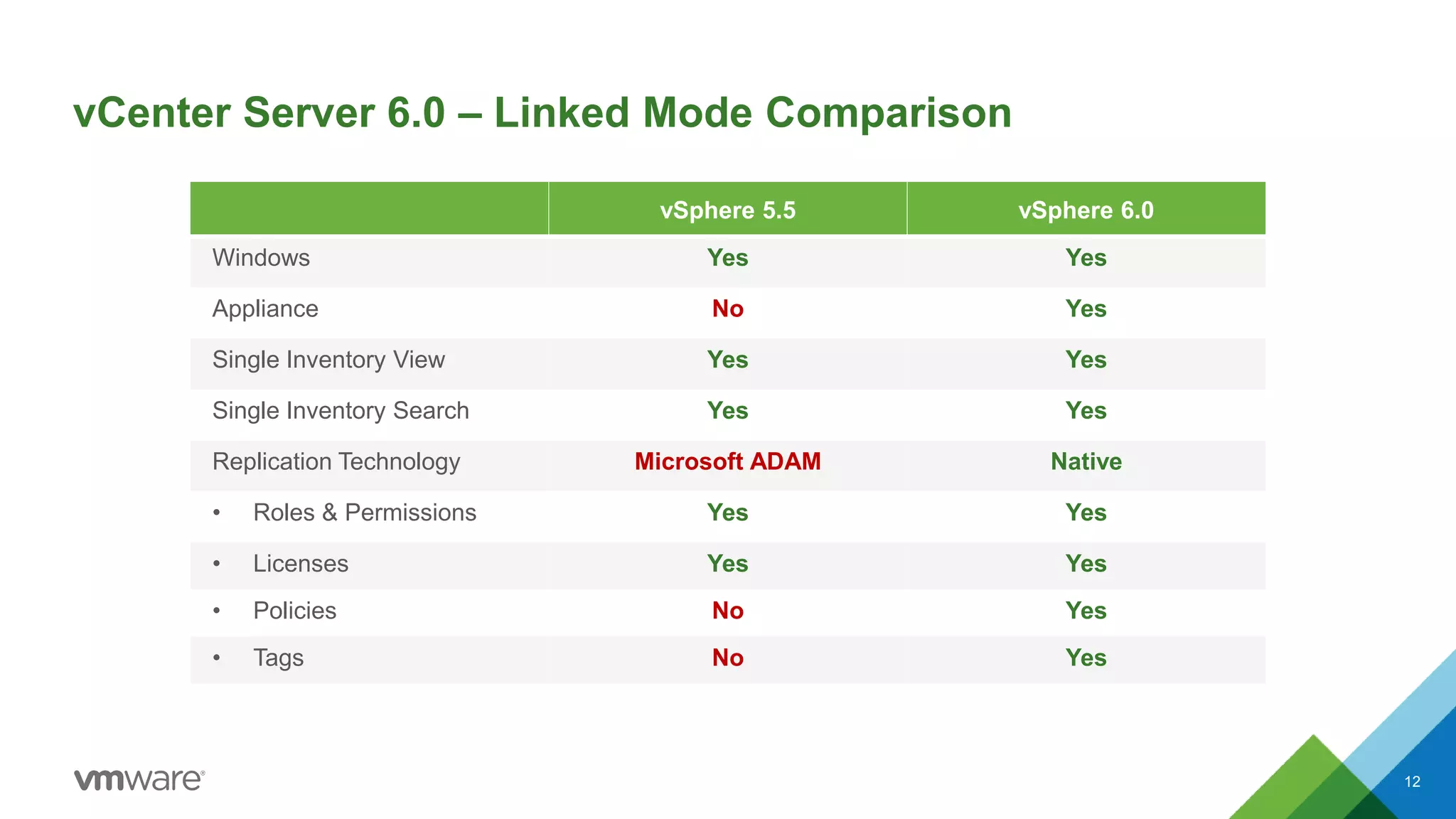
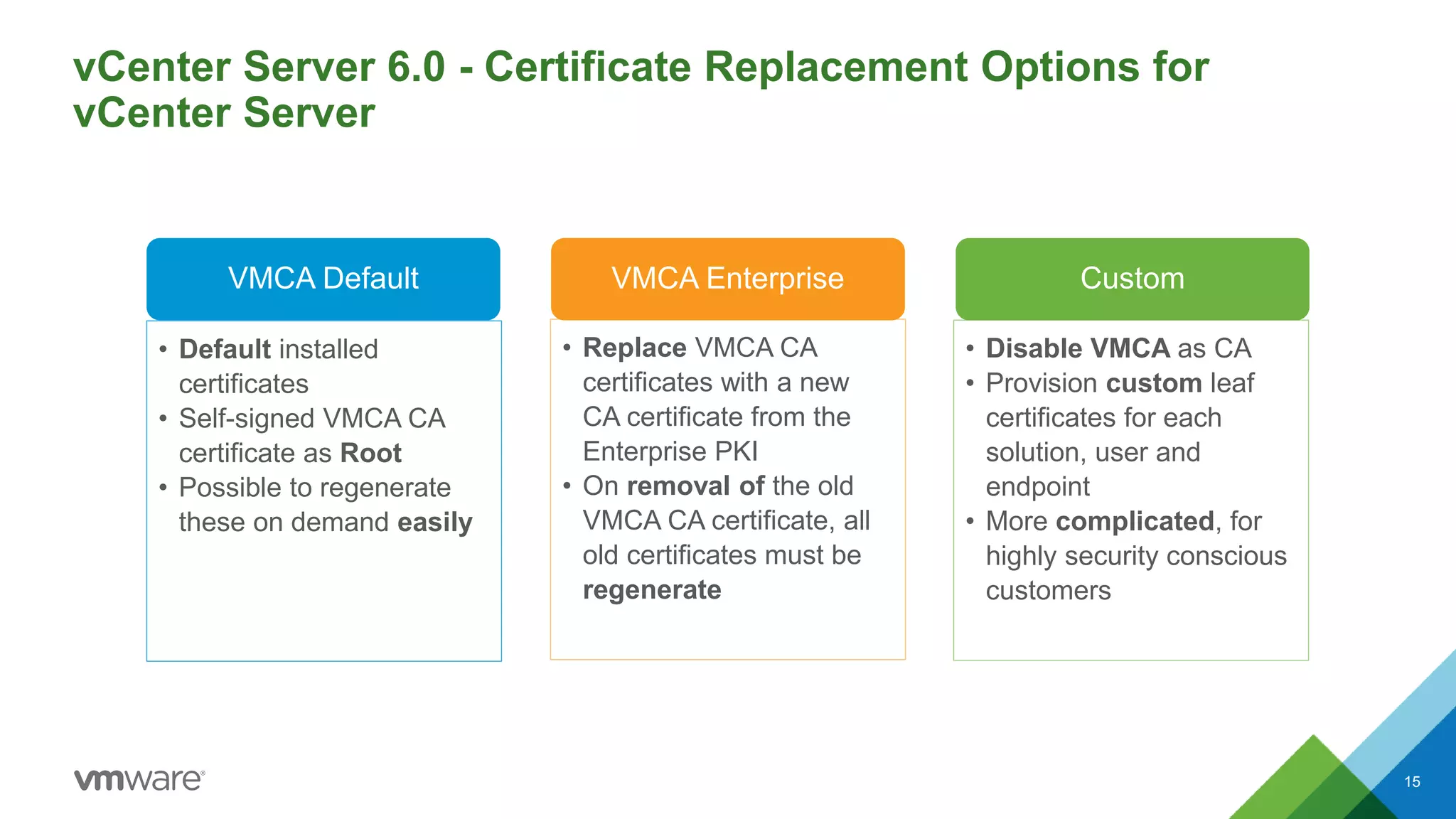
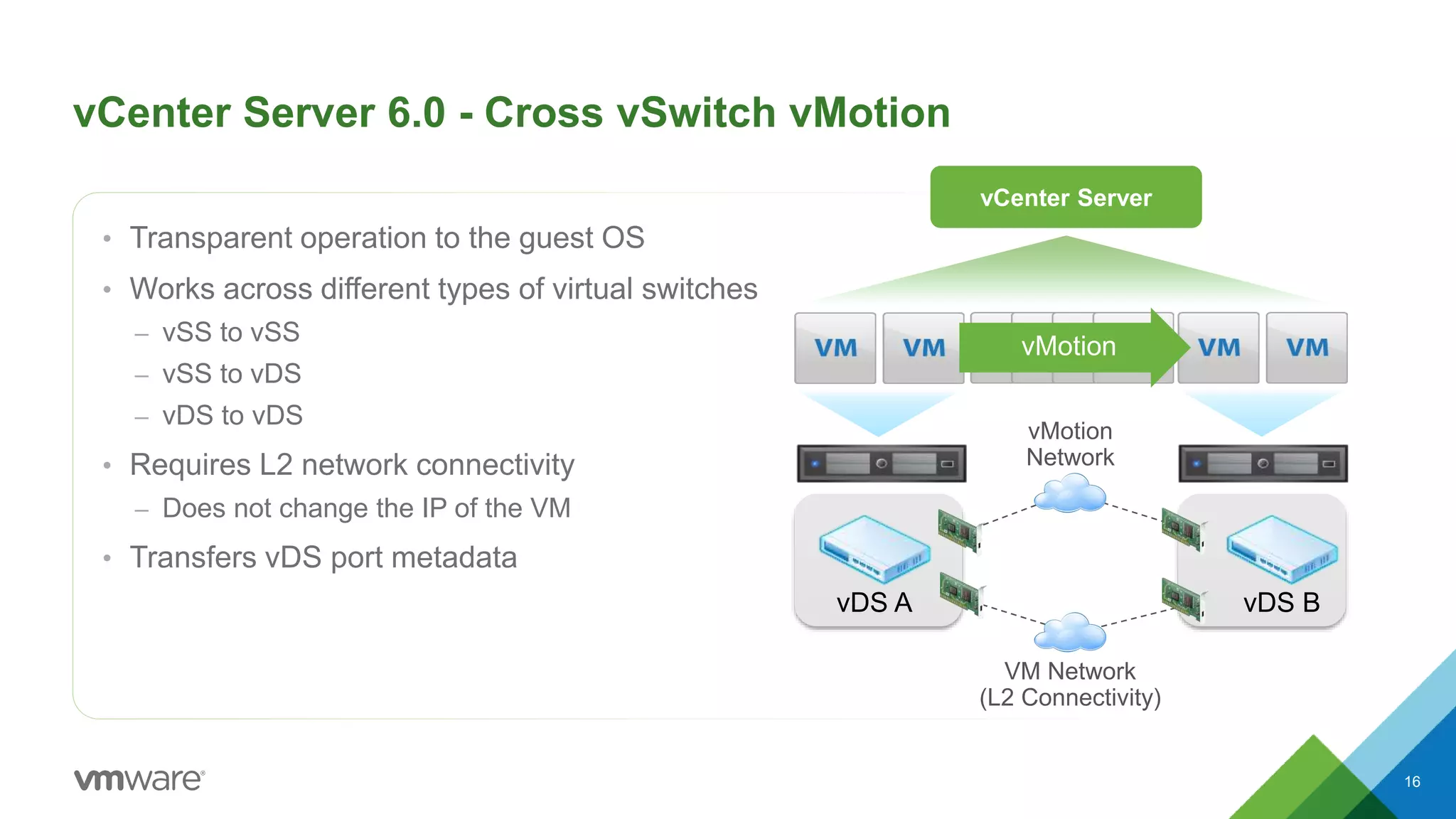
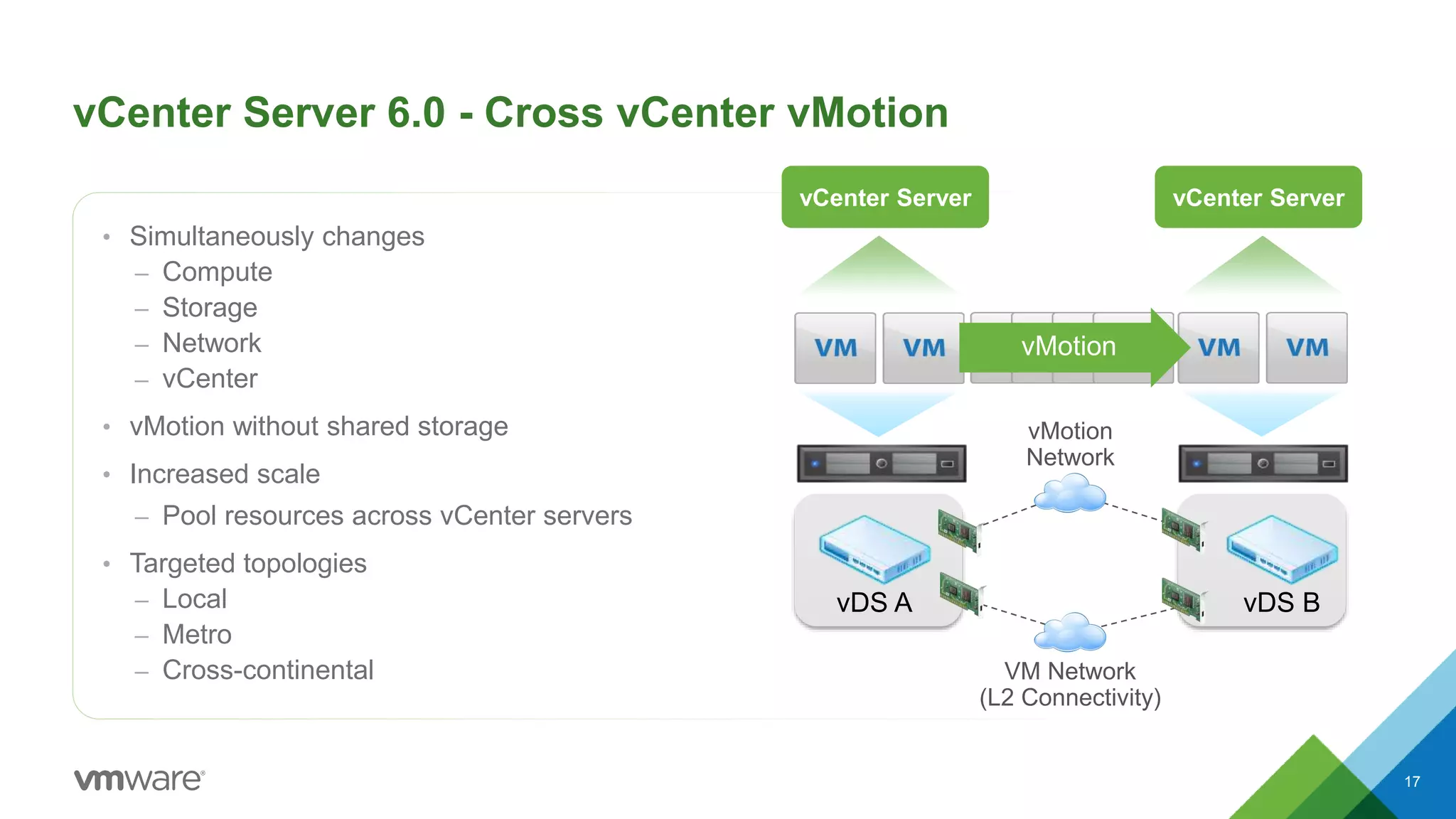
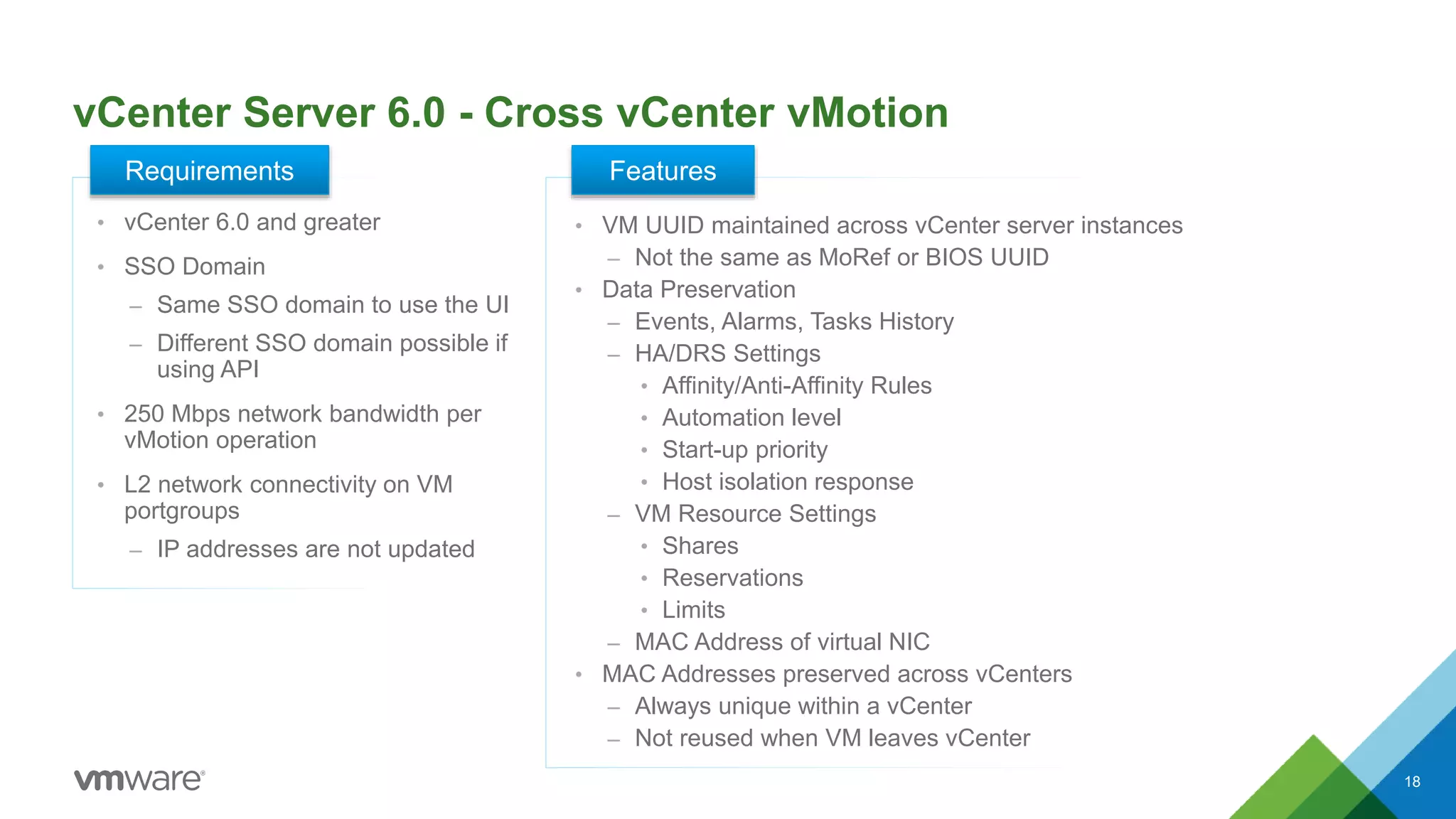
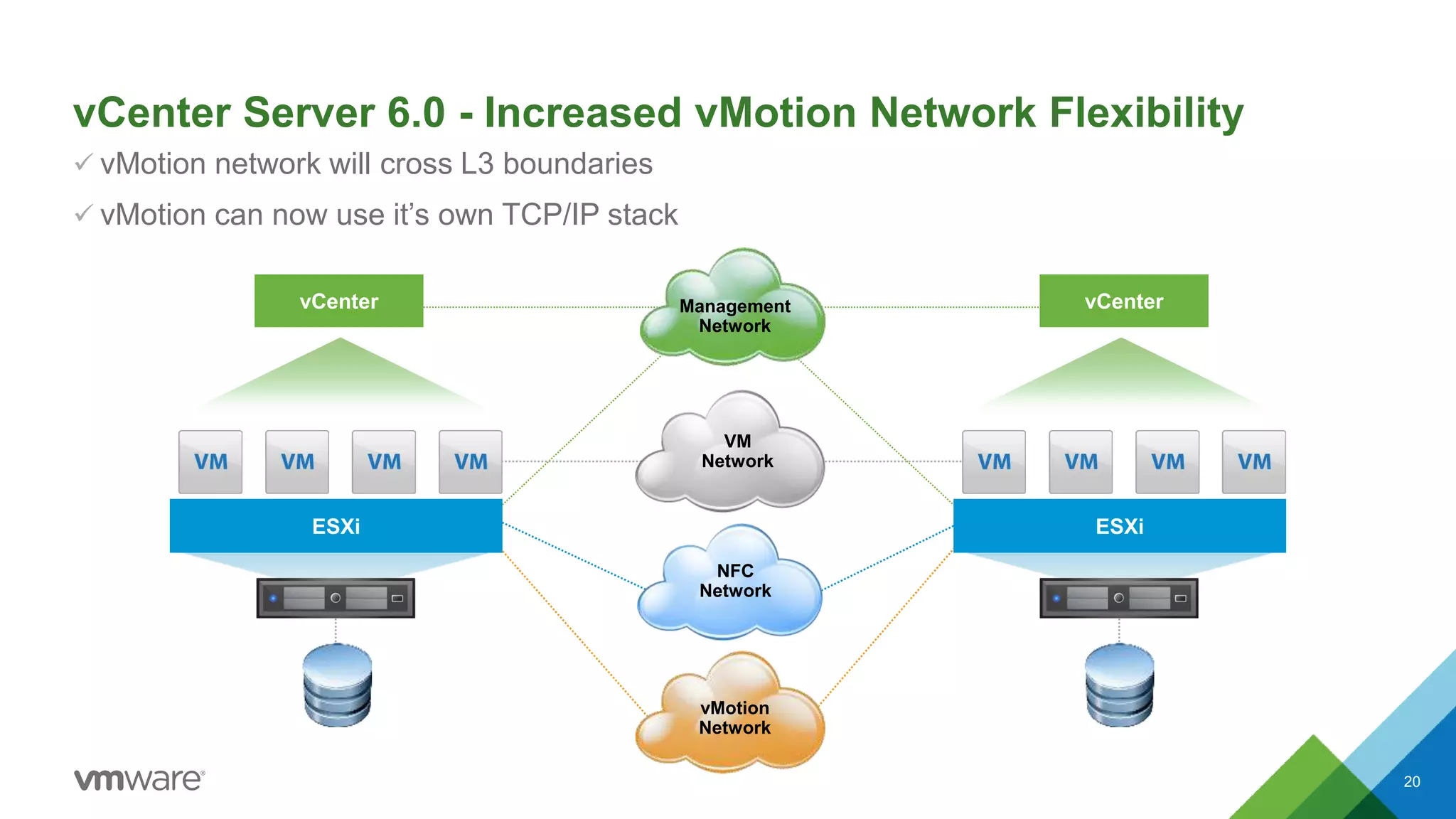
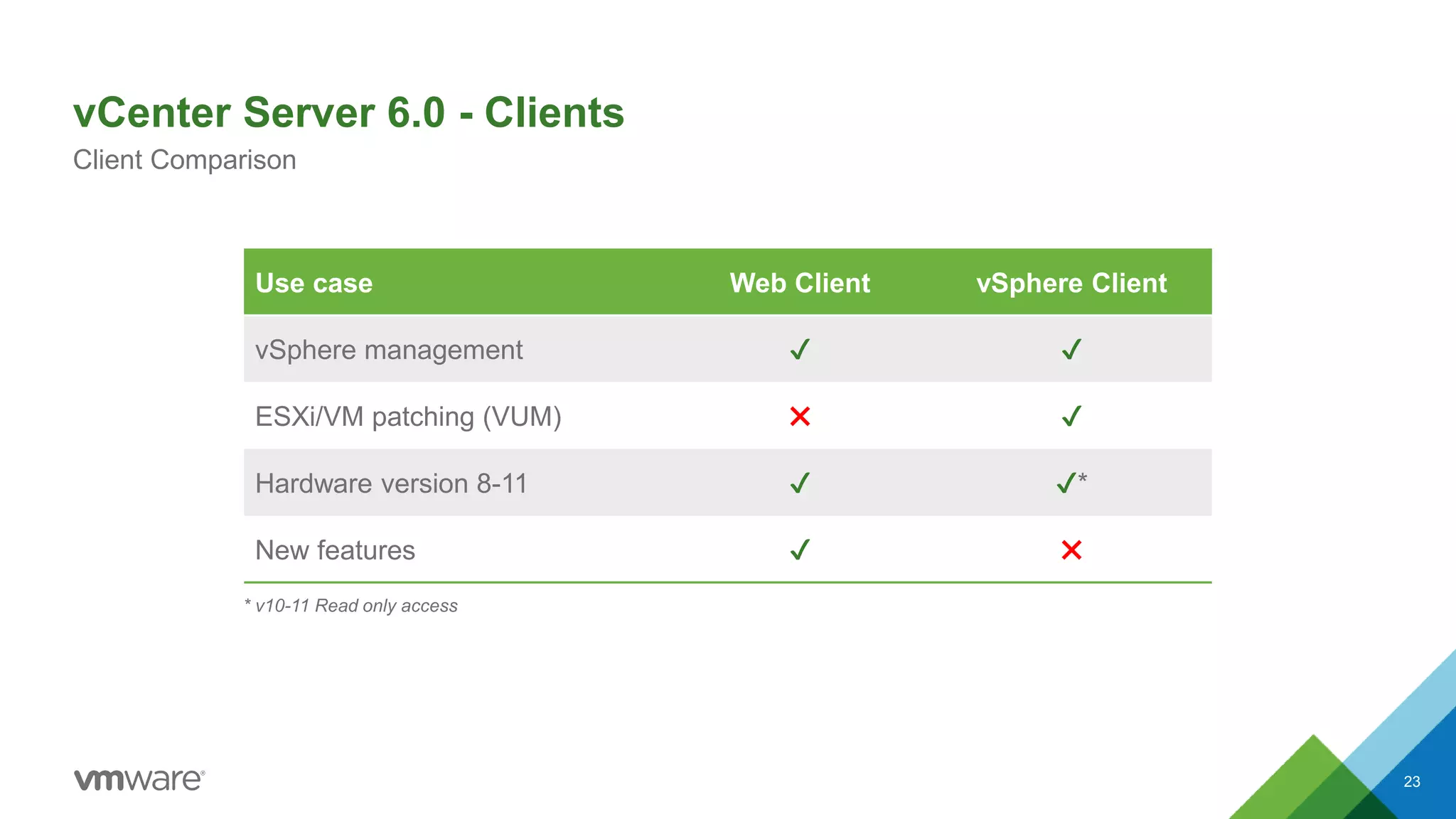
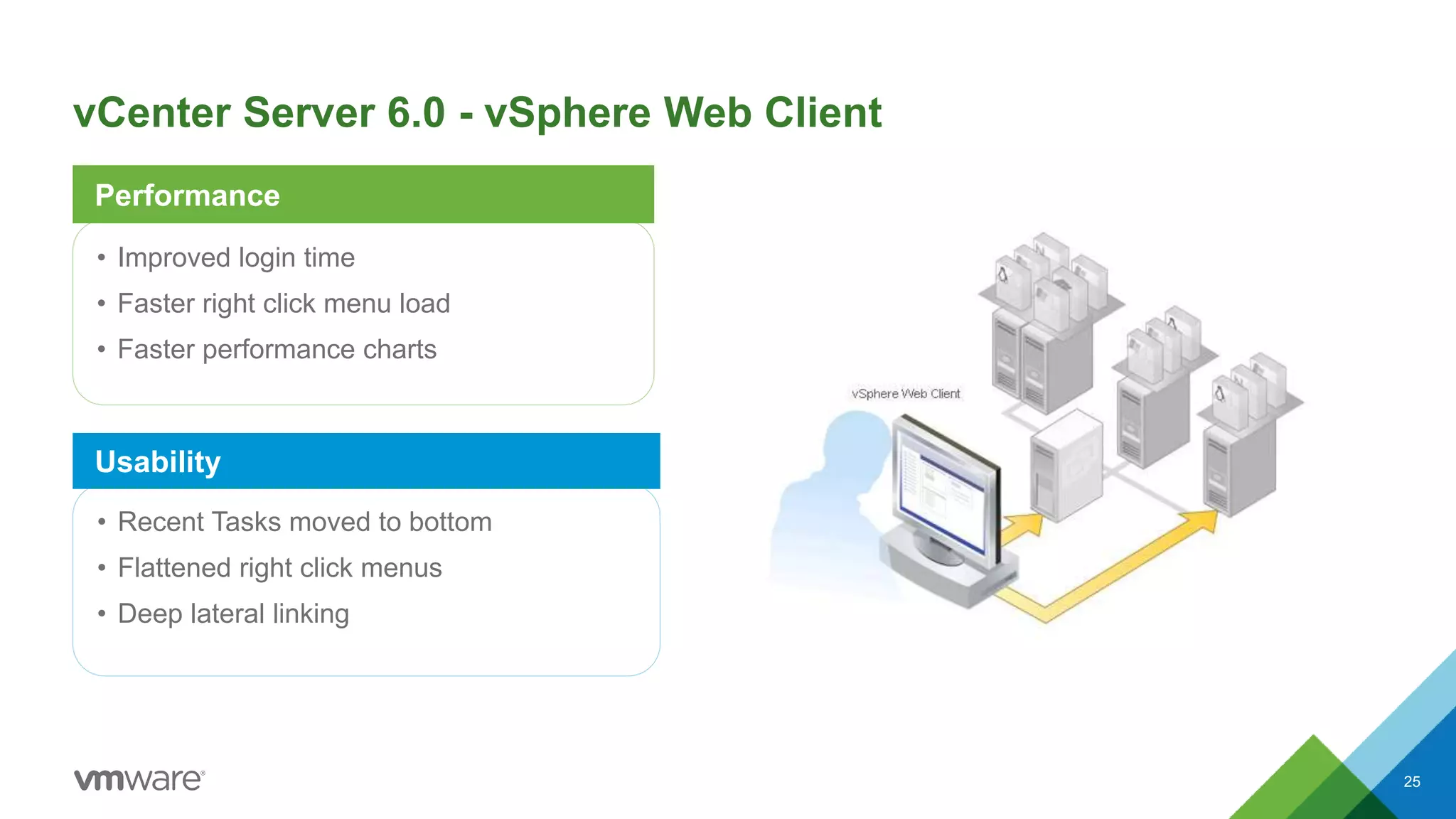
VMware vSphere 6.0 includes several new and enhanced platform and management features. Key updates include increased scalability limits, improved ESXi account management, enhanced Microsoft clustering support, and new certificate lifecycle management capabilities. The vCenter Server has been improved with a Platform Services Controller, linked mode enhancements, cross-vCenter vMotion, and a redesigned web client. Networking features in vSphere 6.0 focus on increased flexibility and guaranteed bandwidth controls.





![Platform Features - Improved Auditability of ESXi Admin Actions
• Prior to 6.0, actions taken at the vCenter level by a named user would show up in ESXi logs with the “vpxuser”
username.
– [user=vpxuser]
– This made for difficult forensic tracking of user actions.
• In 6.0, all actions taken at vCenter against an ESXi server now show up in the ESXi logs with the vCenter
username
– [user=vpxuser:CORPAdministrator]
7](https://image.slidesharecdn.com/whatsnewvsphere6-160214055158/75/Whats-new-v-sphere-6-7-2048.jpg)