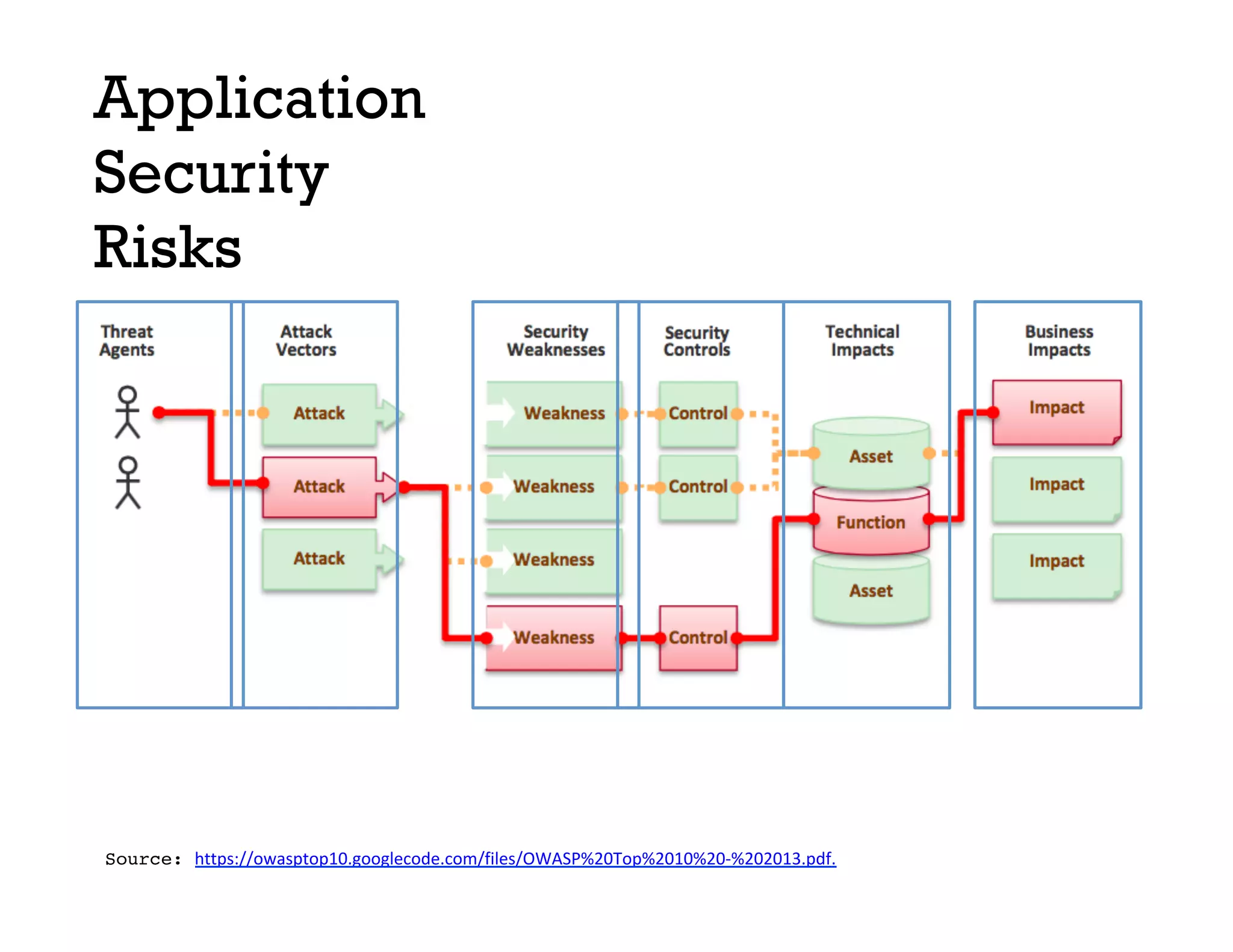
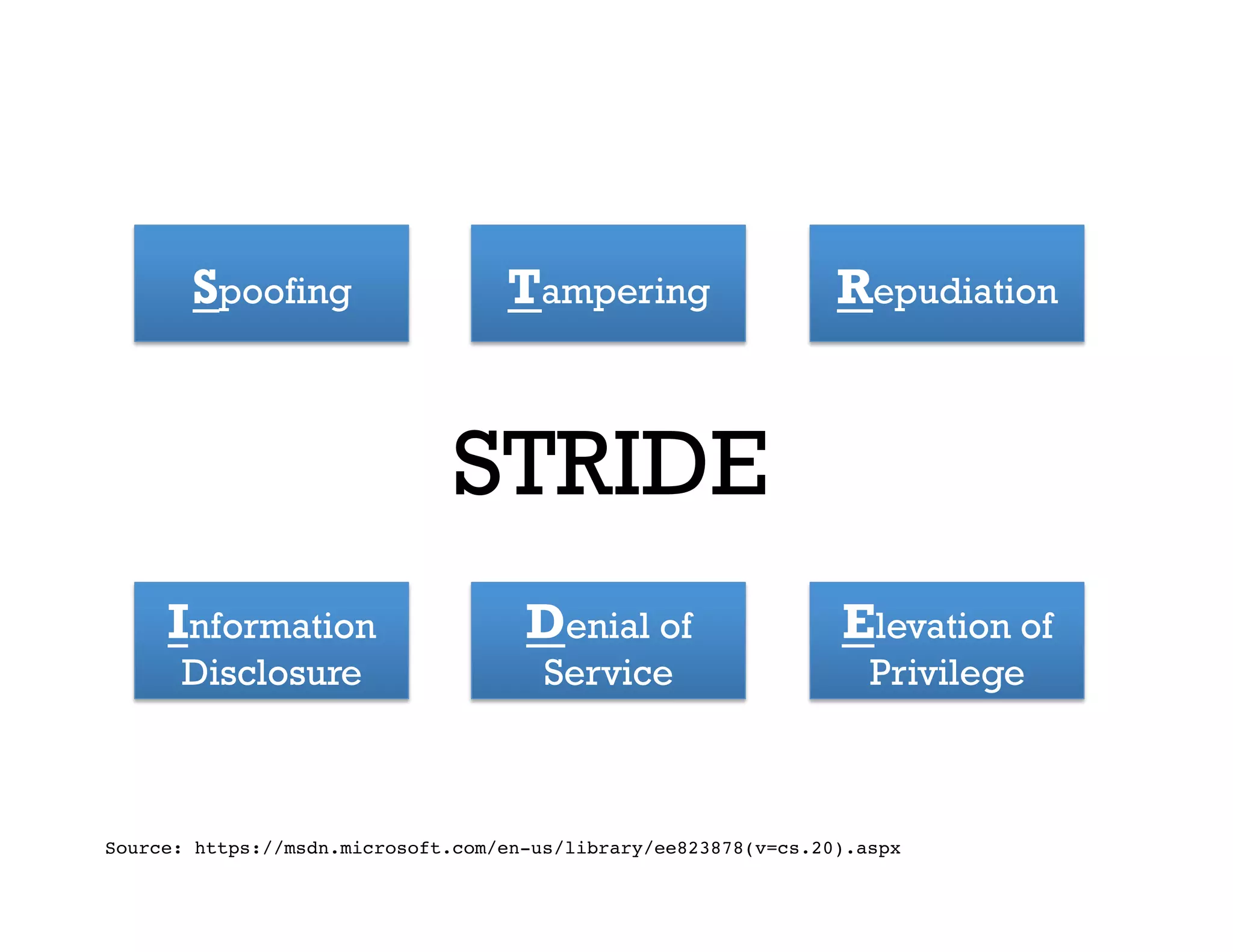
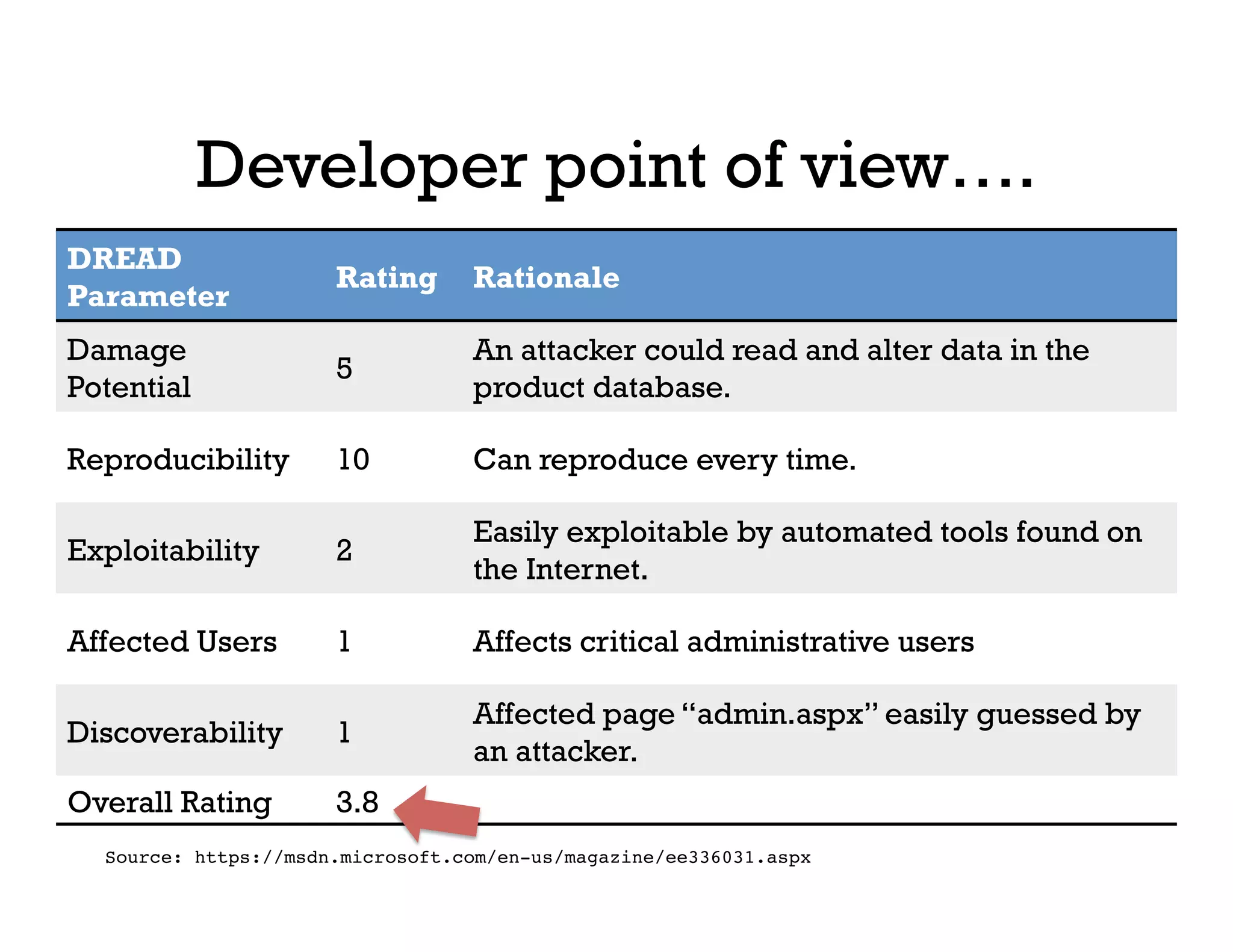
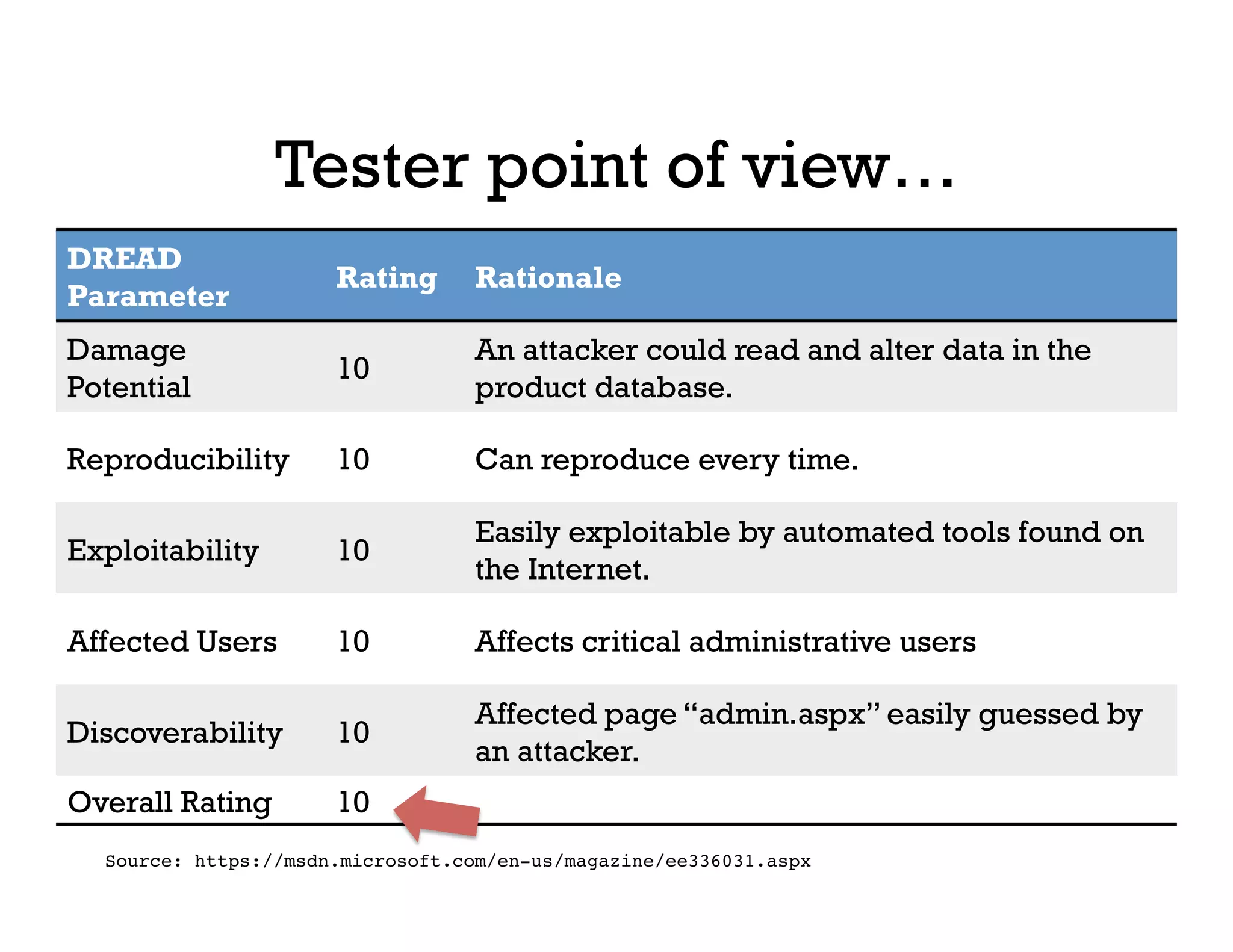
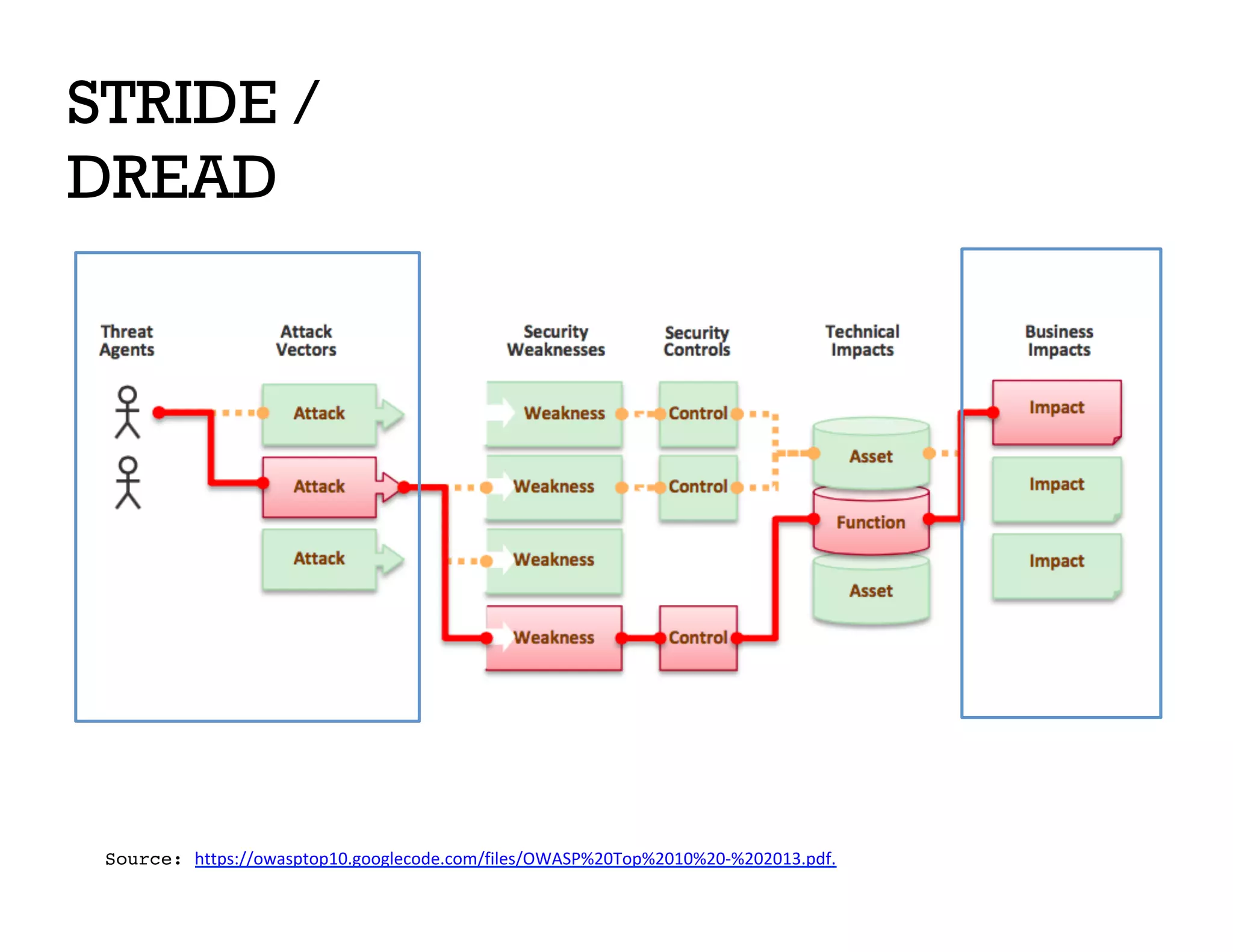
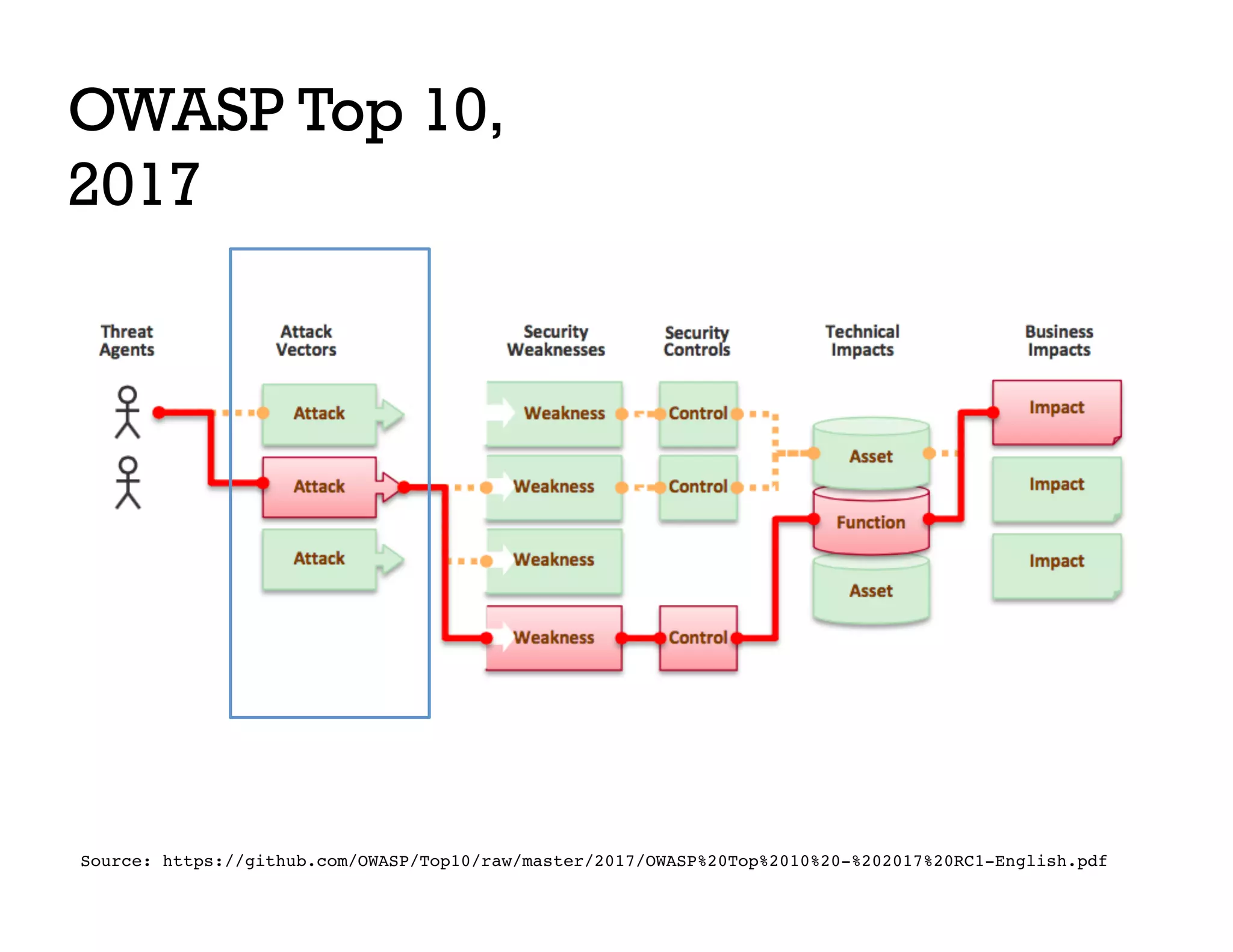
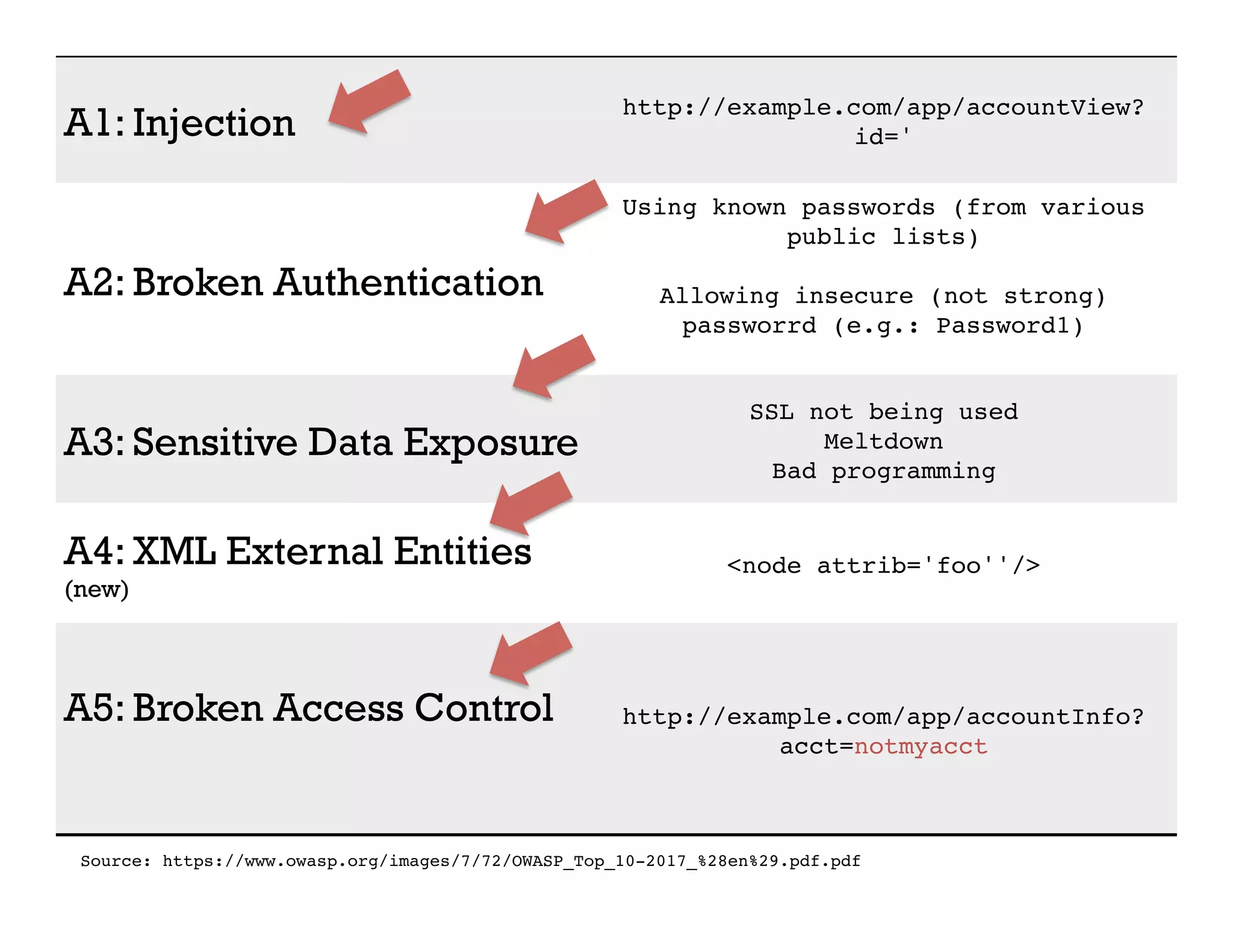
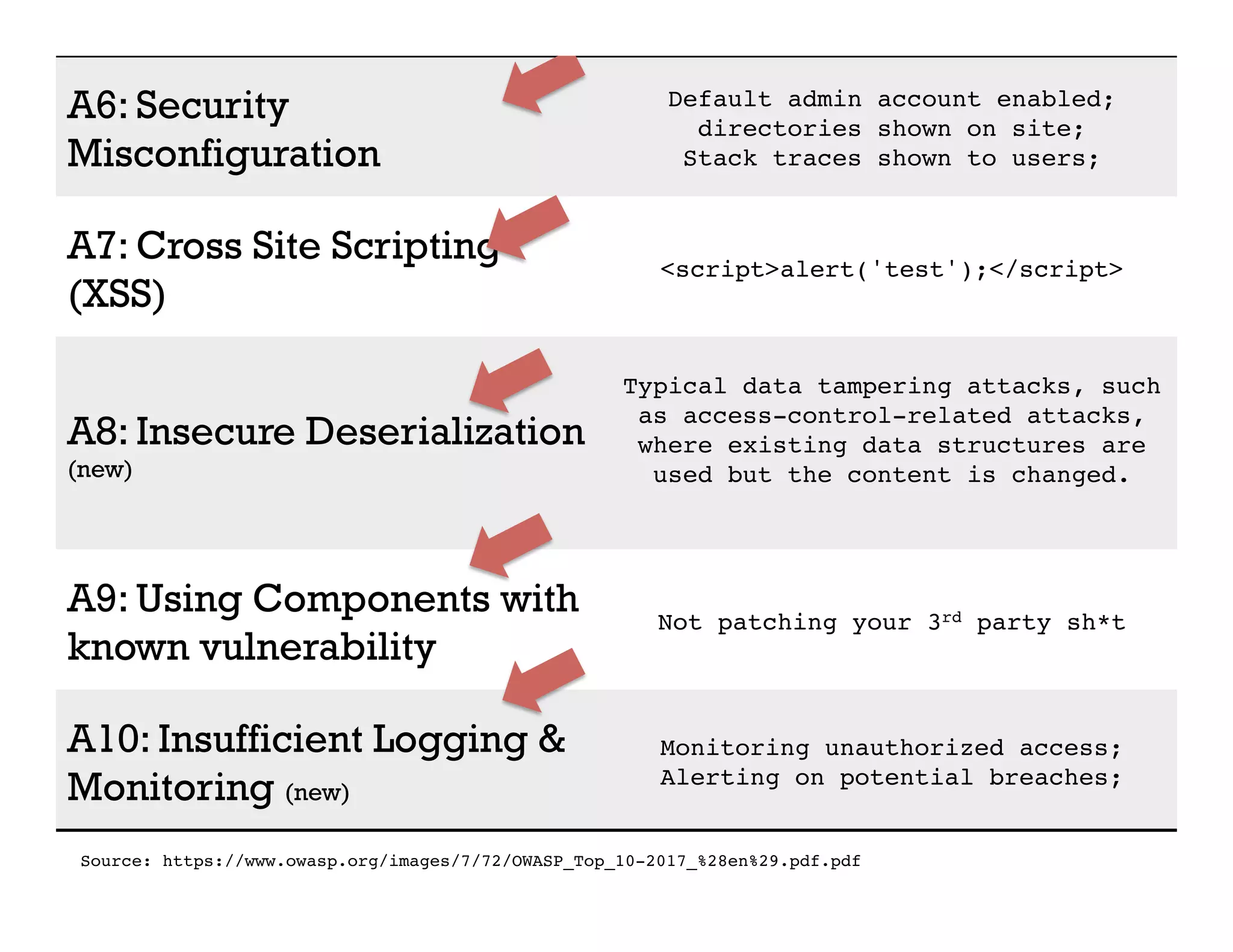
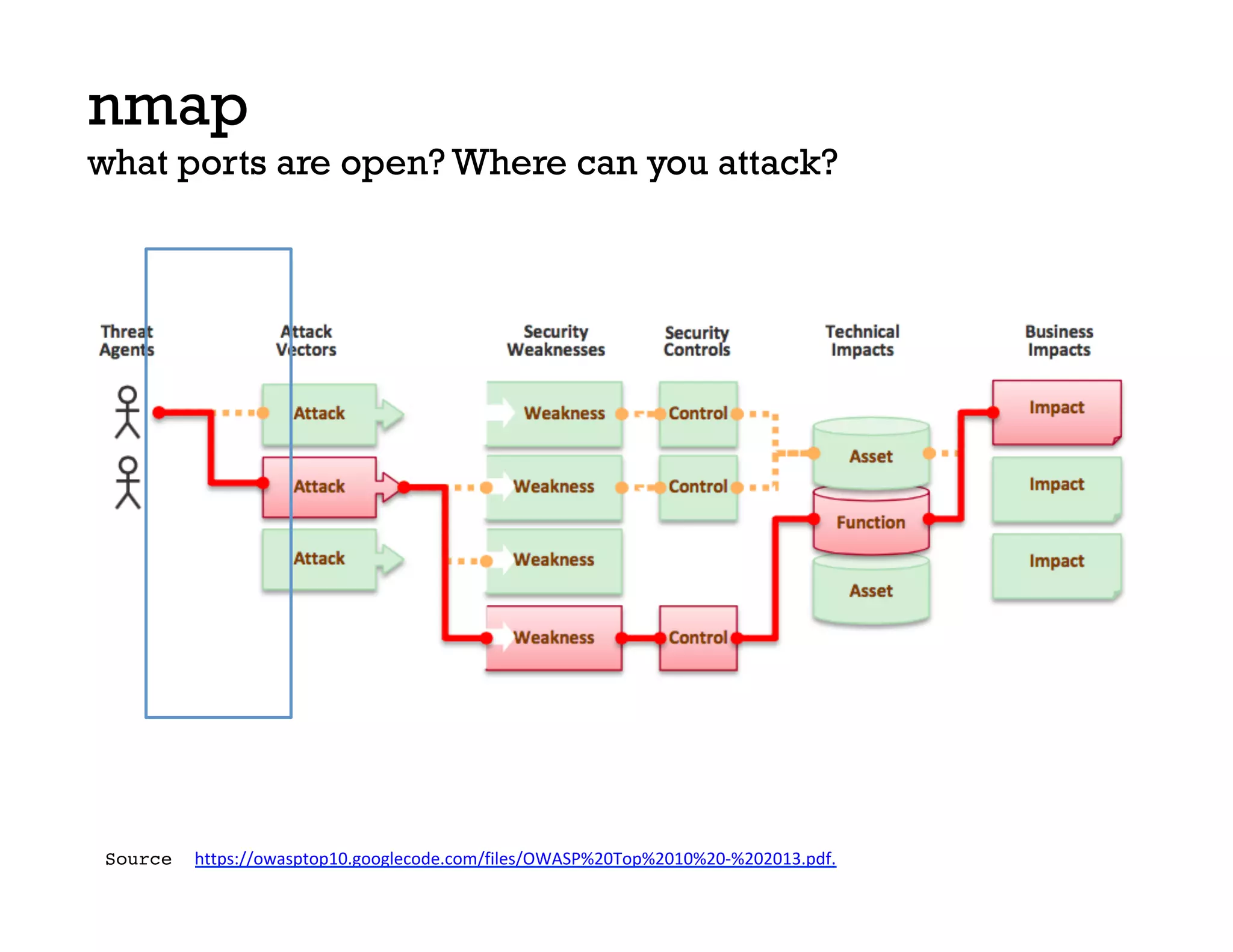
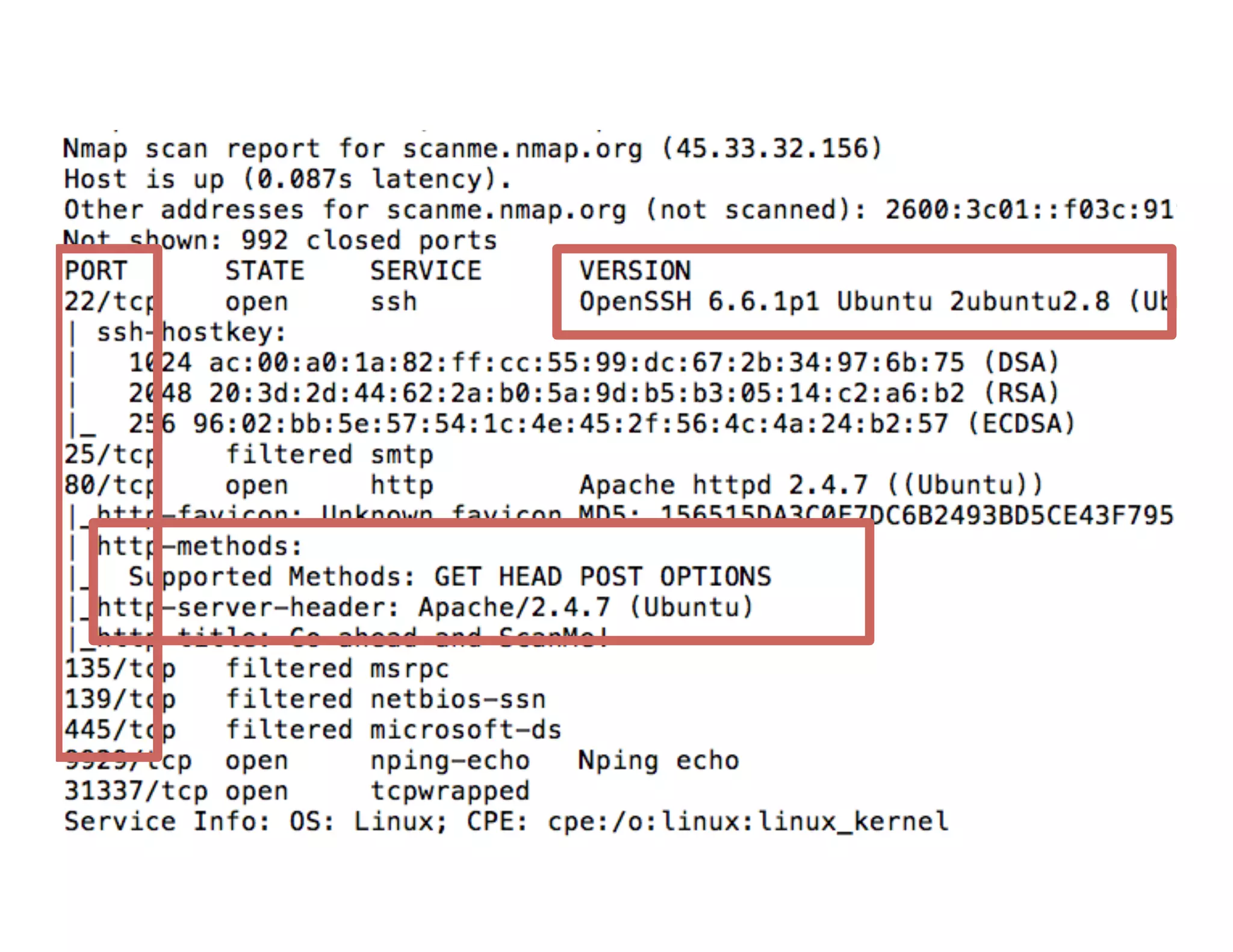
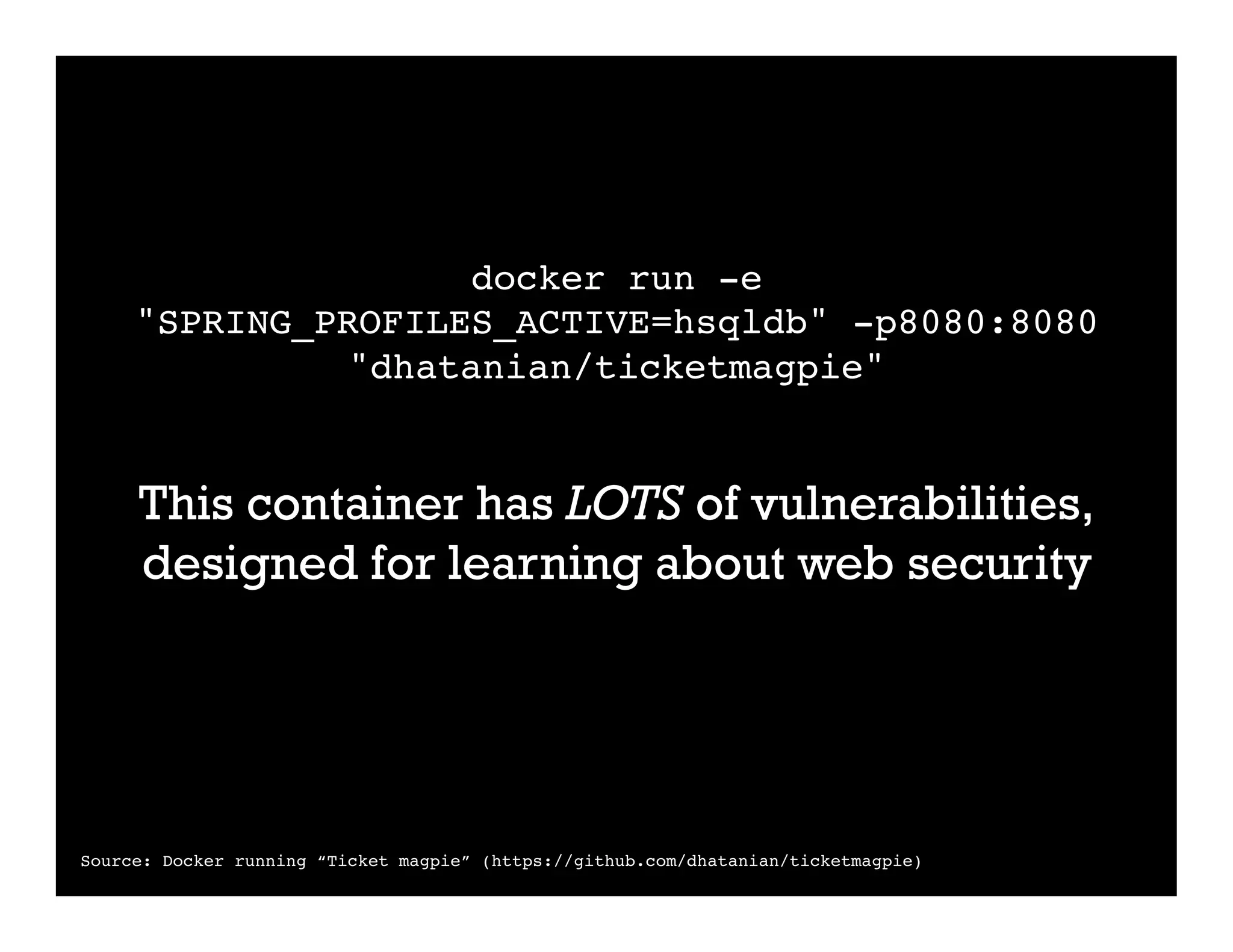
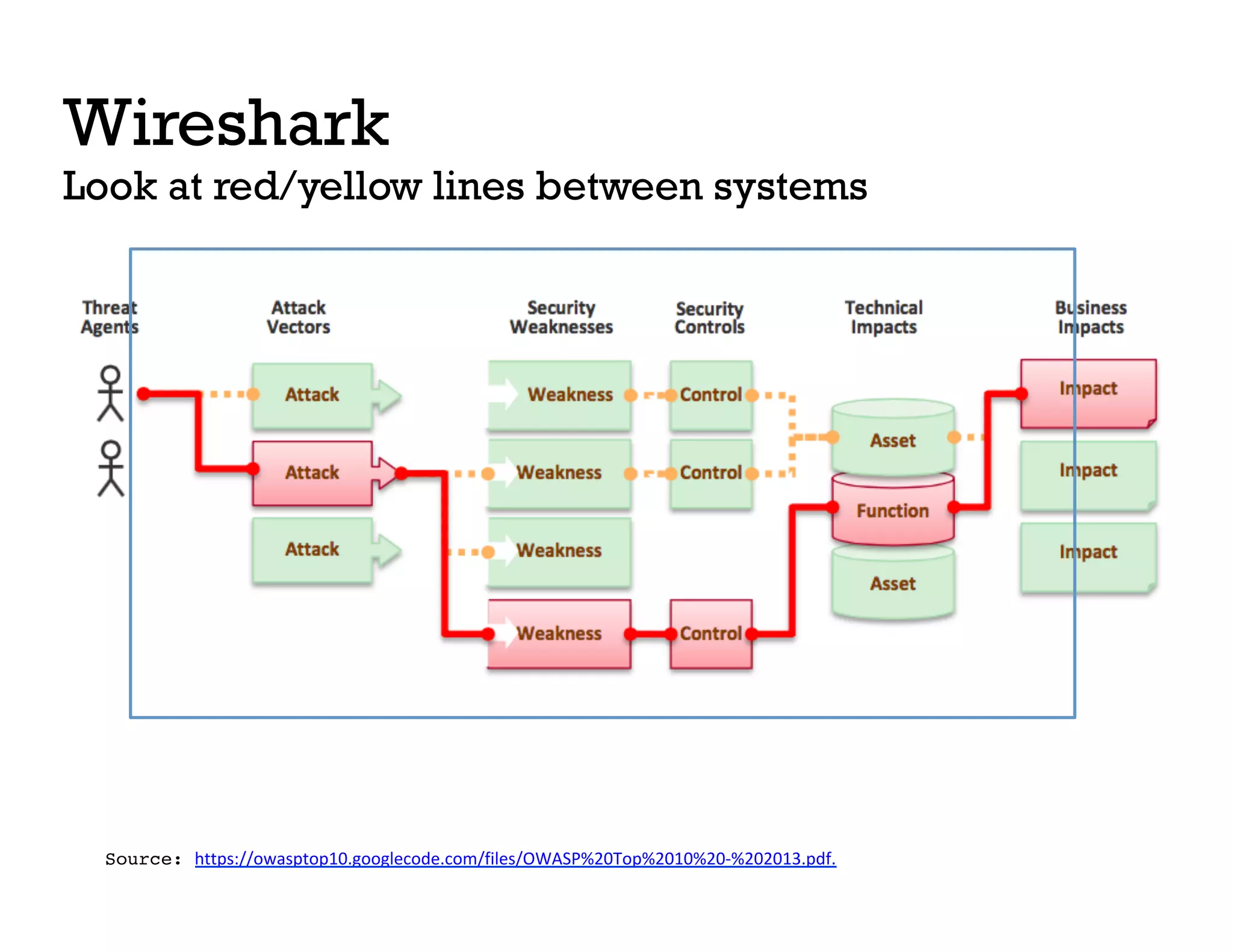
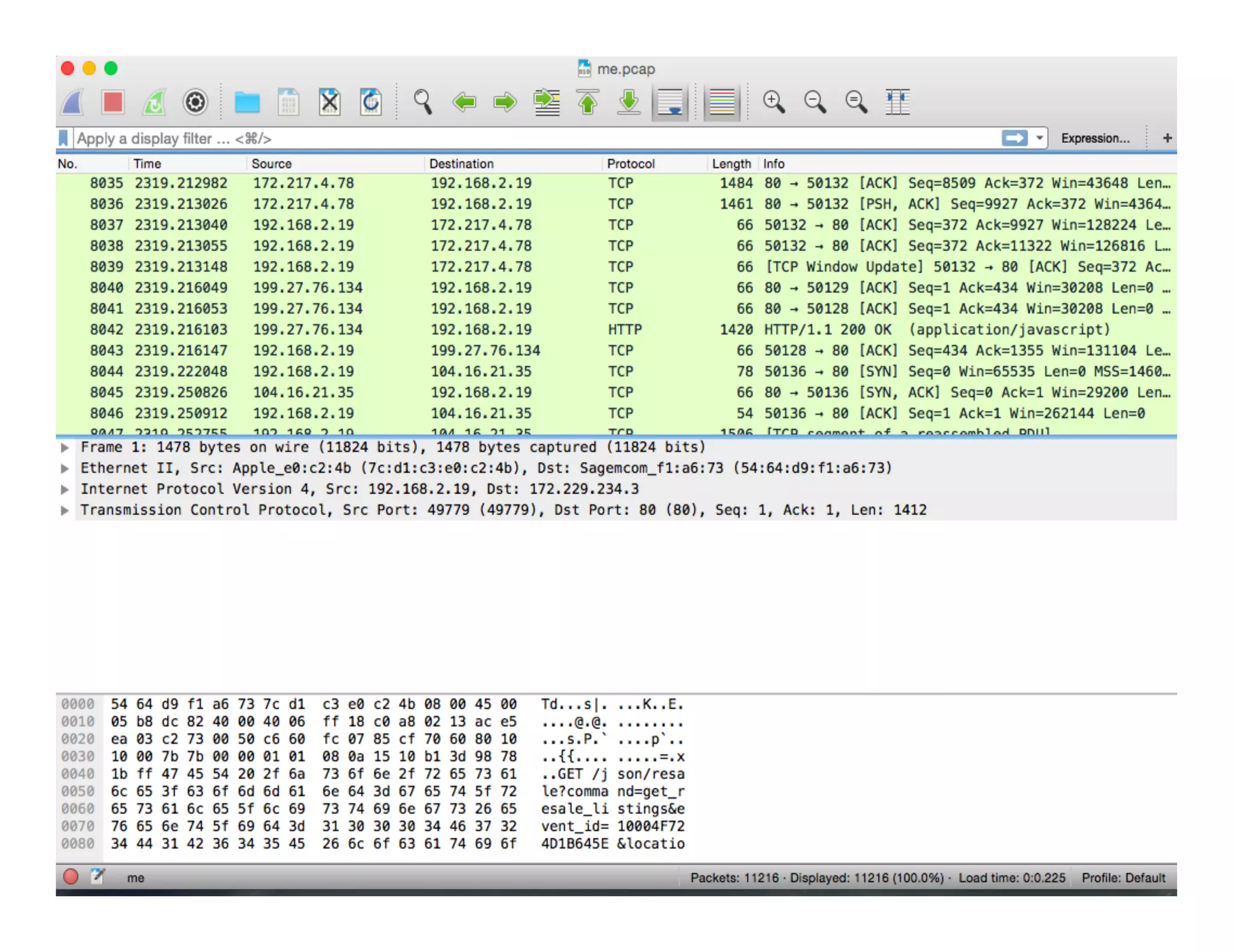
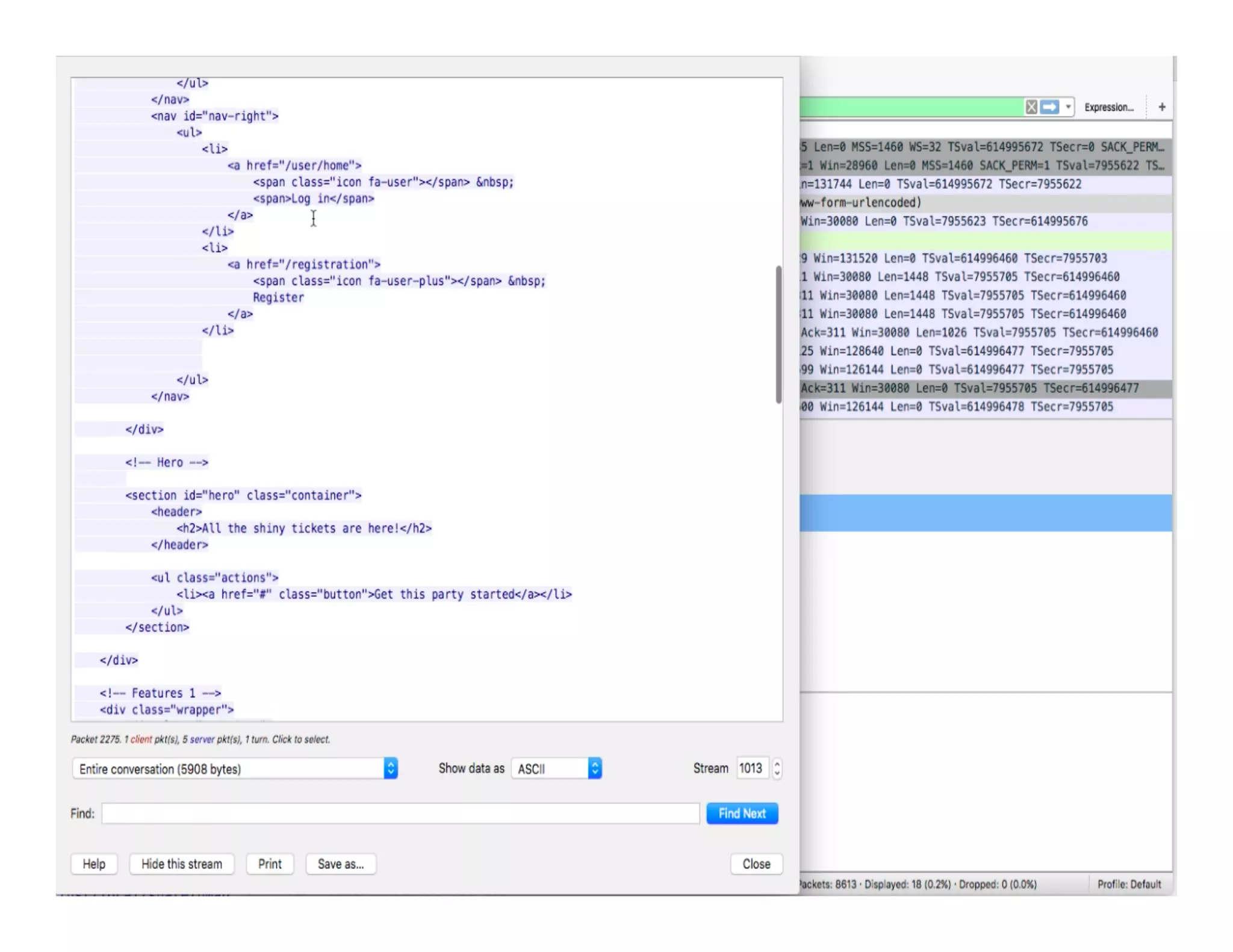
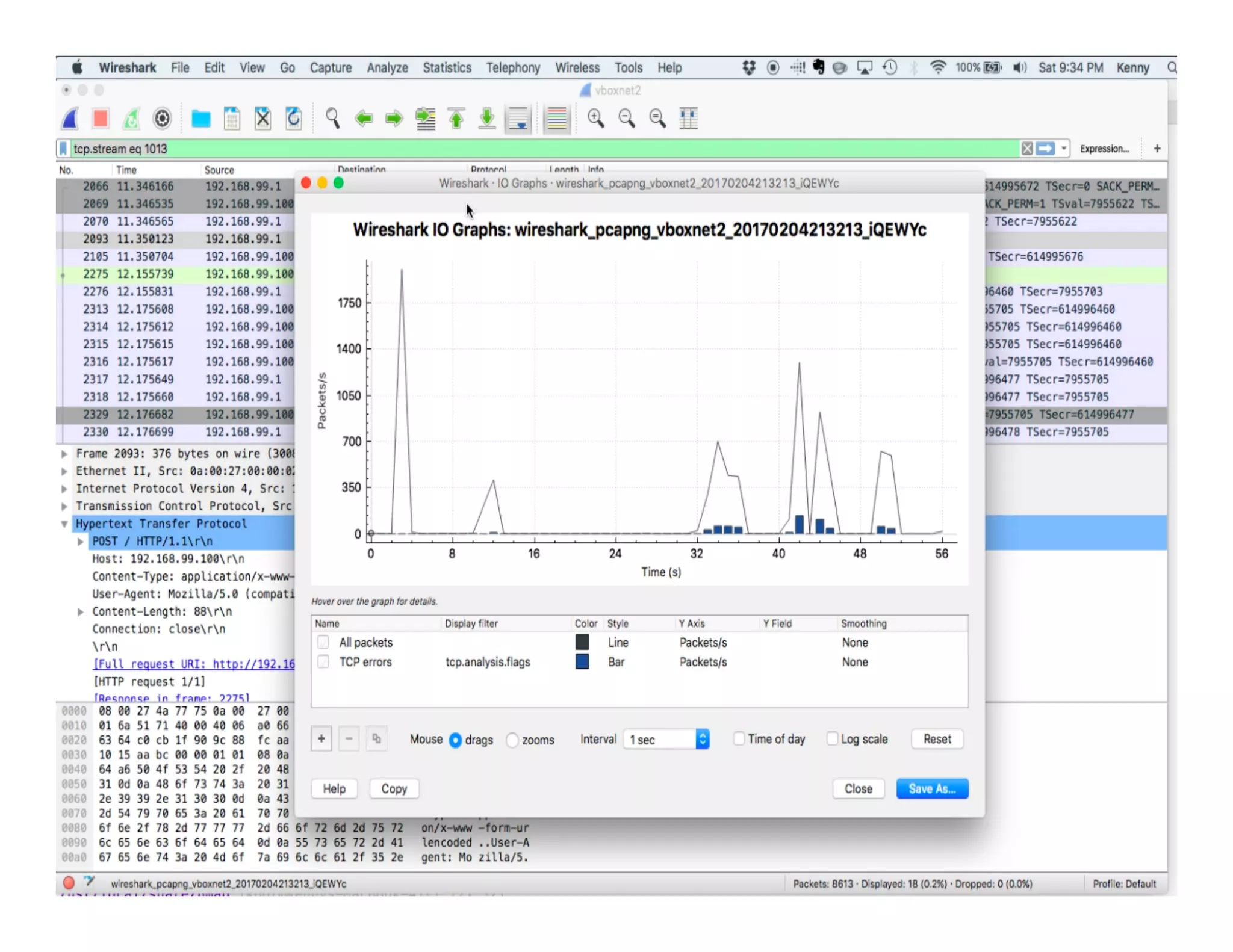
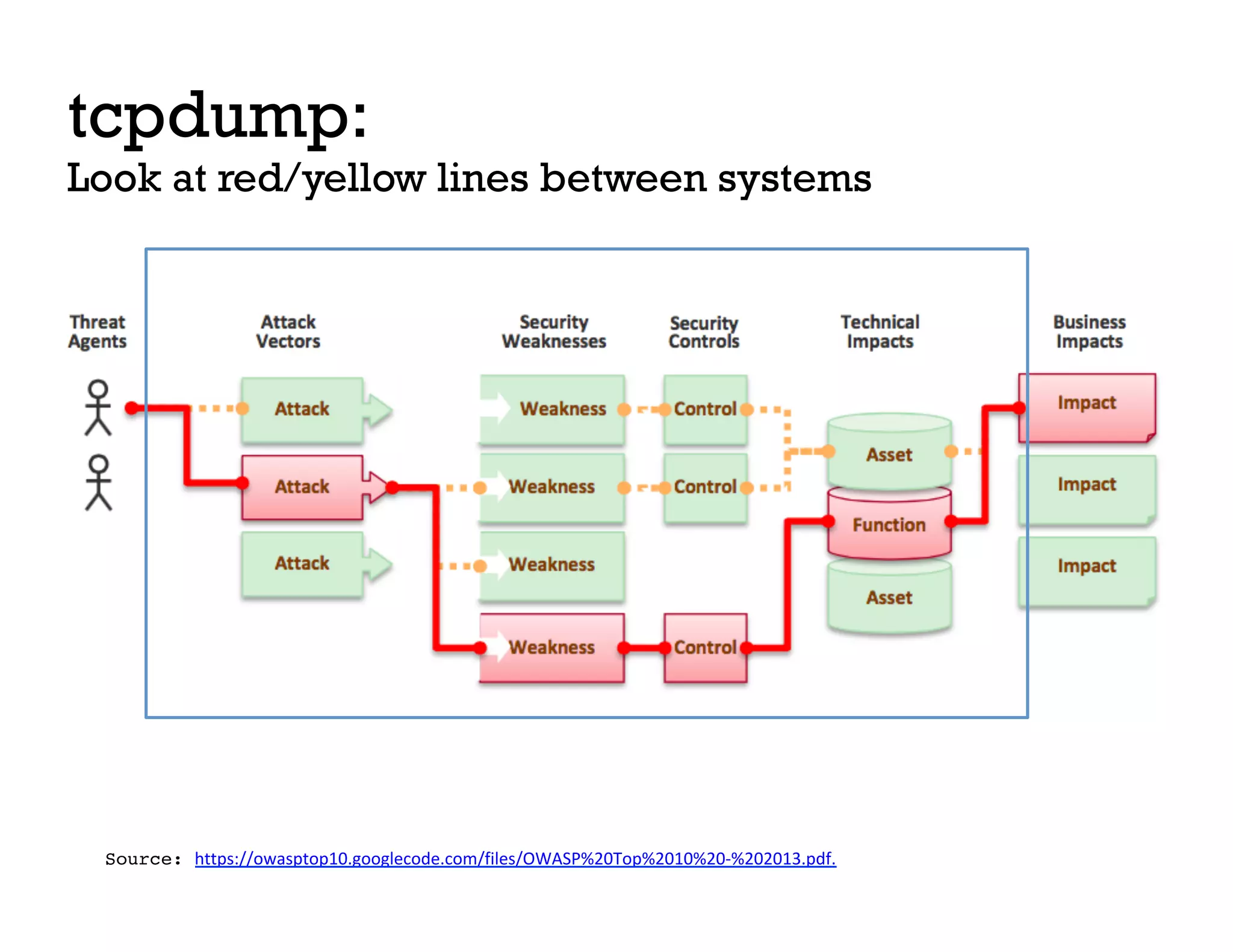
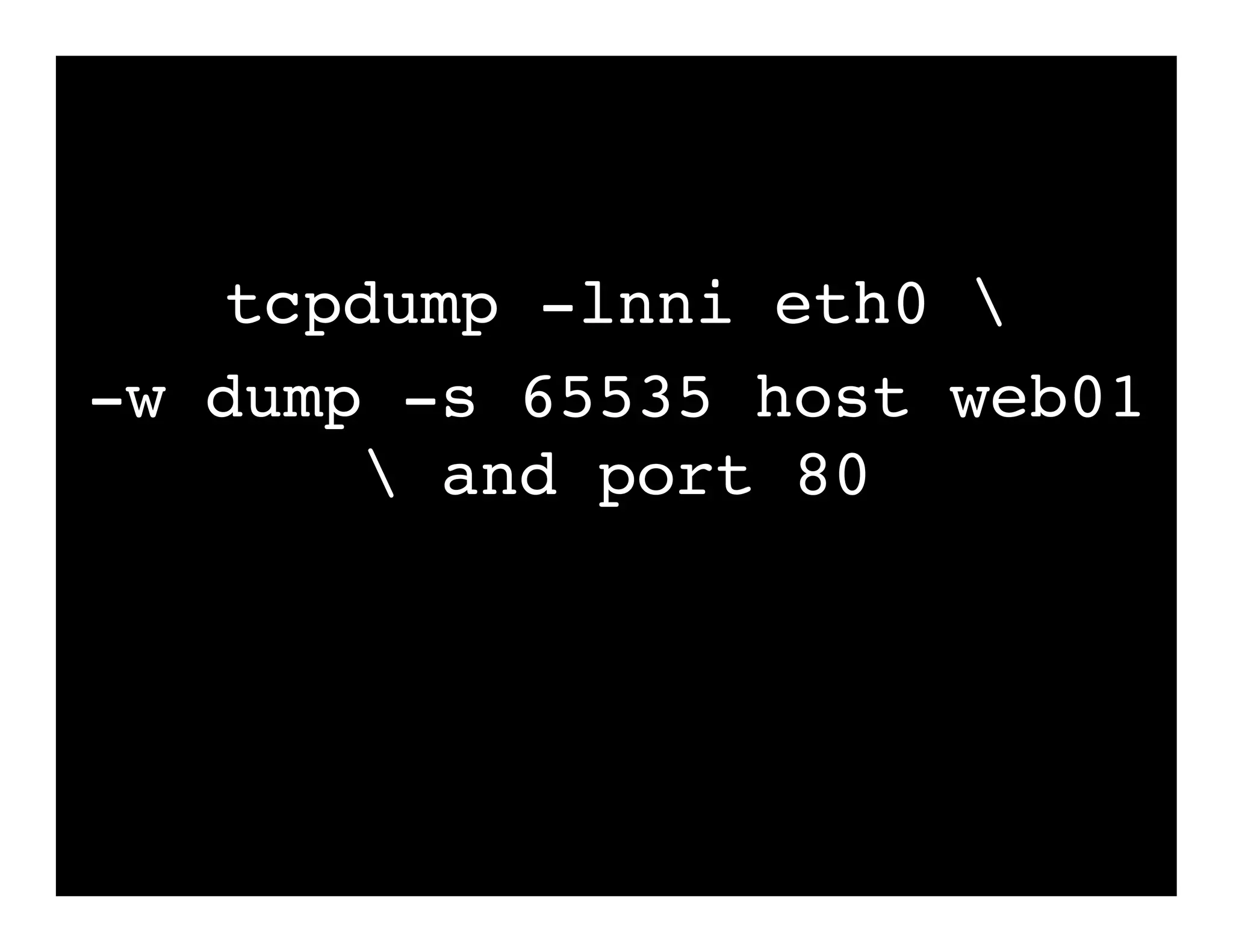
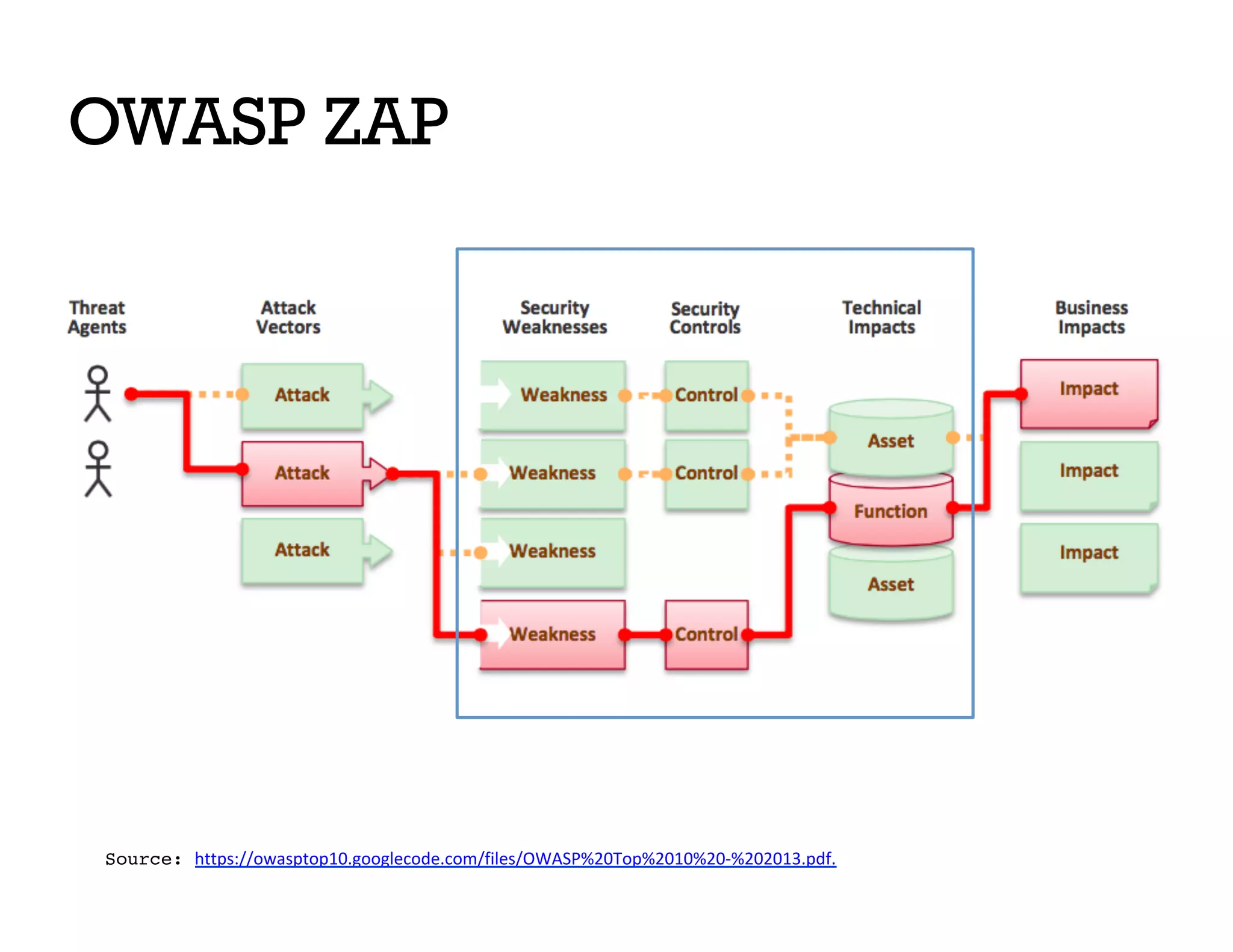
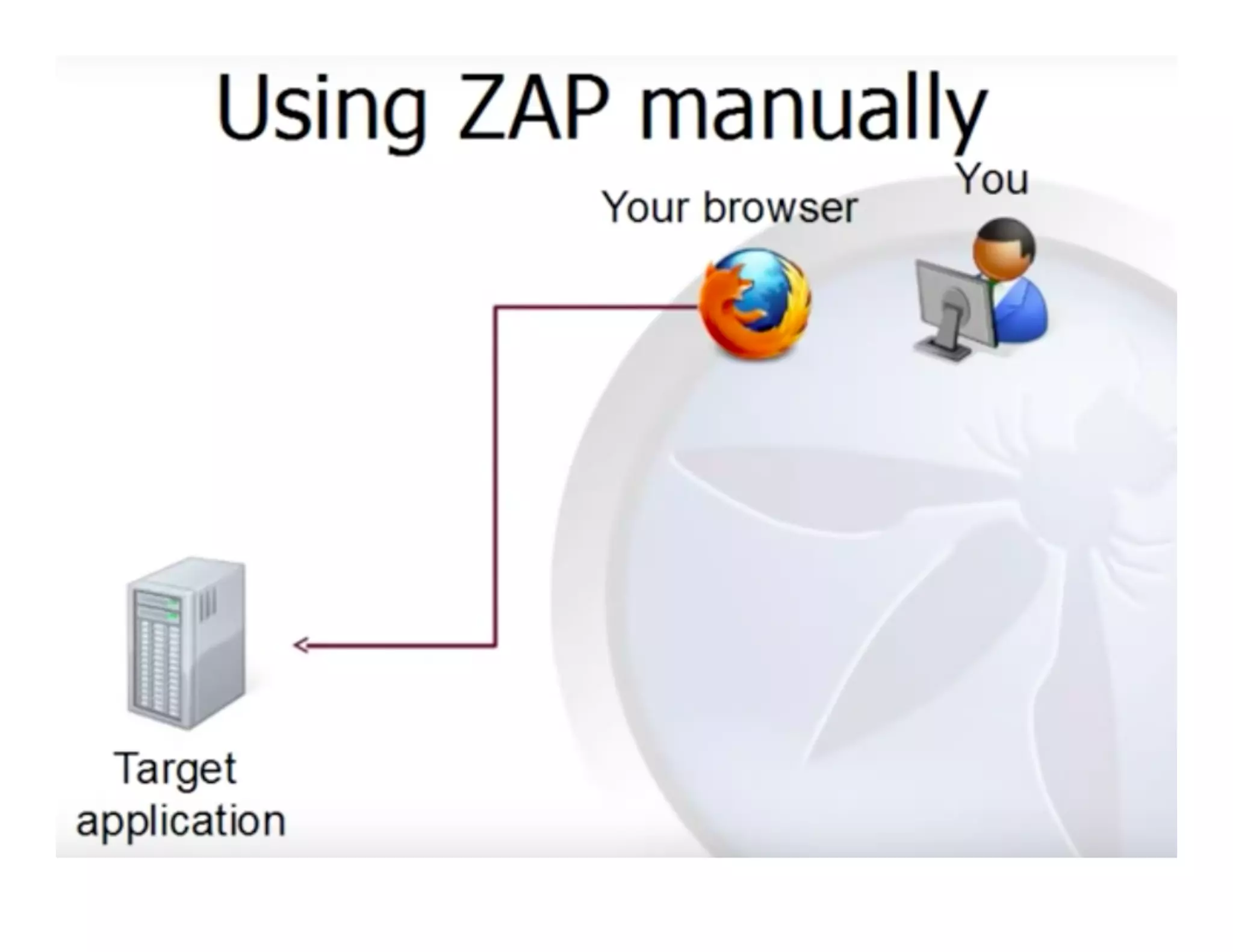
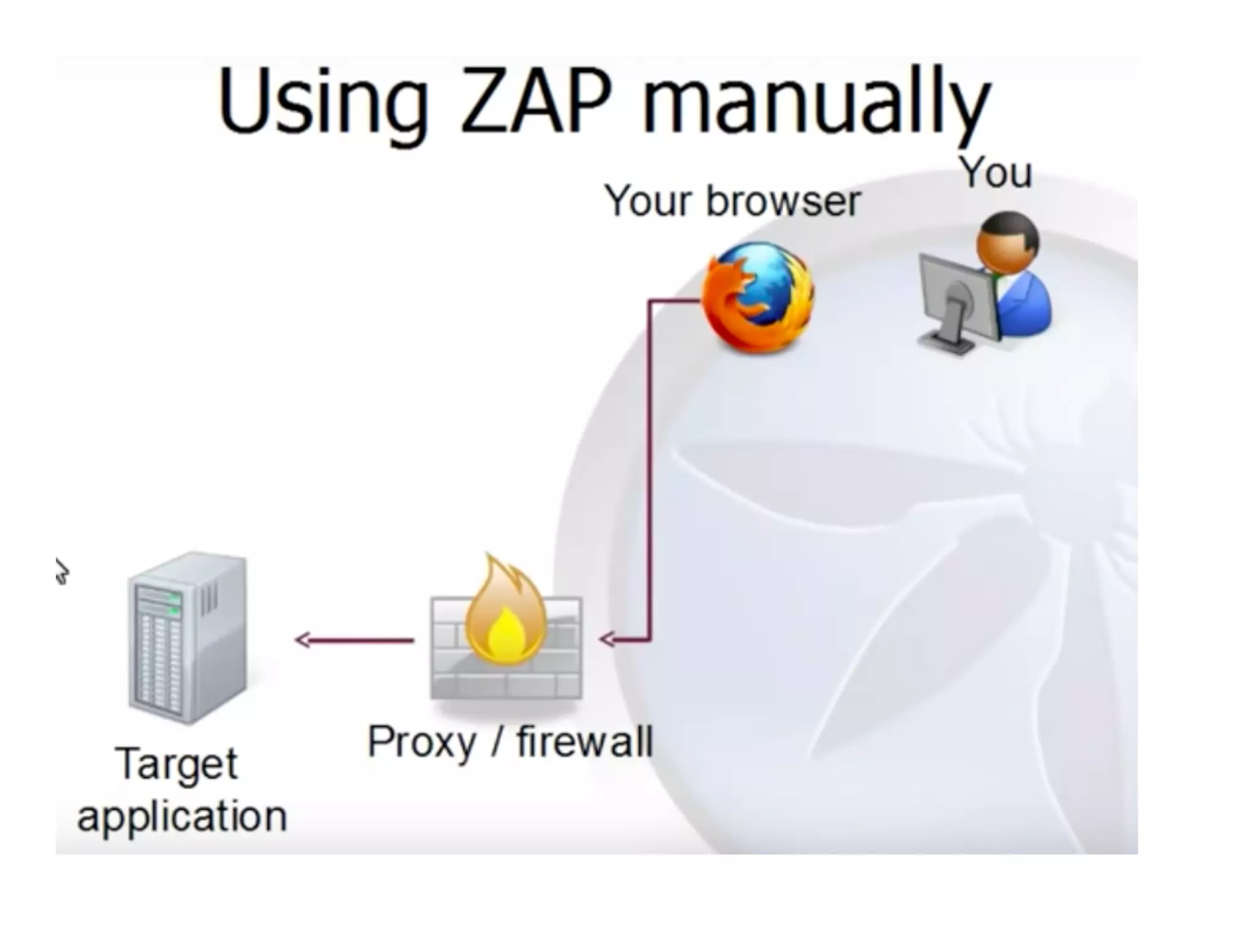
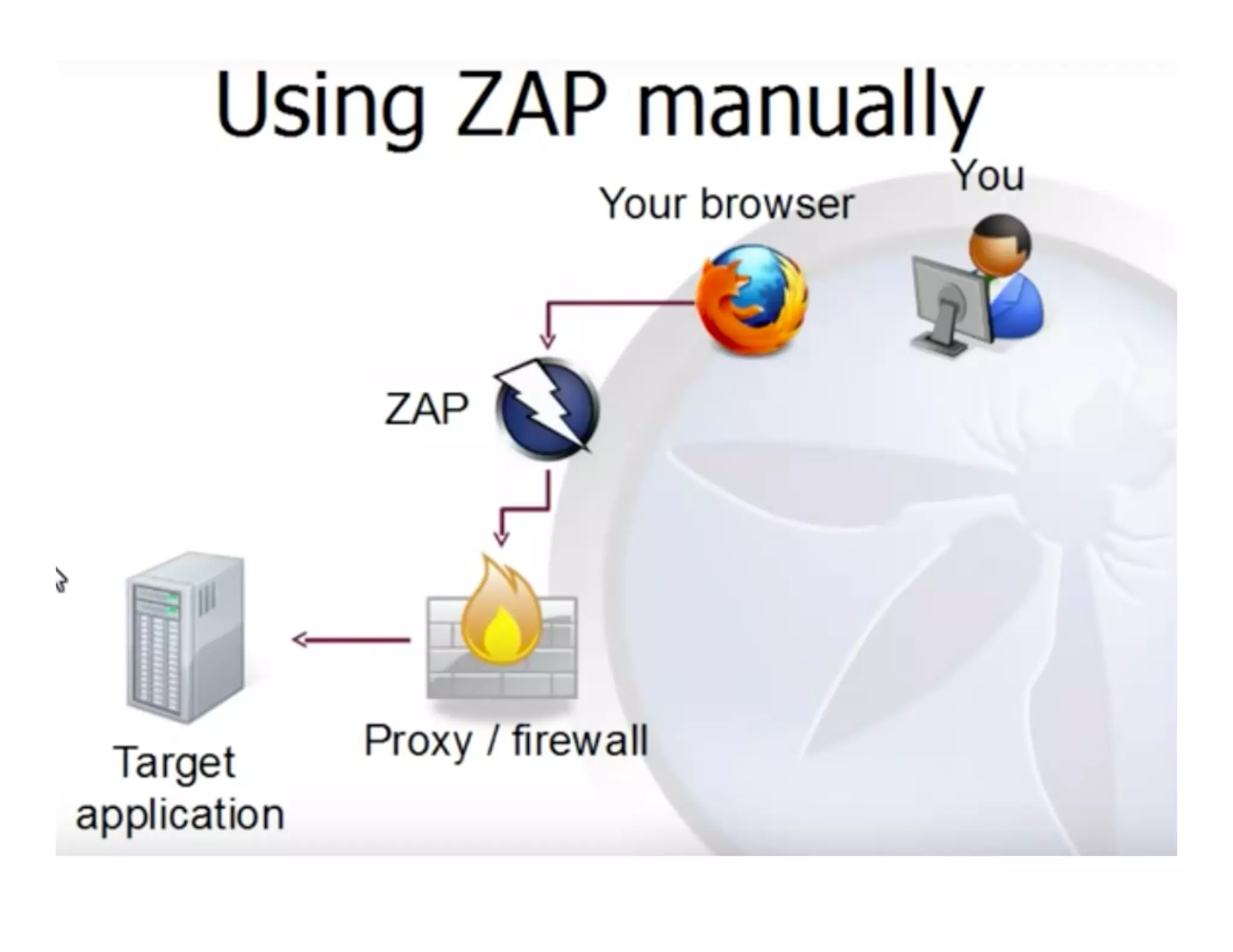
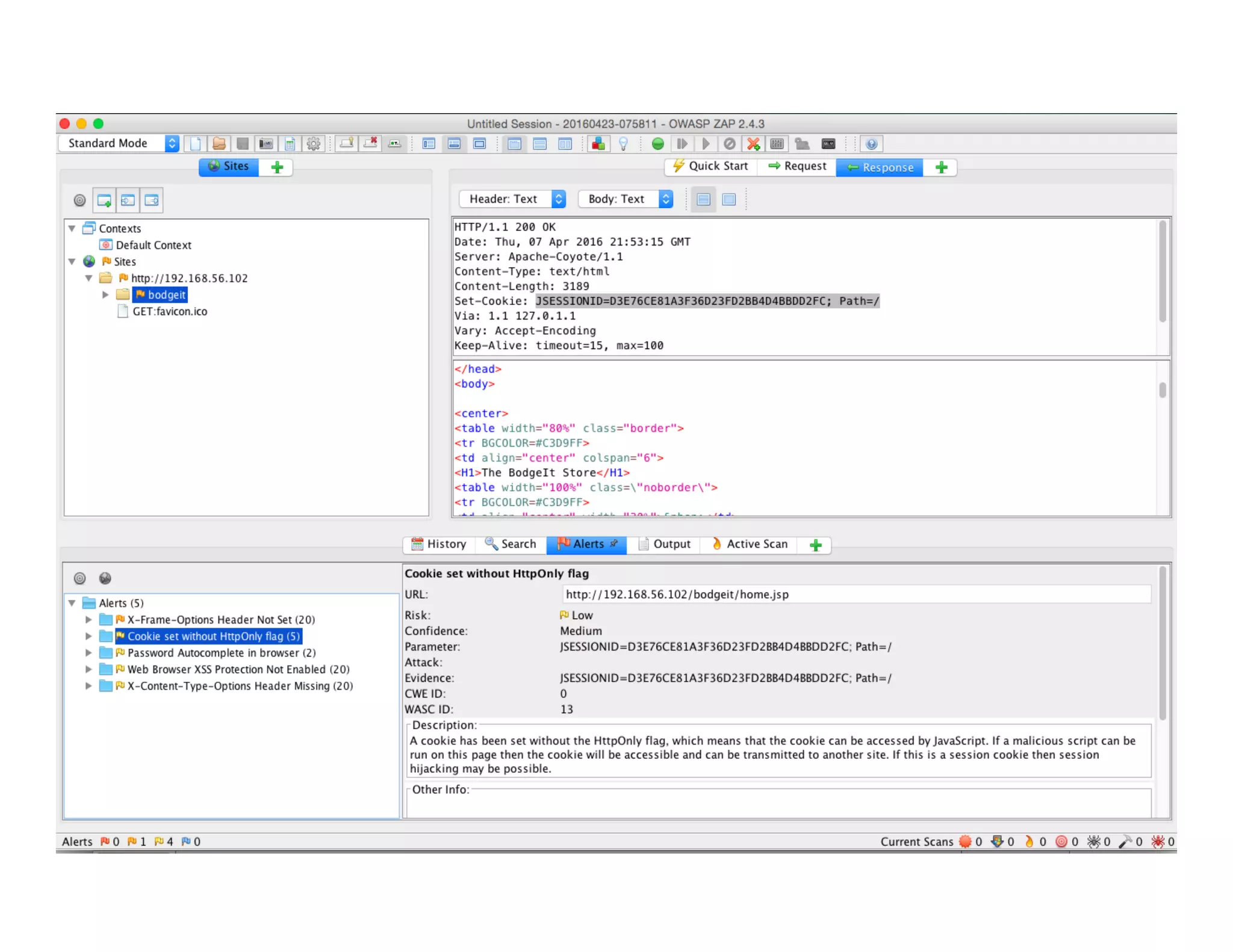
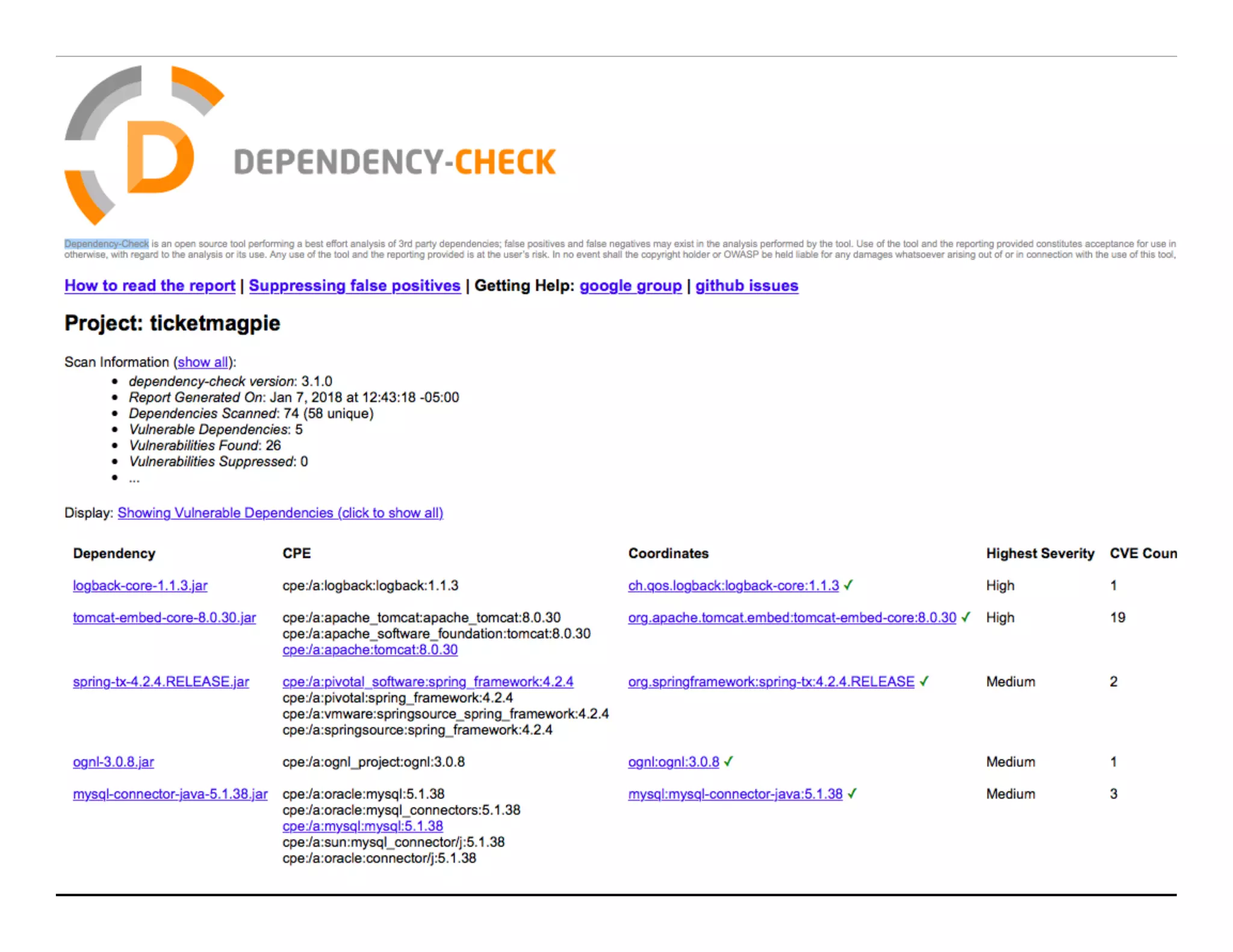
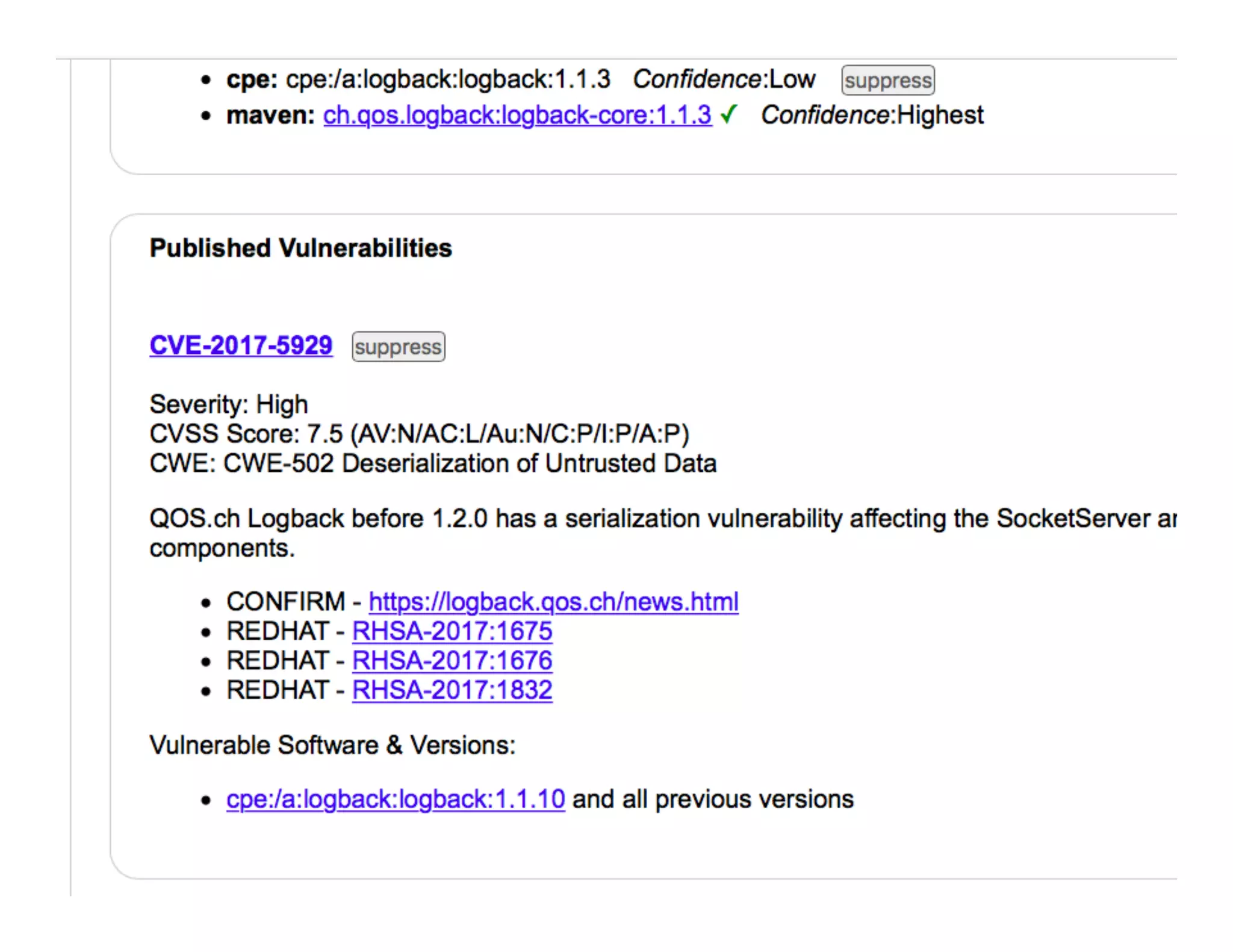
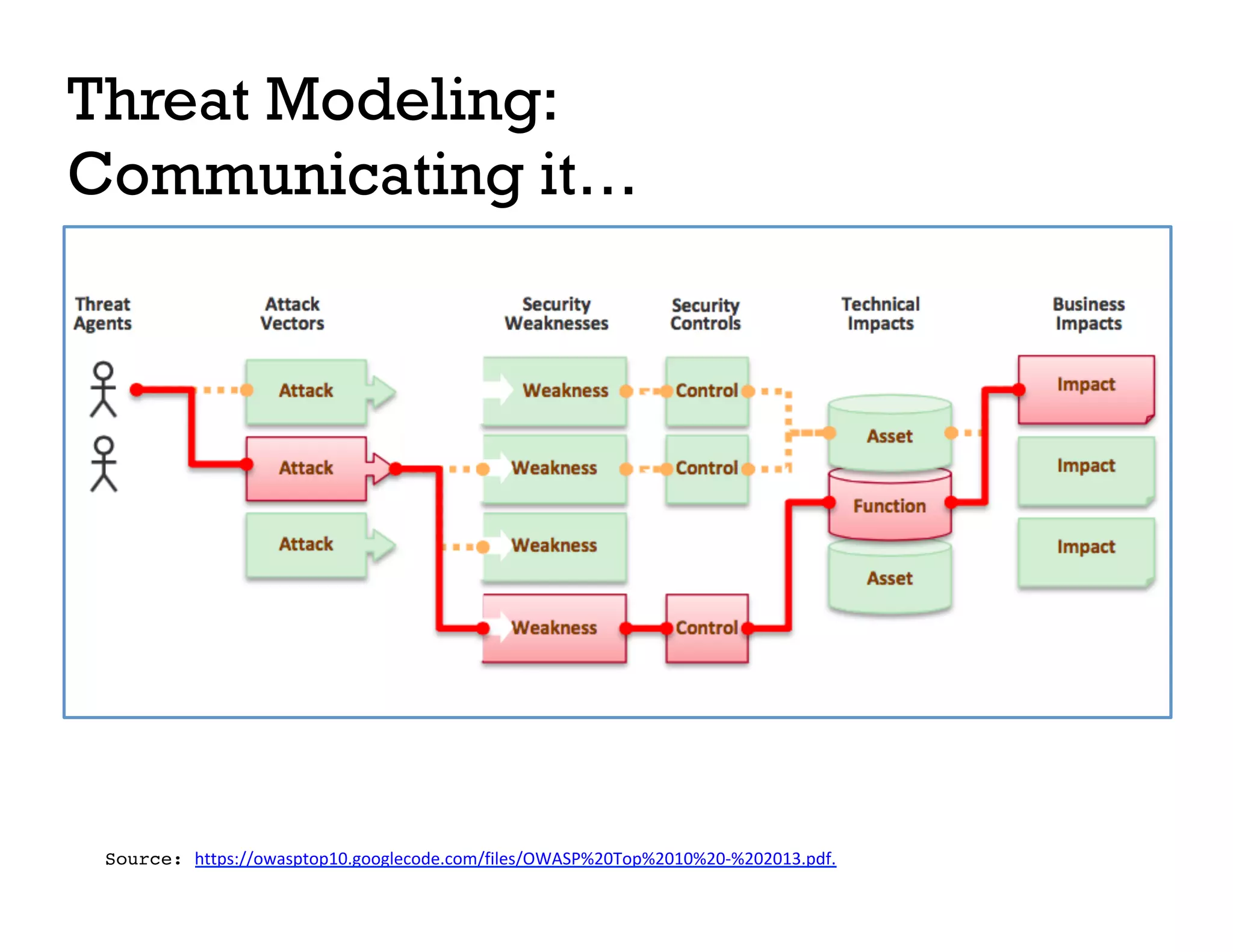
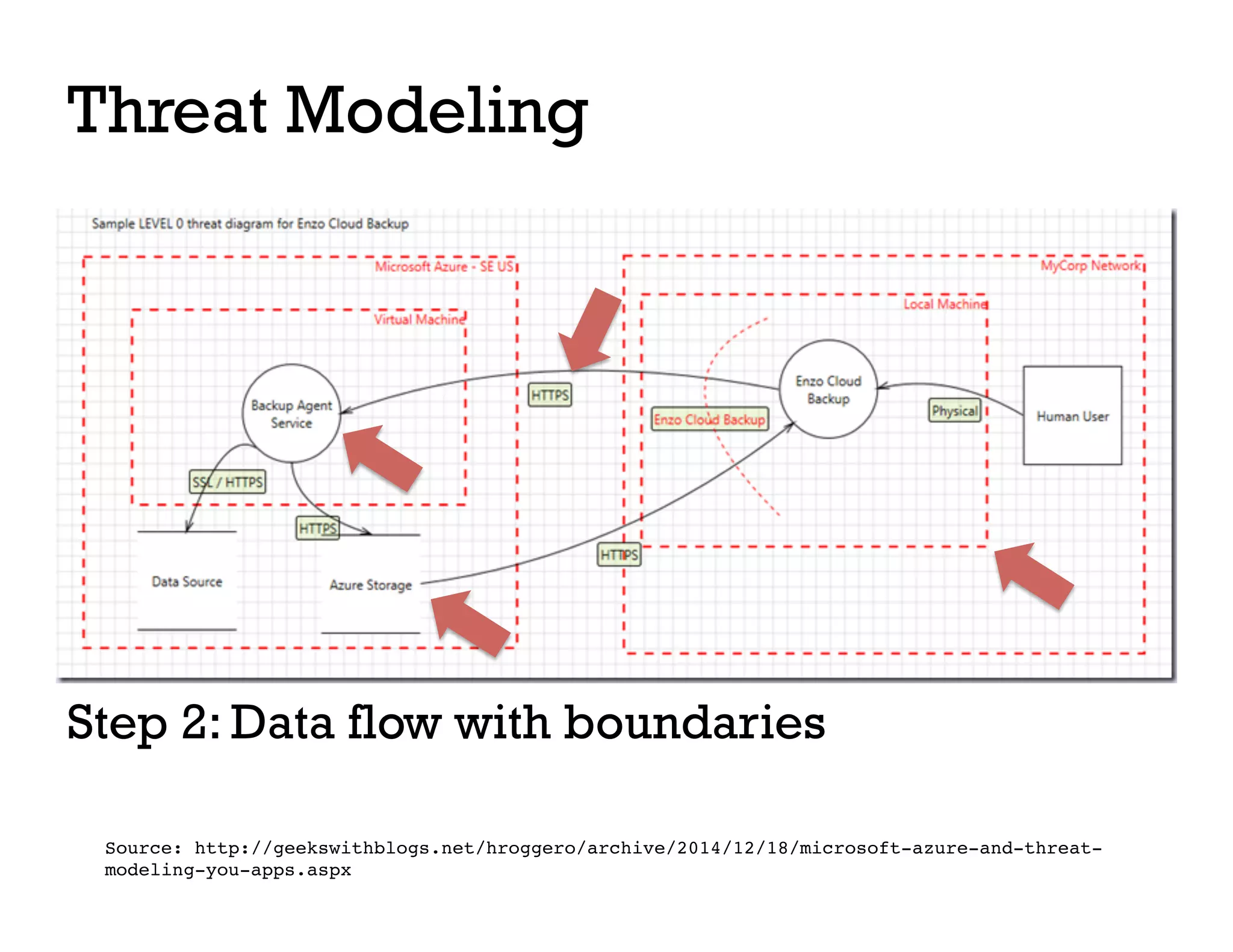
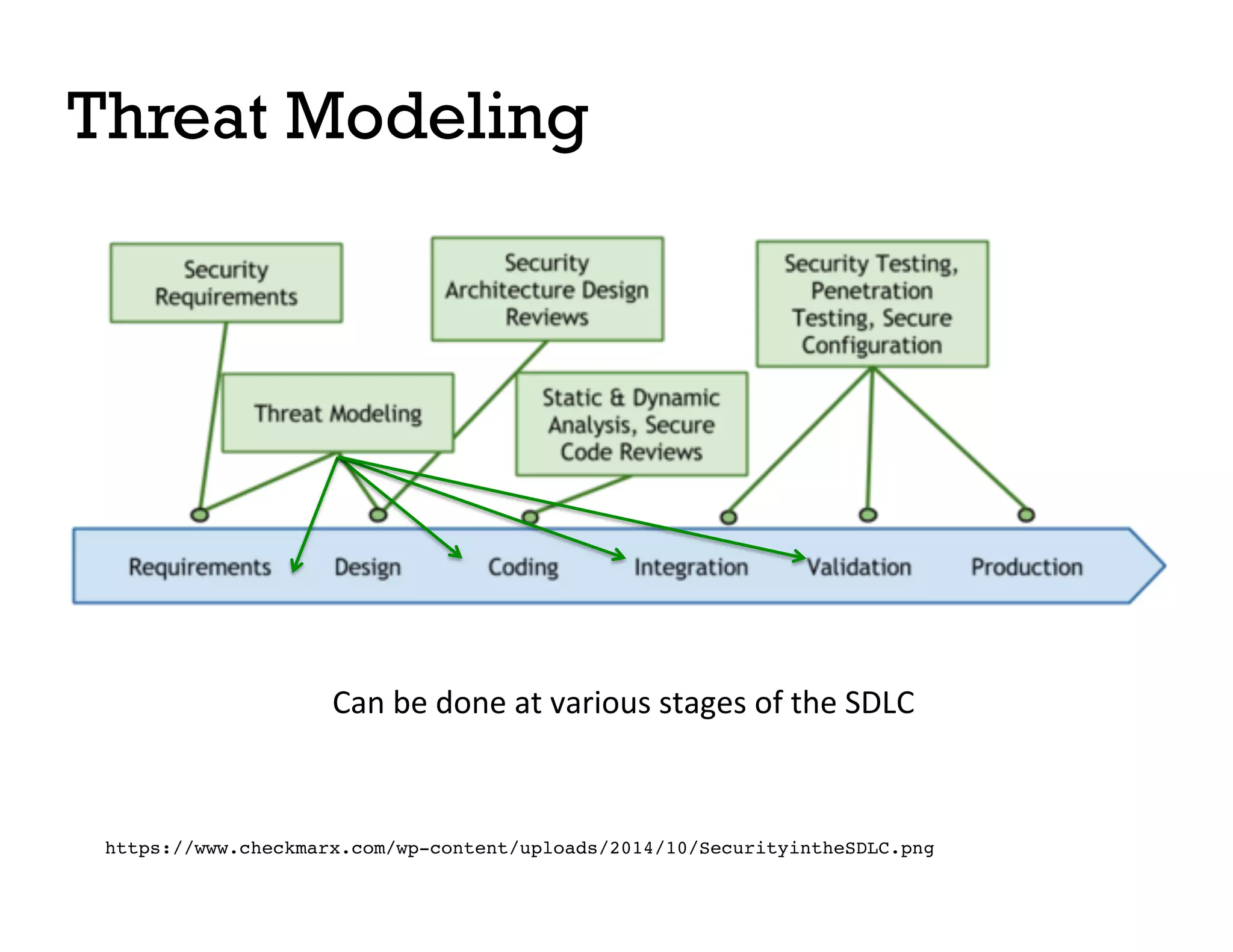
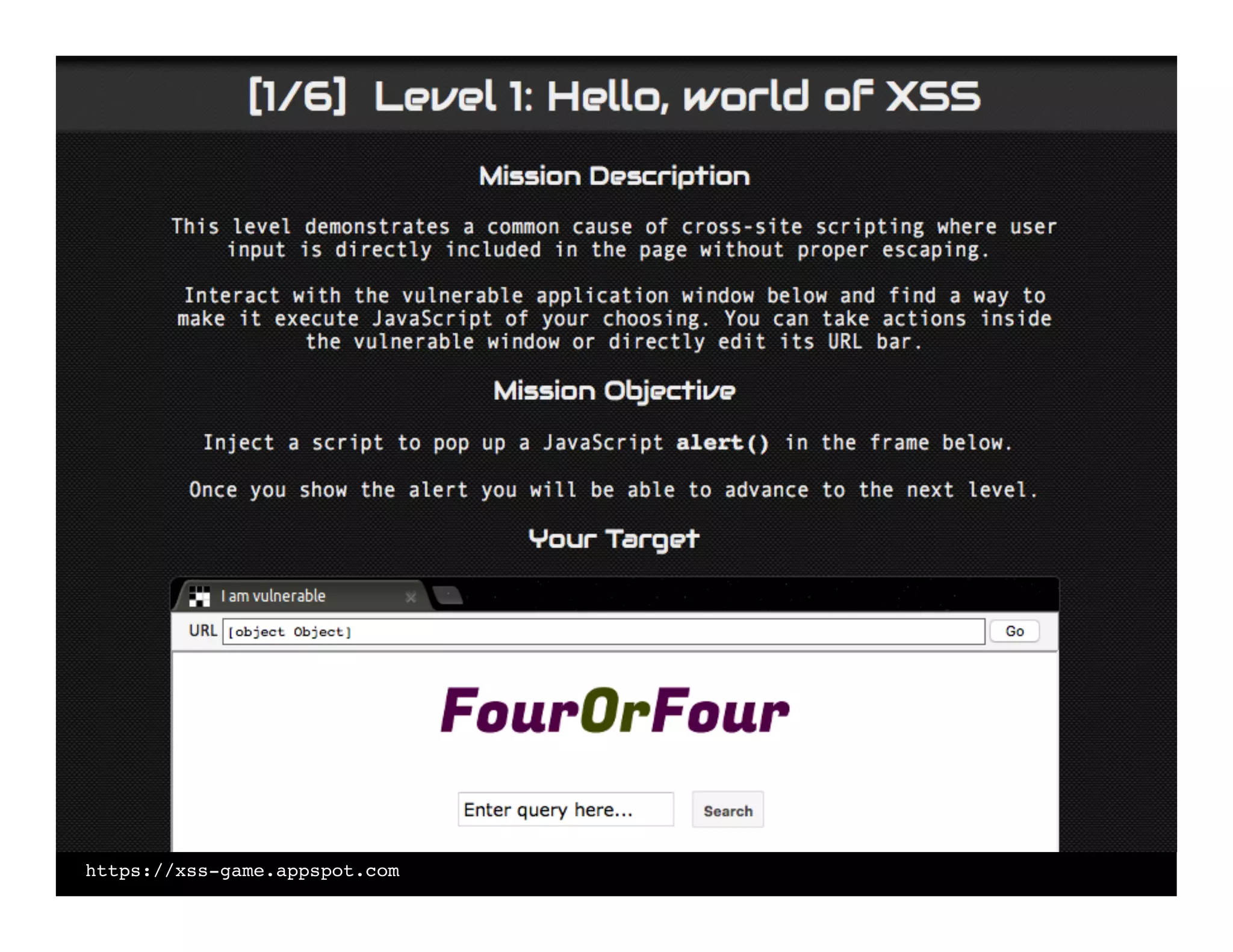
The document provides an overview of web application security testing, detailing tools and methodologies for identifying vulnerabilities such as OWASP Top 10 threats. It emphasizes the importance of proactive security measures, including threat modeling and the use of tools like OWASP ZAP and dependency checks. The talk focuses on practical experiences, underscoring that security is a continuous process rather than a one-time checklist.
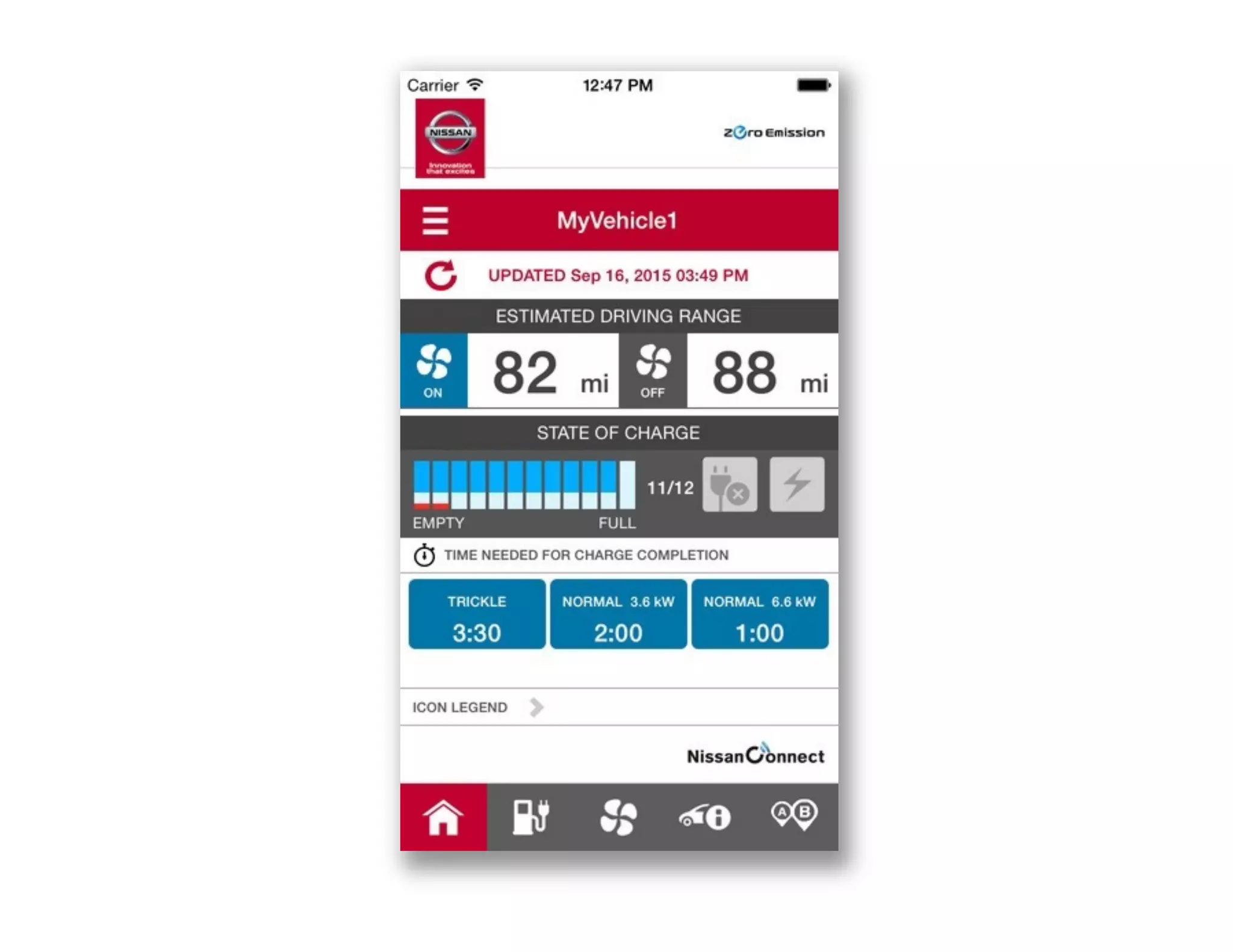
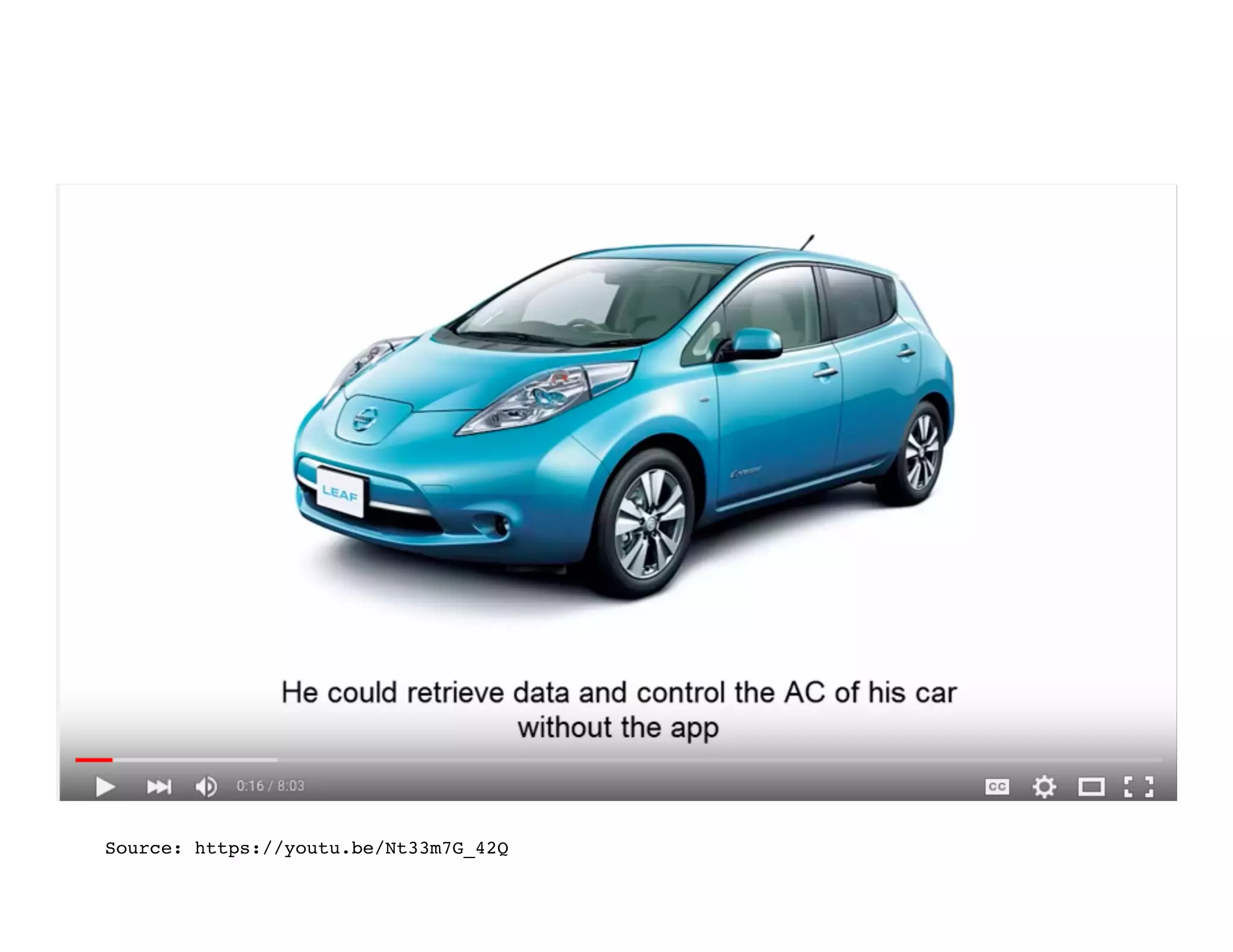
![GET https://[redacted].com/orchestration_1111/gdc/
BatteryStatusRecordsRequest.php?RegionCode=NE&lg=no-
NO&DCMID=&VIN=SJNFAAZE0U60XXXXX&tz=Europe/
Paris&TimeFrom=2014-09-27T09:15:21](https://image.slidesharecdn.com/securityv1-180112004452/75/What-You-Need-to-Know-About-Web-App-Security-Testing-in-2018-4-2048.jpg)
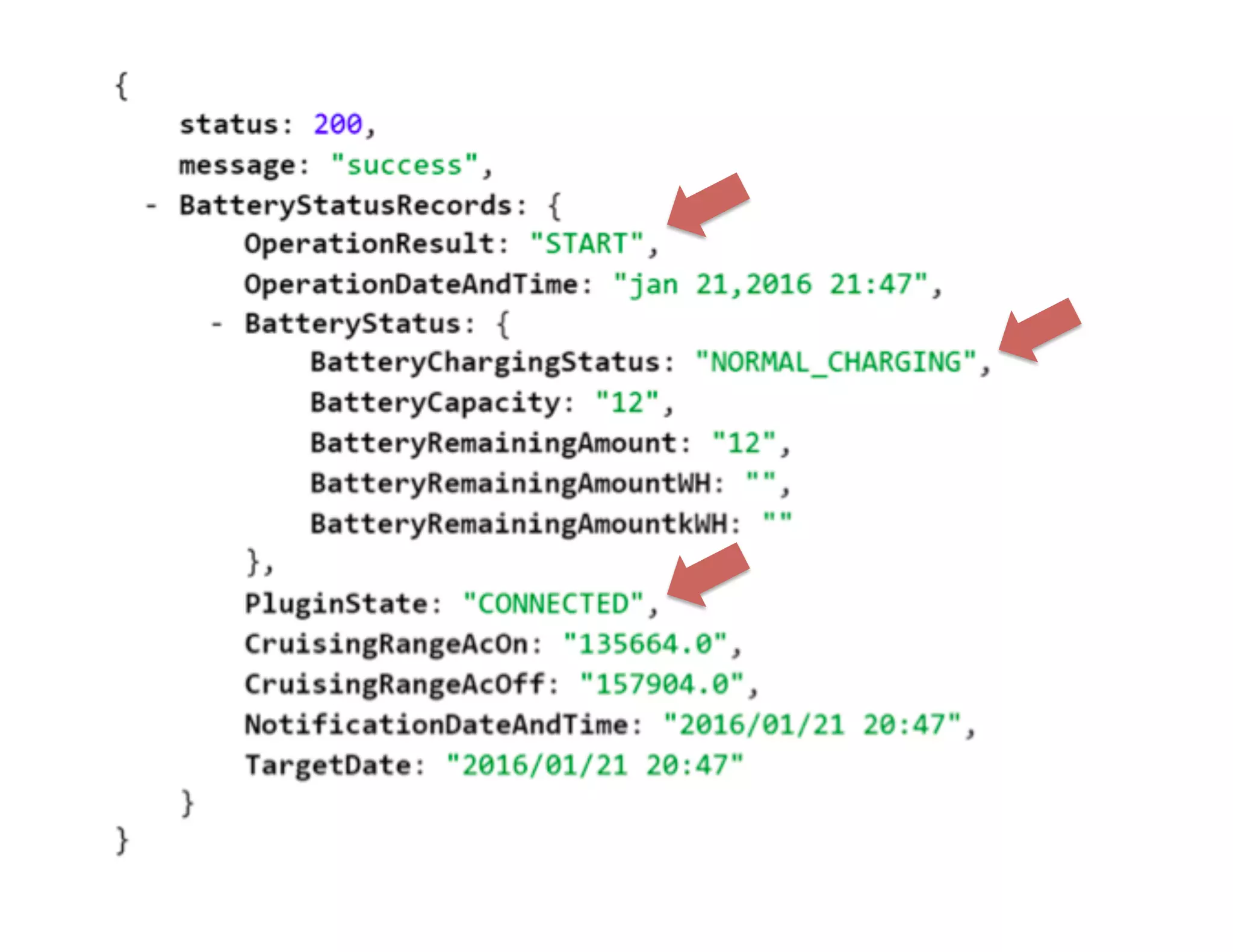
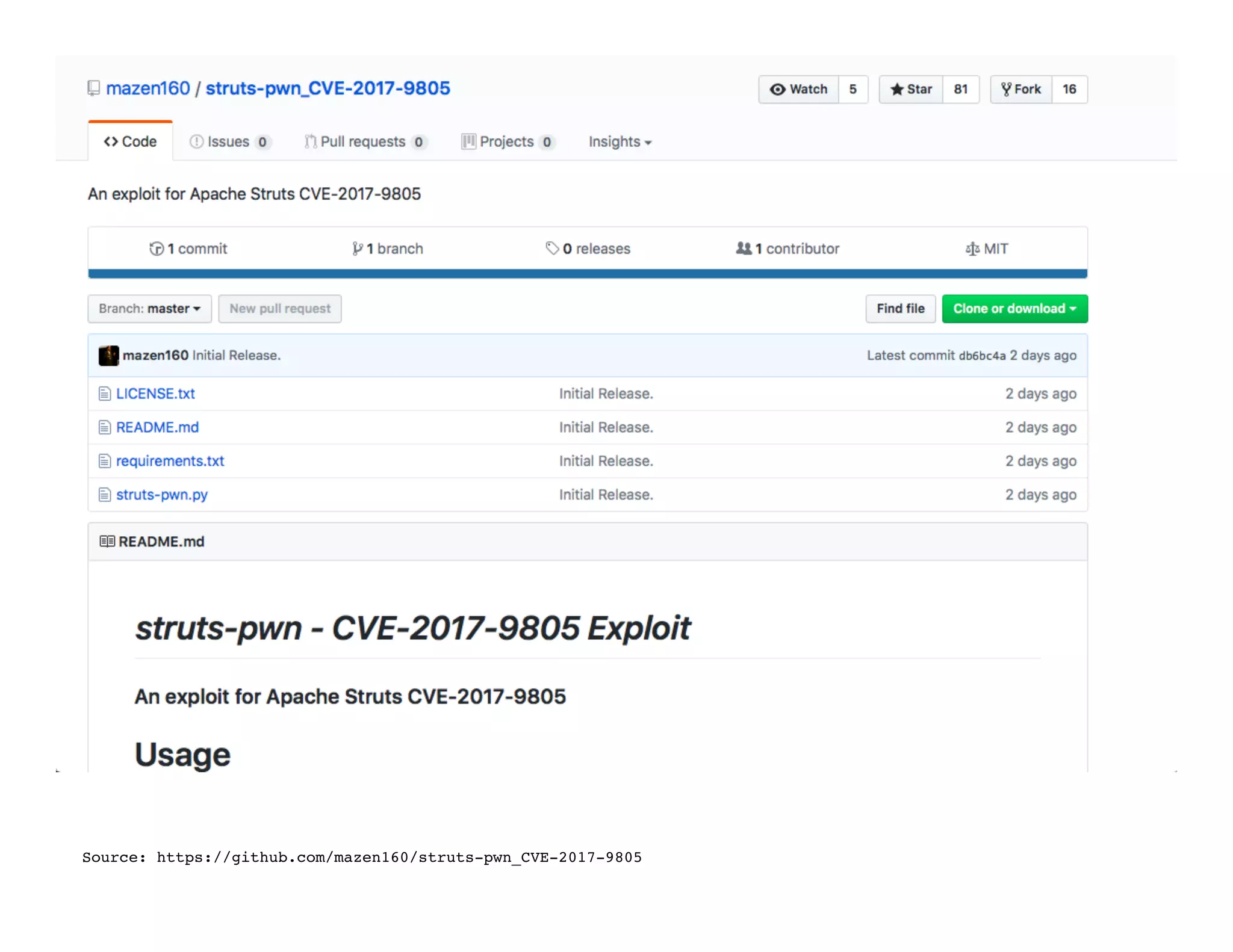
![GET https://[redacted].com/orchestration_1111/gdc/
BatteryStatusRecordsRequest.php?RegionCode=NE&lg=no-
NO&DCMID=&VIN=SJNFAAZE0U60XXXXX&tz=Europe/
Paris&TimeFrom=2014-09-27T09:15:21](https://image.slidesharecdn.com/securityv1-180112004452/75/What-You-Need-to-Know-About-Web-App-Security-Testing-in-2018-6-2048.jpg)