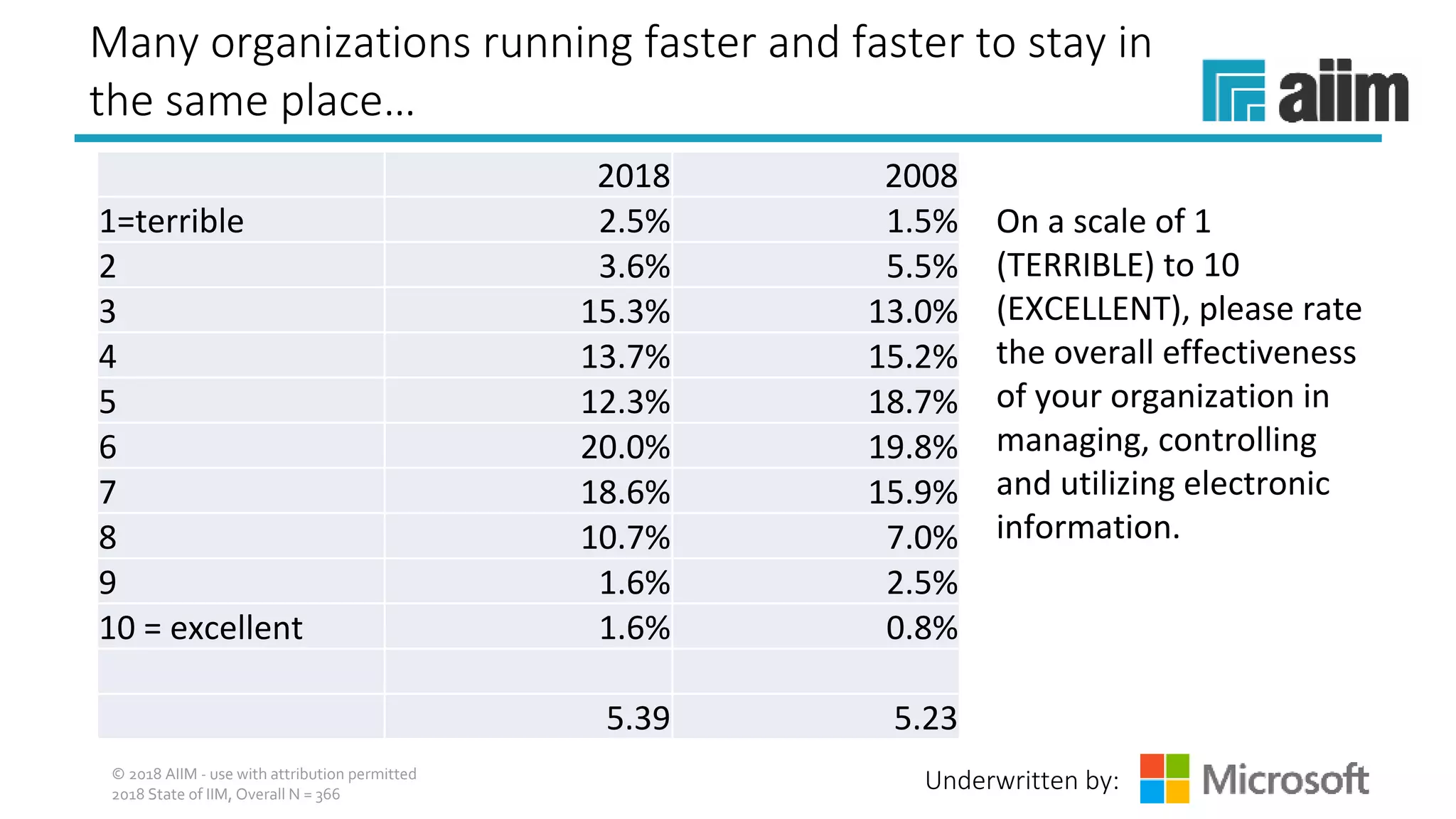
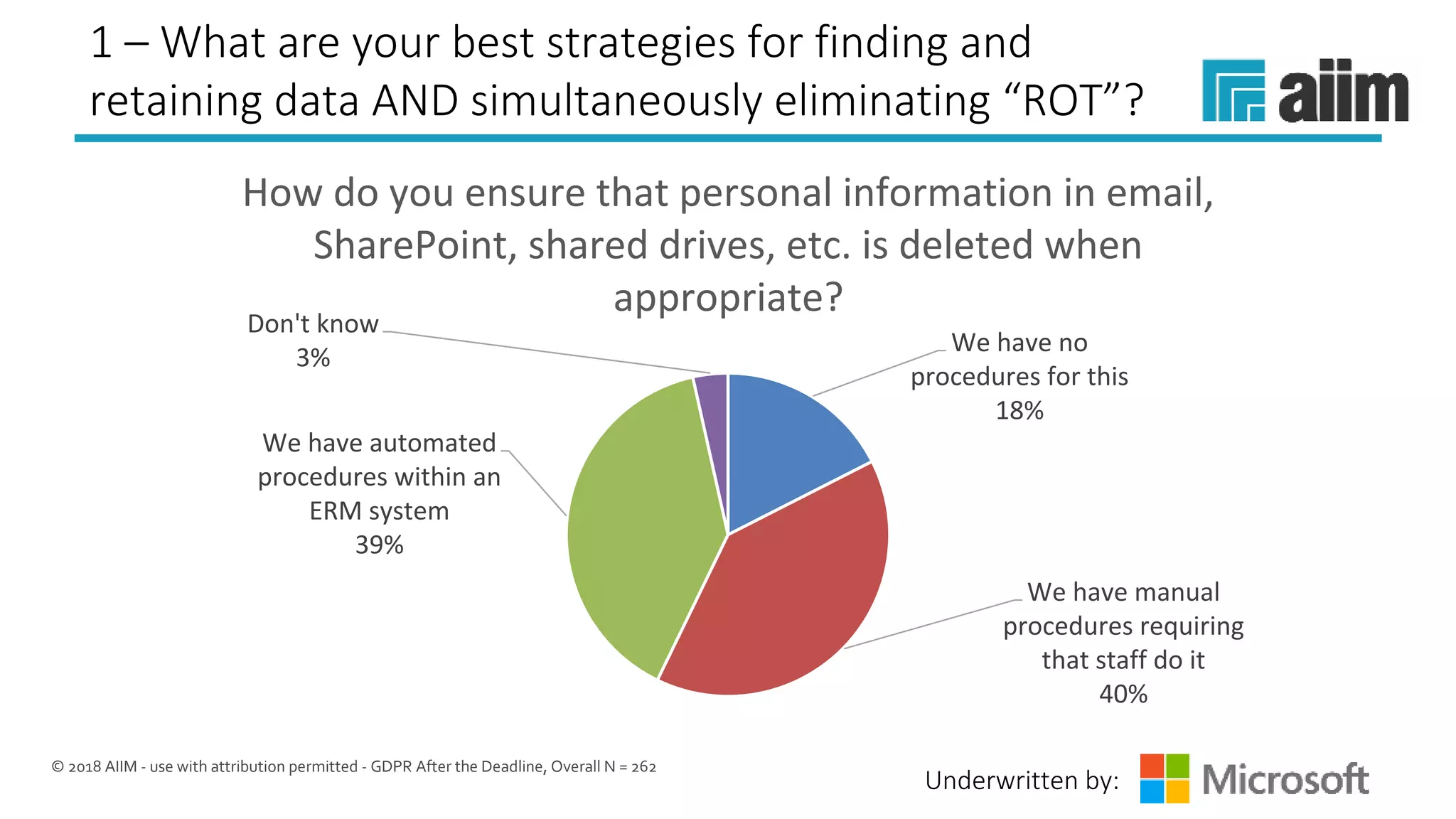
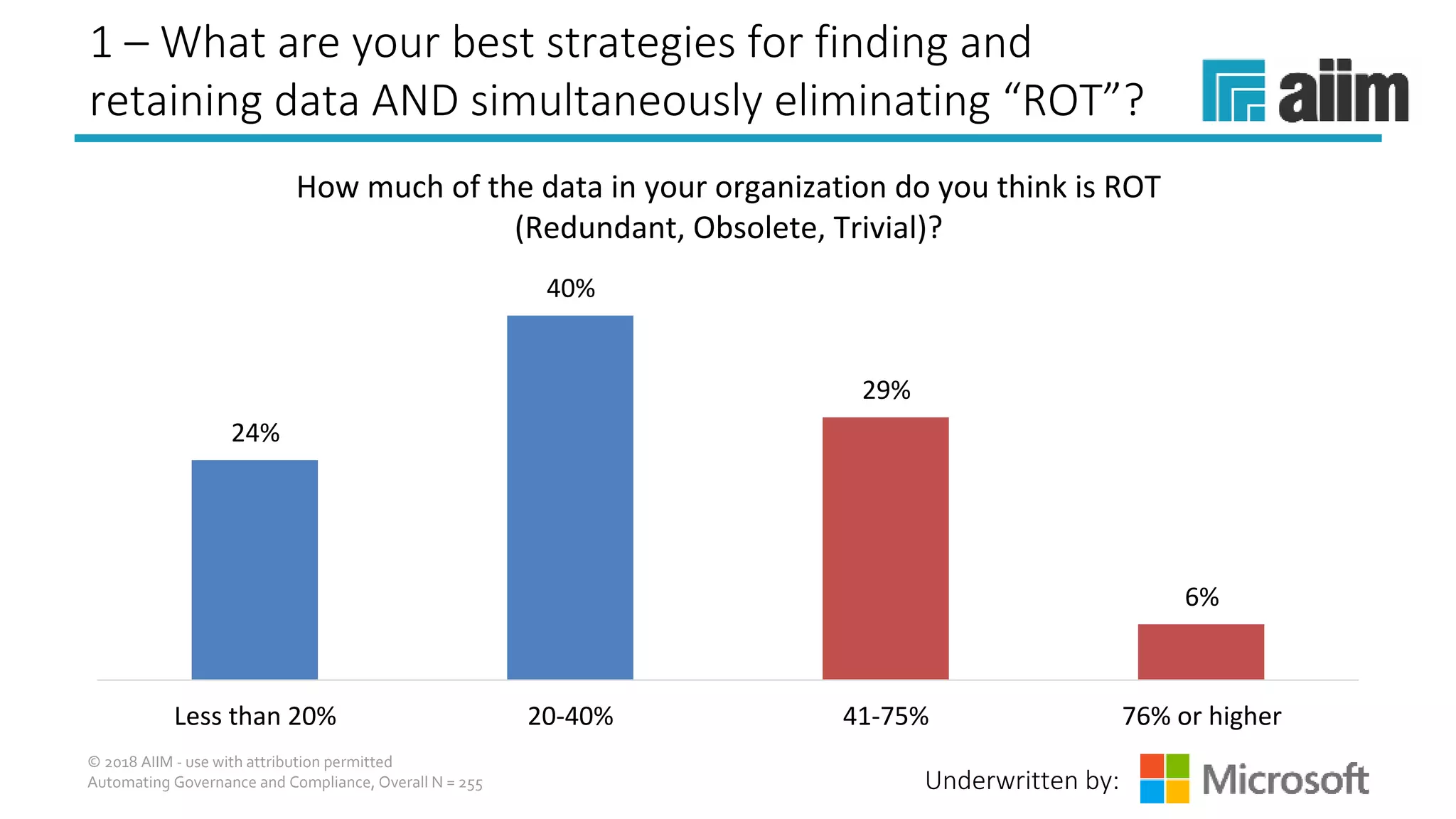
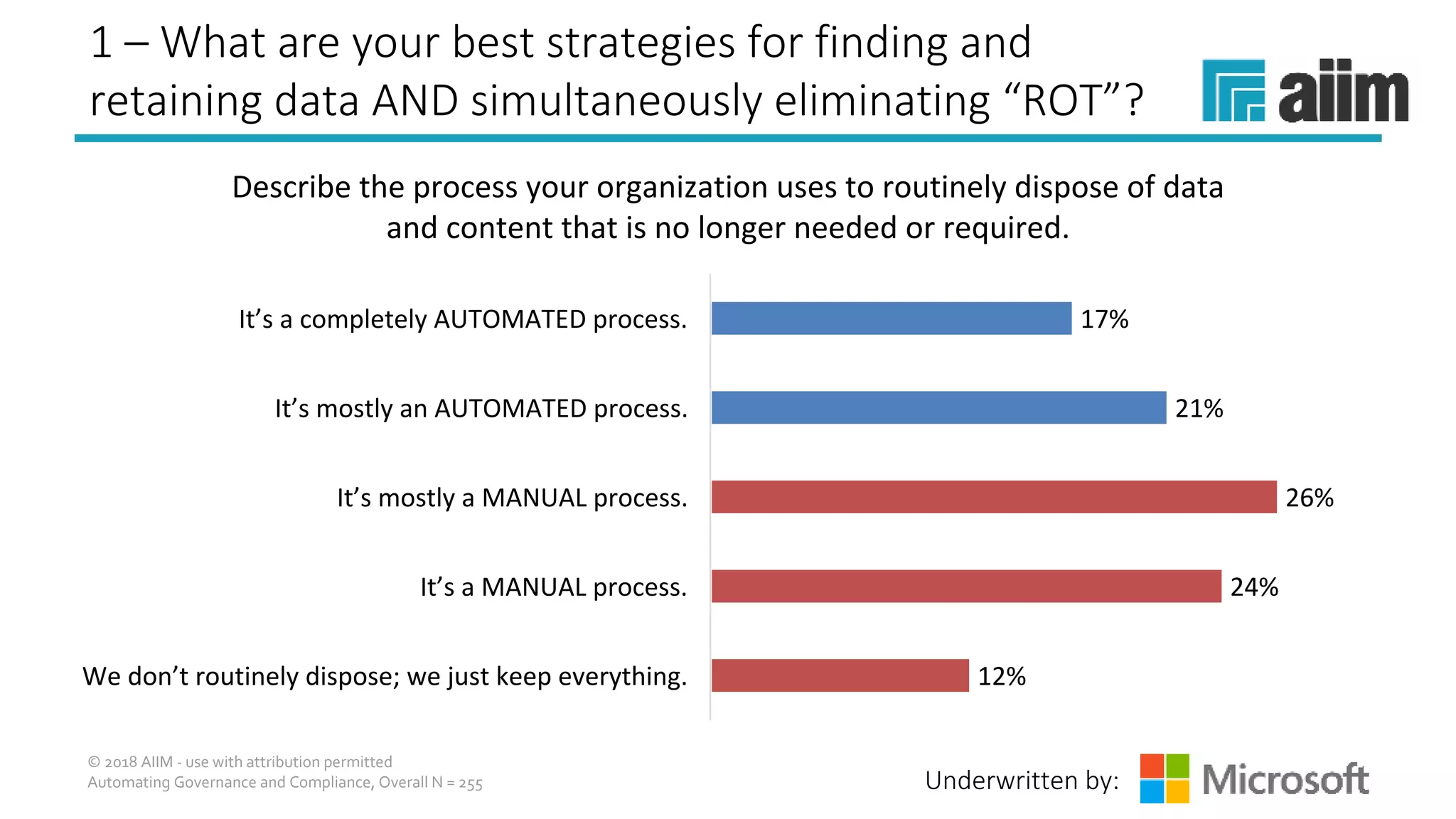
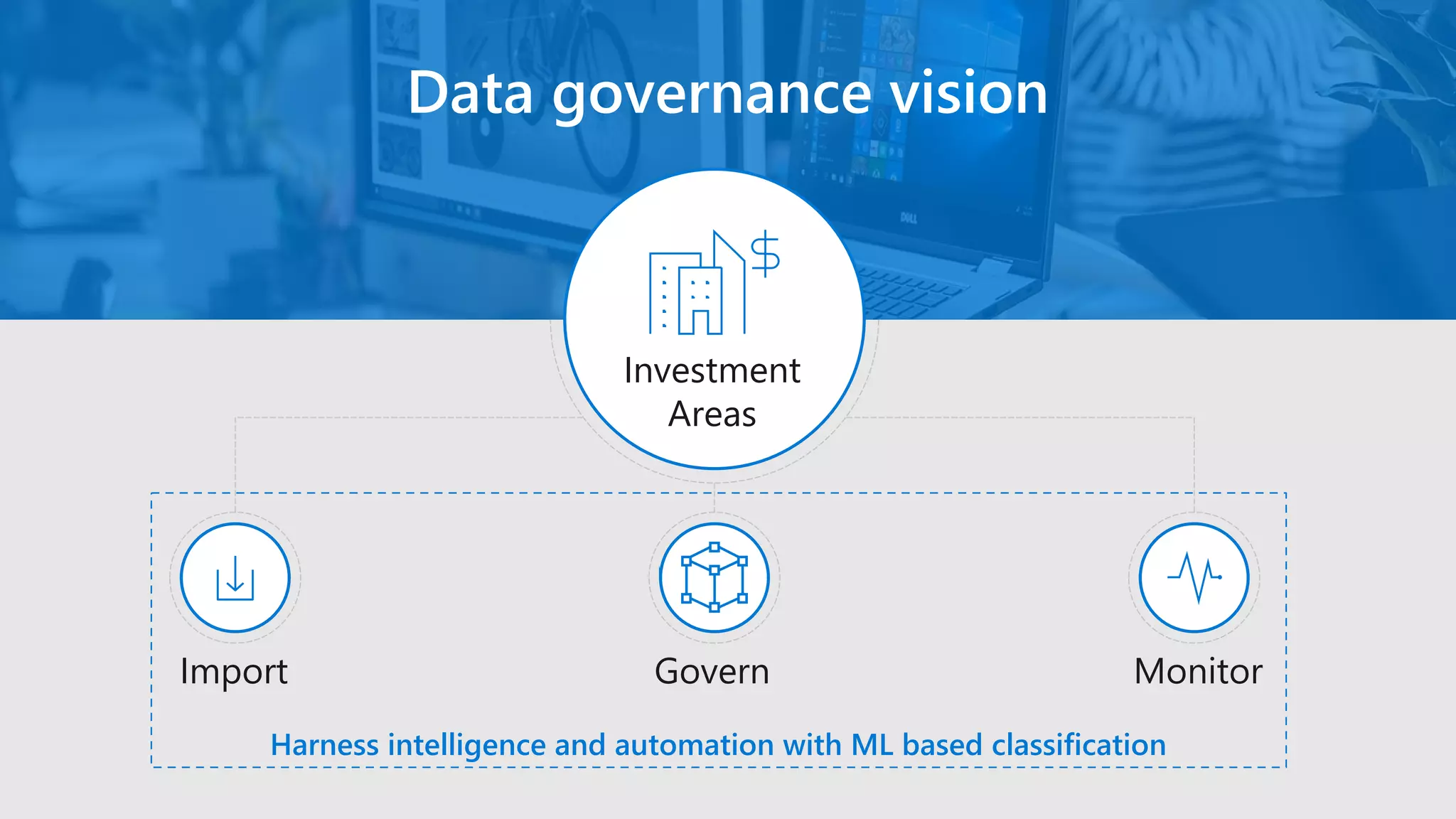
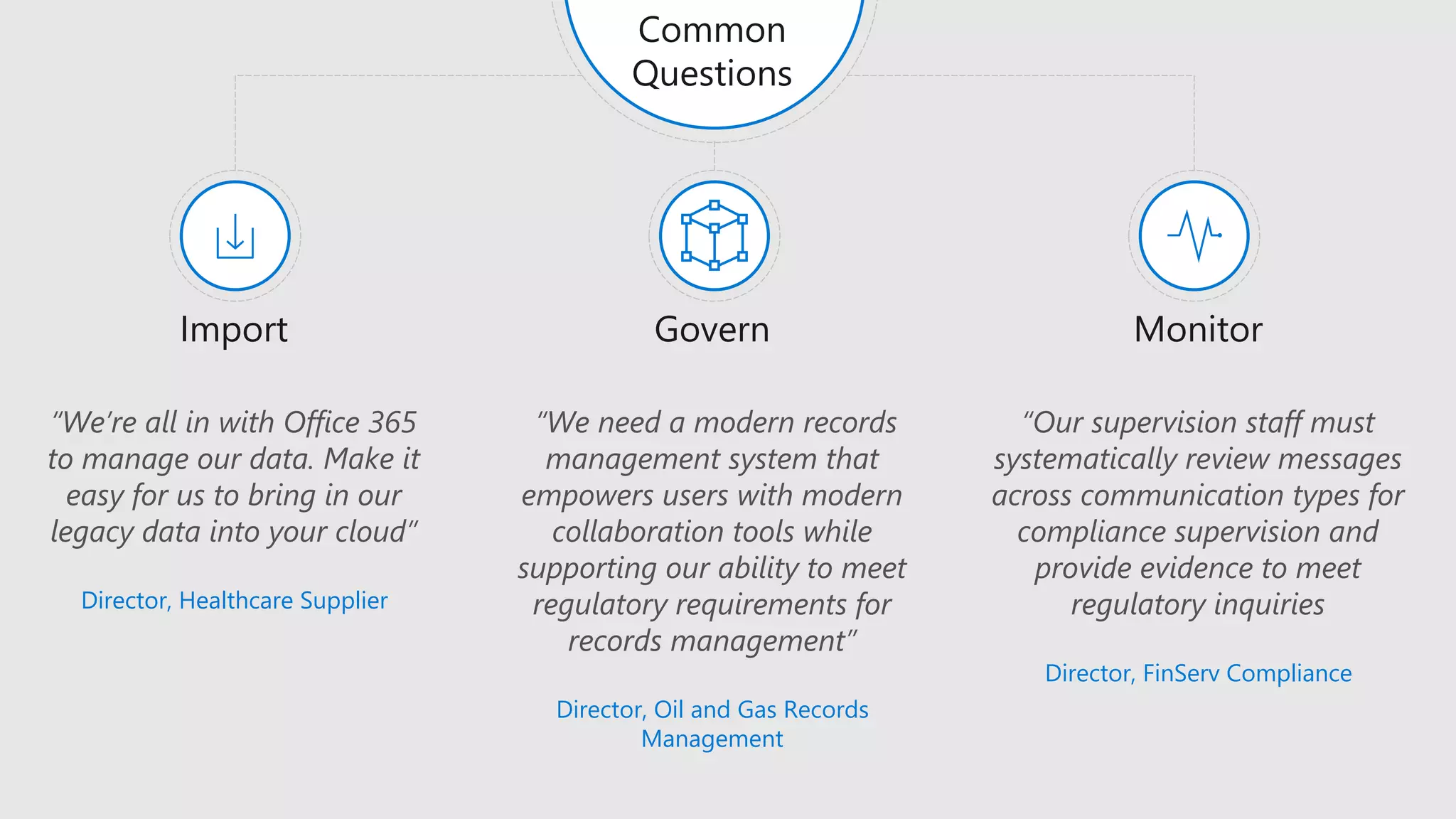
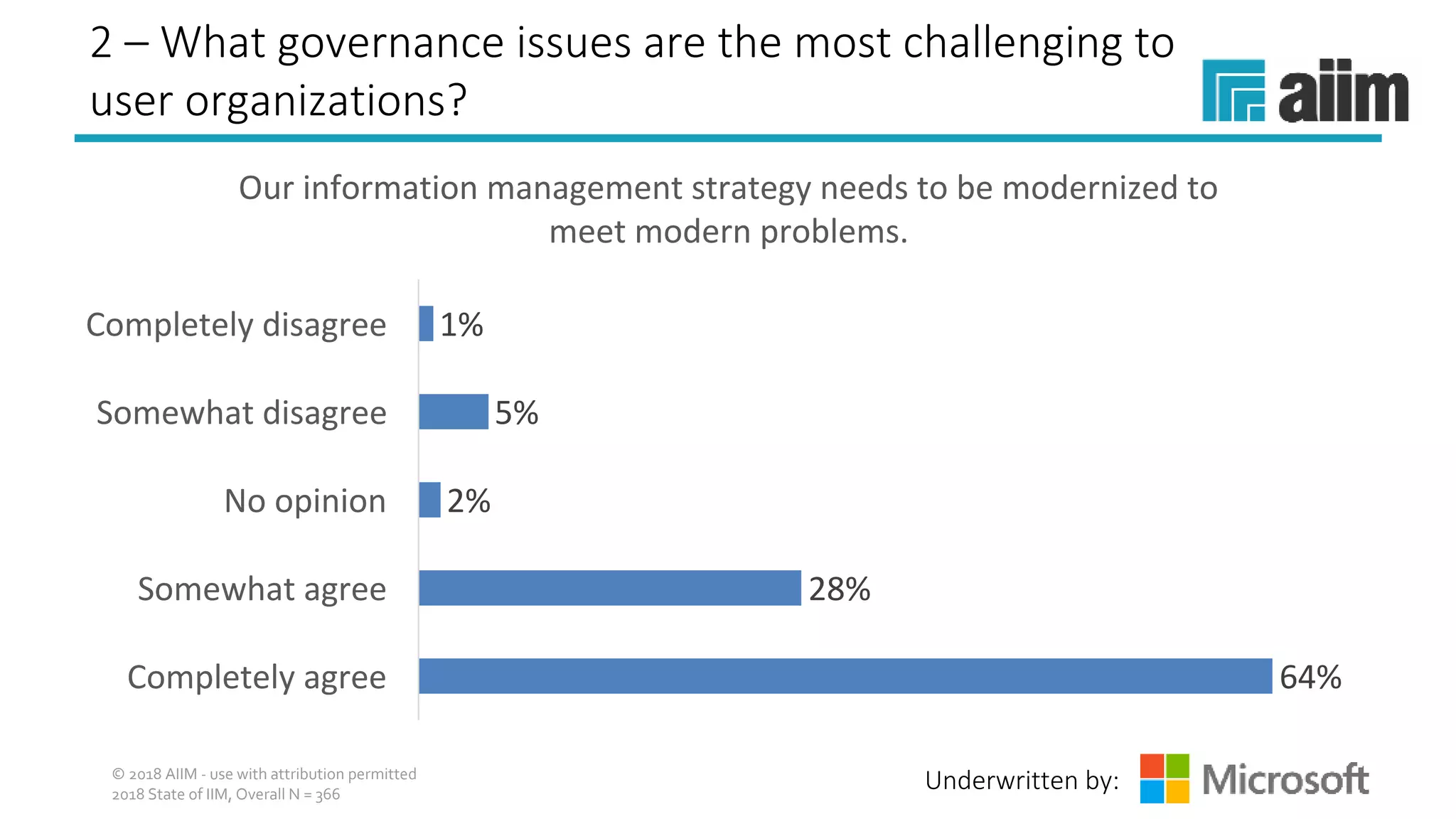
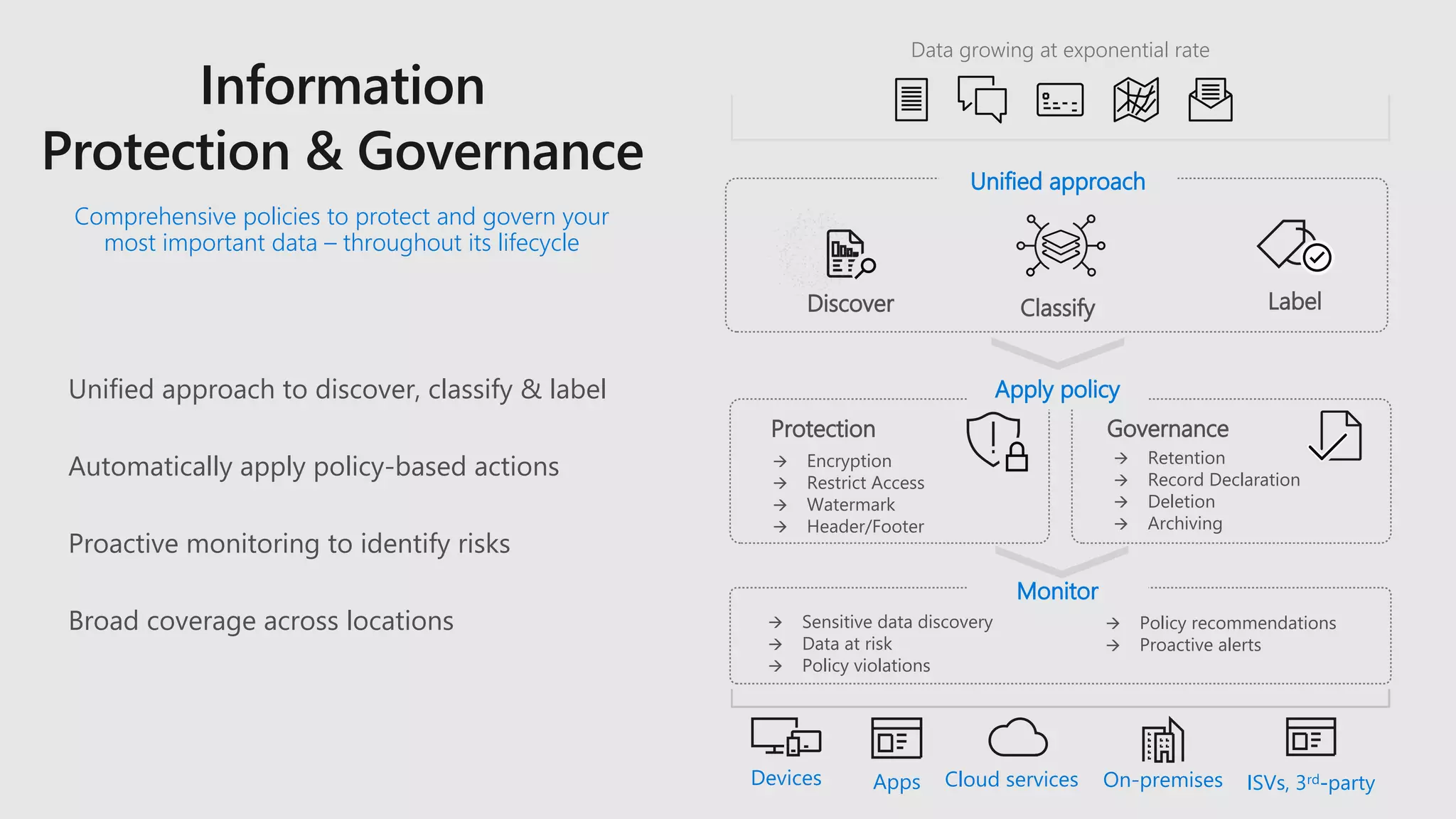
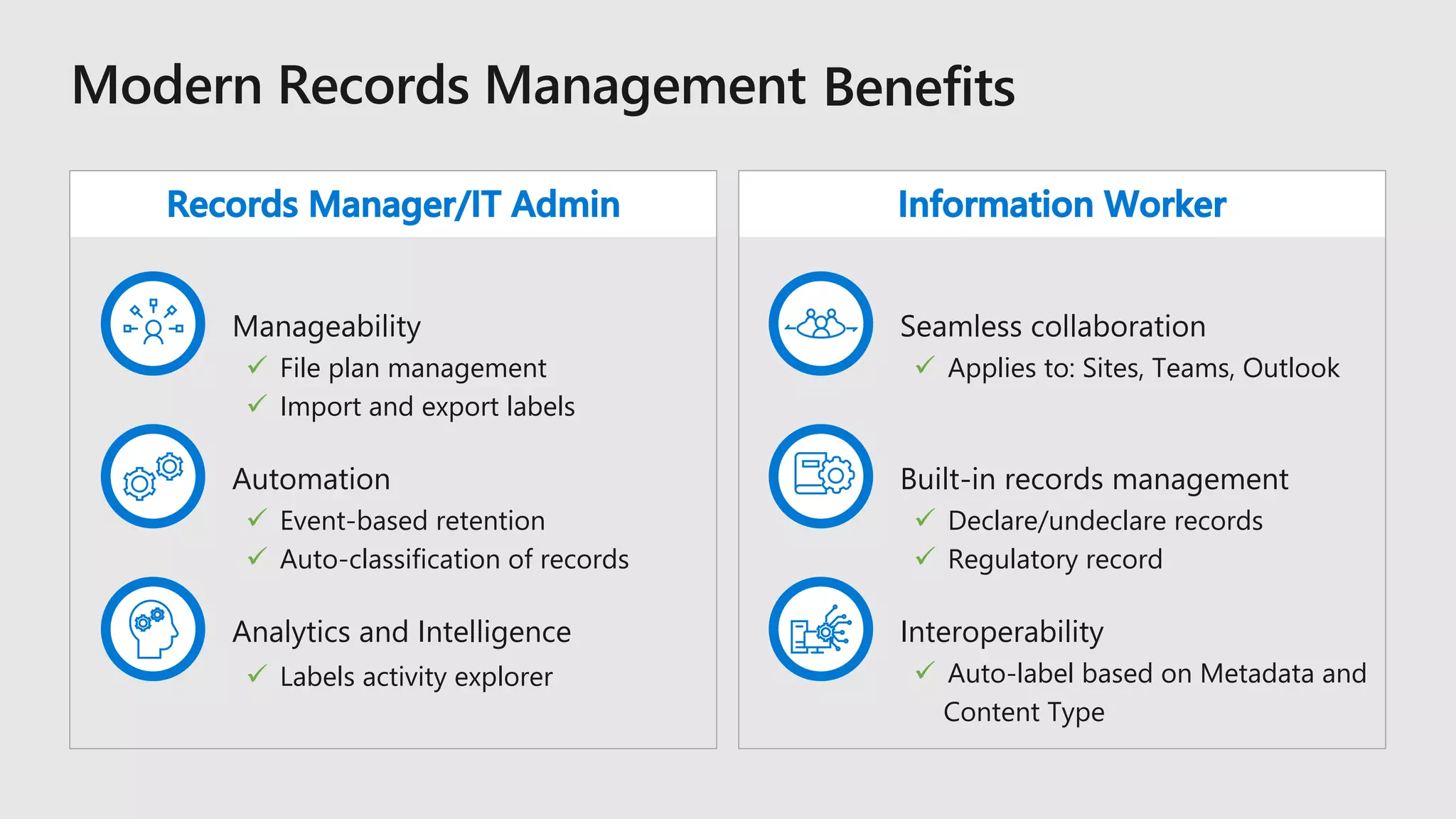
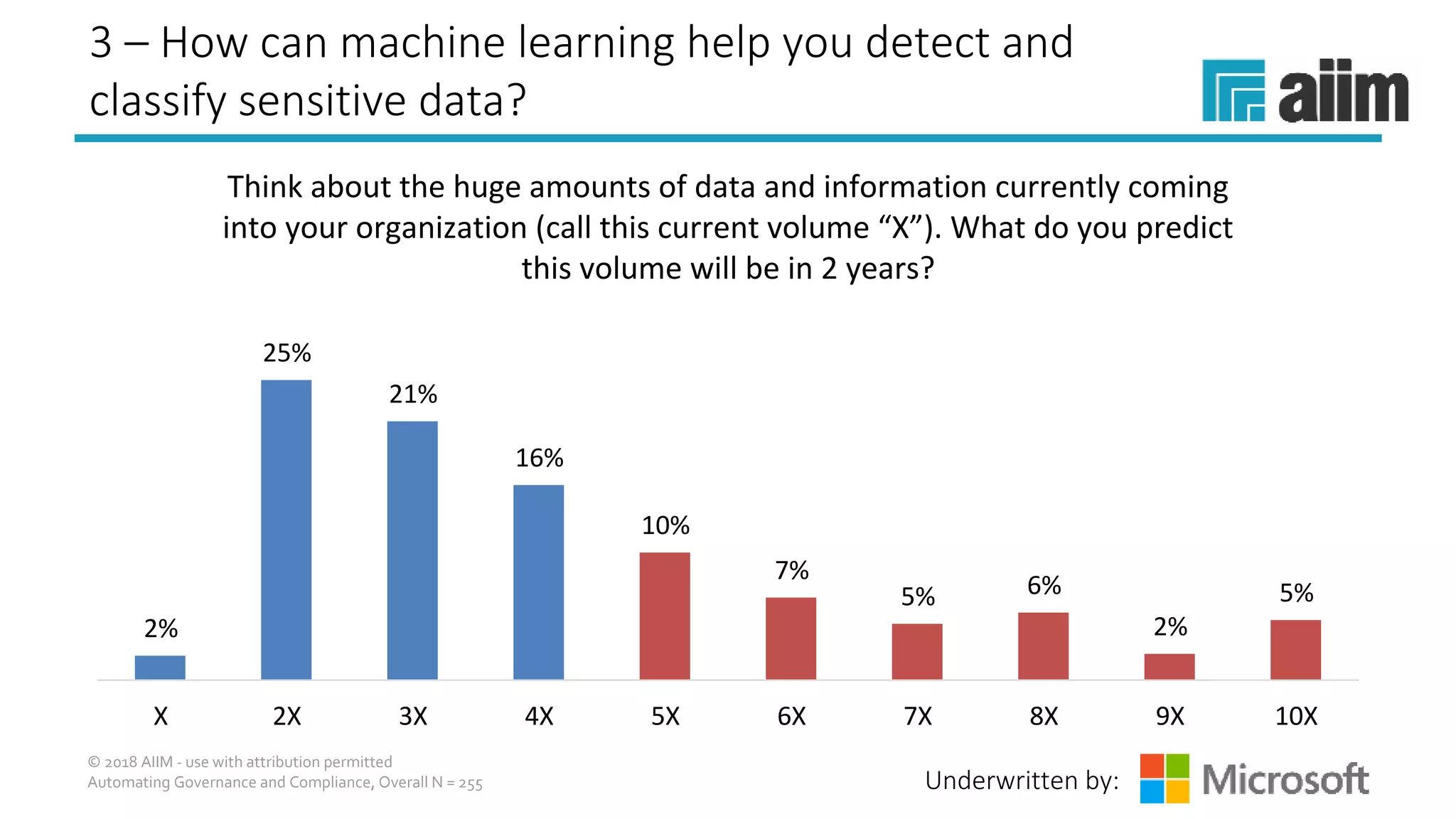
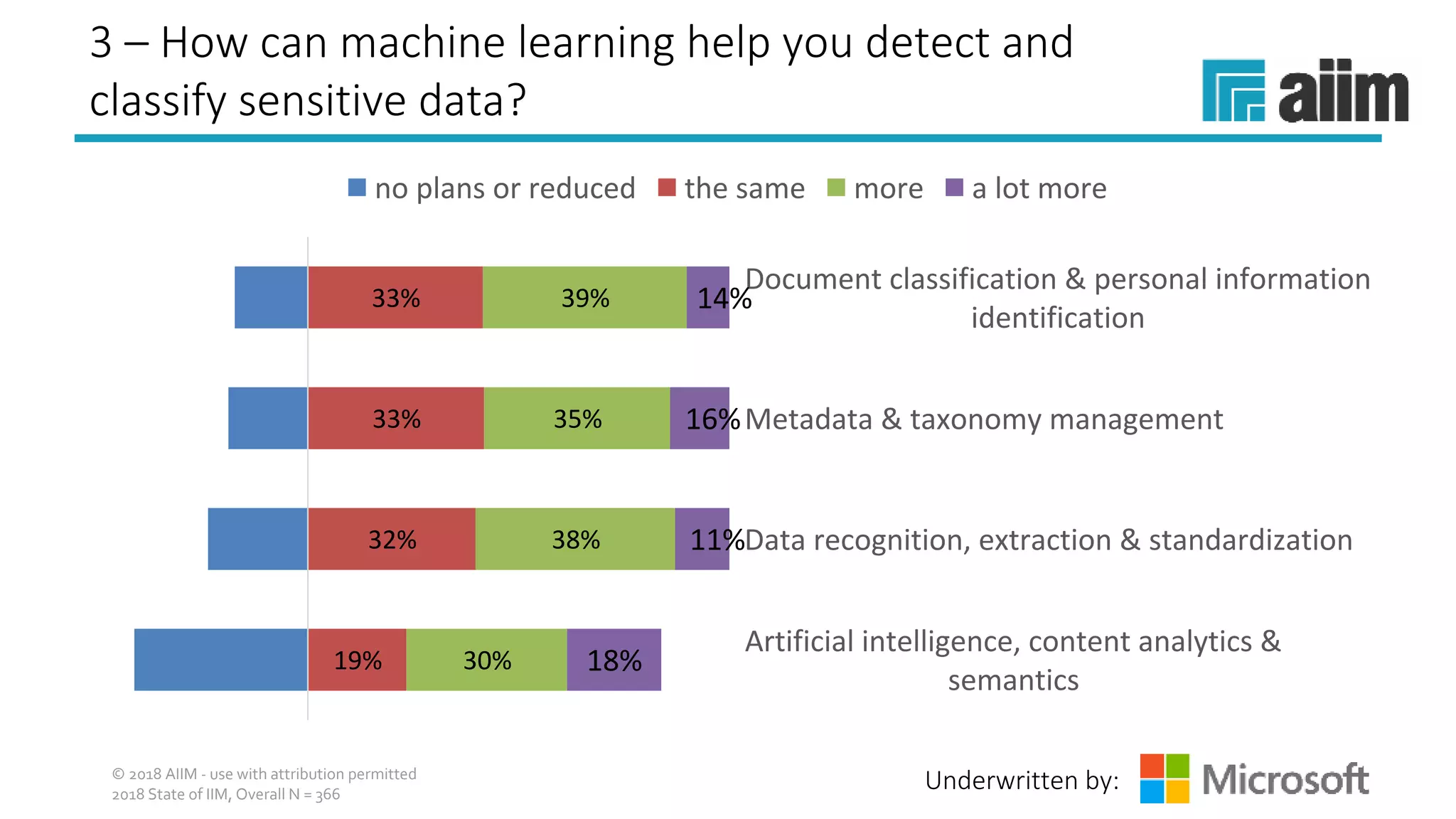
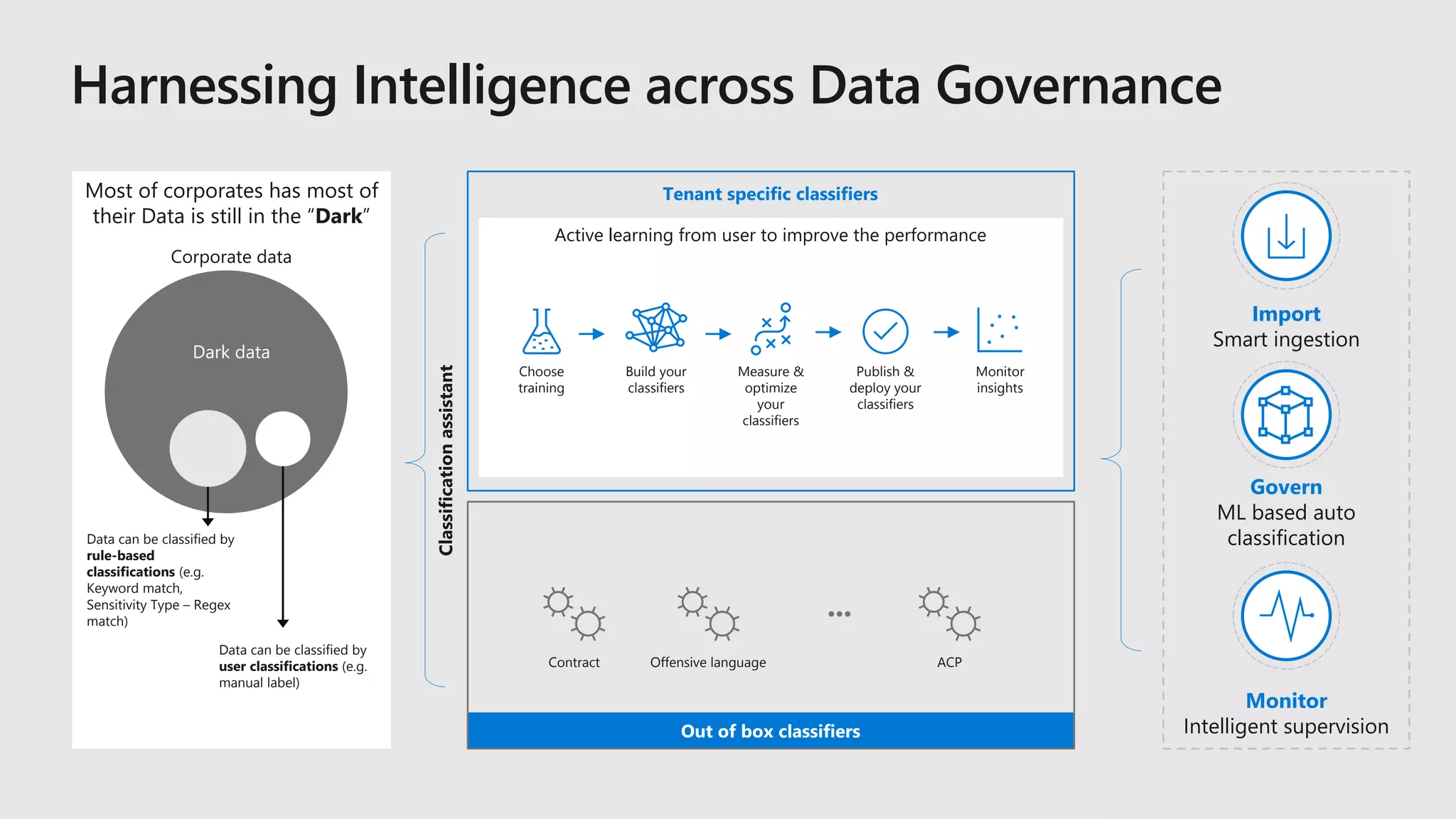
The AIIM webinar discusses strategies for managing the data explosion in organizations, focusing on finding and retaining important data while eliminating redundant information. It addresses governance issues associated with Office 365 and explores how machine learning can aid in detecting and classifying sensitive data. The presentation highlights the need for modernized information management strategies to efficiently handle data throughout its lifecycle.