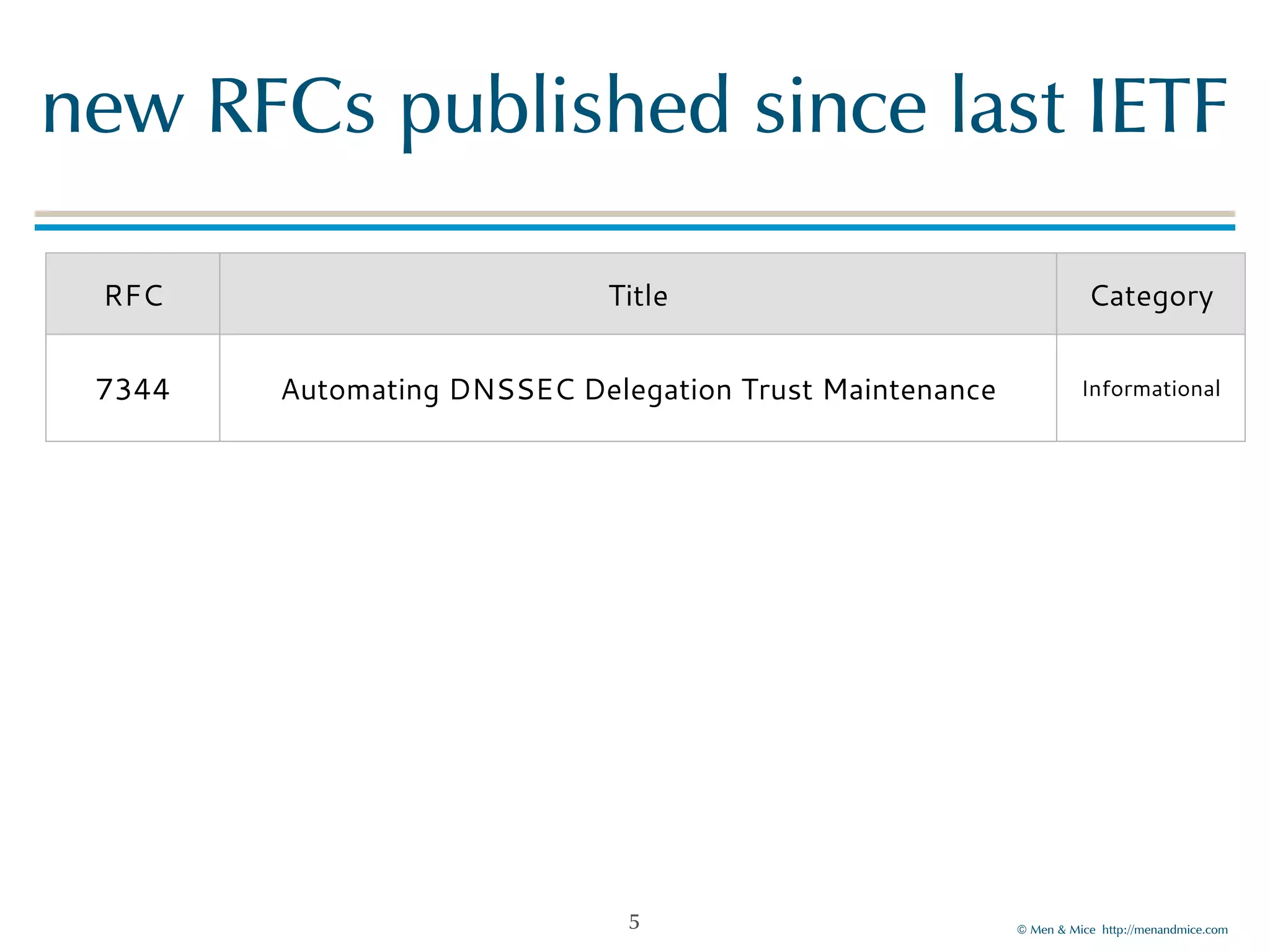
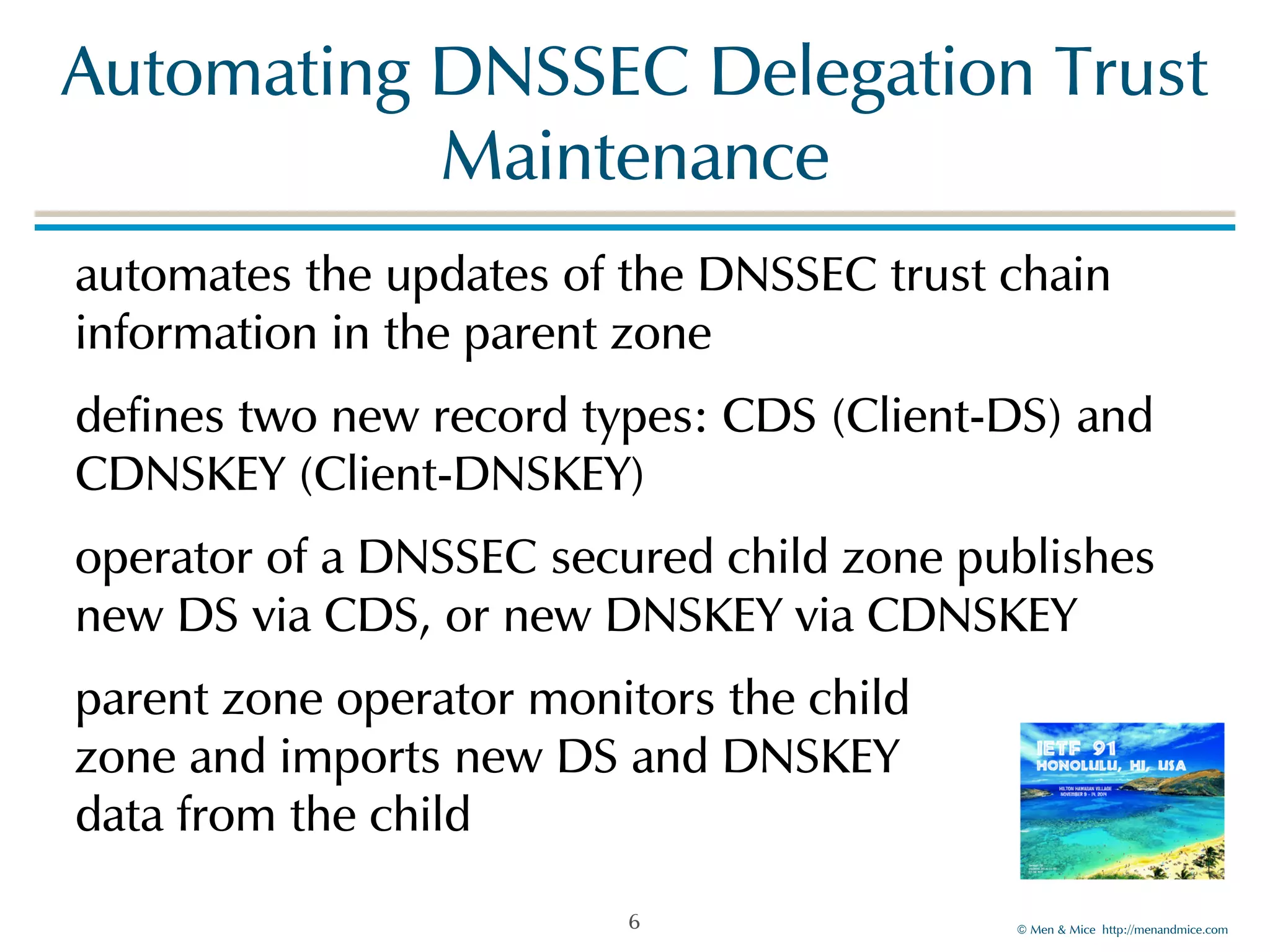
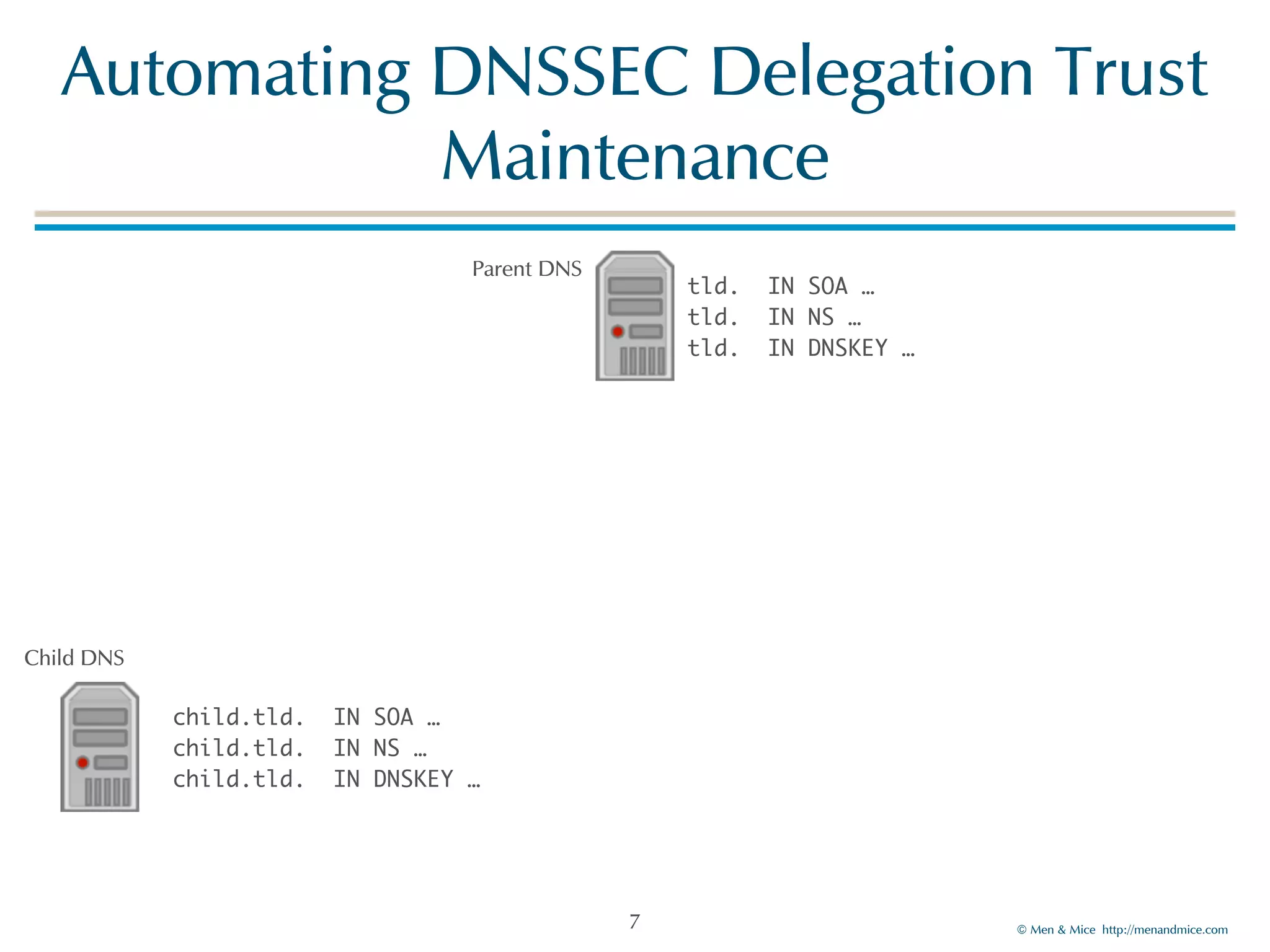
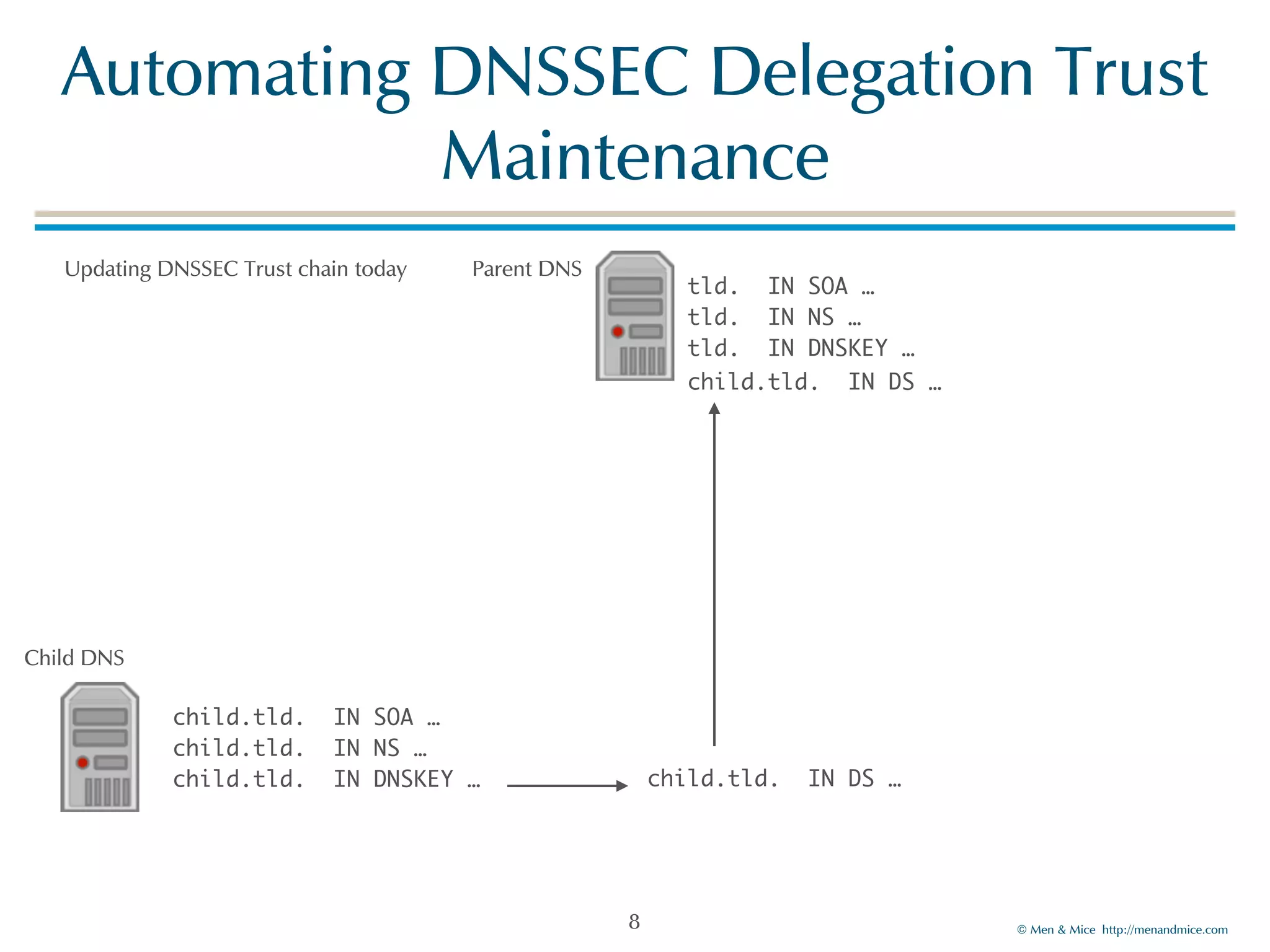
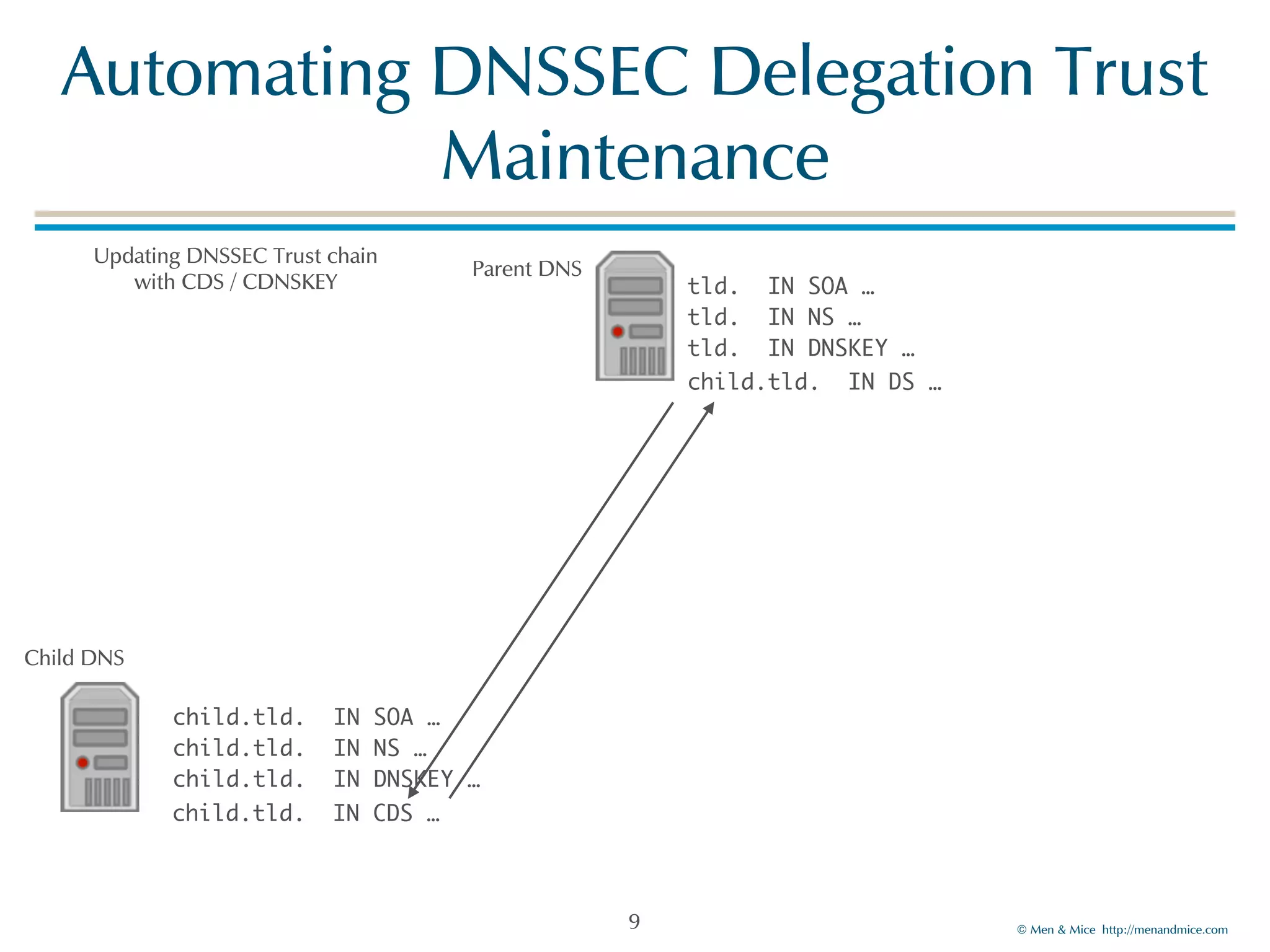
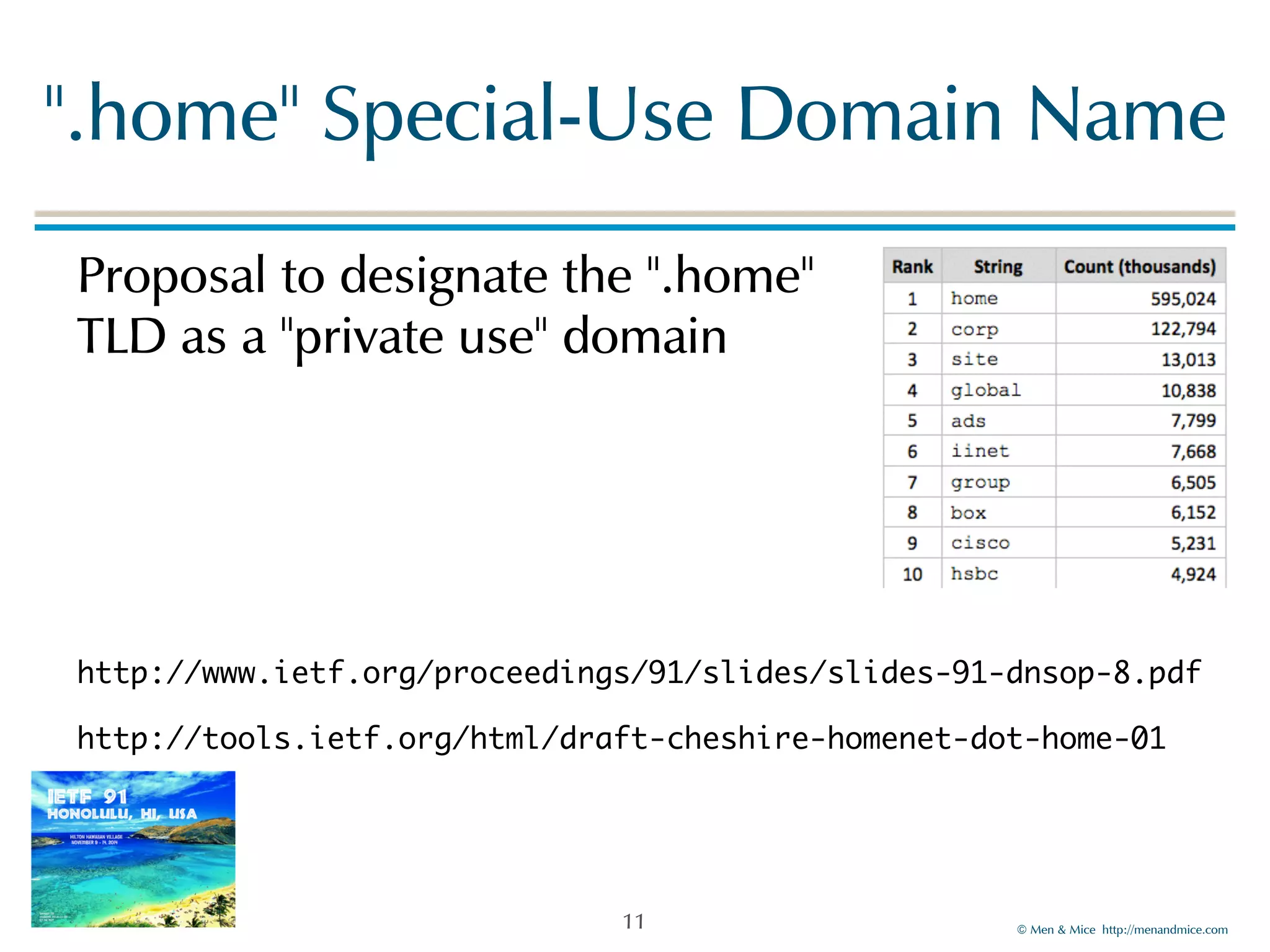
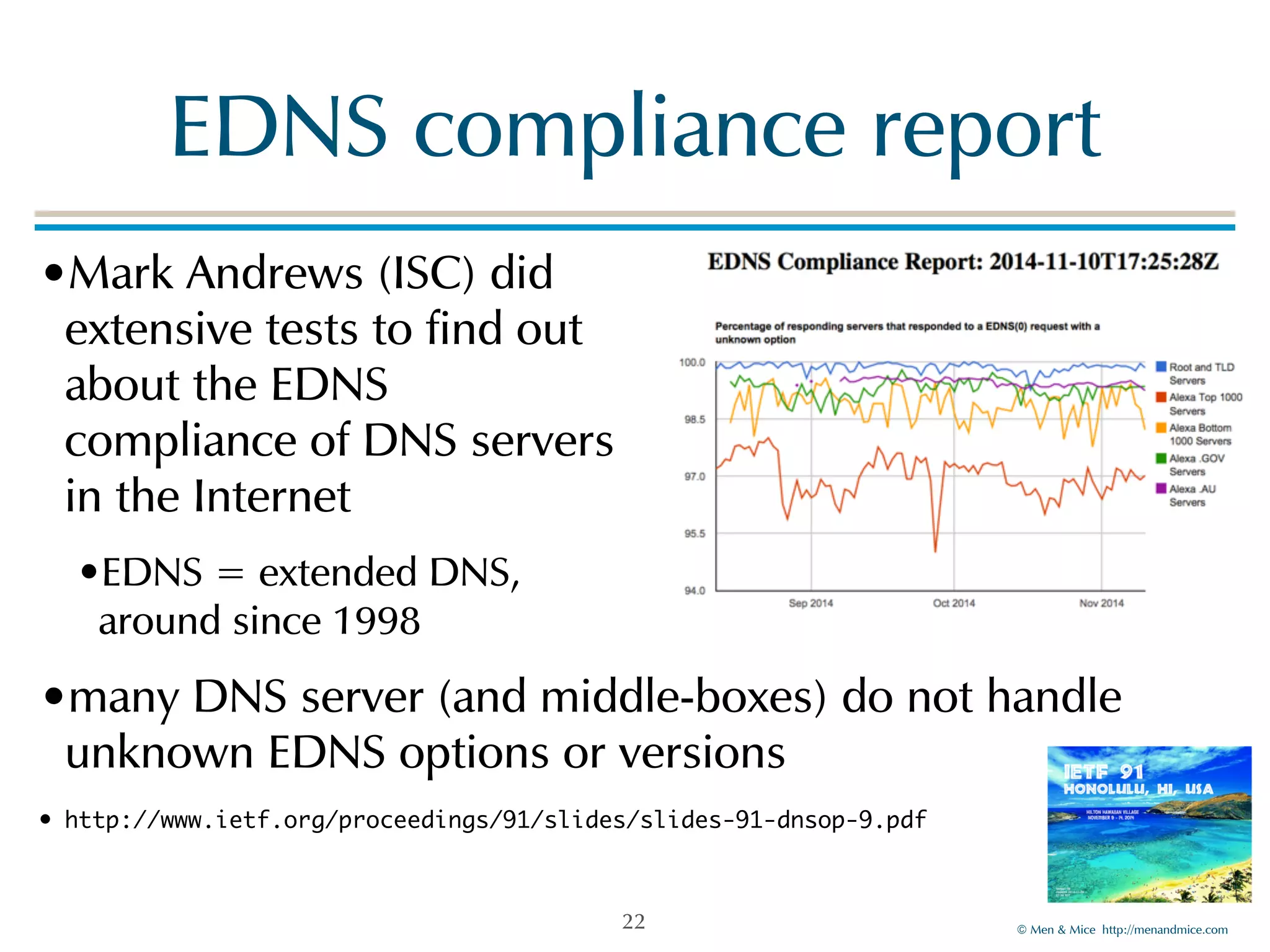
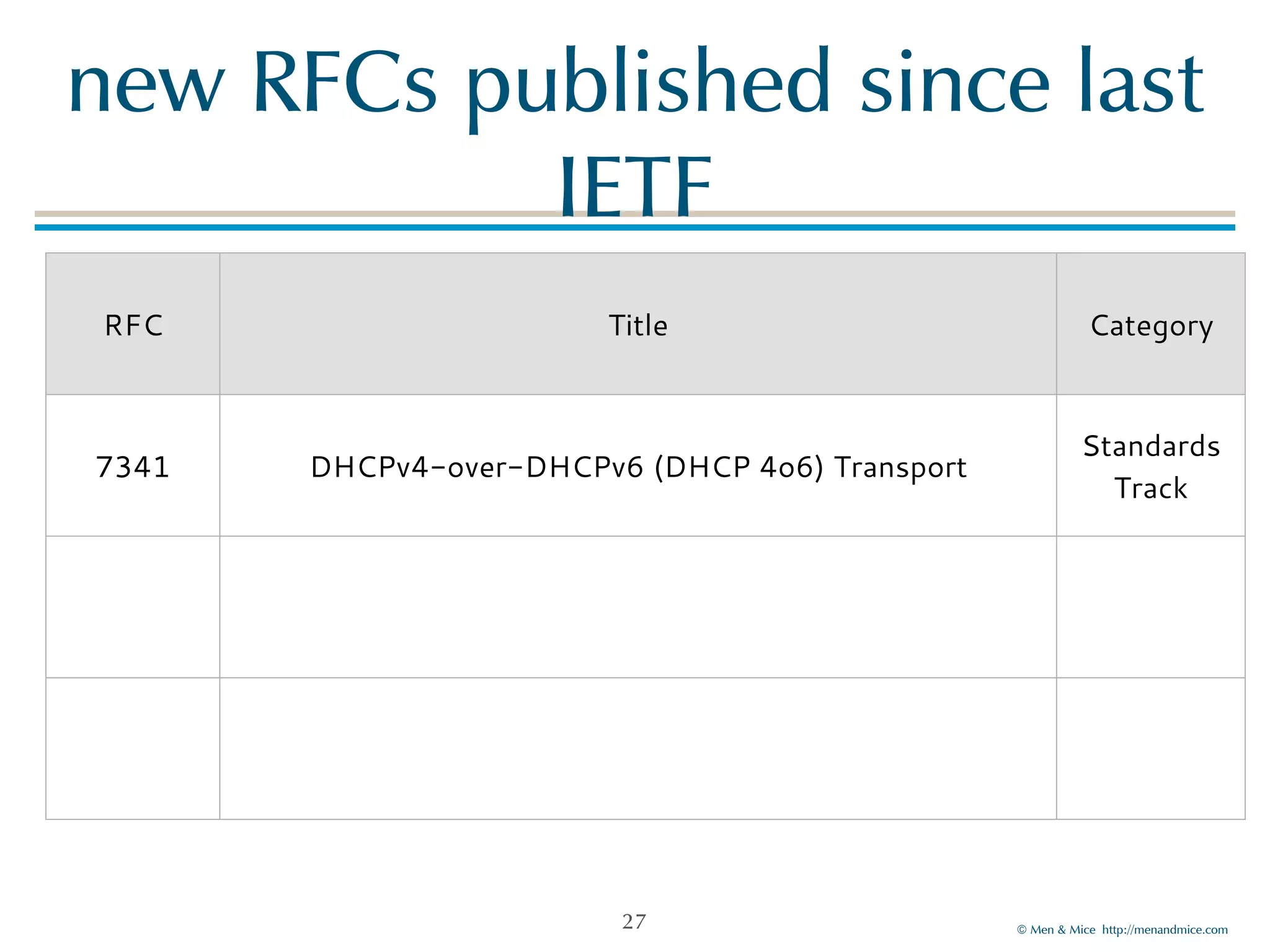
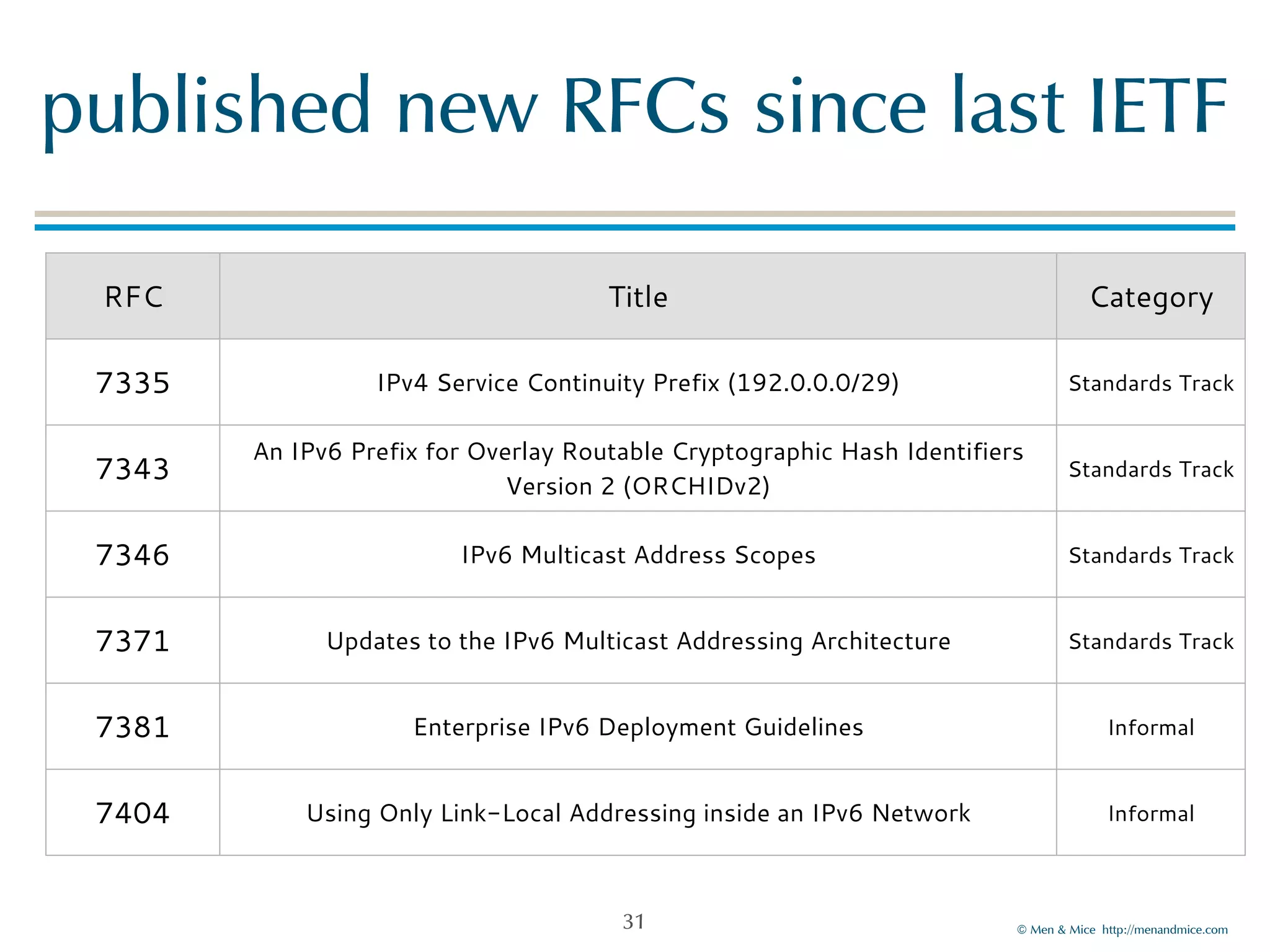
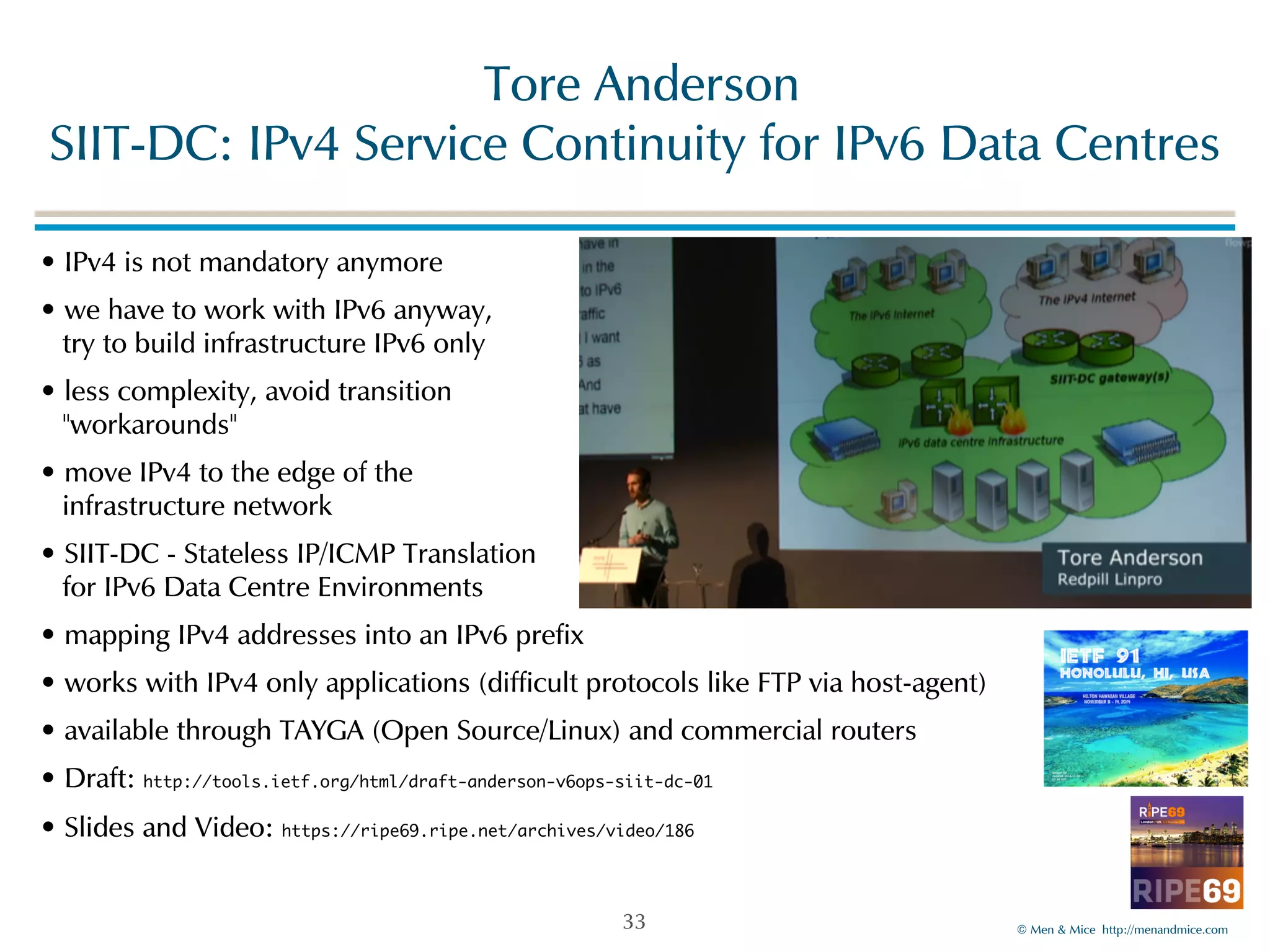
The document provides a comprehensive summary of activities and updates from the RIPE 69 meeting and IETF 91, focusing on various DNS and DHCP topics, new RFCs, and innovations in DNS security. It highlights significant presentations on automating DNSSEC delegation, DNS privacy initiatives, and the challenges associated with implementing IPv6. Additionally, the document offers links to relevant video archives and slides for further information.