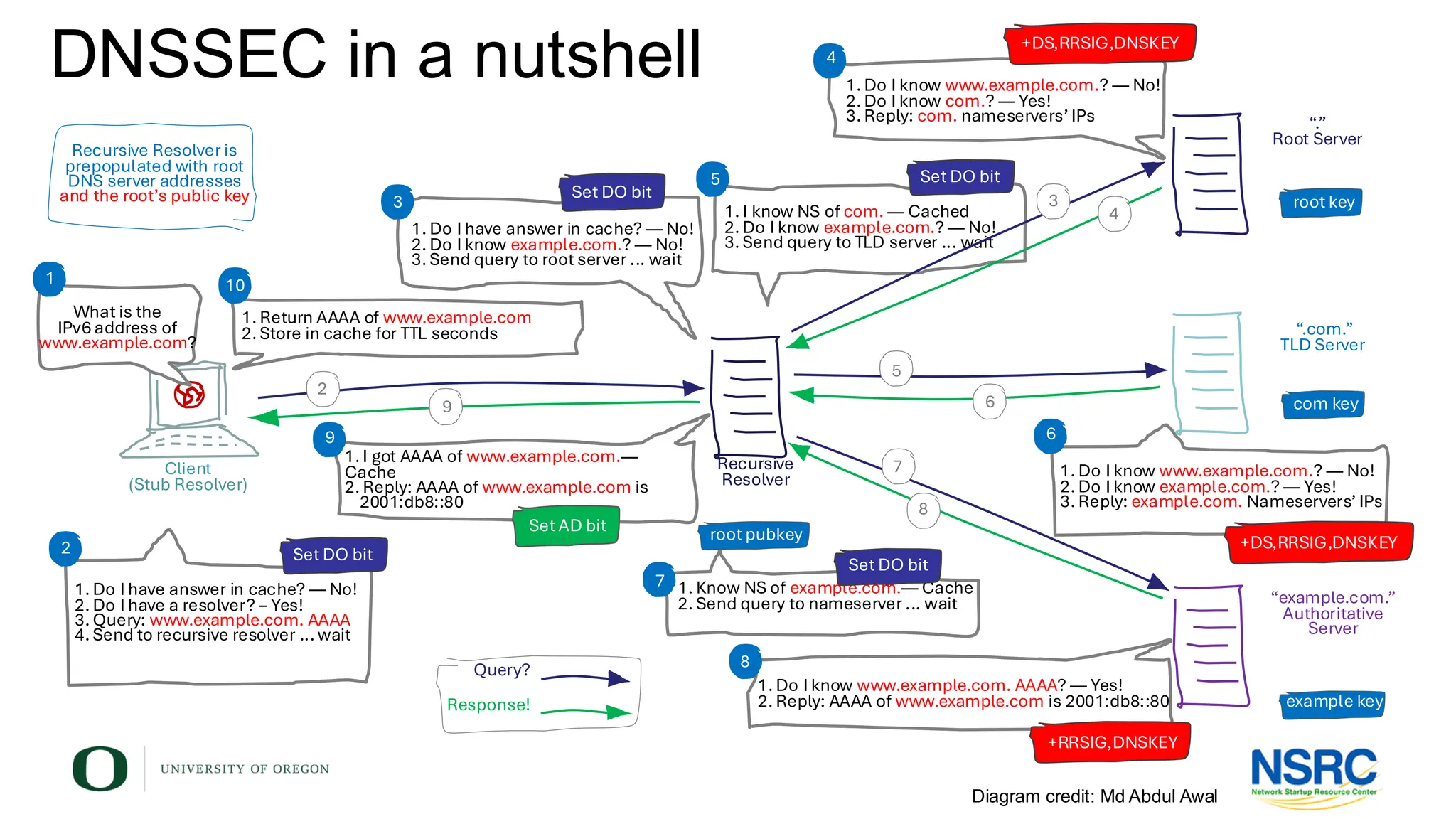
The Domain Name System (DNS) is a critical part of the Internet infrastructure. DNS translates the domain names of websites and email addresses that people can remember to the IP addresses that computers can understand. It is a large distributed system with many moving parts.
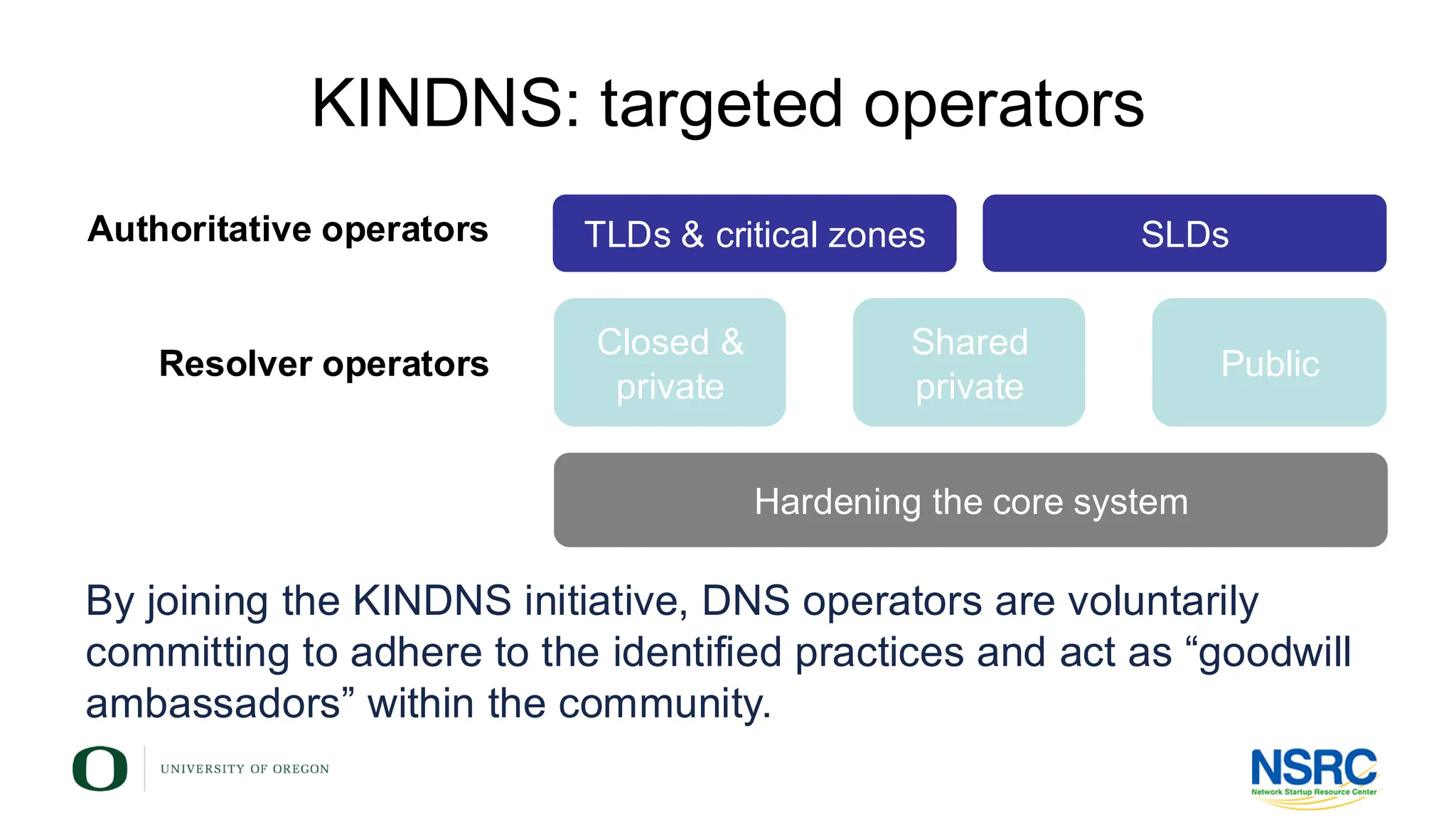
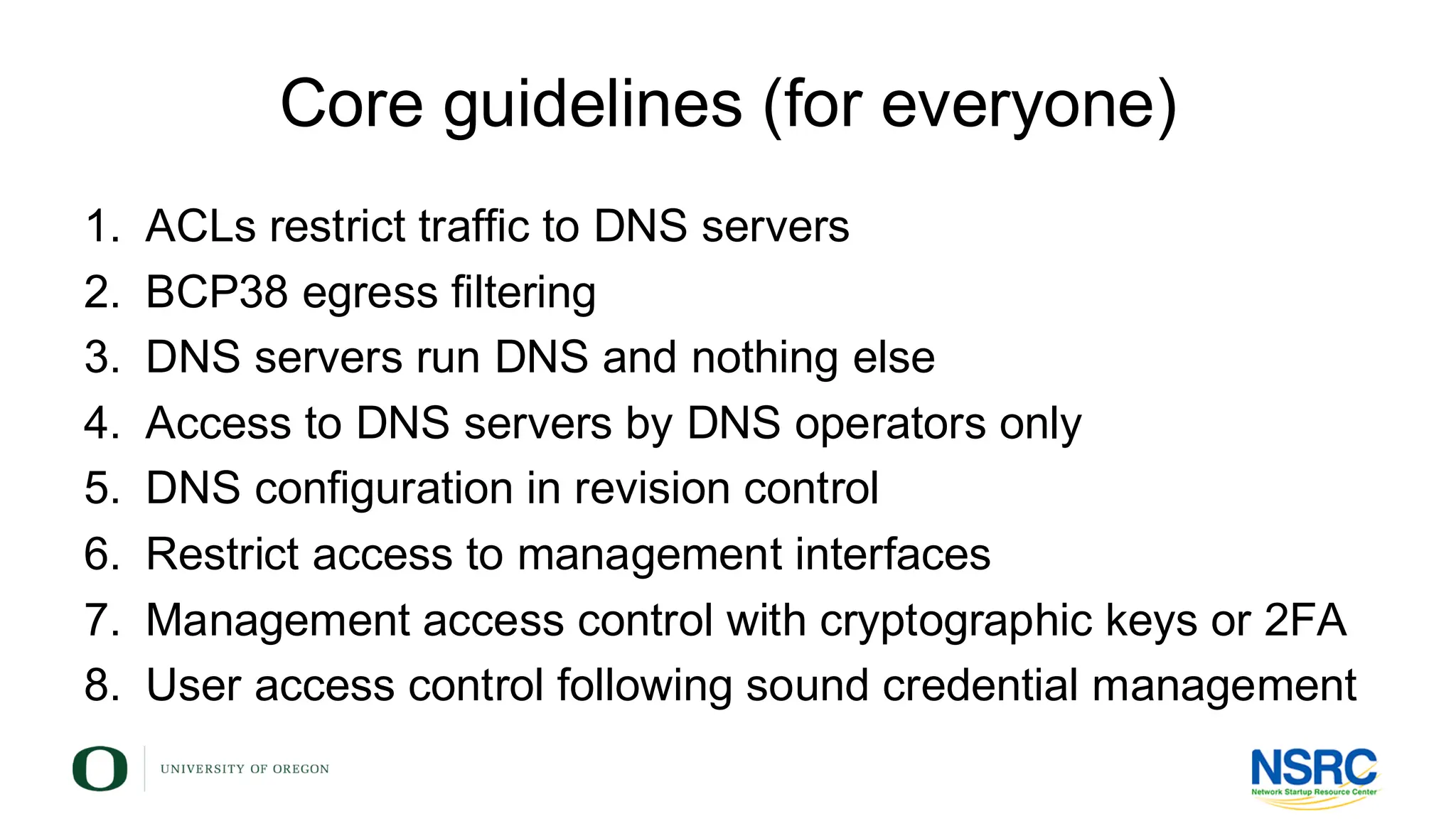
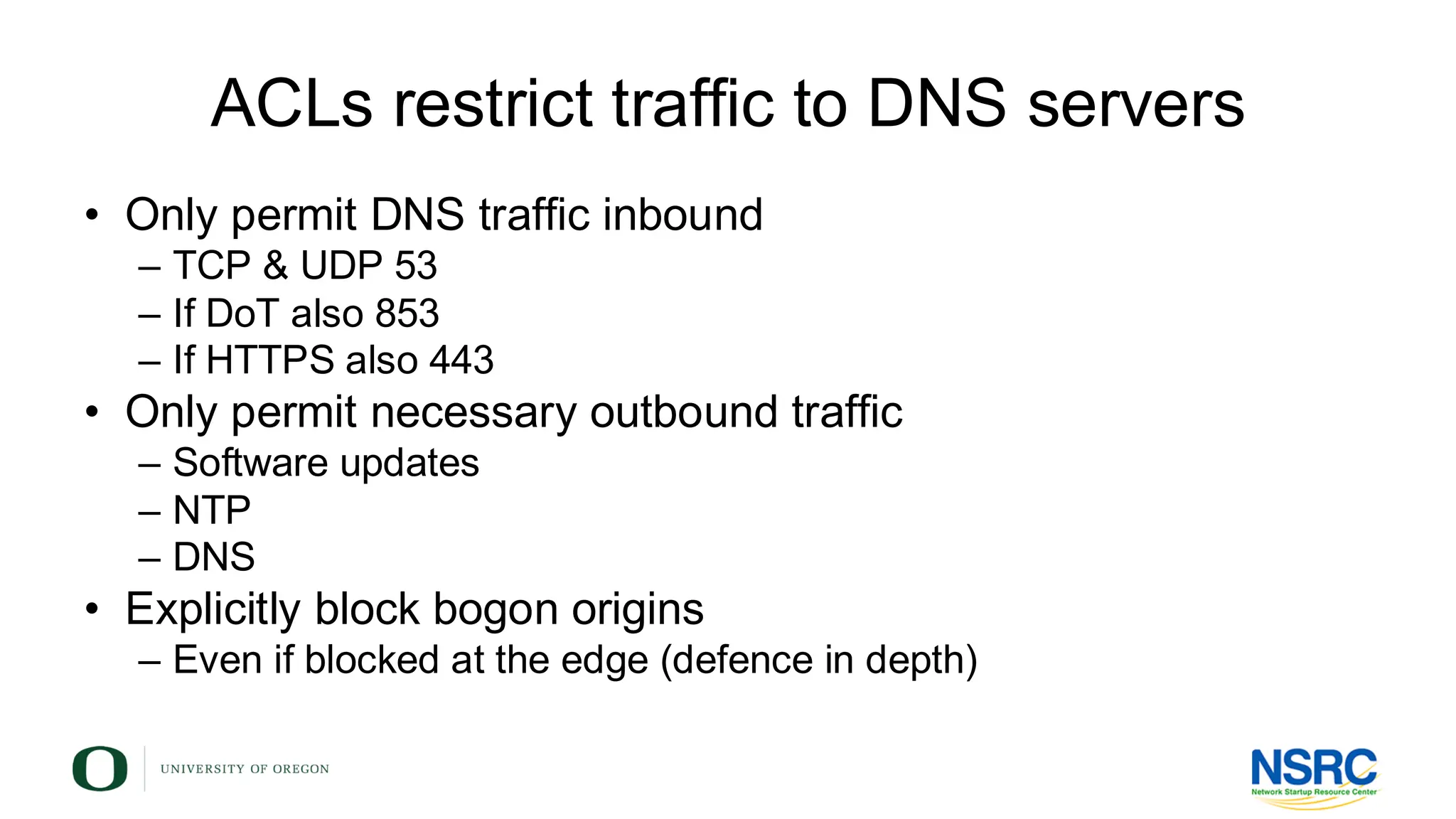
KINDNS is simple framework for stable and secure DNS operations. The KINDNS guidelines are current best practices for DNS operators to improve the security and reliability of their operations.
![Sign your zones
• Avoid administrative overhead of resigning zones
– BIND does that automatically
zone "example.com" in {
type master;
file ”db.example.com";
key-directory "/etc/bind/keys";
inline-signing yes;
auto-dnssec maintain;
};
Where named should look
for the DNSSec key files
BIND keeps unsigned zone
and creates a signed zone
off
allow
maintain
Default. Keys are managed manually
Allows uploading keys and resigning the zone
when user runs “rndc-sign [zone-name]”
Same as “allow” +automatically
adjusts the keys on schedule](https://image.slidesharecdn.com/kindns-bdnog-2025-v117459835921-250523172450-e8c40ea4/75/DNS-DNSSEC-operational-best-practices-Sleep-better-at-night-with-KINDNS-in-your-network-27-2048.jpg)