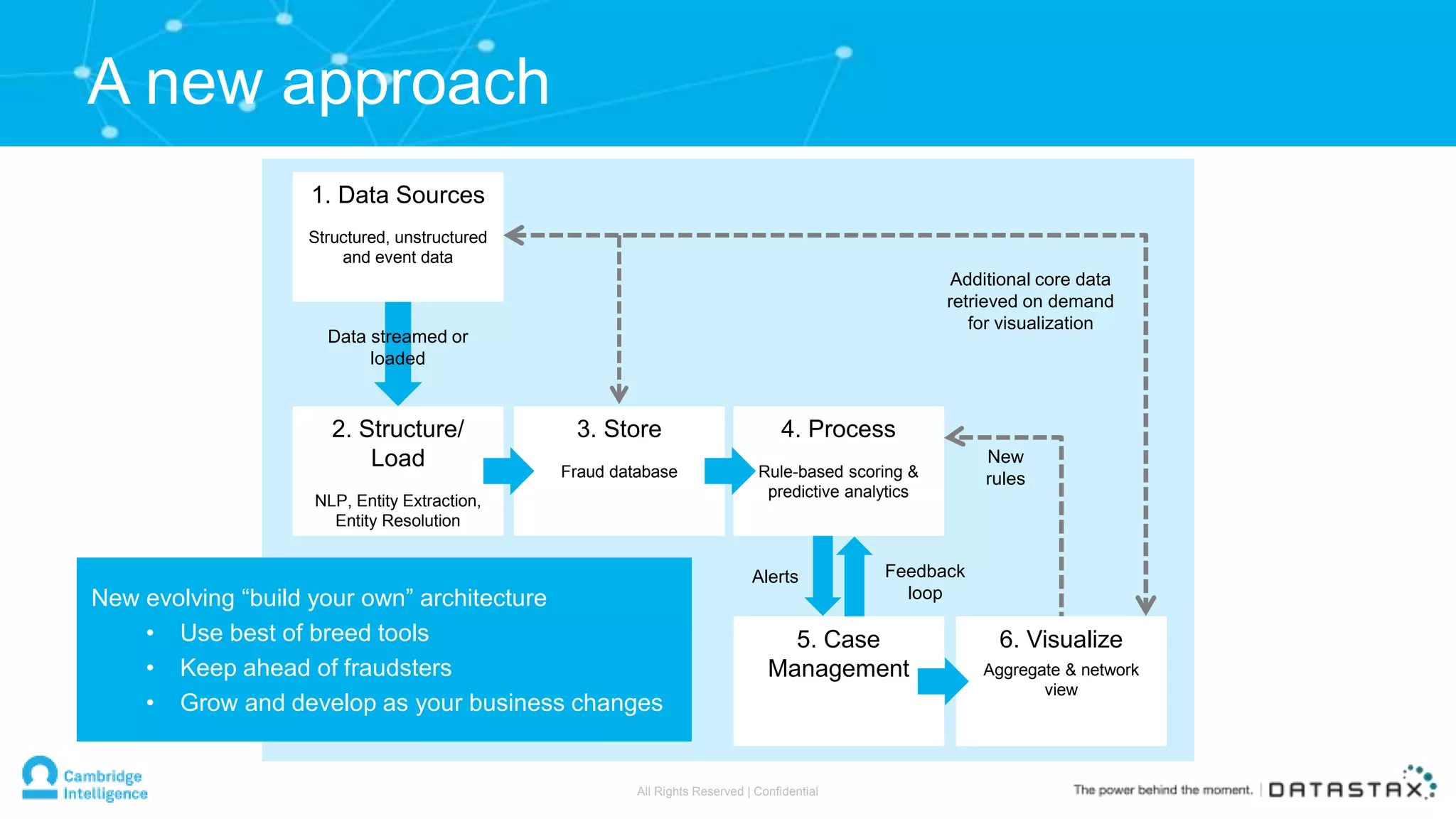
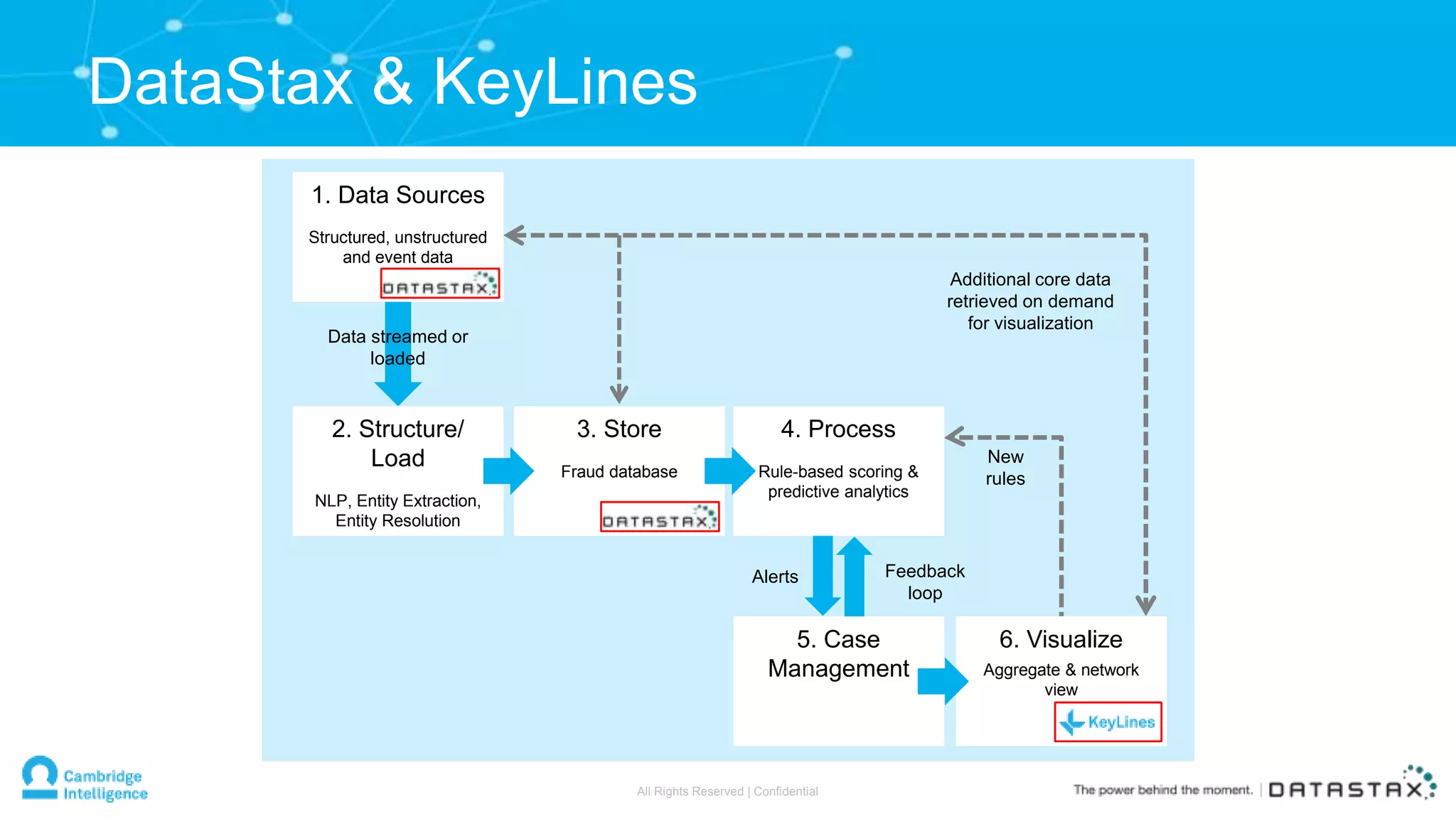
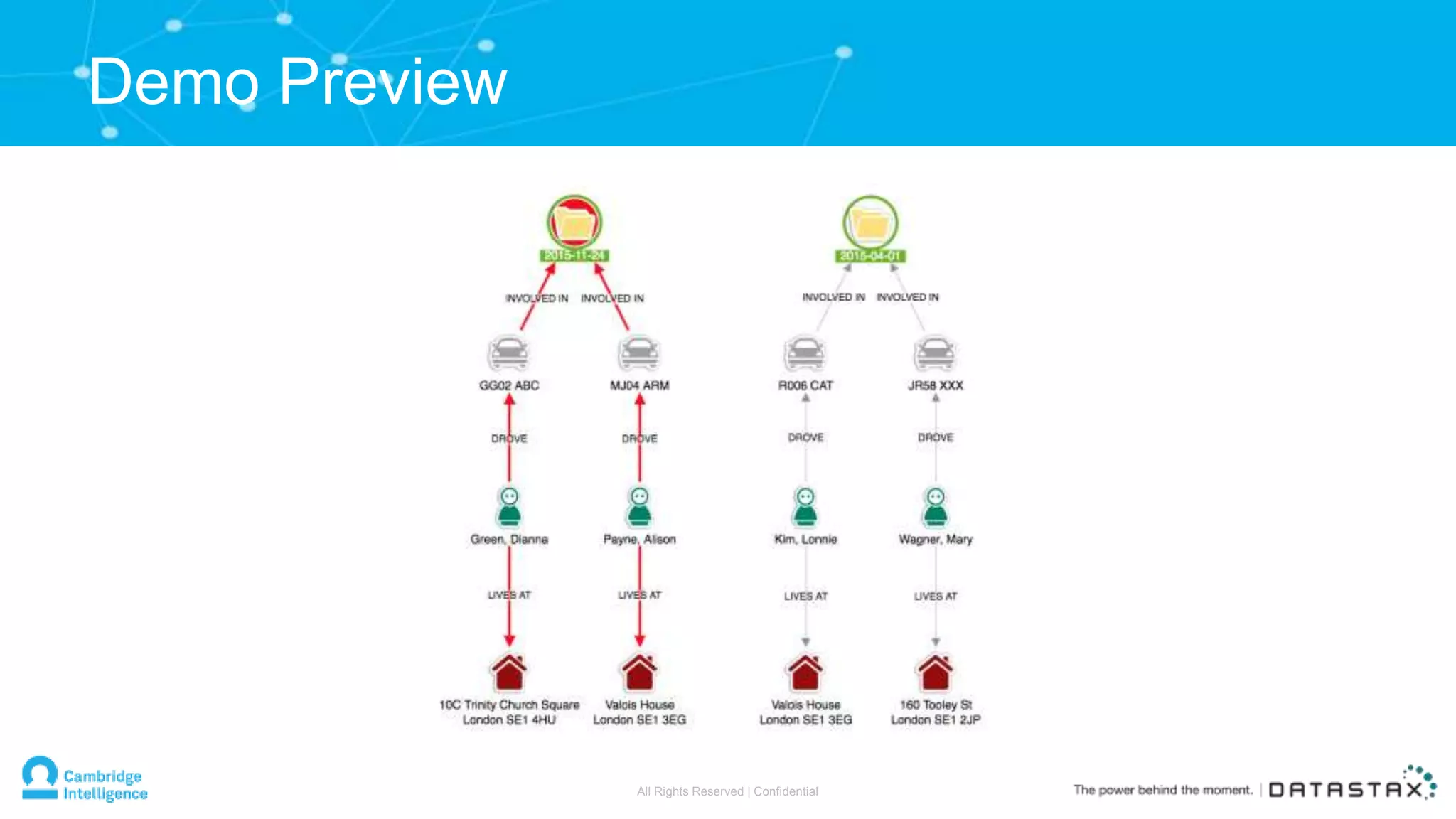
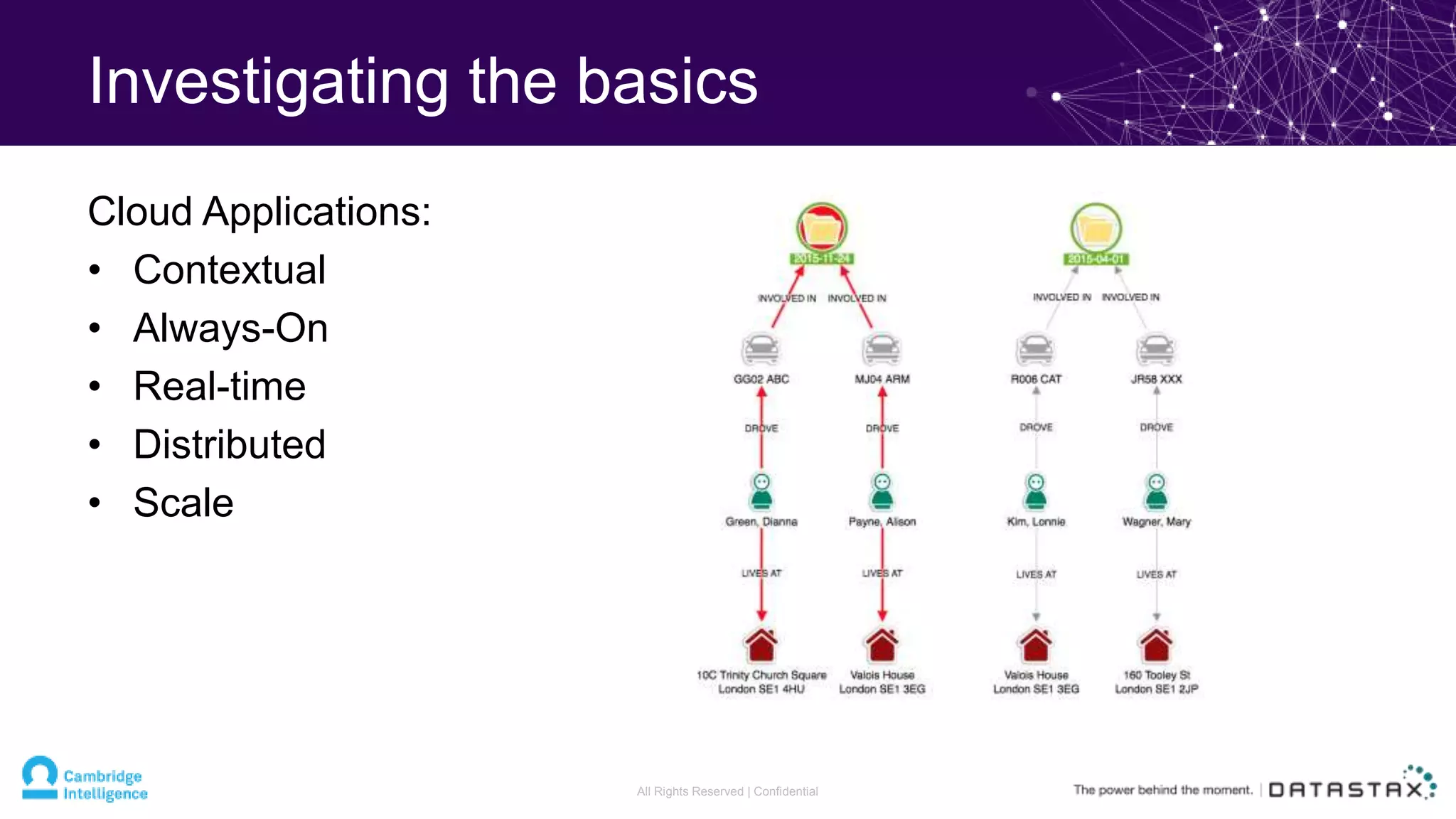
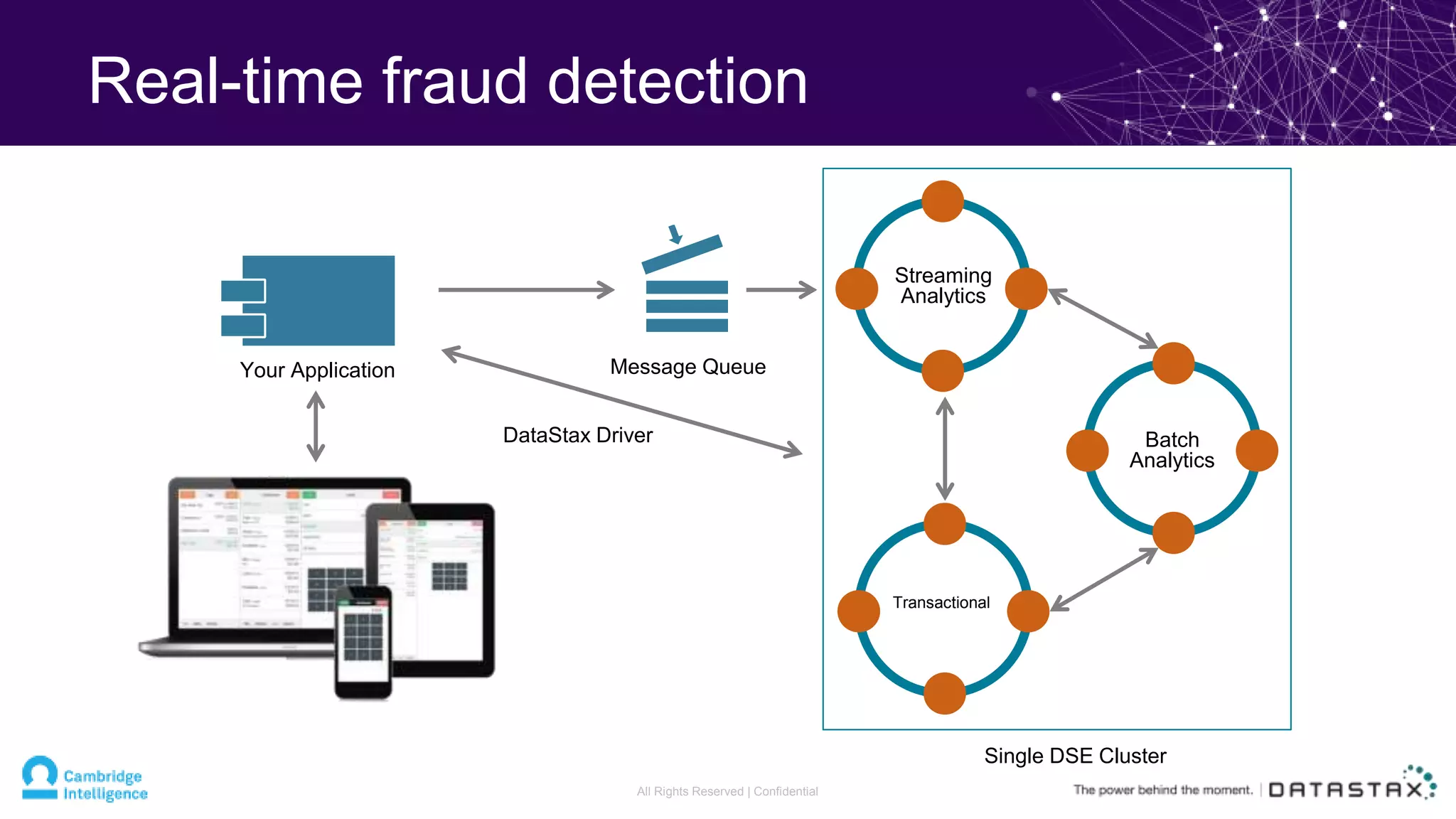
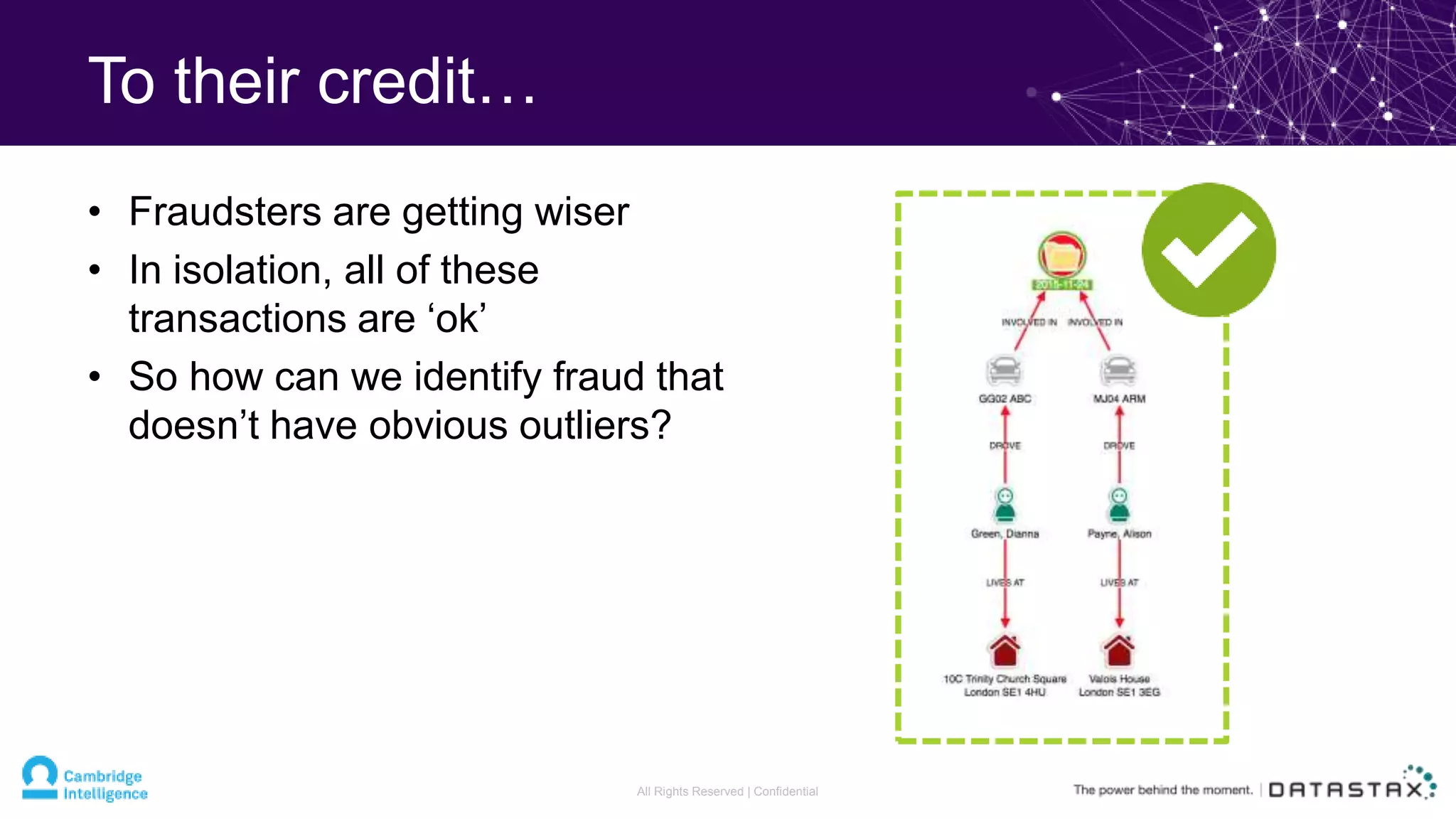
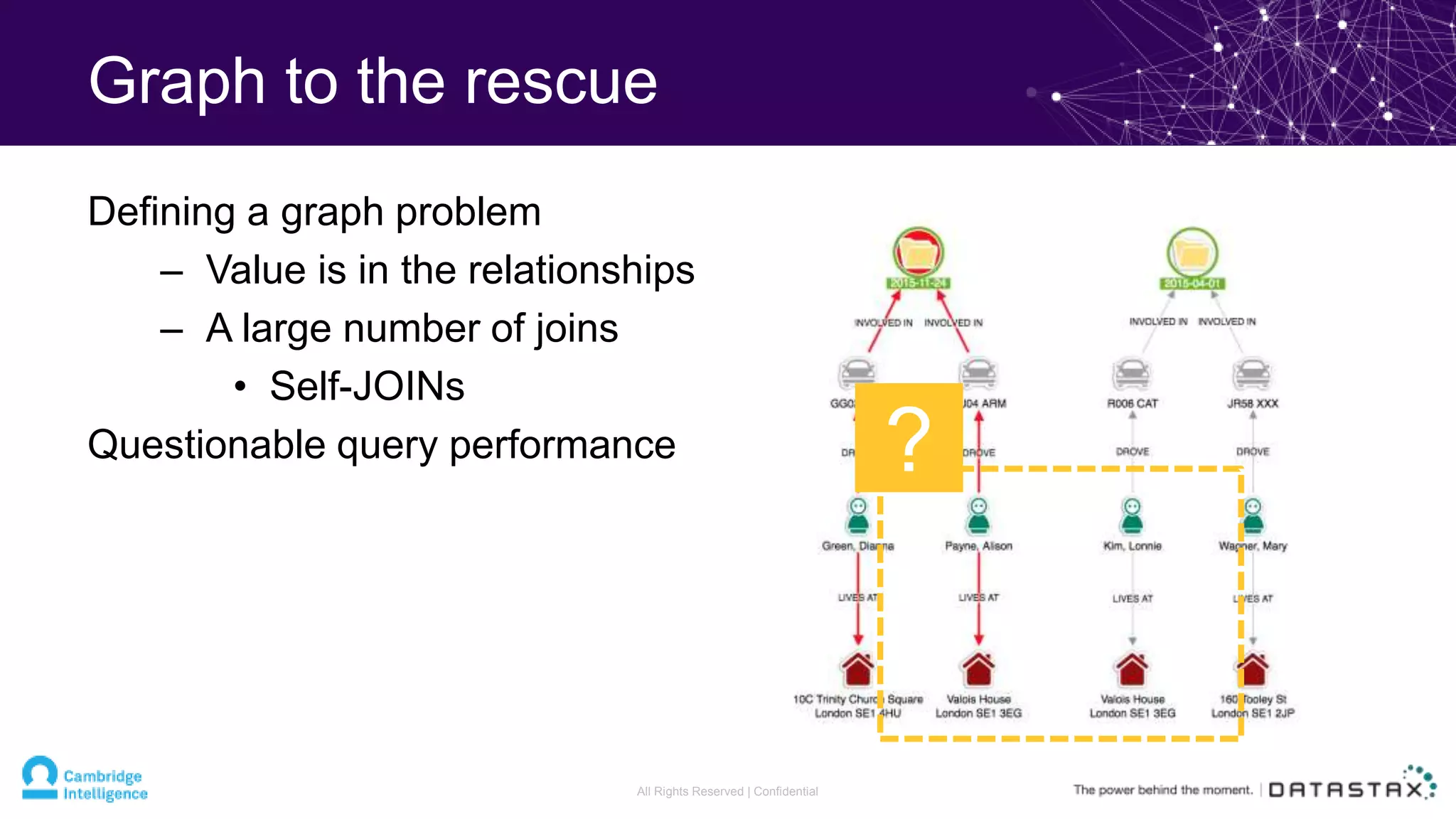
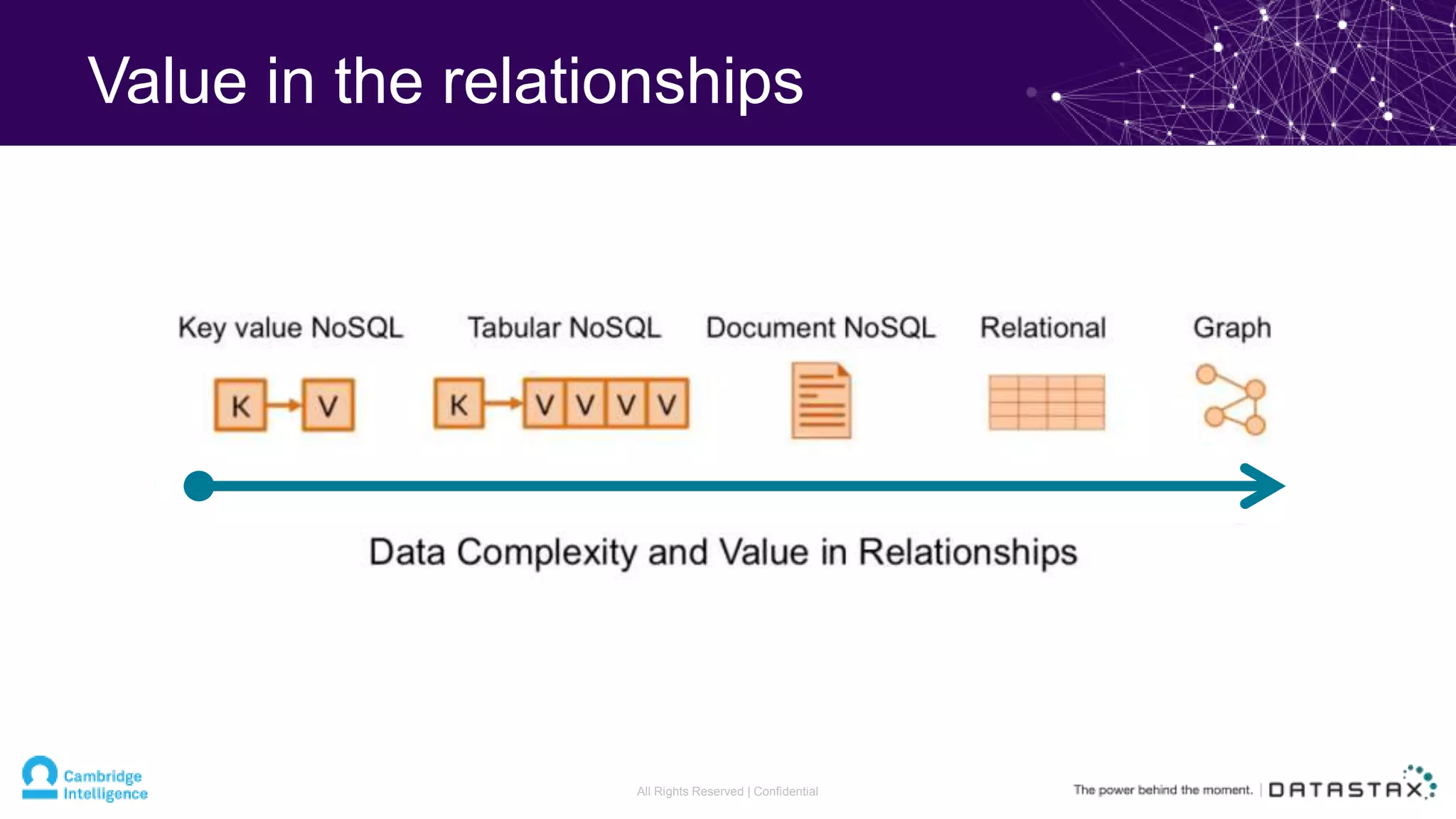
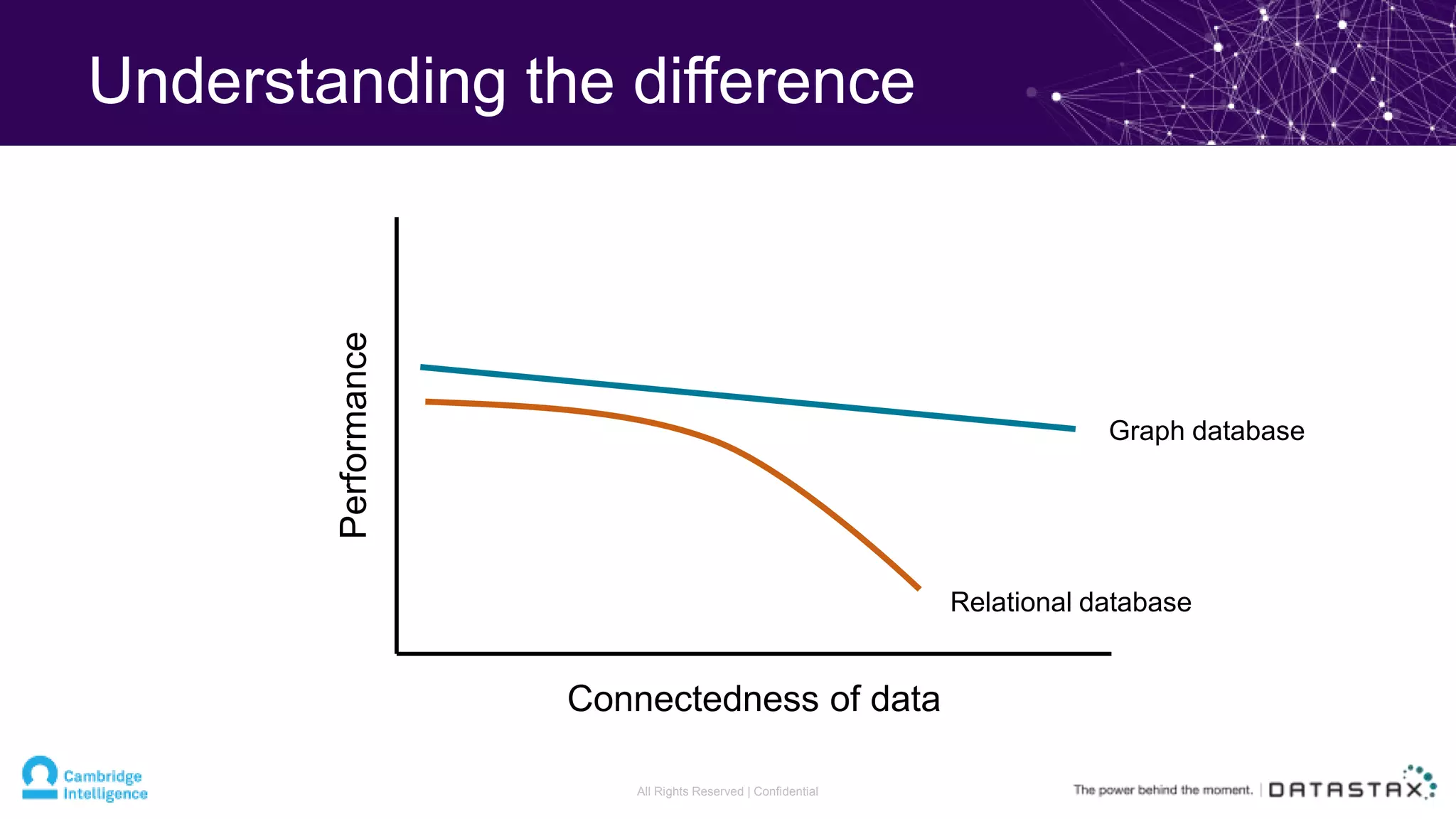
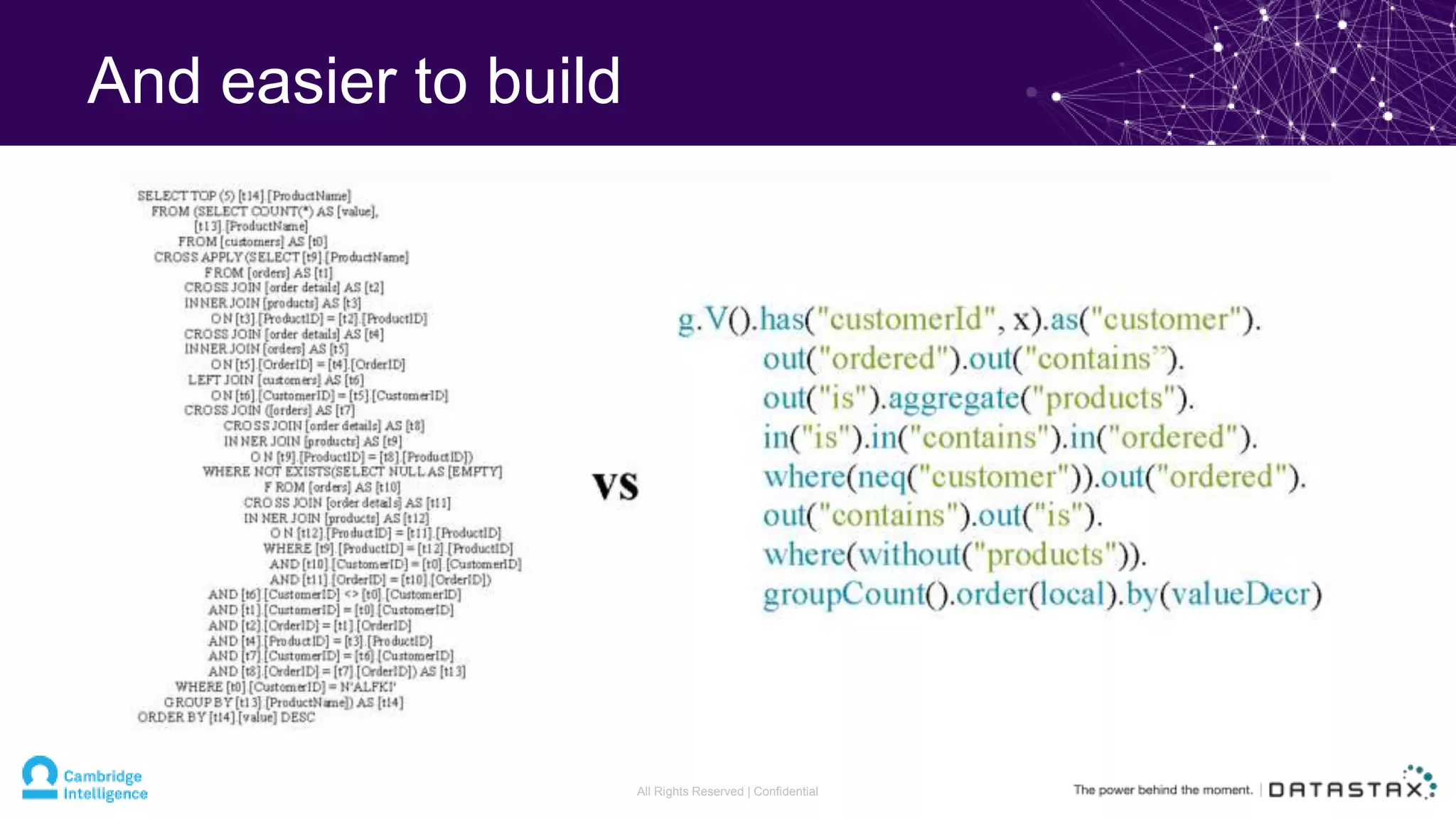
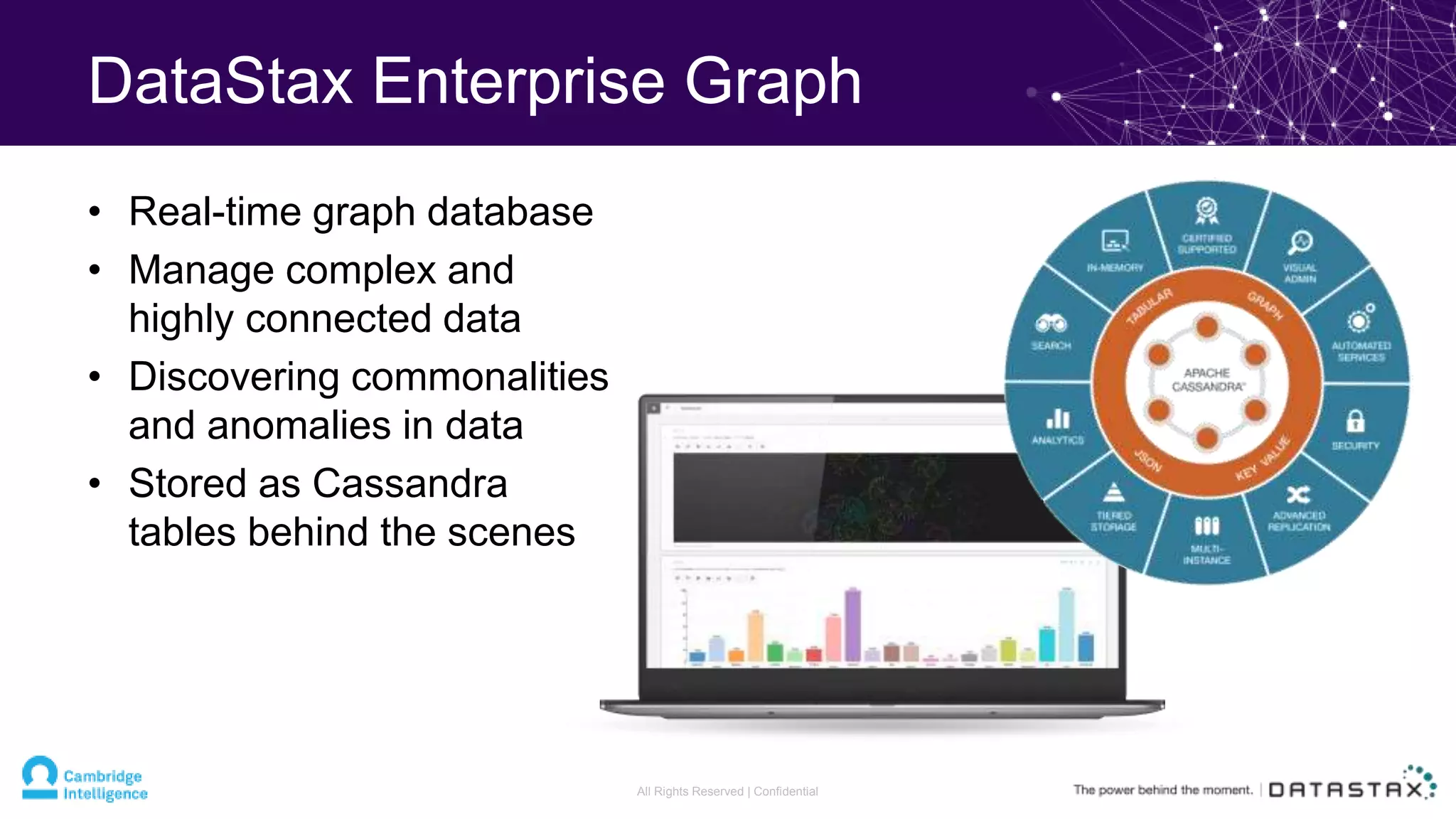
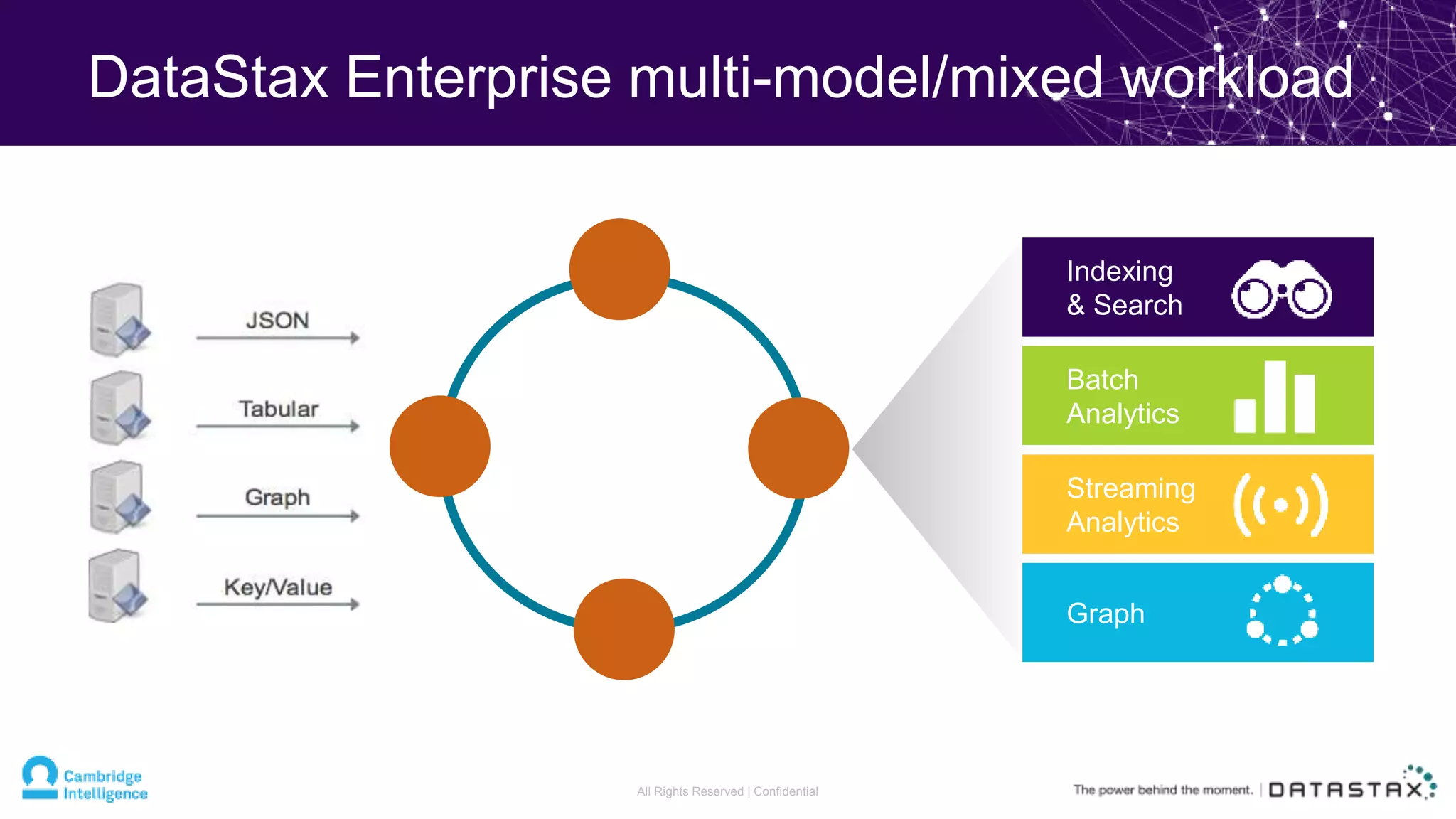
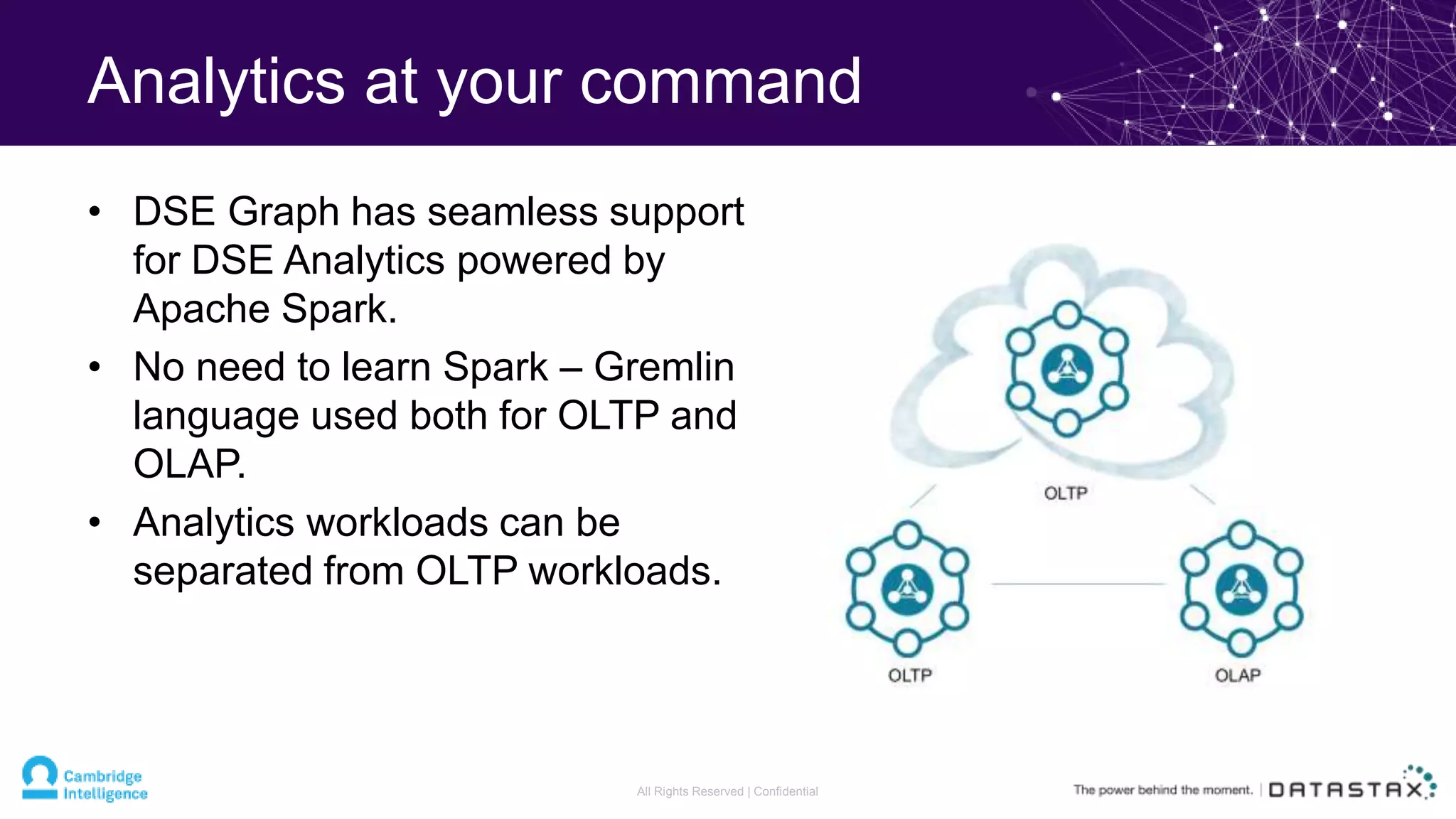
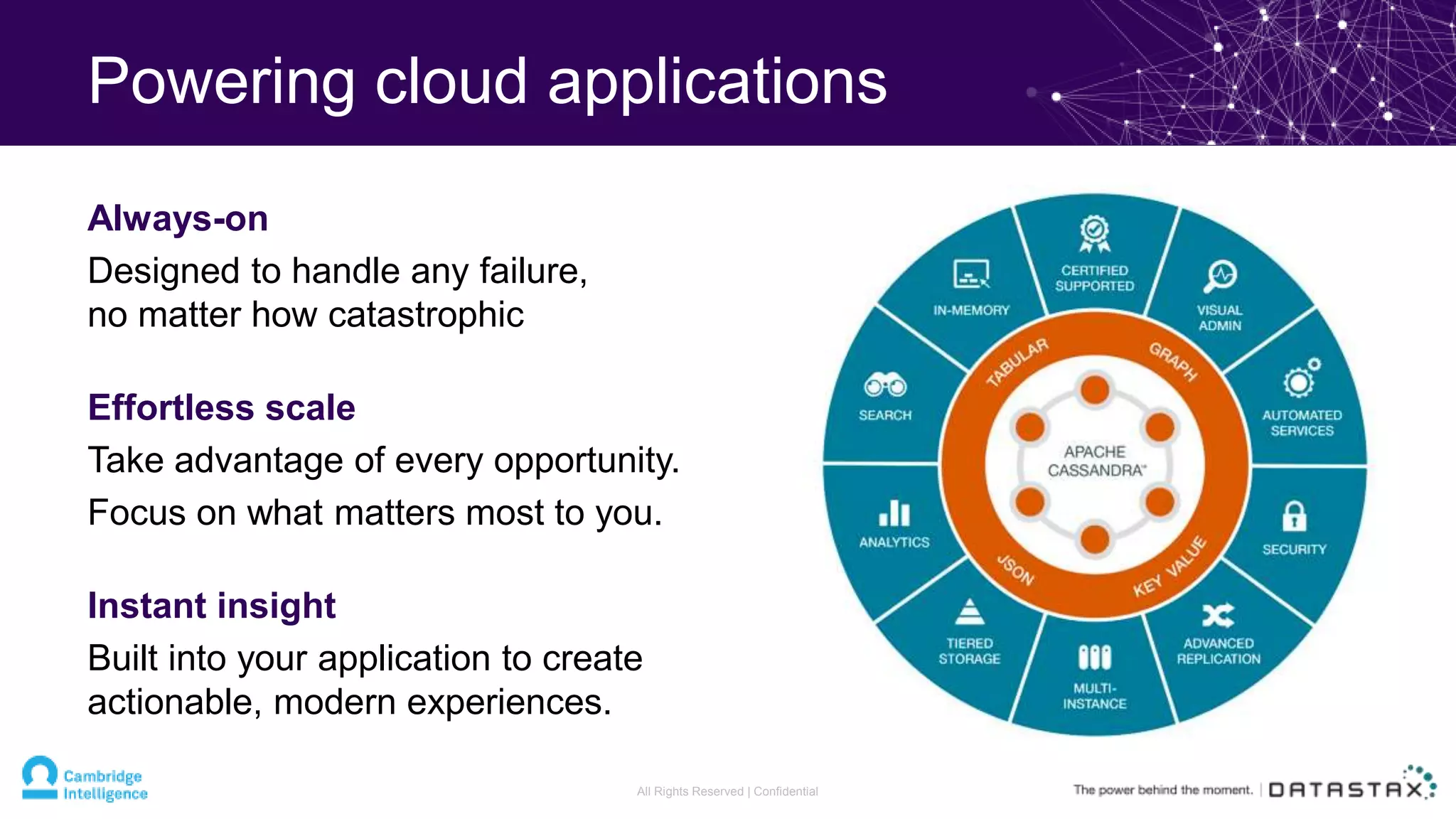
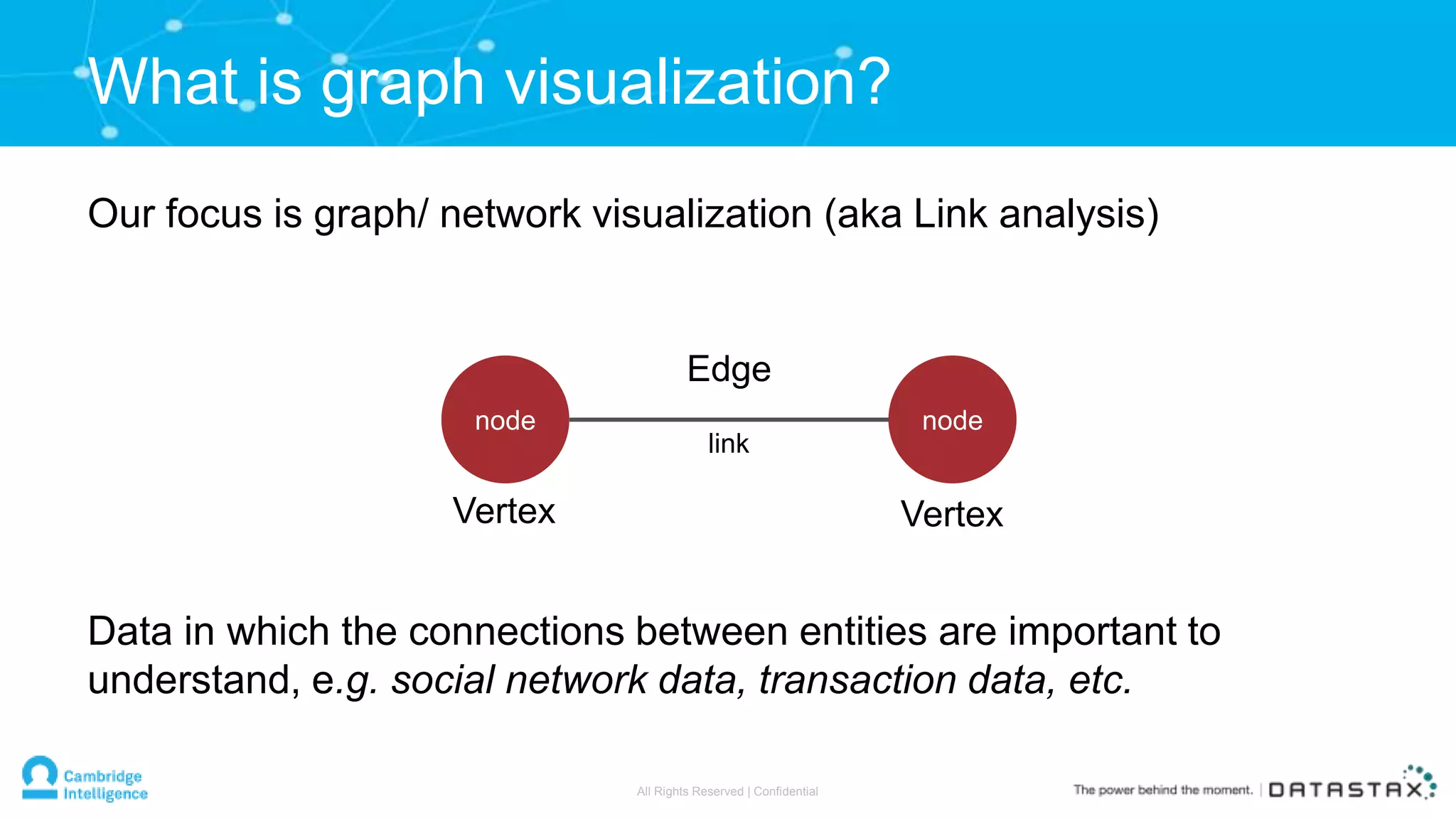
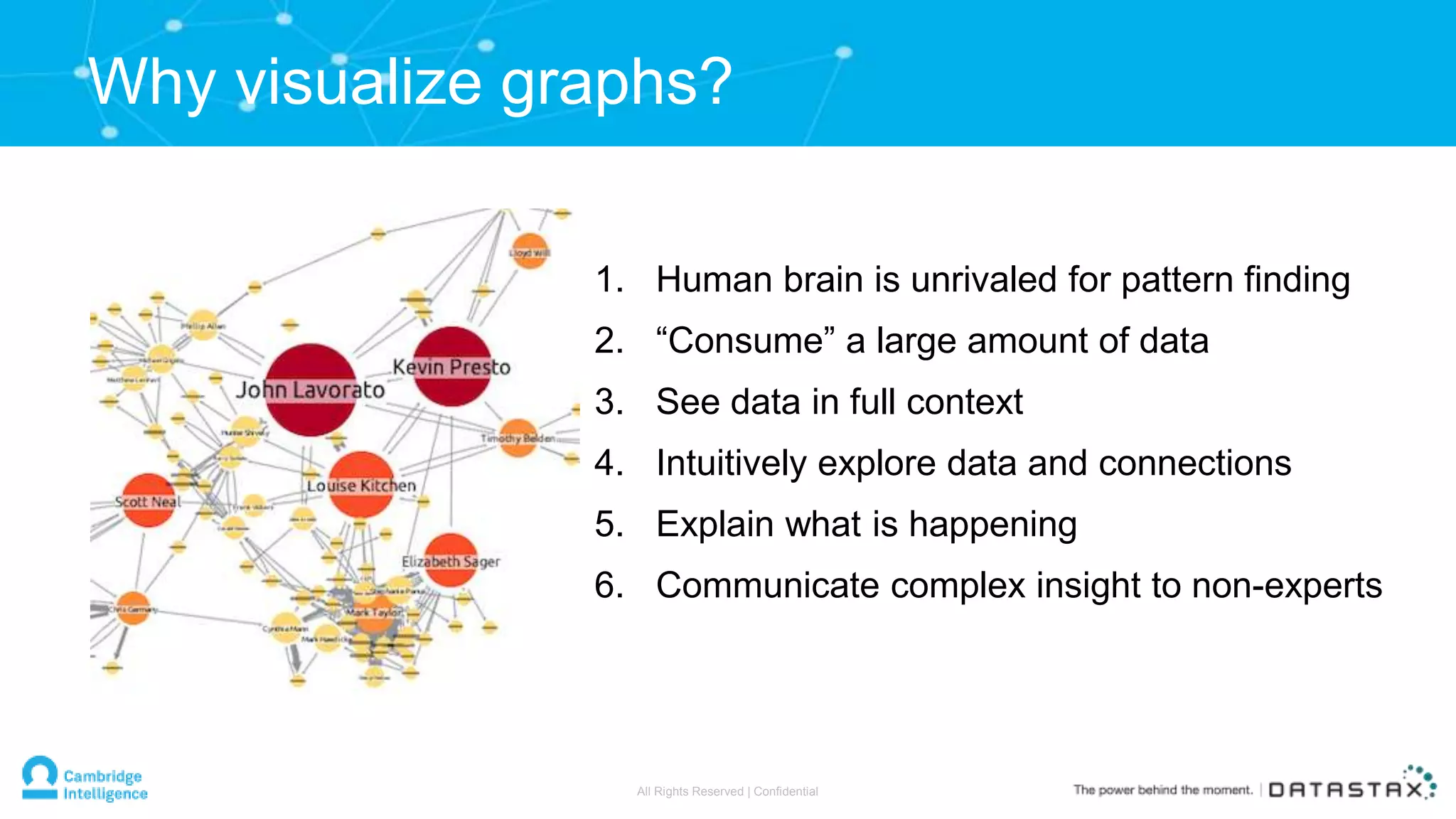
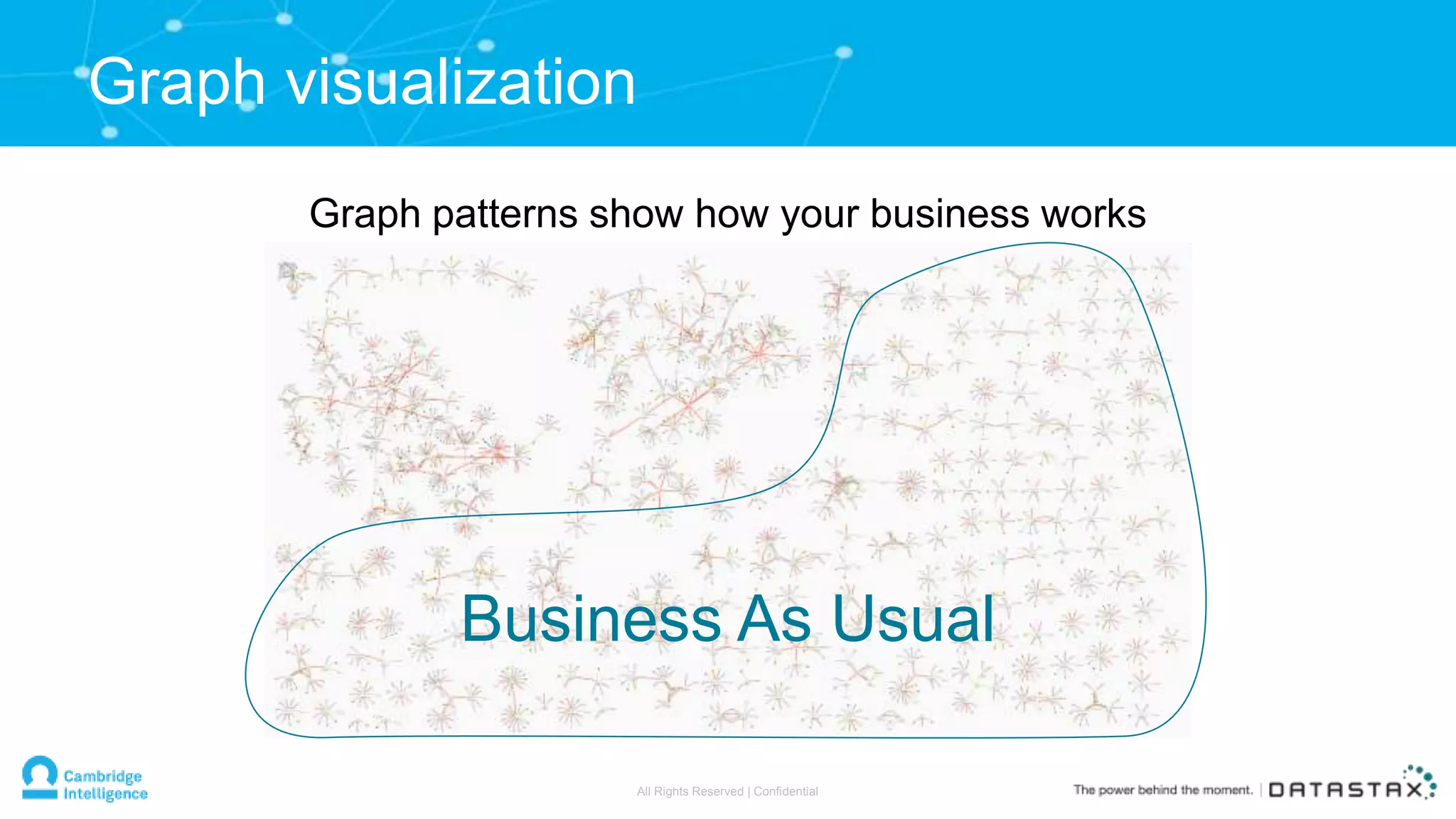
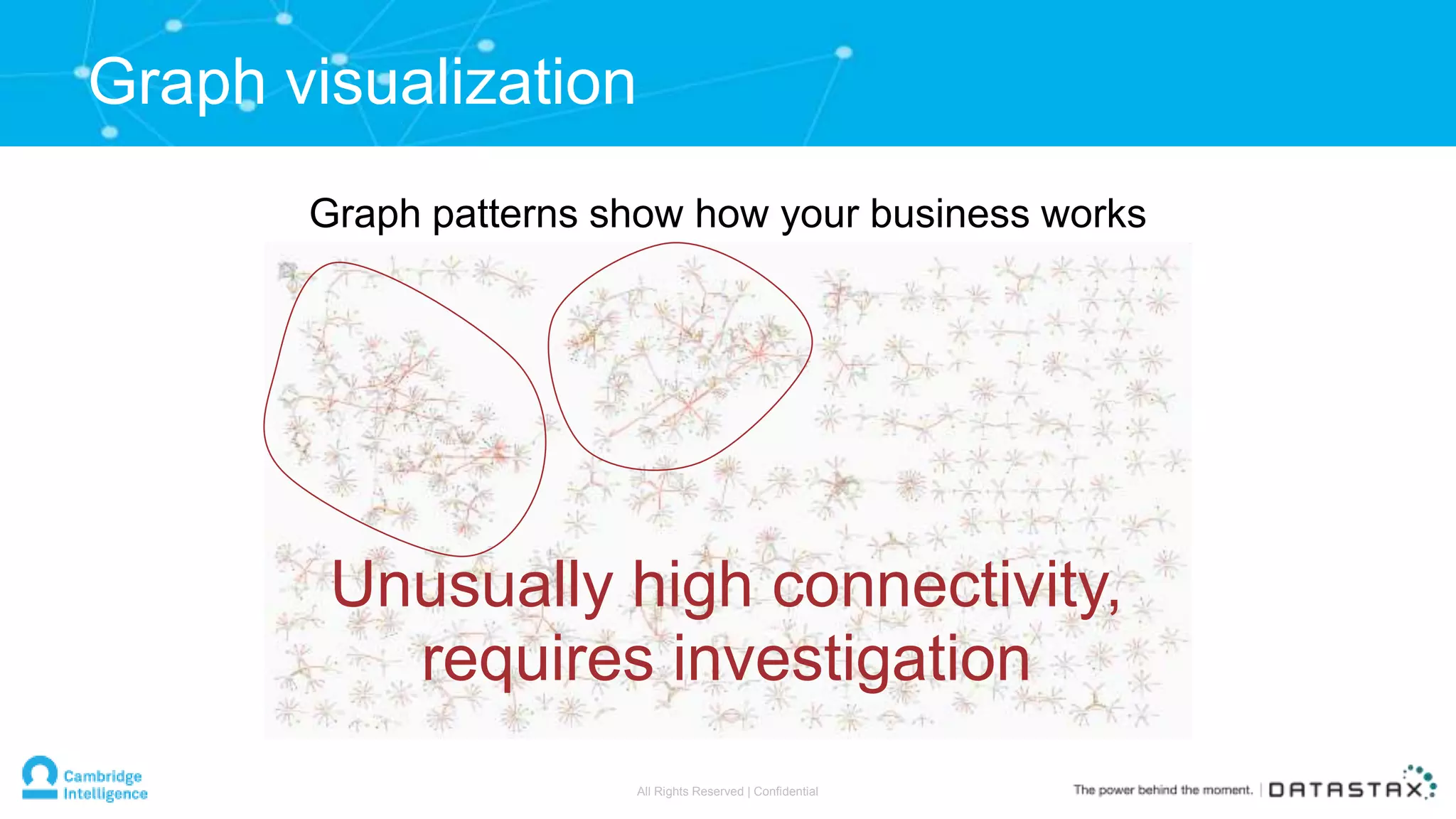
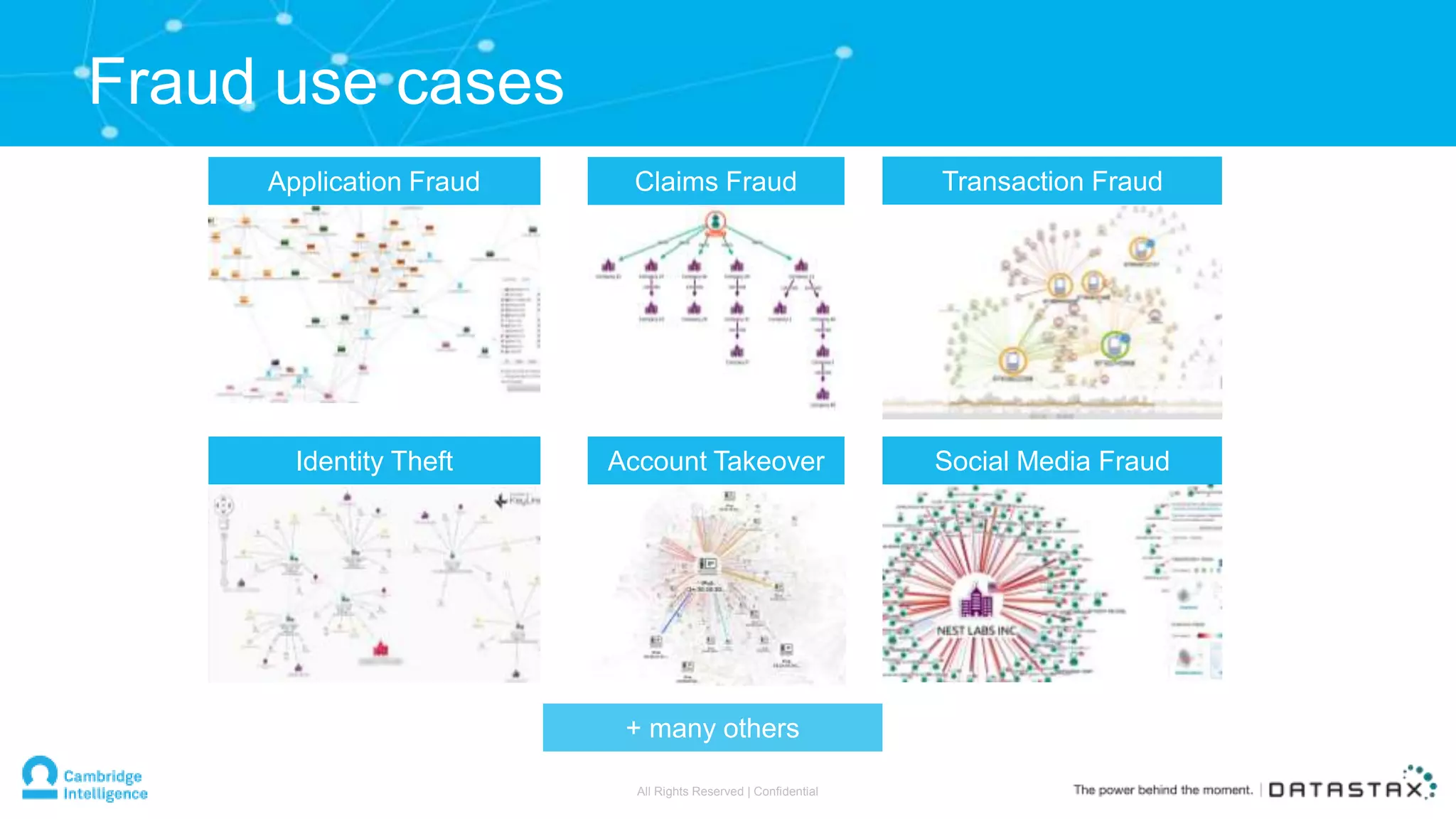
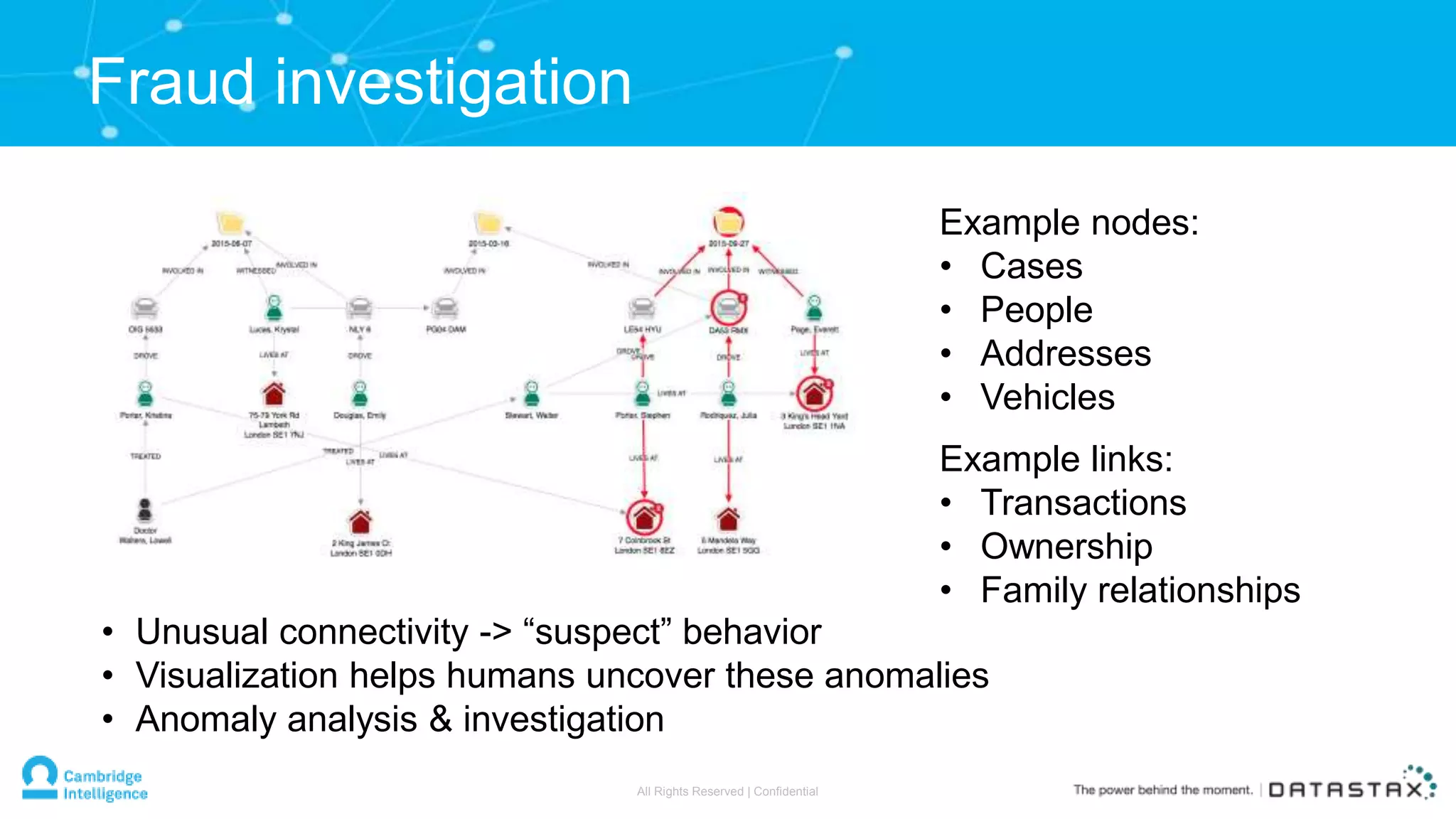
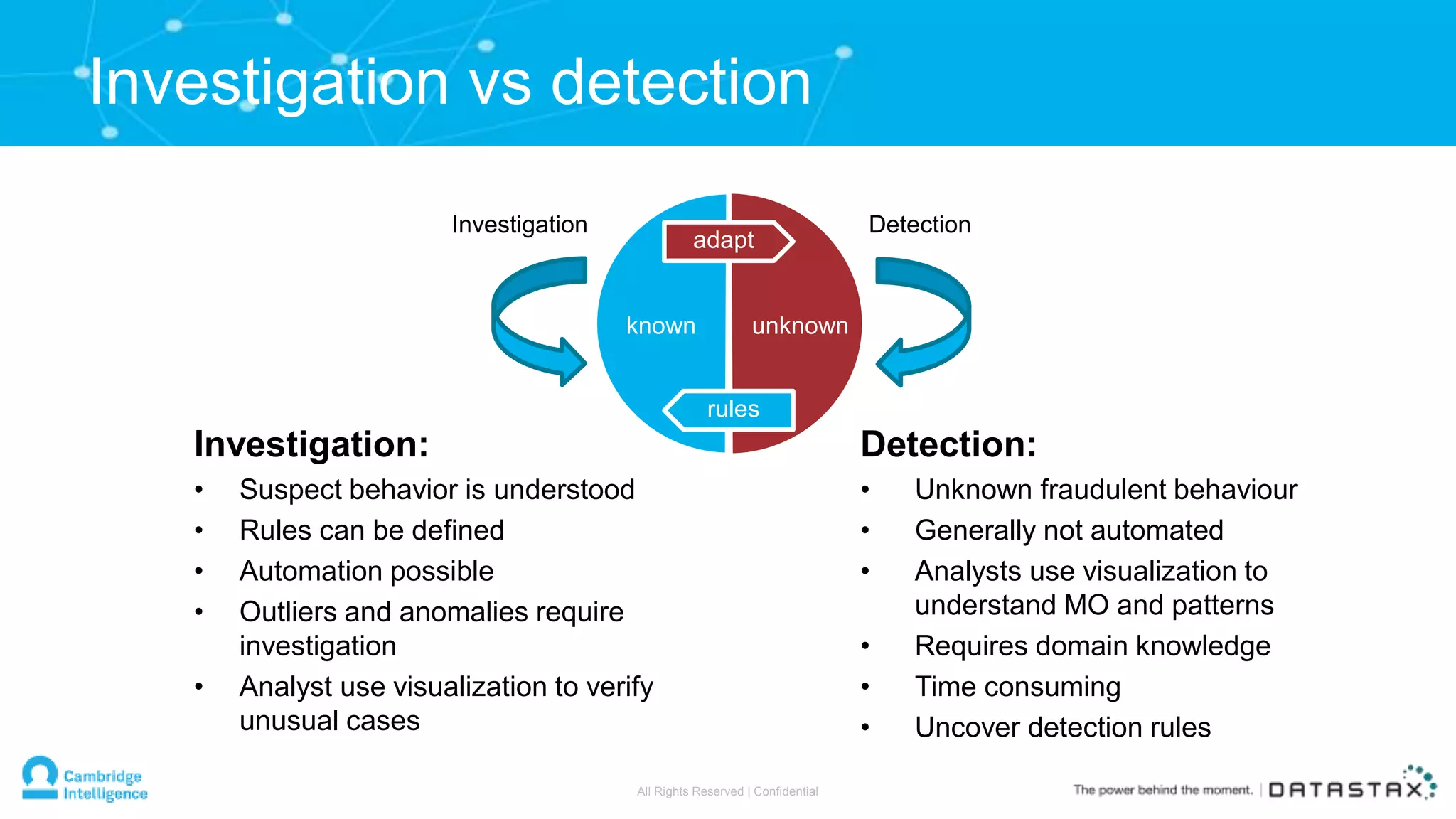
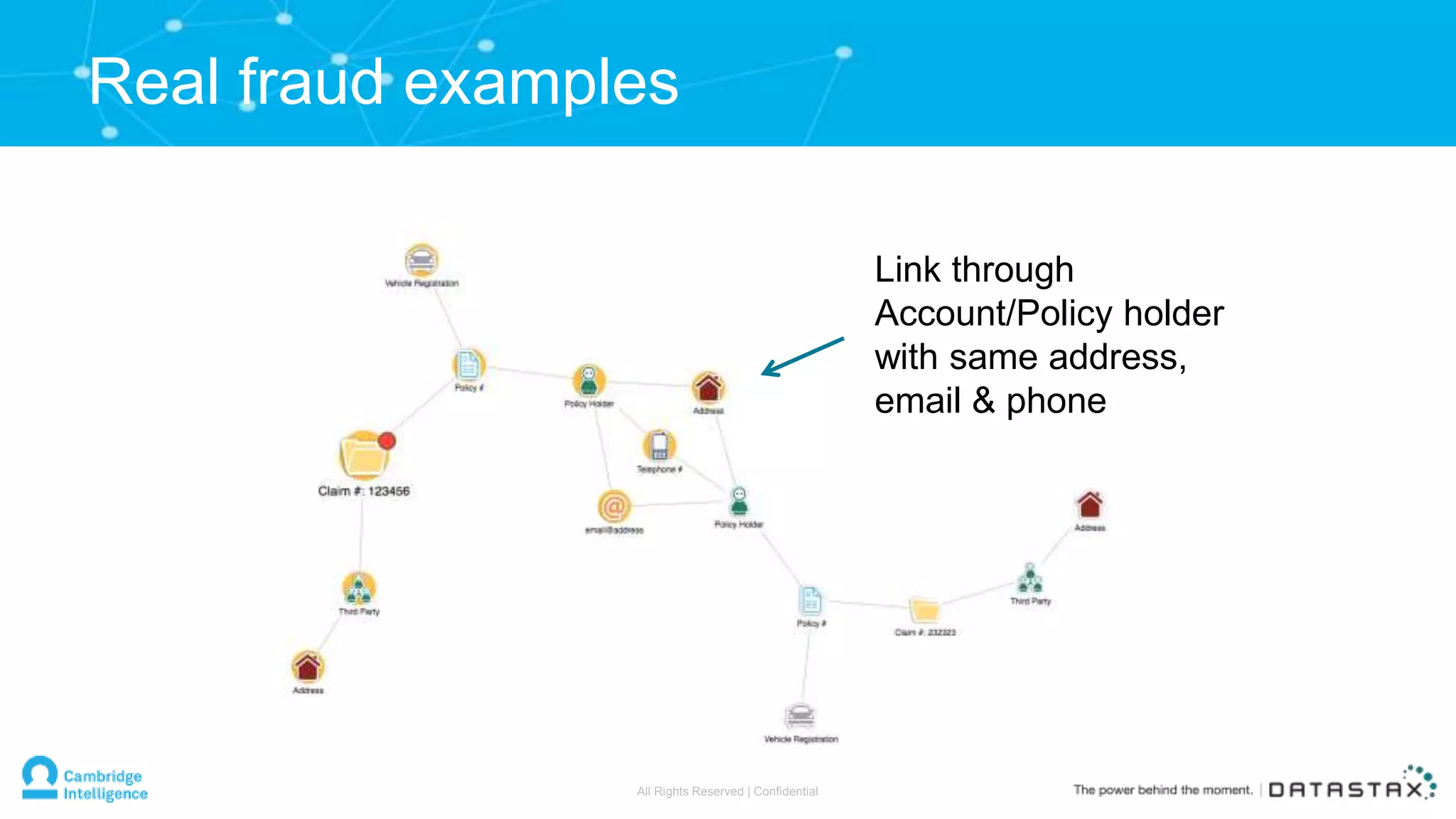
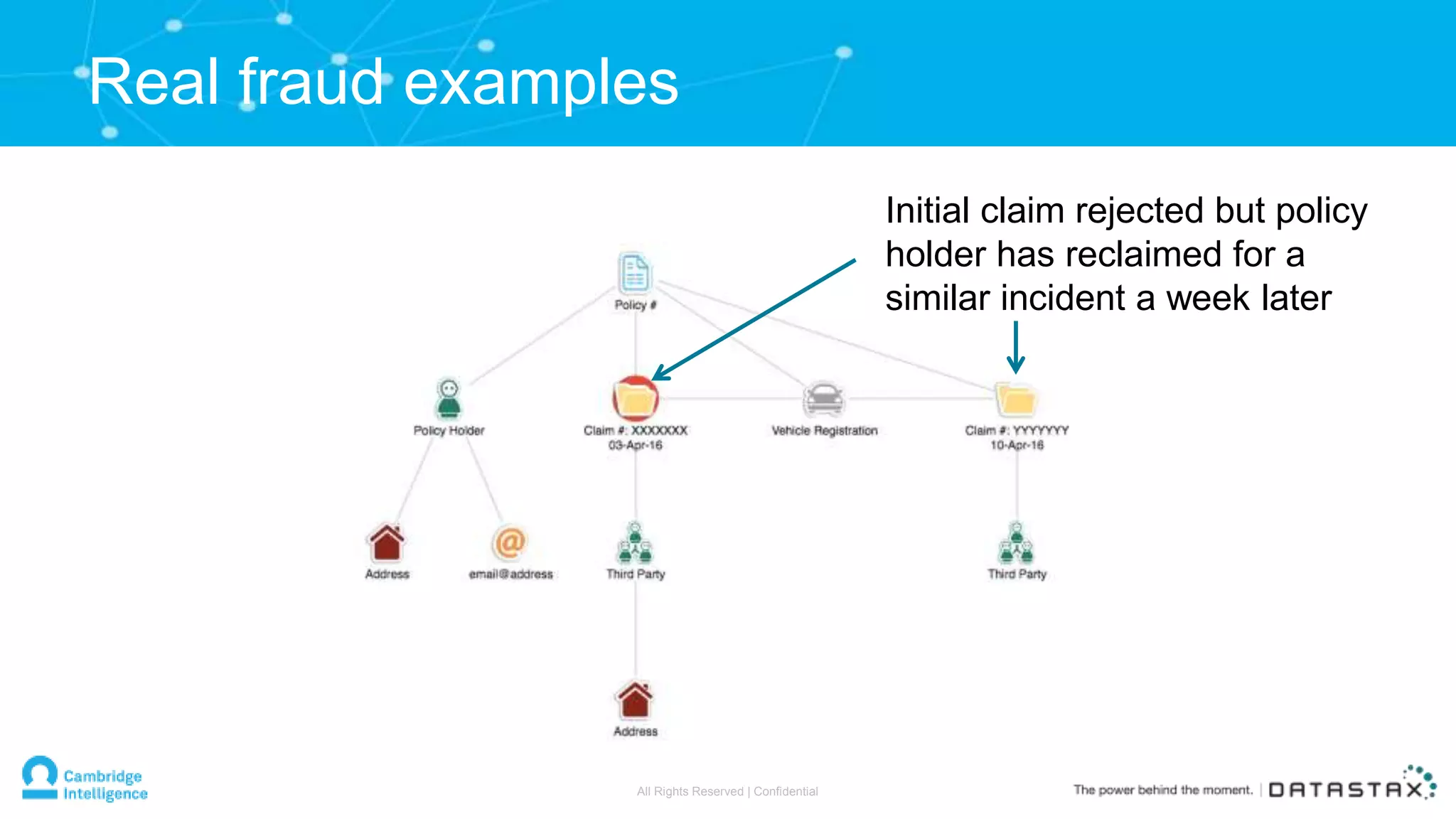
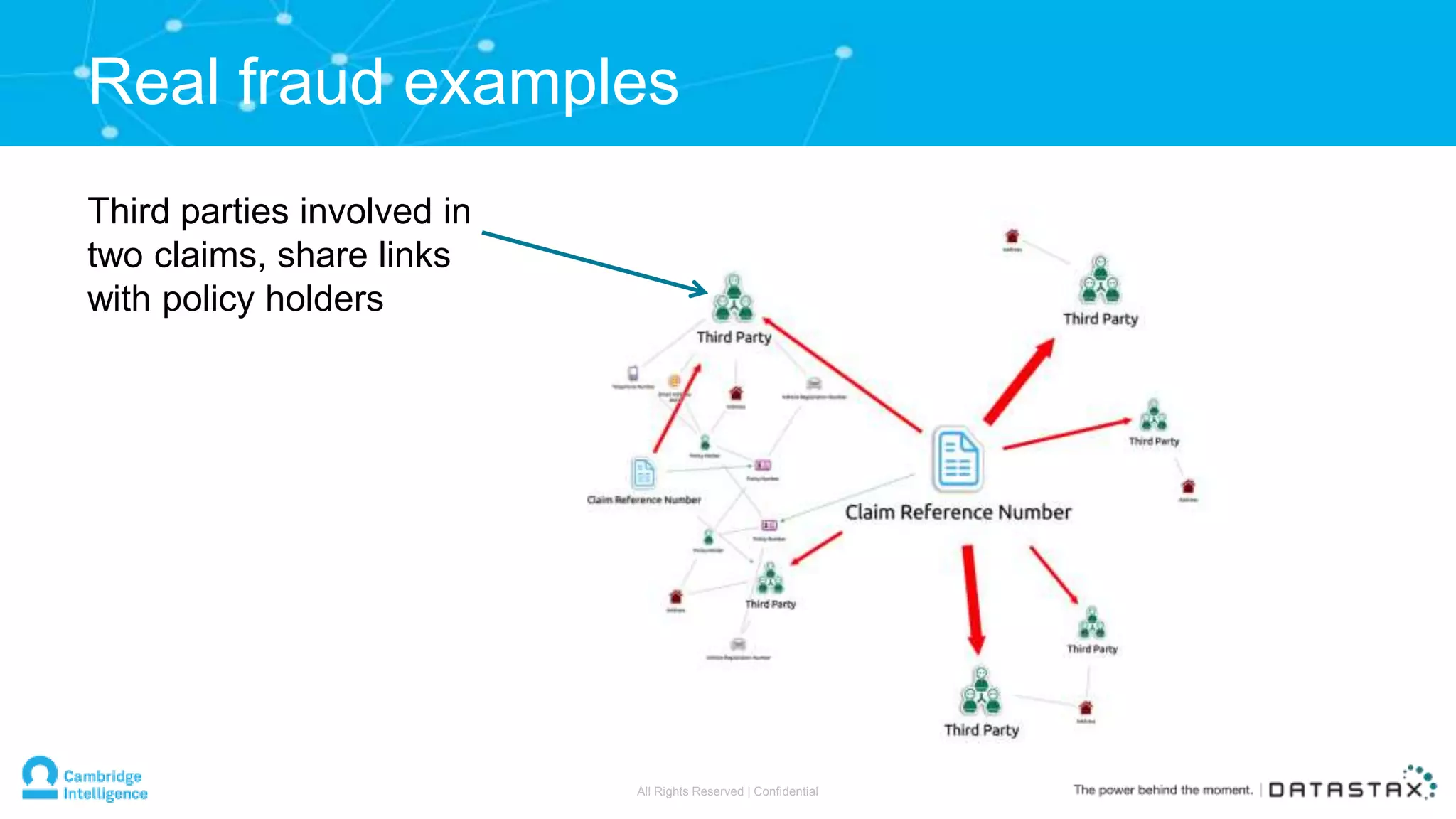
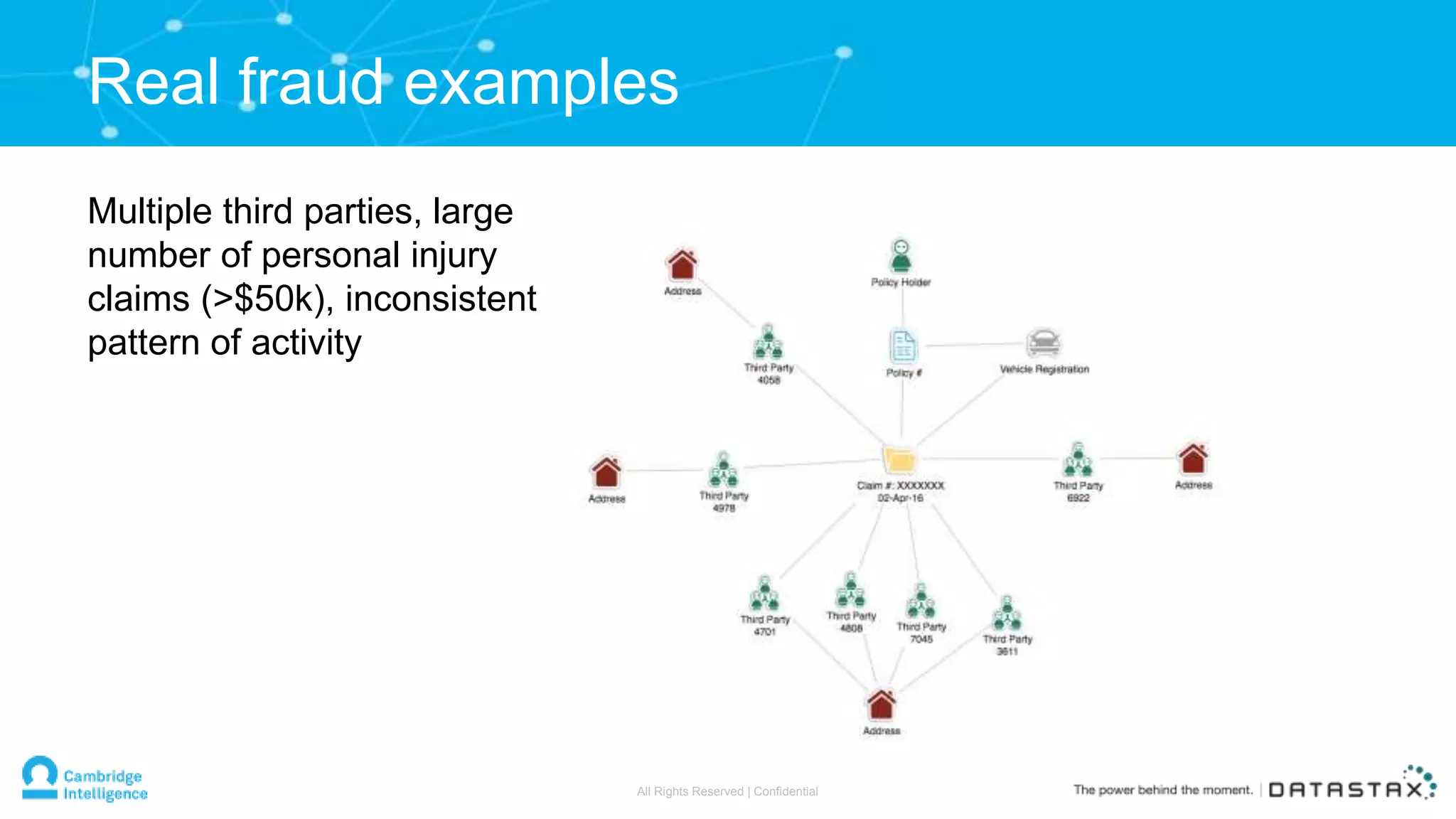
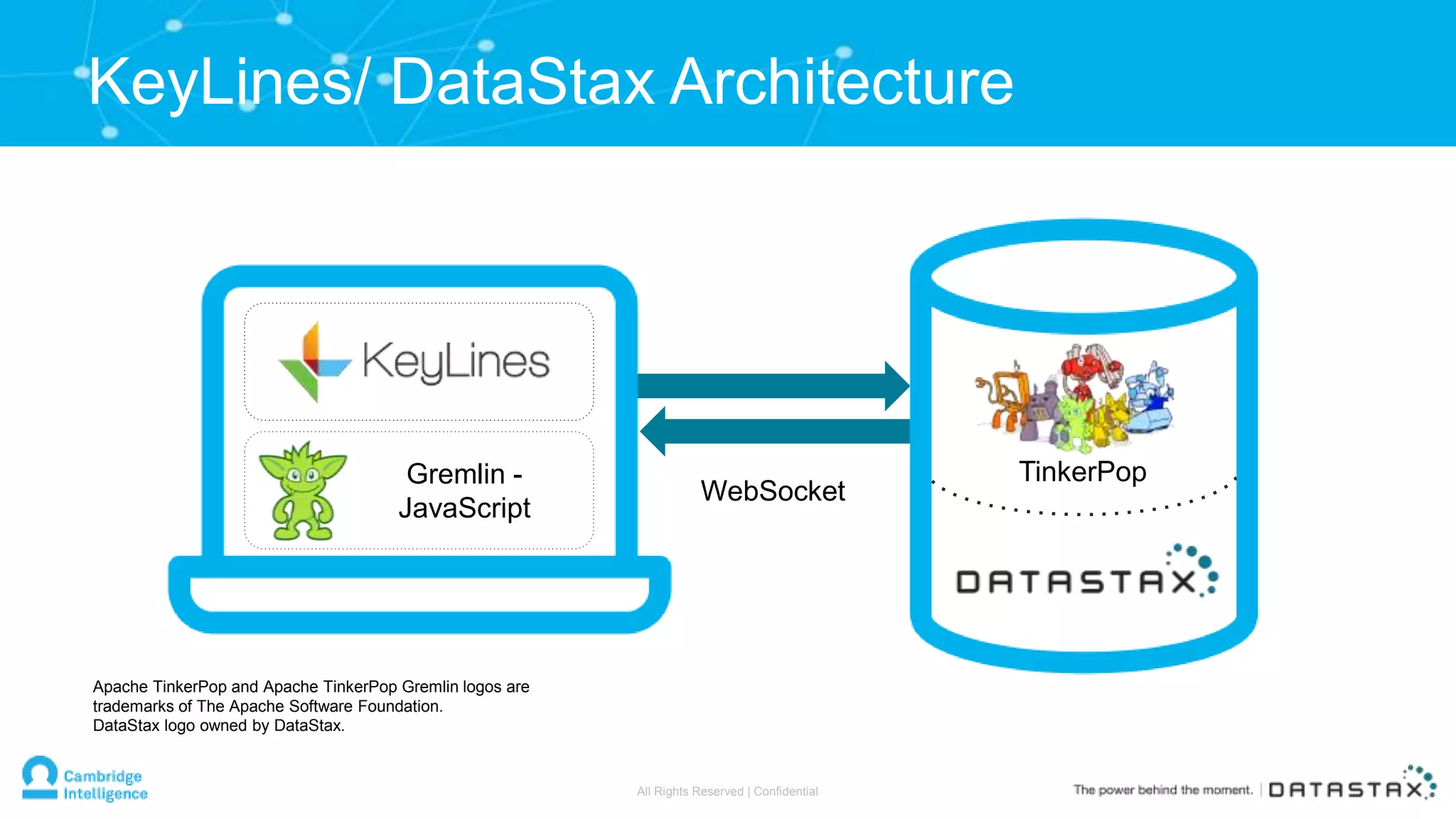
The document presents a webinar discussing the use of graph databases in fraud management, highlighting traditional fraud solutions' limitations and introducing a new, adaptable approach using data visualization. It emphasizes the importance of relationships within data to detect fraud and showcases the capabilities of DataStax and Keylines in creating effective fraud management solutions. The presentation also outlines real-world fraud examples and the necessity of interactive graph visualization for analysts in both detection and investigation.