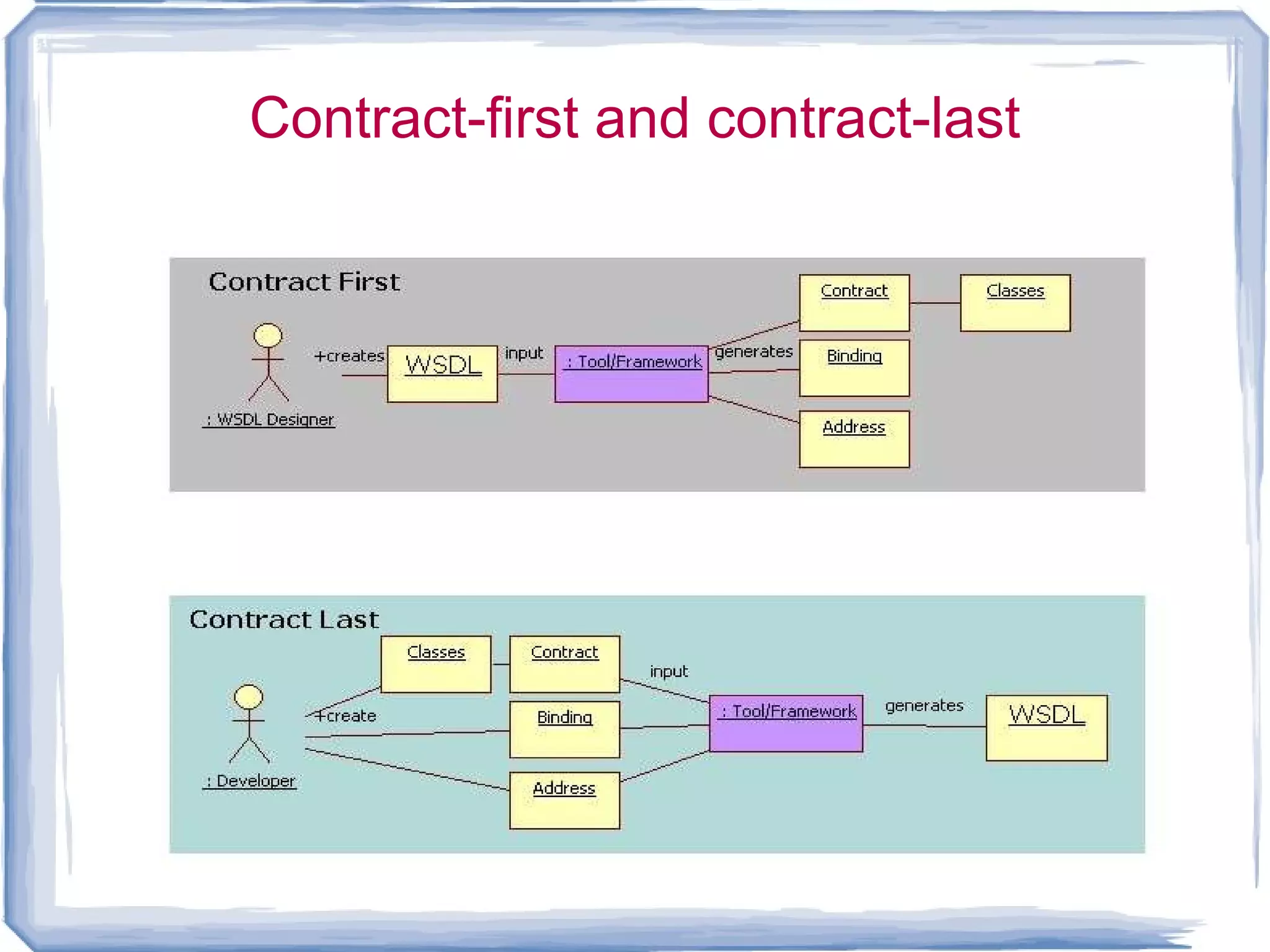
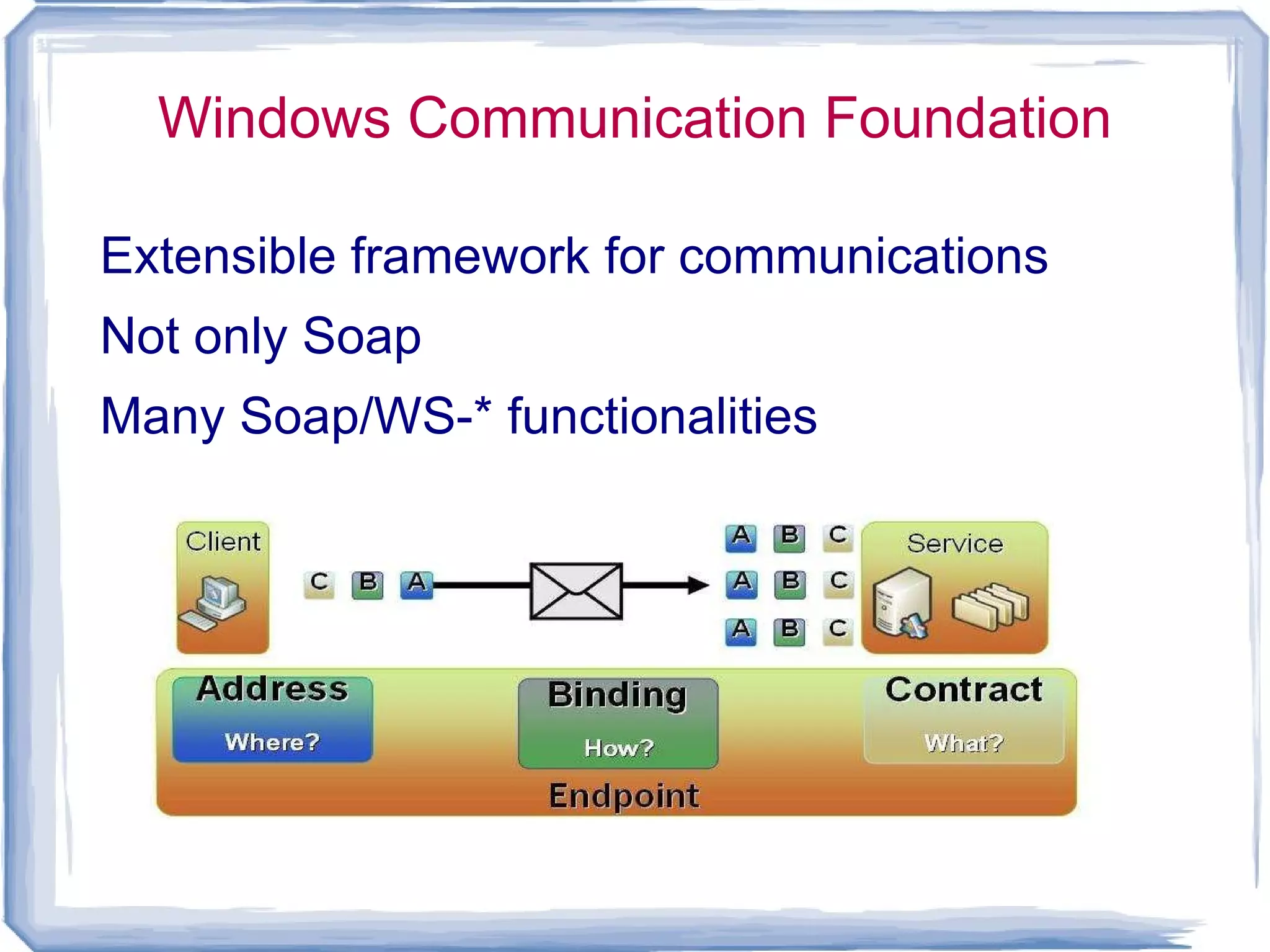
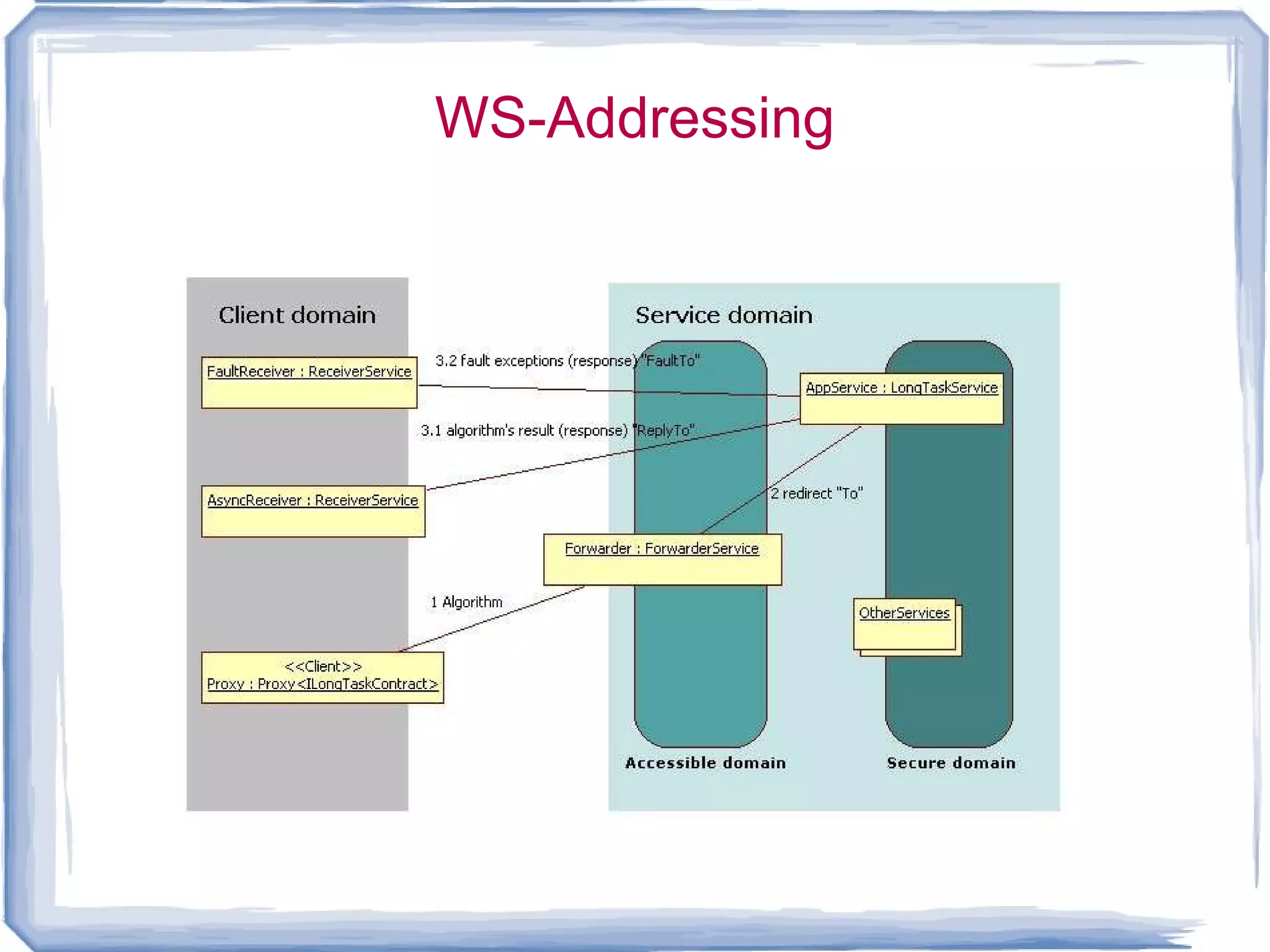
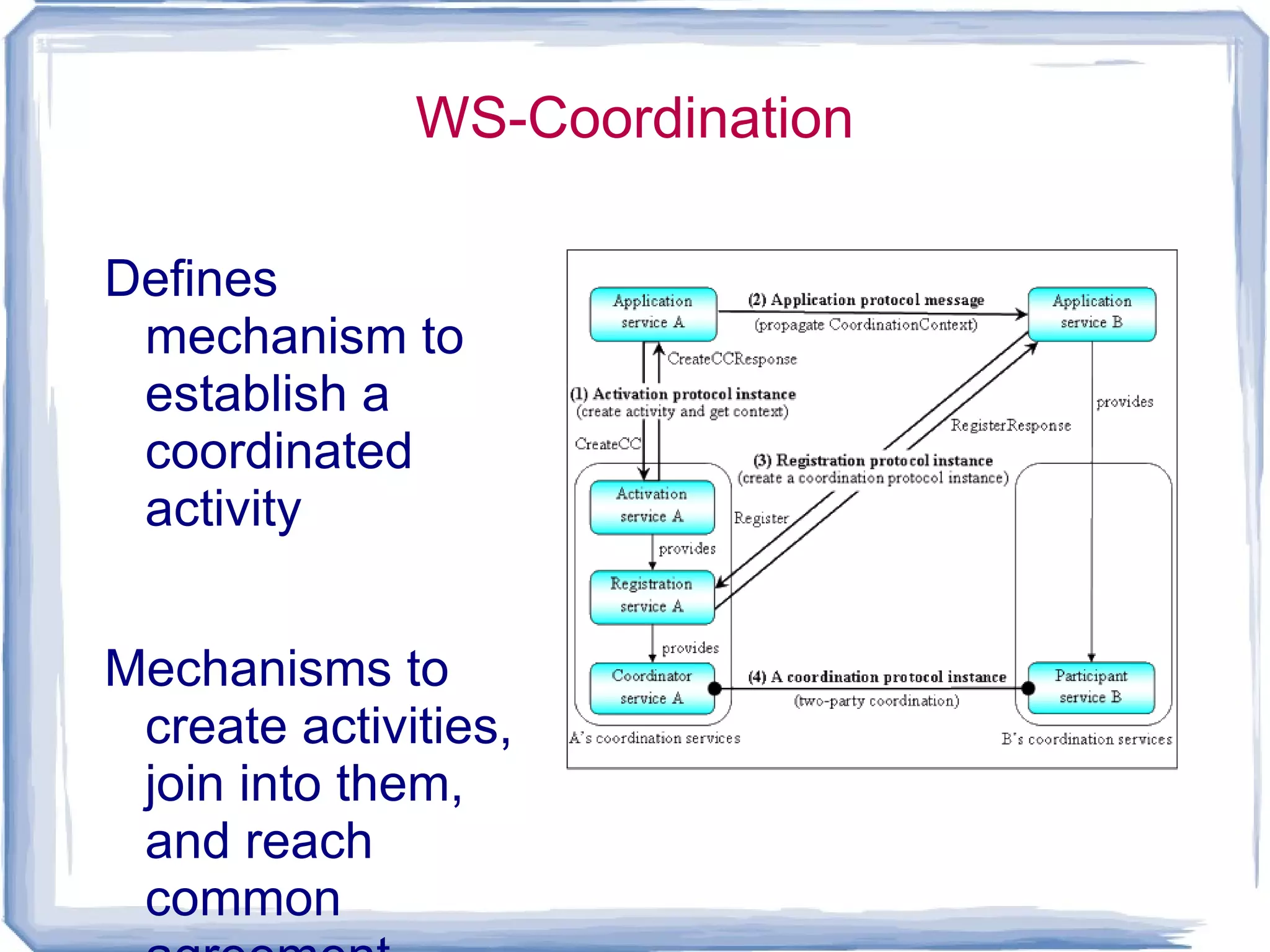
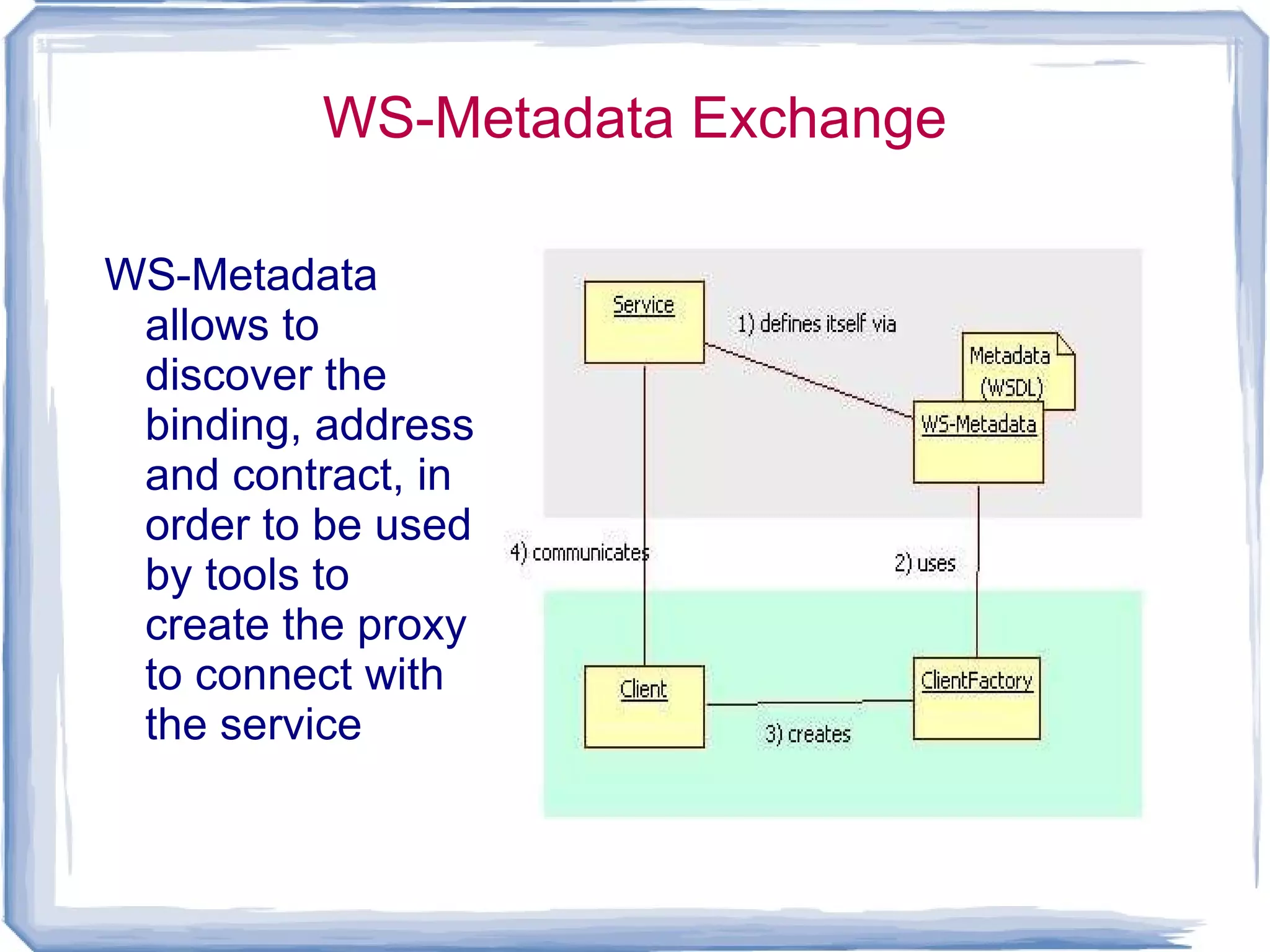
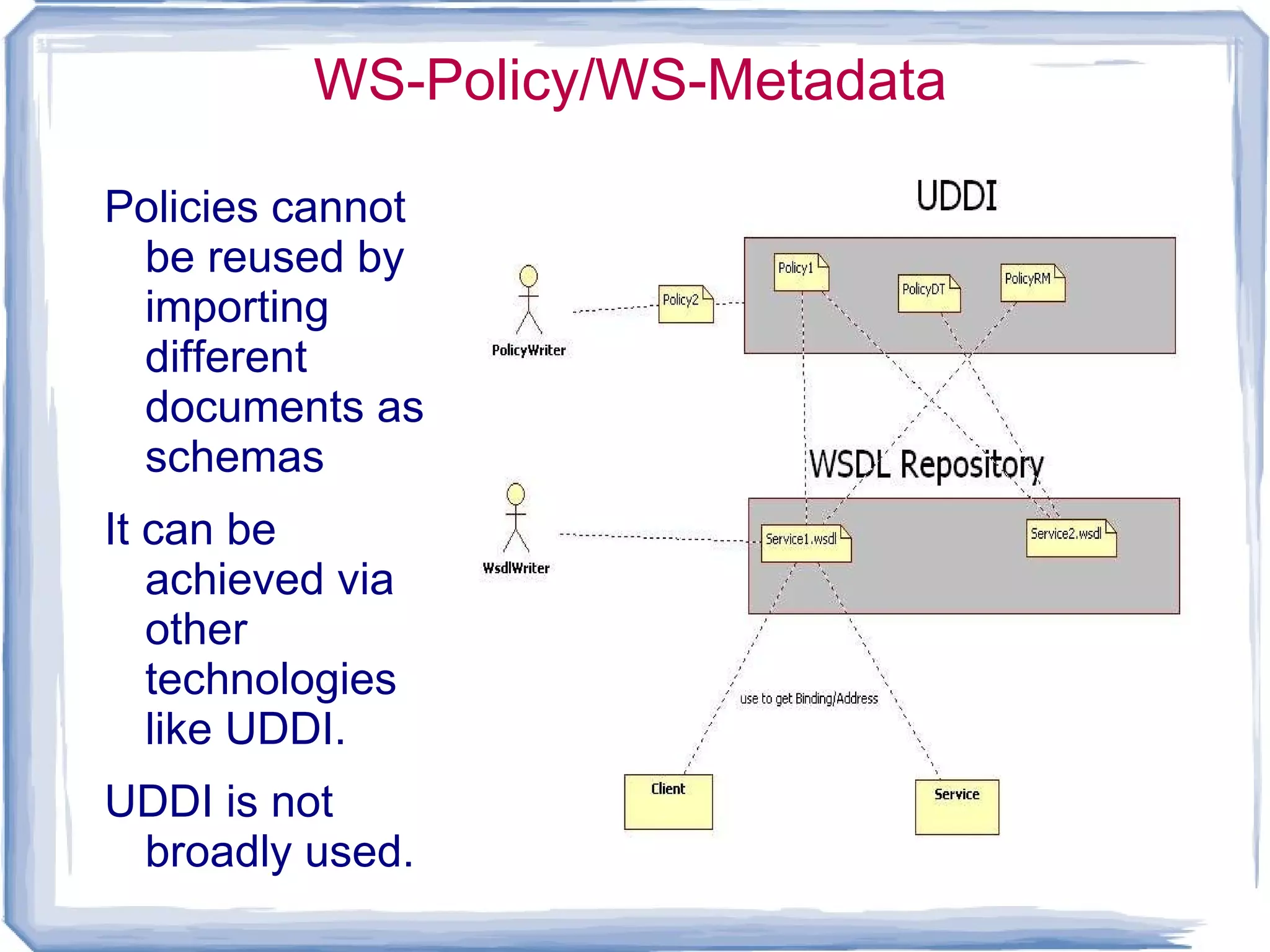
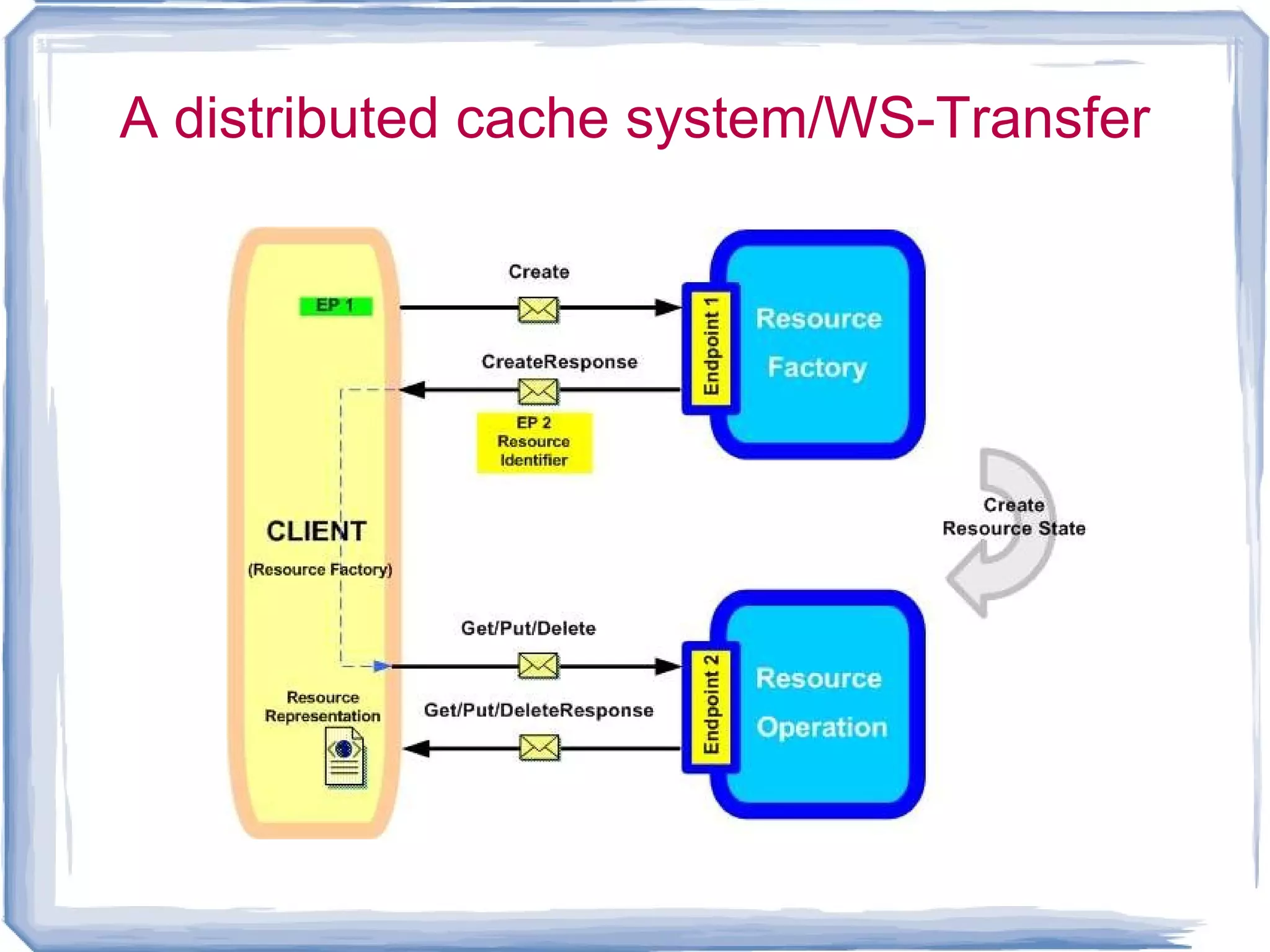
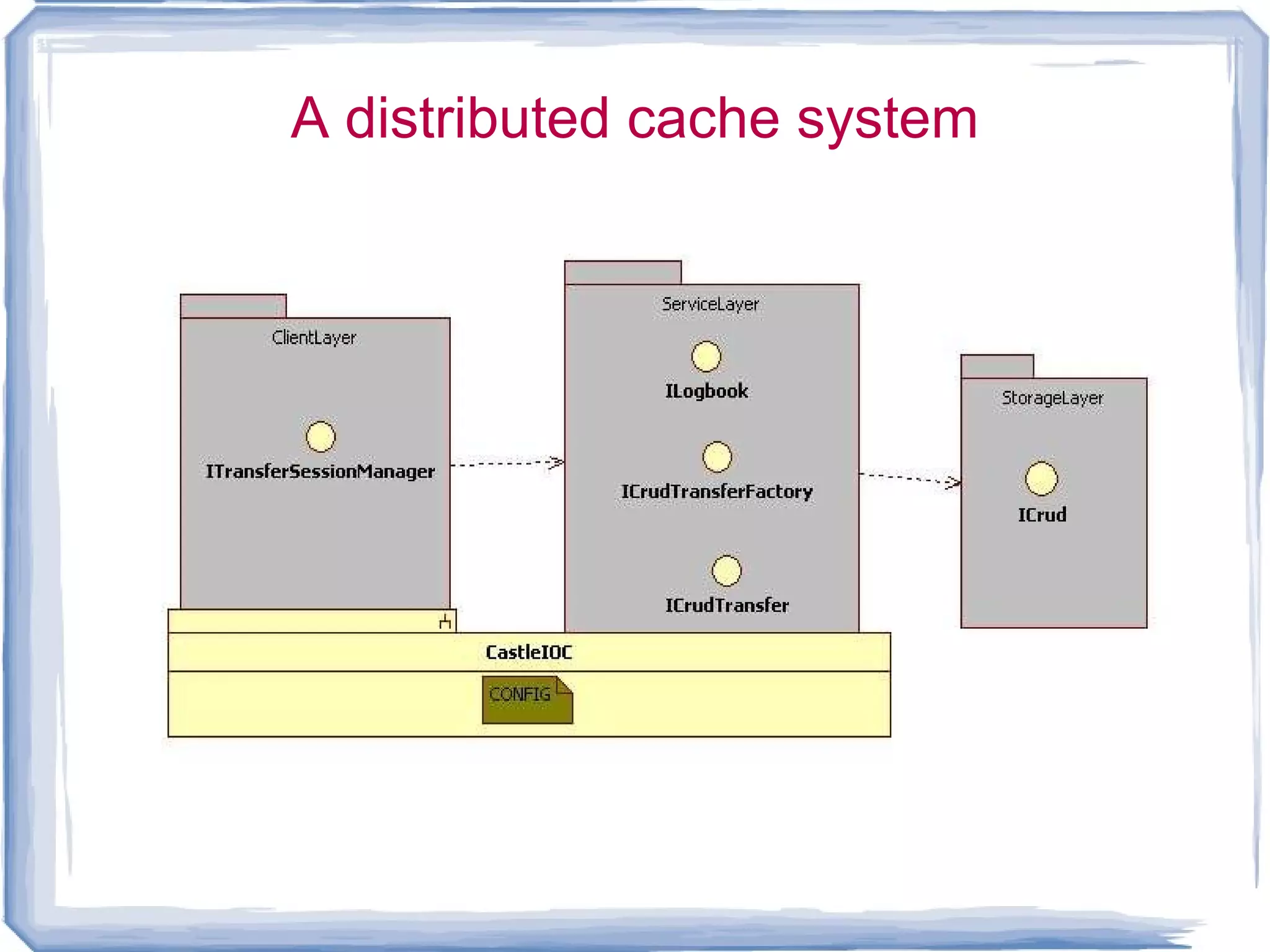
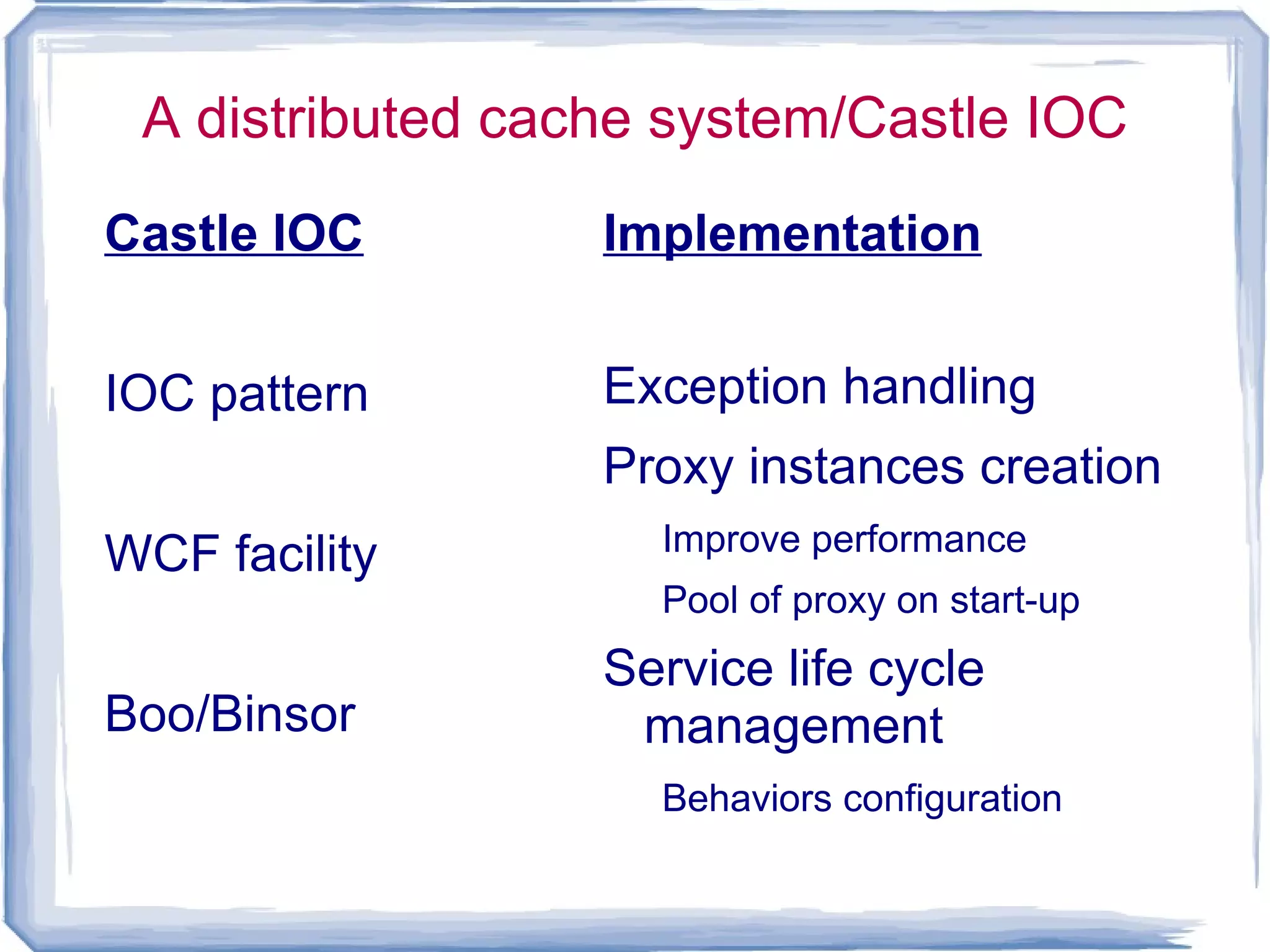
The document discusses web services and SOAP web services. It defines a web service as a service that is accessed over a network and is independent of communication protocols, data formats, and technologies. SOAP is introduced as a standard protocol for exchanging information between computer networks that is also independent of transport protocols, data formats, and standards. The document then summarizes several WS-* specifications and standards related to SOAP, including WS-Addressing, WS-Reliable Messaging, WS-Coordination, WS-Atomic Transaction, and WS-Business Activity. It also discusses WS-Policy and WS-Metadata Exchange. The document concludes with discussing a proof of concept distributed cache system that demonstrates scalability, performance, and