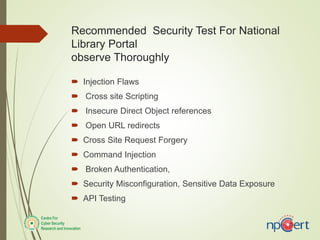
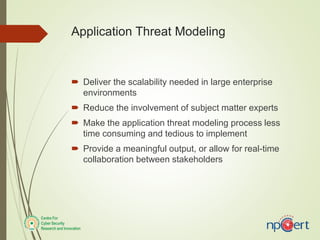
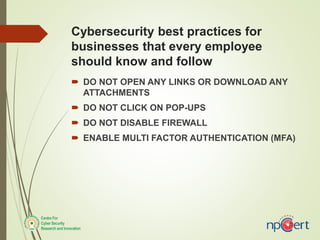
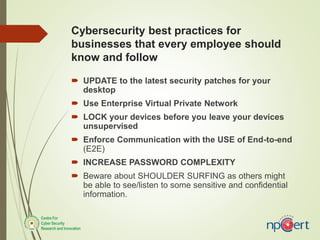
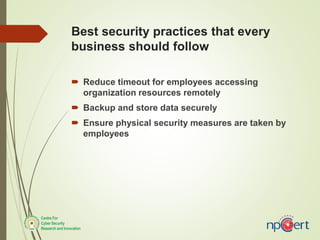
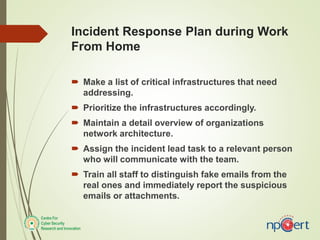
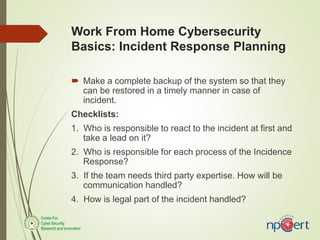
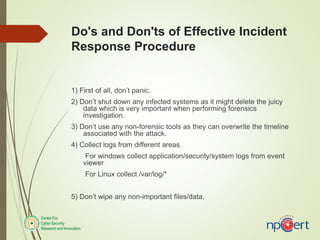
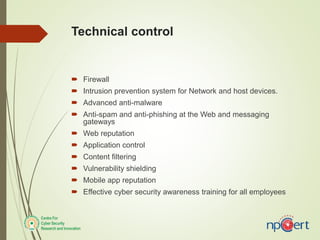
The document outlines the importance of threat modeling for applications in large enterprises, emphasizing scalability, reduced dependency on experts, and efficiency in the modeling process. It includes recommended cybersecurity practices and incident response strategies for businesses, highlighting the necessity of multi-factor authentication, user access monitoring, and employee training on recognizing phishing attempts. Additionally, it covers steps to take after a data breach and the importance of maintaining robust security measures.