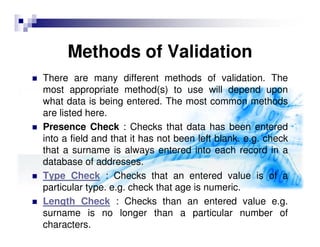
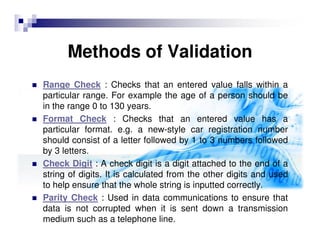
This document discusses validation and verification techniques used to ensure accurate data entry into computer systems. Verification checks that data is correctly transferred from its original source, often by having users confirm entered data on screen or entering it twice. Validation uses automatic checks by computers to ensure data makes sense, for example checking for presence, type, length, or value ranges. Common validation methods include presence, type, length, range, format and check digit checks. Validation helps ensure accurate data but does not check correct entry like verification.