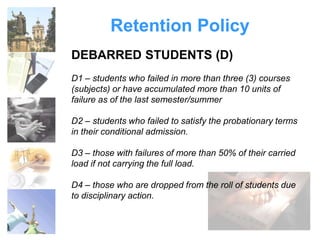
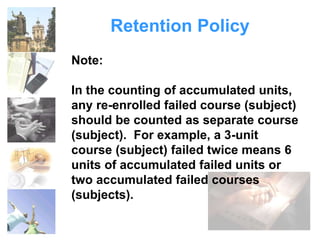
This document provides information about the Freshmen Orientation for the Institute of Information and Computing Sciences (IICS) at the University of Santo Tomas (UST). It details the history and establishment of IICS and its departments of Computer Science, Information Technology, and Information Systems. It also outlines the mission, vision, and administration of IICS, as well as introducing the profiles and policies regarding students, including the retention policy and code of conduct.