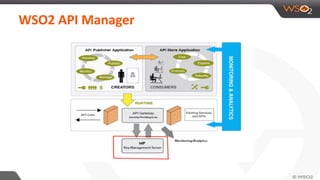
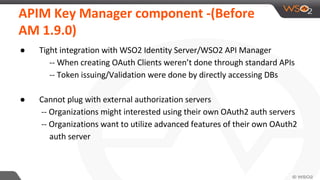
WSO2 API Manager is an open-source solution for creating, publishing, and managing APIs throughout their lifecycle. It includes functionalities for API versioning, monitoring, governance, security, and community engagement. The document outlines key management and OAuth application management features, along with implementation details and various resource endpoints.














![Create OAuth client at key manager
curl -k -X POST -b cookies https://localhost:9443/store/site/blocks/subscription/subscription-
add/ajax/subscription-add.jag -d
'action=generateApplicationKey&application=NewApp1&keytype=PRODUCTION&authorizedDo
mains=ALL&callbackUrl=&validityTime=3600&tokenScope=&jsonParams={"paramname":"
paramvalue"}'
Sample jsonParams for MITred-Connect implementation
{"allowDomains":"ALL","callback_url":["dfsds"],"client_name":"jh_sandbox","contact":[],"
grant_types":[],"response_types":[],"scope":["phone","openid","offline_access","address","
email","profile"],"token_endpoint_auth_method":null}
https://docs.wso2.com/display/AM190/Store+APIs](https://image.slidesharecdn.com/wso2apimanagerintegrationwiththirdpartykeymanager-150821062301-lva1-app6892/85/Using-a-Third-Party-Key-Management-System-with-WSO2-API-Manager-22-320.jpg)
![Update OAuth client
curl -k -X POST -b cookies https://localhost:9443/store/site/blocks/subscription/subscription-
add/ajax/subscription-add.jag -d
'action=updateClientApplication&application=NewApp1&keytype=PRODUCTION&authorizedDo
mains=ALL&callbackUrl=&validityTime=3600&tokenScope=&jsonParams={"paramname":"
paramvalue"}'
Sample jsonParams for MITred-Connect implementation
{"allowDomains":"ALL","callback_url":["dfsds"],"client_name":"jh_sandbox","contact":[],"
grant_types":[],"response_types":[],"scope":["phone","openid","offline_access","address","
email","profile"],"token_endpoint_auth_method":null}](https://image.slidesharecdn.com/wso2apimanagerintegrationwiththirdpartykeymanager-150821062301-lva1-app6892/85/Using-a-Third-Party-Key-Management-System-with-WSO2-API-Manager-23-320.jpg)




