Use of administrative privilege levels in netapp cluster 8.x
•Download as DOCX, PDF•
0 likes•262 views
Here it has been described how to user the administrative privileges in command mode in Netapp cluster mode 8.x
Report
Share
Report
Share
Recommended
Piezo Power Business Plan

Piezo Power is developing Electroturf, a piezoelectric subflooring product that generates electricity from mechanical pressure like walking. It is led by CEO Daniel Walsh, CMO Cesia Gomez, CTO Jessemar Servida, and CFO Enrique Vazquez. Piezo Power believes Electroturf can harness wasted kinetic energy on a large scale and help reduce carbon footprints.
Fmea Innovator - Step by Step

Science has proven that the human mind recalls information best when the information is in a graphical format.
http://www.hoquality.com/software/fmea-innovator.php
Thougnts on the Future of Software Development

The document discusses different levels of automation for vehicles, from no automation where the driver performs all tasks to full automation where the system controls the vehicle under all conditions. It also examines how this classification framework could apply to AI-driven software development and how tools like low-code and AI coders could impact team structures and the role of software developers. The framework aims to effectively manage complexity and translate real-world problems into digital models.
1RUNNING HEAD MANAGING HOST BASED SECURITY IN WINDOWS 8.1La.docx

1RUNNING HEAD: MANAGING HOST BASED SECURITY IN WINDOWS 8.1
Lab Deliverable for Lab 2
a. Procedure to Manage Windows Defender
Operating Environment:
1. Operating System: Windows 8.1 Pro
2. Hardware: A Laptop
3. Software: VMware Horizon Client Installed
Description:
This window configuration project will require the sytem admin permission so as to access the programs and get to know how it is commanded to the action it should peform. Also, to use a virtual box one should have knowledge in how to operate the virtual box and explore the virtual programs
Notes, Warnings and Restrictions:
1. Windows Defender come with windows 8.1 software and are found in the control panel.
2. The application is used only when you login your system as an administarator or have permitted to act as the administrator.
3. For windows defender to run in the system it should be turned on and no other antivirus should be active
4. Scanning the system with windows defender deletes infected files. Also ensure you do the required scanning
5. If a different anti virus has been previously deleted, then windows defender needs to be turned off and to be restarted
Resources (Futher Reading):
Firewalls. (n.d.). Retrieved from https://technet.microsoft.com/en-us/library/cc700820.aspx
Microsoft Baseline Security Analyzer. (2011). Retrieved from https://dougvitale.wordpress.com/2011/11/18/microsoft-baseline-security-analyzer/
CloudFlare. (n.d.). Retrieved from https://www.winhelp.us/configure-windows-defender-in-windows-8.html
Procedures:
Windows defender
Window defender protects a computer system against any form of malware by running in the background of the computer system and gives notification if any suspicious item is found in the syatem for the user to take action. It can also be used by a computer to scan the system if the system has issues e.g becomes slow, switches off when not commanded to, hanging among other things. Windows defender should be updated over time so that it is not outdated and also to improve its performance.
Windows defender is found in the control panel icon, steps of opening are
i. Open control panel and select “windows defender”
ii. While you click on windows defender, the following page appears
a) To update the system click on “update”
b) Real time scanning
c) For the full scan results it will appear in the table as shown below
d) For quick results check the button just before you click on scan. Then the results will appear as shown below.
e) To scan removable device, select “setting” and click on advance
Then check the box just before removing any removable drivers and click save
b. Procedure to configure Windows Firewall for Windows 8.1
Operating Environment:
1. Operating System: Windows 8.1 Pro
2. Hardware: A Laptop
3. Software: VMware Horizon Client Installed
Descriptions:
Windows firewall is a protection application that protects against suspicious items, It helps in blocking suspicious programs .
Remote administration

The document discusses remote administration tools and their uses. Remote administration allows controlling and monitoring networked devices from remote locations. It has evolved beyond simply controlling devices over networks and now provides cost-effective access for remote workers. Remote administration tools can automate tasks, allow remote control and multiple sessions, remotely power devices, and maintain online inventories. Some tools like AndroRAT and Dark Comet are specifically for remote administration on Android and Windows systems, but can also be used maliciously if installed without permission on a target system.
Solution Manager 7.2 SAP Monitoring - Part 3 - Managed System Configuration

The document outlines the steps to configure a SAP HANA system for monitoring in SAP Solution Manager 7.2 SP5, including:
1. Registering the HANA system in the System Landscape Directory.
2. Installing the Diagnostics Agent and connecting it to Solution Manager.
3. Installing the HANA client on the Solution Manager server.
4. Uploading extractors for HANA 2.0 monitoring.
5. Assigning products, checking prerequisites, and finalizing the configuration.
Monitoring of computers 

This document provides instructions on how to use the Reliability Monitor and Performance Monitor tools in Windows to monitor system reliability and performance. It describes how Reliability Monitor calculates a System Stability Index and provides a stability report. It also explains how to open Performance Monitor to view performance data in real time or from log files, and how to connect to remote computers to monitor them. The document recommends increasing monitoring capabilities using Data Collector Sets to store log and trace information as well as general alerts.
Recommended
Piezo Power Business Plan

Piezo Power is developing Electroturf, a piezoelectric subflooring product that generates electricity from mechanical pressure like walking. It is led by CEO Daniel Walsh, CMO Cesia Gomez, CTO Jessemar Servida, and CFO Enrique Vazquez. Piezo Power believes Electroturf can harness wasted kinetic energy on a large scale and help reduce carbon footprints.
Fmea Innovator - Step by Step

Science has proven that the human mind recalls information best when the information is in a graphical format.
http://www.hoquality.com/software/fmea-innovator.php
Thougnts on the Future of Software Development

The document discusses different levels of automation for vehicles, from no automation where the driver performs all tasks to full automation where the system controls the vehicle under all conditions. It also examines how this classification framework could apply to AI-driven software development and how tools like low-code and AI coders could impact team structures and the role of software developers. The framework aims to effectively manage complexity and translate real-world problems into digital models.
1RUNNING HEAD MANAGING HOST BASED SECURITY IN WINDOWS 8.1La.docx

1RUNNING HEAD: MANAGING HOST BASED SECURITY IN WINDOWS 8.1
Lab Deliverable for Lab 2
a. Procedure to Manage Windows Defender
Operating Environment:
1. Operating System: Windows 8.1 Pro
2. Hardware: A Laptop
3. Software: VMware Horizon Client Installed
Description:
This window configuration project will require the sytem admin permission so as to access the programs and get to know how it is commanded to the action it should peform. Also, to use a virtual box one should have knowledge in how to operate the virtual box and explore the virtual programs
Notes, Warnings and Restrictions:
1. Windows Defender come with windows 8.1 software and are found in the control panel.
2. The application is used only when you login your system as an administarator or have permitted to act as the administrator.
3. For windows defender to run in the system it should be turned on and no other antivirus should be active
4. Scanning the system with windows defender deletes infected files. Also ensure you do the required scanning
5. If a different anti virus has been previously deleted, then windows defender needs to be turned off and to be restarted
Resources (Futher Reading):
Firewalls. (n.d.). Retrieved from https://technet.microsoft.com/en-us/library/cc700820.aspx
Microsoft Baseline Security Analyzer. (2011). Retrieved from https://dougvitale.wordpress.com/2011/11/18/microsoft-baseline-security-analyzer/
CloudFlare. (n.d.). Retrieved from https://www.winhelp.us/configure-windows-defender-in-windows-8.html
Procedures:
Windows defender
Window defender protects a computer system against any form of malware by running in the background of the computer system and gives notification if any suspicious item is found in the syatem for the user to take action. It can also be used by a computer to scan the system if the system has issues e.g becomes slow, switches off when not commanded to, hanging among other things. Windows defender should be updated over time so that it is not outdated and also to improve its performance.
Windows defender is found in the control panel icon, steps of opening are
i. Open control panel and select “windows defender”
ii. While you click on windows defender, the following page appears
a) To update the system click on “update”
b) Real time scanning
c) For the full scan results it will appear in the table as shown below
d) For quick results check the button just before you click on scan. Then the results will appear as shown below.
e) To scan removable device, select “setting” and click on advance
Then check the box just before removing any removable drivers and click save
b. Procedure to configure Windows Firewall for Windows 8.1
Operating Environment:
1. Operating System: Windows 8.1 Pro
2. Hardware: A Laptop
3. Software: VMware Horizon Client Installed
Descriptions:
Windows firewall is a protection application that protects against suspicious items, It helps in blocking suspicious programs .
Remote administration

The document discusses remote administration tools and their uses. Remote administration allows controlling and monitoring networked devices from remote locations. It has evolved beyond simply controlling devices over networks and now provides cost-effective access for remote workers. Remote administration tools can automate tasks, allow remote control and multiple sessions, remotely power devices, and maintain online inventories. Some tools like AndroRAT and Dark Comet are specifically for remote administration on Android and Windows systems, but can also be used maliciously if installed without permission on a target system.
Solution Manager 7.2 SAP Monitoring - Part 3 - Managed System Configuration

The document outlines the steps to configure a SAP HANA system for monitoring in SAP Solution Manager 7.2 SP5, including:
1. Registering the HANA system in the System Landscape Directory.
2. Installing the Diagnostics Agent and connecting it to Solution Manager.
3. Installing the HANA client on the Solution Manager server.
4. Uploading extractors for HANA 2.0 monitoring.
5. Assigning products, checking prerequisites, and finalizing the configuration.
Monitoring of computers 

This document provides instructions on how to use the Reliability Monitor and Performance Monitor tools in Windows to monitor system reliability and performance. It describes how Reliability Monitor calculates a System Stability Index and provides a stability report. It also explains how to open Performance Monitor to view performance data in real time or from log files, and how to connect to remote computers to monitor them. The document recommends increasing monitoring capabilities using Data Collector Sets to store log and trace information as well as general alerts.
Fully Automated Nagios (FAN)

FAN (Fully Automated Nagios) is a free and open source network monitoring tool based on Nagios. It provides an easy to install and use platform for monitoring networks and systems through integrated tools like Nagios, Centreon, NagVis and others. Key features of FAN include being free, able to monitor various operating systems and devices, having an easy to understand configuration, and including many monitoring plugins. The document provides information on installing and configuring FAN, including system requirements, the installation process, and how to add and monitor hosts, services, and configure alerts.
Techno-Fest-15nov16

These slides were presented during technical event at my organization. It focuses on overview to find a root cause of the unexpected system down events. It is mainly useful for Linux or Unix system administrators. Here, I tried to cover all aspects of the topic. It took me more than 2 hours to present these slides, but one can also cover these slides within short time-span. Gray background of slides is implemented to hide the company logo and to preserve the confidentially of private template. However, The Knowledge is not restricted :)
Why Is My Laptop Running Slow ? Read Tips & Solution 2024

Is your laptop running slow? Discover effective tips to boost its speed and performance. Contact Hire IT Expert for professional tech support.
paladintroubleshootingguide-1273931003659-phpapp02

This document provides troubleshooting guidance for issues that may arise with Paladin, an anti-spyware software created by Aluria Software. It addresses frequently asked questions about installing and using Paladin's server and client components, and provides steps to resolve common errors. The document is organized into sections on the Paladin Server, Client, and General troubleshooting.
Priority levels in Windows

The document discusses Windows thread priority levels, which range from 0 to 31 and are divided into variable and real-time levels. All threads are initially created with a normal priority level. Thread priority can be adjusted relative to other threads in the same process using the SetThreadPriority function. Input threads are typically given above normal or highest priority to ensure responsiveness, while background threads may use below normal or lowest priority levels. Processors use priority levels internally, and they can be viewed and changed through various tools.
Ad control

This document provides information about using AD Control (adctrl) to manage workers for Oracle E-Business Suite application patching (AD) and AutoPatch processes. Adctrl allows checking worker status, restarting or skipping failed workers. Common worker errors seen during patching are discussed along with their resolutions. The document also notes some undocumented adctrl options and how to find worker log files.
access-control-time-attendance-management-system-user-manual-rev-e103.pptx

The document is a user manual for an Access Control & Time Attendance Management System. It contains 10 chapters that describe:
1) The software installation process and requirements
2) An overview of the system's functional properties and main sub-systems
3) Instructions for user management, attendance management, device management, and system maintenance features.
4) Details on setting up departments, registering and managing users, connecting devices, and generating various reports.
Implementing Vulnerability Management 

Derek Milroy, IS Security Architect at U.S. Cellular Corporation, defined “vulnerability management” and how it affects today’s organizations during his presentation at the 2014 Chief Information Security Officer (CISO) Leadership Forum in Chicago on Nov. 19. In his presentation, “Enterprise Vulnerability Management/Security Incident Response,” Milroy noted vulnerability management has different meanings to different organizations, but an organization that utilizes vulnerability management processes can effectively safeguard its data.
According to Milroy, an organization should develop its own vulnerability management baselines to monitor its security levels. By doing so, Milroy said an organization can launch and control vulnerability management systems successfully. In addition, Milroy pointed out that vulnerability management problems occasionally will arise, but a well-prepared organization will be equipped to handle such issues: “Problems are going to happen … You have to work with your people. This can translate to any tool that you’re putting in place. Make sure your people have plans for what happens when it goes wrong, because it’s going to [happen] every single time.”
Milroy also noted that having actionable vulnerability management data is important for organizations of all sizes. If an organization evaluates its vulnerability management processes regularly, Milroy said, it can collect data and use this information to improve its security: “The simplest rule of thumb for vulnerability management, click the report, hand the report to someone. Don’t ever do that. There is no such thing as a report from a tool that you can just click and hand to someone until you first tune it and pare it down.”
- See more at: http://www.argylejournal.com/chief-information-security-officer/enterprise-vulnerability-managementsecurity-incident-response-derek-milroy-is-security-architect-u-s-cellular-corporation/#sthash.Buh6CzLS.dpuf
Laptop Selection System

The document describes a proposed Laptop Selection System that would help users choose the best laptop to purchase. The system would use rule-based techniques to analyze user-selected preference criteria and recommend suitable laptop options. It would have separate interfaces for administrators to manage laptop and criteria information, and for users to provide their criteria and receive recommendations. The system aims to address the challenges of selecting a laptop by simplifying the process and matching users with laptops that meet their needs.
IT6701 Information Management - Unit II 

The document discusses various types of malicious code and program security issues. It describes viruses, trojan horses, worms, and other types of malicious code. It also discusses common program vulnerabilities like buffer overflows, incomplete input validation, and race conditions. The document provides examples of each and methods to prevent vulnerabilities and defend against malicious code threats.
Sample Test Plan

This test case document describes testing the customization of application views by allowing users to select and modify templates. It includes the main success scenario of selecting a template, modifying appearance properties, saving changes, and seeing the updated view. It also includes alternative test cases like using a missing or restricted template, performing invalid edits, and exiting without saving. Requirements for help, offline use, and performance are also checked.
Troubleshooting Your ABAP Programs Using Coverage Analyzer

This document provides information on using Coverage Analyzer in ABAP to analyze and monitor processing blocks such as reports, subroutines, functions, and methods. Coverage Analyzer allows administrators to set parameters, filter programs by package, and view summary statistics. It also allows developers to check program execution counts, runtime errors, and view details to help troubleshoot ABAP programs.
Exchange manage with scom

This document provides instructions for managing Exchange Server 2013 with System Center 2012 R2. It describes using System Center 2012 R2 Data Protection Manager to back up and restore Exchange databases, using System Center 2012 R2 Operations Manager to monitor Exchange health, and automating tasks with System Center 2012 R2 Orchestrator. The lab guide walks through backing up Exchange with DPM, restoring a full database and individual mailbox with DPM, and reviewing backup health with Operations Manager.
Hp storage 

This document provides instructions for installing and using the HP Storage Manager utility to configure and manage RAID configurations on HP SATA RAID controllers. It describes how to install HP Storage Manager on Windows, Linux and NetWare operating systems. It also explains how to log in to systems, create logical drives, and set up remote monitoring to receive notifications about events on managed systems.
Pharmacymanagement- Harish(221348092).pptx

This document outlines a pharmacy management system project. The objectives are to develop a user-friendly application to help pharmacists manage tasks like medicine management and billing. It aims to automate billing and allow fast searching, adding, editing and deleting of medicine data. The design includes responsive user and admin panels and a database. Development involved setting up the LAMP stack, composer, and the database. Programming languages used include PHP, MySQL, CSS, JavaScript, HTML and jQuery. Testing was conducted before deployment. Problems addressed include interface issues, invoice numbering, server changes, case sensitivity for searching, and stock and account management.
Dot Net Application Monitoring

This document provides an overview of different tools for troubleshooting production application issues: IntelliTrace, WinDbg, and System Center Application Performance Monitoring (APM). IntelliTrace allows recording an application's execution flow and data for historical debugging. WinDbg generates dump files for critical hang/termination issues. System Center APM provides always-on monitoring of applications, performance monitoring, and correlation across servers. The document compares the tools and provides demos of collecting traces using IntelliTrace and monitoring an application with System Center APM.
Mnl,eng,rasplus%20 blank,v1.6

The document describes the Remote Administration System Plus (RASplus) software. It has chapters on installation, configuration, operation, and appendices. The configuration chapter explains the different panels of the RASplus interface, including the screen, remote sites panel, favorite sites panel, map panel, and others. It describes how to connect to remote sites, view their status, control PTZ cameras, and search recorded video.
Paladin Troubleshooting Guide

This document provides troubleshooting information for Paladin, an anti-spyware software created by Aluria Software. It addresses frequently asked questions about installing and using Paladin's server and client components. The document is divided into sections on the Paladin server, client, and general troubleshooting. Questions cover issues installing software requirements, deploying clients, updating clients, and resolving error codes. Answers provide steps to resolve installation errors, manually deploy or uninstall clients, and check that server services are running properly.
Preventive maintainnance

This document provides information on common computer issues and solutions. It defines preventive maintenance as maintenance performed on working machines to prevent breakdowns. It then gives solutions for issues like a non-responsive computer which can be fixed by restoring to an earlier restore point, a failing hard drive which may require disk checking software, a CPU stuck to a heat sink which can be gently twisted or soaked in alcohol to remove, a slow computer which can benefit from more RAM or hard drive maintenance, and a computer turning off itself which may have cable, overheating, or battery issues.
Solman managed system_configuration_abap_systems-libre

1. An ABAP system was added to the SLD of Solution Manager 7.1 by executing transaction RZ70 and selecting appropriate components. This ensures any system upgrades are reported to the Solution Manager SLD.
2. The technical system was assigned to a product instance and product system in LMDB after being added to the SLD. The product instance was marked as diagnostic relevant.
3. The managed system was configured in Solution Manager 7.1 by executing transaction solman_setup and following the configuration steps. This included assigning a diagnostic agent, setting up DBA Cockpit connection, creating a user, activating services, and selecting a logical system.
How to shutdown the Netapp SAN 8.3 and 9.2 version

Here it has been described the step by step process "how to shutdown or power down of the Netapp Cluster mode system version 8.3 onwards
How to Shutdown Netapp Cluster Mode Storage System with Multi-Node Cluster (6...

Here we have explain step by step how to shutdown the Netapp storage System with Multi-Node Cluster (6 nodes cluster with ontap version 9.1P14 with model FAS8200, AFF8040 & AFF8020)
More Related Content
Similar to Use of administrative privilege levels in netapp cluster 8.x
Fully Automated Nagios (FAN)

FAN (Fully Automated Nagios) is a free and open source network monitoring tool based on Nagios. It provides an easy to install and use platform for monitoring networks and systems through integrated tools like Nagios, Centreon, NagVis and others. Key features of FAN include being free, able to monitor various operating systems and devices, having an easy to understand configuration, and including many monitoring plugins. The document provides information on installing and configuring FAN, including system requirements, the installation process, and how to add and monitor hosts, services, and configure alerts.
Techno-Fest-15nov16

These slides were presented during technical event at my organization. It focuses on overview to find a root cause of the unexpected system down events. It is mainly useful for Linux or Unix system administrators. Here, I tried to cover all aspects of the topic. It took me more than 2 hours to present these slides, but one can also cover these slides within short time-span. Gray background of slides is implemented to hide the company logo and to preserve the confidentially of private template. However, The Knowledge is not restricted :)
Why Is My Laptop Running Slow ? Read Tips & Solution 2024

Is your laptop running slow? Discover effective tips to boost its speed and performance. Contact Hire IT Expert for professional tech support.
paladintroubleshootingguide-1273931003659-phpapp02

This document provides troubleshooting guidance for issues that may arise with Paladin, an anti-spyware software created by Aluria Software. It addresses frequently asked questions about installing and using Paladin's server and client components, and provides steps to resolve common errors. The document is organized into sections on the Paladin Server, Client, and General troubleshooting.
Priority levels in Windows

The document discusses Windows thread priority levels, which range from 0 to 31 and are divided into variable and real-time levels. All threads are initially created with a normal priority level. Thread priority can be adjusted relative to other threads in the same process using the SetThreadPriority function. Input threads are typically given above normal or highest priority to ensure responsiveness, while background threads may use below normal or lowest priority levels. Processors use priority levels internally, and they can be viewed and changed through various tools.
Ad control

This document provides information about using AD Control (adctrl) to manage workers for Oracle E-Business Suite application patching (AD) and AutoPatch processes. Adctrl allows checking worker status, restarting or skipping failed workers. Common worker errors seen during patching are discussed along with their resolutions. The document also notes some undocumented adctrl options and how to find worker log files.
access-control-time-attendance-management-system-user-manual-rev-e103.pptx

The document is a user manual for an Access Control & Time Attendance Management System. It contains 10 chapters that describe:
1) The software installation process and requirements
2) An overview of the system's functional properties and main sub-systems
3) Instructions for user management, attendance management, device management, and system maintenance features.
4) Details on setting up departments, registering and managing users, connecting devices, and generating various reports.
Implementing Vulnerability Management 

Derek Milroy, IS Security Architect at U.S. Cellular Corporation, defined “vulnerability management” and how it affects today’s organizations during his presentation at the 2014 Chief Information Security Officer (CISO) Leadership Forum in Chicago on Nov. 19. In his presentation, “Enterprise Vulnerability Management/Security Incident Response,” Milroy noted vulnerability management has different meanings to different organizations, but an organization that utilizes vulnerability management processes can effectively safeguard its data.
According to Milroy, an organization should develop its own vulnerability management baselines to monitor its security levels. By doing so, Milroy said an organization can launch and control vulnerability management systems successfully. In addition, Milroy pointed out that vulnerability management problems occasionally will arise, but a well-prepared organization will be equipped to handle such issues: “Problems are going to happen … You have to work with your people. This can translate to any tool that you’re putting in place. Make sure your people have plans for what happens when it goes wrong, because it’s going to [happen] every single time.”
Milroy also noted that having actionable vulnerability management data is important for organizations of all sizes. If an organization evaluates its vulnerability management processes regularly, Milroy said, it can collect data and use this information to improve its security: “The simplest rule of thumb for vulnerability management, click the report, hand the report to someone. Don’t ever do that. There is no such thing as a report from a tool that you can just click and hand to someone until you first tune it and pare it down.”
- See more at: http://www.argylejournal.com/chief-information-security-officer/enterprise-vulnerability-managementsecurity-incident-response-derek-milroy-is-security-architect-u-s-cellular-corporation/#sthash.Buh6CzLS.dpuf
Laptop Selection System

The document describes a proposed Laptop Selection System that would help users choose the best laptop to purchase. The system would use rule-based techniques to analyze user-selected preference criteria and recommend suitable laptop options. It would have separate interfaces for administrators to manage laptop and criteria information, and for users to provide their criteria and receive recommendations. The system aims to address the challenges of selecting a laptop by simplifying the process and matching users with laptops that meet their needs.
IT6701 Information Management - Unit II 

The document discusses various types of malicious code and program security issues. It describes viruses, trojan horses, worms, and other types of malicious code. It also discusses common program vulnerabilities like buffer overflows, incomplete input validation, and race conditions. The document provides examples of each and methods to prevent vulnerabilities and defend against malicious code threats.
Sample Test Plan

This test case document describes testing the customization of application views by allowing users to select and modify templates. It includes the main success scenario of selecting a template, modifying appearance properties, saving changes, and seeing the updated view. It also includes alternative test cases like using a missing or restricted template, performing invalid edits, and exiting without saving. Requirements for help, offline use, and performance are also checked.
Troubleshooting Your ABAP Programs Using Coverage Analyzer

This document provides information on using Coverage Analyzer in ABAP to analyze and monitor processing blocks such as reports, subroutines, functions, and methods. Coverage Analyzer allows administrators to set parameters, filter programs by package, and view summary statistics. It also allows developers to check program execution counts, runtime errors, and view details to help troubleshoot ABAP programs.
Exchange manage with scom

This document provides instructions for managing Exchange Server 2013 with System Center 2012 R2. It describes using System Center 2012 R2 Data Protection Manager to back up and restore Exchange databases, using System Center 2012 R2 Operations Manager to monitor Exchange health, and automating tasks with System Center 2012 R2 Orchestrator. The lab guide walks through backing up Exchange with DPM, restoring a full database and individual mailbox with DPM, and reviewing backup health with Operations Manager.
Hp storage 

This document provides instructions for installing and using the HP Storage Manager utility to configure and manage RAID configurations on HP SATA RAID controllers. It describes how to install HP Storage Manager on Windows, Linux and NetWare operating systems. It also explains how to log in to systems, create logical drives, and set up remote monitoring to receive notifications about events on managed systems.
Pharmacymanagement- Harish(221348092).pptx

This document outlines a pharmacy management system project. The objectives are to develop a user-friendly application to help pharmacists manage tasks like medicine management and billing. It aims to automate billing and allow fast searching, adding, editing and deleting of medicine data. The design includes responsive user and admin panels and a database. Development involved setting up the LAMP stack, composer, and the database. Programming languages used include PHP, MySQL, CSS, JavaScript, HTML and jQuery. Testing was conducted before deployment. Problems addressed include interface issues, invoice numbering, server changes, case sensitivity for searching, and stock and account management.
Dot Net Application Monitoring

This document provides an overview of different tools for troubleshooting production application issues: IntelliTrace, WinDbg, and System Center Application Performance Monitoring (APM). IntelliTrace allows recording an application's execution flow and data for historical debugging. WinDbg generates dump files for critical hang/termination issues. System Center APM provides always-on monitoring of applications, performance monitoring, and correlation across servers. The document compares the tools and provides demos of collecting traces using IntelliTrace and monitoring an application with System Center APM.
Mnl,eng,rasplus%20 blank,v1.6

The document describes the Remote Administration System Plus (RASplus) software. It has chapters on installation, configuration, operation, and appendices. The configuration chapter explains the different panels of the RASplus interface, including the screen, remote sites panel, favorite sites panel, map panel, and others. It describes how to connect to remote sites, view their status, control PTZ cameras, and search recorded video.
Paladin Troubleshooting Guide

This document provides troubleshooting information for Paladin, an anti-spyware software created by Aluria Software. It addresses frequently asked questions about installing and using Paladin's server and client components. The document is divided into sections on the Paladin server, client, and general troubleshooting. Questions cover issues installing software requirements, deploying clients, updating clients, and resolving error codes. Answers provide steps to resolve installation errors, manually deploy or uninstall clients, and check that server services are running properly.
Preventive maintainnance

This document provides information on common computer issues and solutions. It defines preventive maintenance as maintenance performed on working machines to prevent breakdowns. It then gives solutions for issues like a non-responsive computer which can be fixed by restoring to an earlier restore point, a failing hard drive which may require disk checking software, a CPU stuck to a heat sink which can be gently twisted or soaked in alcohol to remove, a slow computer which can benefit from more RAM or hard drive maintenance, and a computer turning off itself which may have cable, overheating, or battery issues.
Solman managed system_configuration_abap_systems-libre

1. An ABAP system was added to the SLD of Solution Manager 7.1 by executing transaction RZ70 and selecting appropriate components. This ensures any system upgrades are reported to the Solution Manager SLD.
2. The technical system was assigned to a product instance and product system in LMDB after being added to the SLD. The product instance was marked as diagnostic relevant.
3. The managed system was configured in Solution Manager 7.1 by executing transaction solman_setup and following the configuration steps. This included assigning a diagnostic agent, setting up DBA Cockpit connection, creating a user, activating services, and selecting a logical system.
Similar to Use of administrative privilege levels in netapp cluster 8.x (20)
Why Is My Laptop Running Slow ? Read Tips & Solution 2024

Why Is My Laptop Running Slow ? Read Tips & Solution 2024
paladintroubleshootingguide-1273931003659-phpapp02

paladintroubleshootingguide-1273931003659-phpapp02
access-control-time-attendance-management-system-user-manual-rev-e103.pptx

access-control-time-attendance-management-system-user-manual-rev-e103.pptx
Troubleshooting Your ABAP Programs Using Coverage Analyzer

Troubleshooting Your ABAP Programs Using Coverage Analyzer
Solman managed system_configuration_abap_systems-libre

Solman managed system_configuration_abap_systems-libre
More from Saroj Sahu
How to shutdown the Netapp SAN 8.3 and 9.2 version

Here it has been described the step by step process "how to shutdown or power down of the Netapp Cluster mode system version 8.3 onwards
How to Shutdown Netapp Cluster Mode Storage System with Multi-Node Cluster (6...

Here we have explain step by step how to shutdown the Netapp storage System with Multi-Node Cluster (6 nodes cluster with ontap version 9.1P14 with model FAS8200, AFF8040 & AFF8020)
Autosupport email sending failed issue netapp cluster mode-

Sometimes autosupport message is not sending to the "autosupport.to" list, means we are not getting as an mail.
How to assign the disks in Netapp storage cluster mode 8.X

Here we have described how to assign the disks which are in unassigned state in netapp cluster mode storage system and explained in which scenario we have to assign the disks.
How to assign unowned disk in the netapp cluster 8.3 

Here it has been described how to assign the disk which is unowned to the node in the netapp cluster mode 8.3 and how to enable the disk assign option shelf level and stack level
Different type of shells In Netapp Cluster mode 8.X and how to access them t...

Here it has been described how to use different type of shells in the Netapp cluster mode 8.x storage
How to access the Netapp cluster mode 8.2 through CLI (command mode)

This document provides 3 methods for accessing a NetApp cluster mode storage system through the command line interface (CLI).
Method 1 involves connecting a laptop directly to the storage system's serial port using PuTTY software and logging in with username "admin". Method 2 allows using telnet or RSH by first cloning the firewall policy and enabling those services, but they are insecure. Method 3, which is recommended, uses SSH to securely access the storage system by hostname or IP and log in as "admin". The document provides instructions for downloading PuTTY and checking which CLI services are enabled or disabled.
How to shut down Netapp san 9.2 cluster mode version1

The document provides step-by-step instructions for shutting down and powering up a NetApp cluster mode system. It describes the process of:
1. Shutting down connected host machines, switches, and SAN components like controllers and disk shelves.
2. Powering up disk shelves first, then controllers, switches, and host machines after 5-10 minutes.
3. Entering commands like disabling the cluster, halting nodes, and enabling the cluster during shutdown and startup.
Unable to access the net app cluster mode 9.2 san through gui after power mai...

Unable to access the NetApp storage system 9.2 cluster mode due to cluster management LIF down and http service was disable. Here we have mentioned the real time issue which we have faced and solution has been given step by stem by using the command mode. Hope it can be useful for NetApp Administrators
Volume migration from one aggregate to other without impacting the applicatio...

How to migrate a volume from one aggregate to another in the cluster mode Netapp storage system with version 9.2 without any impact to the production
Uable to do ssh from the RedHat Linux machine to Netapp filer 7 mode storage ...

Unable to access Netapp Filer by ssh from the RedHat Linux machine throwing the error message as "Unable to negotiate with 10.150.10.10 port 22: no matching cipher found. Their offer: 3des-cbc
How to work seamlessly in your vm without pressing host key again and again

How to work seamlessly in your oracle VM which is installed with Cent OS or RedHat Linux? You can copy and past from your local machine to the VM without any difficulties. (HOST KEY is not required) (Guest editions CD image installation in Oracle VM (Cent OS, RedHat Linux
Deleting a vserver in Netapp cluster mode 

How to delete a vserver step by step in command mode in Netapp cluster mode version 9.2 system. Lot of hurdles can be avoided if you follow this document.Thank you!
How to enable efficiency (deduplication and compression in netapp cluster mod...

This step by step implementation of deduplication and compression will make you easy to implement in your environment on the volume of Netapp storage. we will get lot of space savings which will benefit for customer and business can grow beyond our limitation.
How to see the event and audit logs through ( gui and cli) in cluster ontap n...

With the help of this document, we can check the logs in NetApp storage. It will very helpful for troubleshooting of the issues. we can easily take the decision to act on the current issue by analysing the logs.
How to see the log files through ( gui and cli) in cluster ontap netapp stora...

How to see the logs in cluster data on tap storage system through the graphical user interface and the command line interface.
Snapshot technology Netapp storage

NetApp snapshot technology works by preserving the inode map at the time a snapshot is created and continuing to change the inode map on the active file system, while keeping the older version for the snapshot. Snapshots can be created quickly in just a few seconds without impacting performance and up to 255 snapshots can be created per volume, providing point-in-time copies of data.
SAN High availability (Netapp Storage) 

High availability ensures that network services and data are accessible at all times by configuring storage systems in high availability pairs. When a network interface fails, negotiated failover can trigger an automatic failover of the storage system to prevent loss of connectivity. Enabling negotiated failover and selecting which network interfaces to include allows the storage system to fail over to the other node. The benefits of high availability include uninterrupted data access, and the ability to perform nondisruptive upgrades to storage system components like motherboards, adapters, disks and interfaces.
3PAR: HOW TO CHANGE THE IP ADDRESS OF HP 3PAR SAN

The document provides steps to change the IP address of a HP 3PAR SAN. It outlines logging into the SAN through Putty using default credentials. It then details using the 'setnet' command to change the IP address, netmask, and gateway. The 'shownet' command confirms the new network settings. Login to the SP console allows changing additional settings like the hostname through interactive menus.
Aggregate standard for Netapp storage 7 mode 

1. Storage teams create aggregates using naming conventions like aggr0, aggr1 to provision storage. They decide the configuration including the RAID type, number of disks, and disk size.
2. When creating an aggregate, factors like recovery speed, data assurance, and storage space must be considered. Larger RAID groups improve performance but increase risk of data loss if multiple disks fail, while smaller groups reduce this risk but decrease performance.
3. Guidelines for RAID group sizing depend on disk type, with ATA/SATA generally having smaller groups than FC/SAS. The default sizes balance speed, protection, and space utilization, though the maximum sizes allow flexibility based on needs.
More from Saroj Sahu (20)
How to shutdown the Netapp SAN 8.3 and 9.2 version

How to shutdown the Netapp SAN 8.3 and 9.2 version
How to Shutdown Netapp Cluster Mode Storage System with Multi-Node Cluster (6...

How to Shutdown Netapp Cluster Mode Storage System with Multi-Node Cluster (6...
Autosupport email sending failed issue netapp cluster mode-

Autosupport email sending failed issue netapp cluster mode-
How to assign the disks in Netapp storage cluster mode 8.X

How to assign the disks in Netapp storage cluster mode 8.X
How to assign unowned disk in the netapp cluster 8.3 

How to assign unowned disk in the netapp cluster 8.3
Different type of shells In Netapp Cluster mode 8.X and how to access them t...

Different type of shells In Netapp Cluster mode 8.X and how to access them t...
How to access the Netapp cluster mode 8.2 through CLI (command mode)

How to access the Netapp cluster mode 8.2 through CLI (command mode)
How to shut down Netapp san 9.2 cluster mode version1

How to shut down Netapp san 9.2 cluster mode version1
Unable to access the net app cluster mode 9.2 san through gui after power mai...

Unable to access the net app cluster mode 9.2 san through gui after power mai...
Volume migration from one aggregate to other without impacting the applicatio...

Volume migration from one aggregate to other without impacting the applicatio...
Uable to do ssh from the RedHat Linux machine to Netapp filer 7 mode storage ...

Uable to do ssh from the RedHat Linux machine to Netapp filer 7 mode storage ...
How to work seamlessly in your vm without pressing host key again and again

How to work seamlessly in your vm without pressing host key again and again
How to enable efficiency (deduplication and compression in netapp cluster mod...

How to enable efficiency (deduplication and compression in netapp cluster mod...
How to see the event and audit logs through ( gui and cli) in cluster ontap n...

How to see the event and audit logs through ( gui and cli) in cluster ontap n...
How to see the log files through ( gui and cli) in cluster ontap netapp stora...

How to see the log files through ( gui and cli) in cluster ontap netapp stora...
Recently uploaded
GraphSummit Singapore | Graphing Success: Revolutionising Organisational Stru...

Sudheer Mechineni, Head of Application Frameworks, Standard Chartered Bank
Discover how Standard Chartered Bank harnessed the power of Neo4j to transform complex data access challenges into a dynamic, scalable graph database solution. This keynote will cover their journey from initial adoption to deploying a fully automated, enterprise-grade causal cluster, highlighting key strategies for modelling organisational changes and ensuring robust disaster recovery. Learn how these innovations have not only enhanced Standard Chartered Bank’s data infrastructure but also positioned them as pioneers in the banking sector’s adoption of graph technology.
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
Presentation of the OECD Artificial Intelligence Review of Germany

Consult the full report at https://www.oecd.org/digital/oecd-artificial-intelligence-review-of-germany-609808d6-en.htm
Pushing the limits of ePRTC: 100ns holdover for 100 days

At WSTS 2024, Alon Stern explored the topic of parametric holdover and explained how recent research findings can be implemented in real-world PNT networks to achieve 100 nanoseconds of accuracy for up to 100 days.
Microsoft - Power Platform_G.Aspiotis.pdf

Revolutionizing Application Development
with AI-powered low-code, presentation by George Aspiotis, Sr. Partner Development Manager, Microsoft
Essentials of Automations: The Art of Triggers and Actions in FME

In this second installment of our Essentials of Automations webinar series, we’ll explore the landscape of triggers and actions, guiding you through the nuances of authoring and adapting workspaces for seamless automations. Gain an understanding of the full spectrum of triggers and actions available in FME, empowering you to enhance your workspaces for efficient automation.
We’ll kick things off by showcasing the most commonly used event-based triggers, introducing you to various automation workflows like manual triggers, schedules, directory watchers, and more. Plus, see how these elements play out in real scenarios.
Whether you’re tweaking your current setup or building from the ground up, this session will arm you with the tools and insights needed to transform your FME usage into a powerhouse of productivity. Join us to discover effective strategies that simplify complex processes, enhancing your productivity and transforming your data management practices with FME. Let’s turn complexity into clarity and make your workspaces work wonders!
Mind map of terminologies used in context of Generative AI

Mind map of common terms used in context of Generative AI.
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
20240609 QFM020 Irresponsible AI Reading List May 2024

Everything I found interesting about the irresponsible use of machine intelligence in May 2024
Uni Systems Copilot event_05062024_C.Vlachos.pdf

Unlocking Productivity: Leveraging the Potential of Copilot in Microsoft 365, a presentation by Christoforos Vlachos, Senior Solutions Manager – Modern Workplace, Uni Systems
GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...

Leonard Jayamohan, Partner & Generative AI Lead, Deloitte
This keynote will reveal how Deloitte leverages Neo4j’s graph power for groundbreaking digital twin solutions, achieving a staggering 100x performance boost. Discover the essential role knowledge graphs play in successful generative AI implementations. Plus, get an exclusive look at an innovative Neo4j + Generative AI solution Deloitte is developing in-house.
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

As the digital landscape continually evolves, operating systems play a critical role in shaping user experiences and productivity. The launch of Nitrux Linux 3.5.0 marks a significant milestone, offering a robust alternative to traditional systems such as Windows 11. This article delves into the essence of Nitrux Linux 3.5.0, exploring its unique features, advantages, and how it stands as a compelling choice for both casual users and tech enthusiasts.
Communications Mining Series - Zero to Hero - Session 1

This session provides introduction to UiPath Communication Mining, importance and platform overview. You will acquire a good understand of the phases in Communication Mining as we go over the platform with you. Topics covered:
• Communication Mining Overview
• Why is it important?
• How can it help today’s business and the benefits
• Phases in Communication Mining
• Demo on Platform overview
• Q/A
Best 20 SEO Techniques To Improve Website Visibility In SERP

Boost your website's visibility with proven SEO techniques! Our latest blog dives into essential strategies to enhance your online presence, increase traffic, and rank higher on search engines. From keyword optimization to quality content creation, learn how to make your site stand out in the crowded digital landscape. Discover actionable tips and expert insights to elevate your SEO game.
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

Dr. Sean Tan, Head of Data Science, Changi Airport Group
Discover how Changi Airport Group (CAG) leverages graph technologies and generative AI to revolutionize their search capabilities. This session delves into the unique search needs of CAG’s diverse passengers and customers, showcasing how graph data structures enhance the accuracy and relevance of AI-generated search results, mitigating the risk of “hallucinations” and improving the overall customer journey.
“I’m still / I’m still / Chaining from the Block”

“An Outlook of the Ongoing and Future Relationship between Blockchain Technologies and Process-aware Information Systems.” Invited talk at the joint workshop on Blockchain for Information Systems (BC4IS) and Blockchain for Trusted Data Sharing (B4TDS), co-located with with the 36th International Conference on Advanced Information Systems Engineering (CAiSE), 3 June 2024, Limassol, Cyprus.
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Are you ready to revolutionize how you handle data? Join us for a webinar where we’ll bring you up to speed with the latest advancements in Generative AI technology and discover how leveraging FME with tools from giants like Google Gemini, Amazon, and Microsoft OpenAI can supercharge your workflow efficiency.
During the hour, we’ll take you through:
Guest Speaker Segment with Hannah Barrington: Dive into the world of dynamic real estate marketing with Hannah, the Marketing Manager at Workspace Group. Hear firsthand how their team generates engaging descriptions for thousands of office units by integrating diverse data sources—from PDF floorplans to web pages—using FME transformers, like OpenAIVisionConnector and AnthropicVisionConnector. This use case will show you how GenAI can streamline content creation for marketing across the board.
Ollama Use Case: Learn how Scenario Specialist Dmitri Bagh has utilized Ollama within FME to input data, create custom models, and enhance security protocols. This segment will include demos to illustrate the full capabilities of FME in AI-driven processes.
Custom AI Models: Discover how to leverage FME to build personalized AI models using your data. Whether it’s populating a model with local data for added security or integrating public AI tools, find out how FME facilitates a versatile and secure approach to AI.
We’ll wrap up with a live Q&A session where you can engage with our experts on your specific use cases, and learn more about optimizing your data workflows with AI.
This webinar is ideal for professionals seeking to harness the power of AI within their data management systems while ensuring high levels of customization and security. Whether you're a novice or an expert, gain actionable insights and strategies to elevate your data processes. Join us to see how FME and AI can revolutionize how you work with data!
Recently uploaded (20)
GraphSummit Singapore | Graphing Success: Revolutionising Organisational Stru...

GraphSummit Singapore | Graphing Success: Revolutionising Organisational Stru...
Presentation of the OECD Artificial Intelligence Review of Germany

Presentation of the OECD Artificial Intelligence Review of Germany
Pushing the limits of ePRTC: 100ns holdover for 100 days

Pushing the limits of ePRTC: 100ns holdover for 100 days
Essentials of Automations: The Art of Triggers and Actions in FME

Essentials of Automations: The Art of Triggers and Actions in FME
Mind map of terminologies used in context of Generative AI

Mind map of terminologies used in context of Generative AI
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
20240609 QFM020 Irresponsible AI Reading List May 2024

20240609 QFM020 Irresponsible AI Reading List May 2024
GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...

GraphSummit Singapore | The Future of Agility: Supercharging Digital Transfor...
Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!

Goodbye Windows 11: Make Way for Nitrux Linux 3.5.0!
Communications Mining Series - Zero to Hero - Session 1

Communications Mining Series - Zero to Hero - Session 1
Best 20 SEO Techniques To Improve Website Visibility In SERP

Best 20 SEO Techniques To Improve Website Visibility In SERP
GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...

GraphSummit Singapore | Enhancing Changi Airport Group's Passenger Experience...
Driving Business Innovation: Latest Generative AI Advancements & Success Story

Driving Business Innovation: Latest Generative AI Advancements & Success Story
Use of administrative privilege levels in netapp cluster 8.x
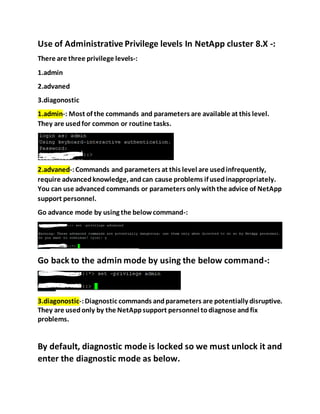
- 1. Use of Administrative Privilege levels In NetApp cluster 8.X -: There are three privilege levels-: 1.admin 2.advaned 3.diagonostic 1.admin-: Most of the commands and parameters are available at this level. They are usedfor common or routine tasks. 2.advaned-:Commands and parameters at this level are usedinfrequently, require advancedknowledge, andcan cause problems if usedinappropriately. You can use advanced commands or parameters only withthe advice of NetApp support personnel. Go advance mode by using the belowcommand-: Go back to the admin mode by using the below command-: 3.diagonostic-:Diagnostic commands andparameters are potentially disruptive. They are usedonly by the NetAppsupport personnel todiagnose andfix problems. By default, diagnostic mode is locked so we must unlock it and enter the diagnostic mode as below.
- 2. (Or) Exit from the diagnosticmode to admin mode Thank you! Saroj (NCDA Certified)!