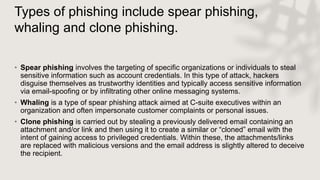
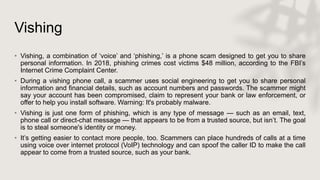
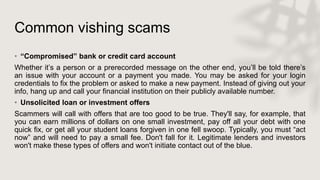
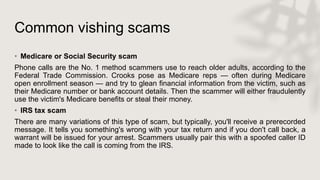
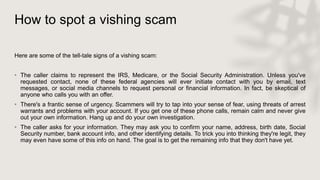
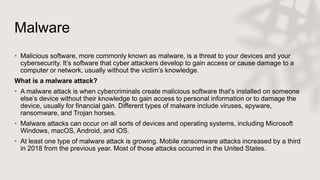
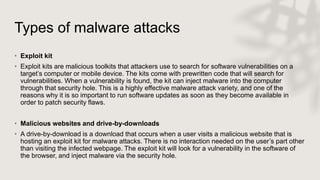
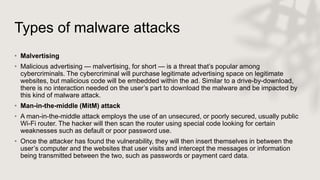
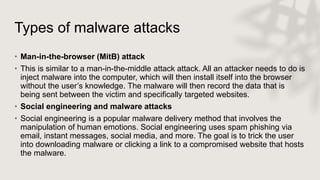
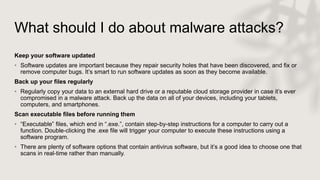
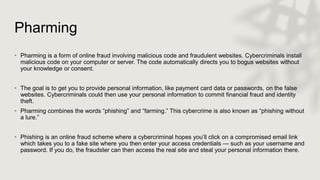
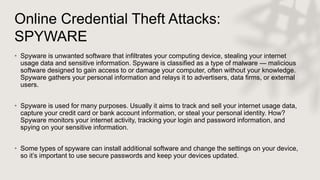
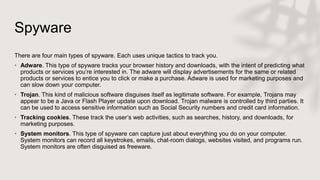
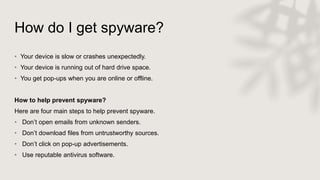
The document covers various hacking techniques, primarily focusing on credential-stealing attacks such as phishing, vishing, malware, and pharming. It details how these attacks occur, the types of phishing including spear phishing and whaling, as well as the functionalities of malware like spyware, worms, and trojans. Additionally, it emphasizes the importance of security measures, including multi-factor authentication and vigilance against common scams.