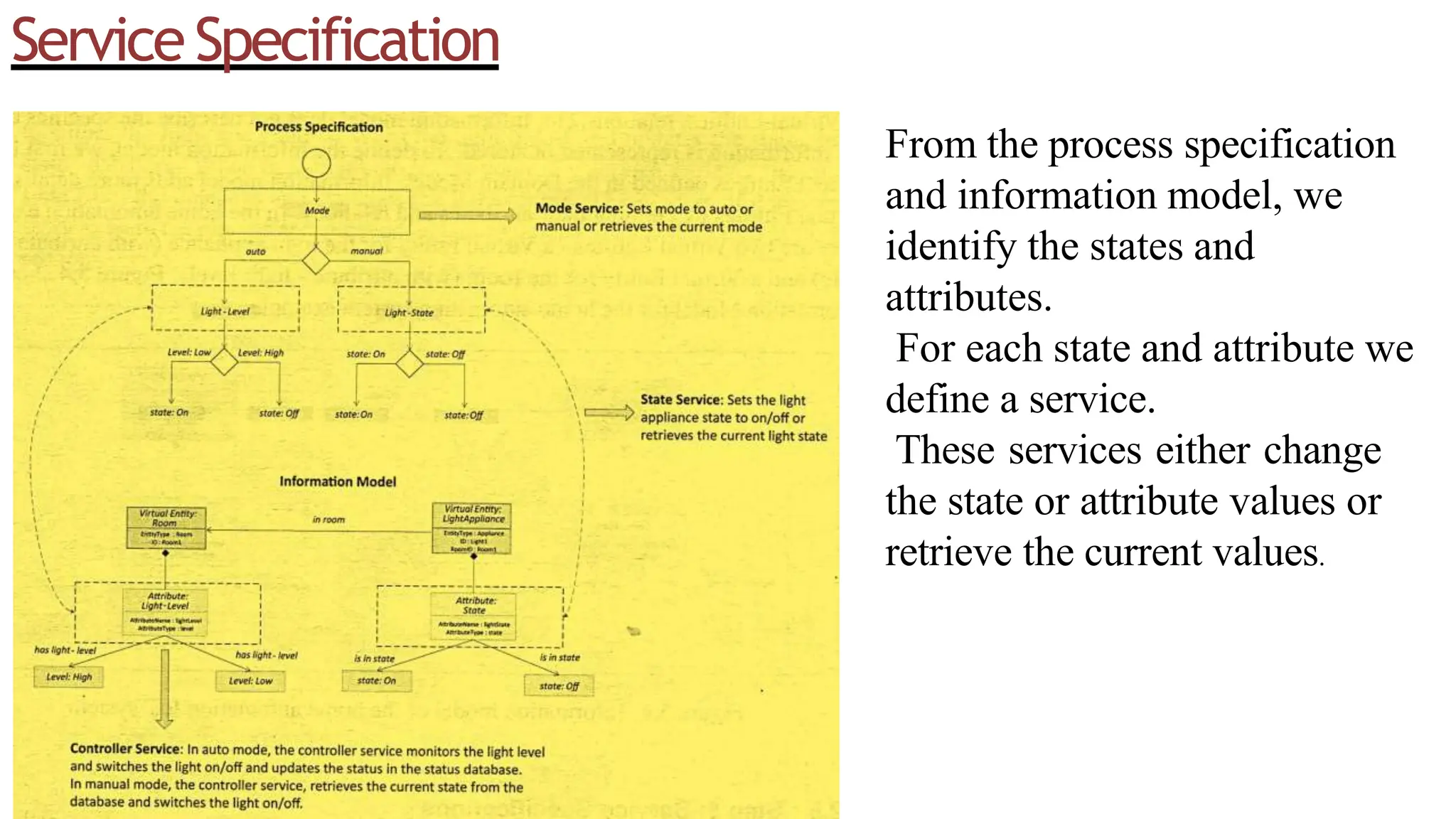
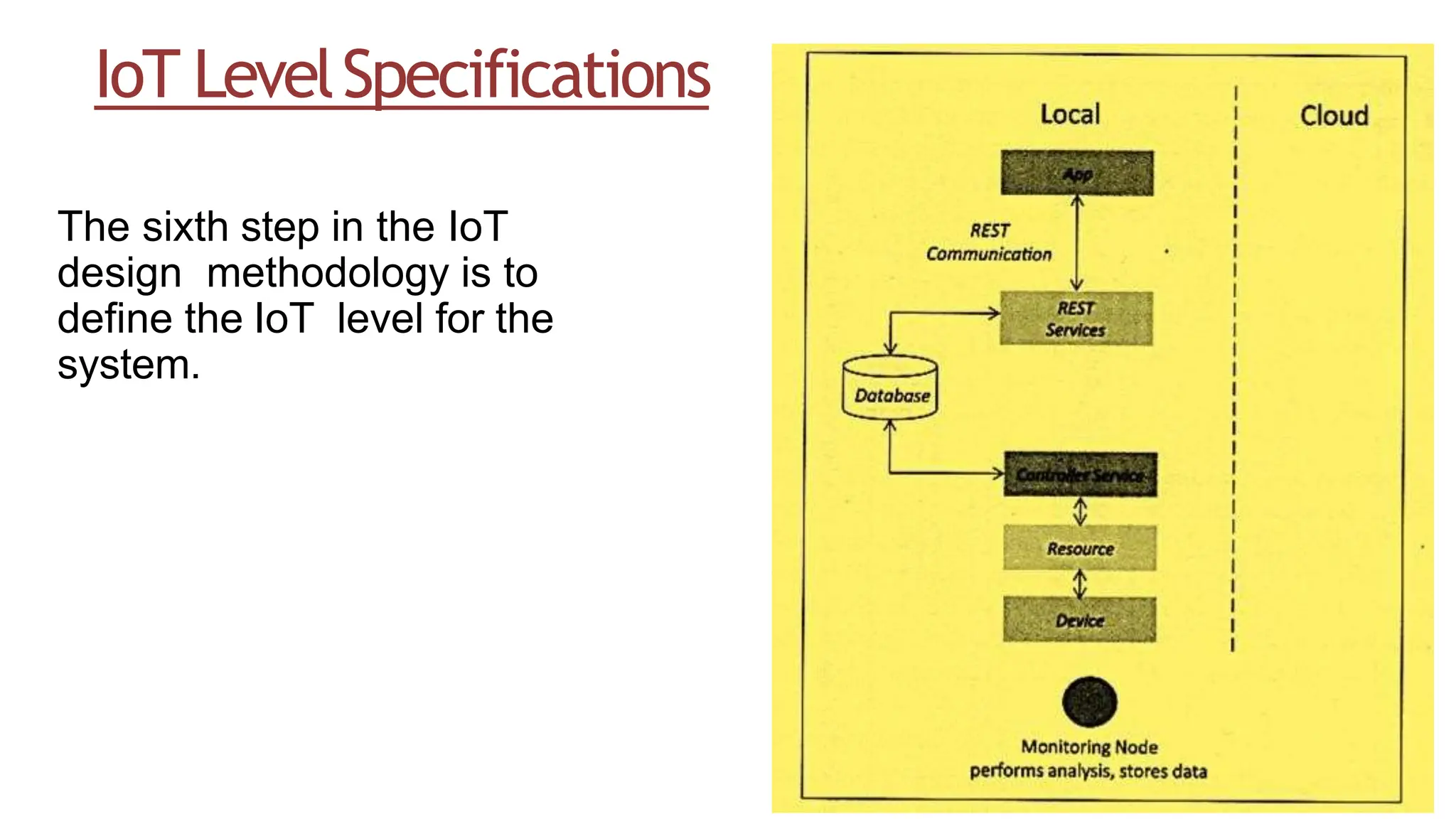
This document outlines the IoT platform design methodology, focusing on step-by-step specifications including purpose, process, domain, information, and service specifications. It emphasizes the importance of defining an information model to outline the structure of information within the IoT system, as well as service specifications that detail the services, inputs, outputs, and states relevant to the system. The document highlights defining IoT levels as a key part of the methodology.