The document discusses Trusted Platform Modules (TPMs), which are chips integrated into platforms that are intended to provide more security. TPMs can securely store encryption keys and perform cryptographic operations to establish trust. They aim to prevent compromise by malicious software. However, TPMs also enable new capabilities for digital rights management and attestation that could potentially be abused by software vendors. While TPMs may increase security for corporations and governments, they reduce user control and privacy.
![What is Trusted Computing?
In 1999, many industry heavyweights
came together to form an industry group.
Mission Statement
“to create a standard set of system
hardware based functions needed to
establish trust on the platform.” [2]](https://image.slidesharecdn.com/trustedcomputing1-240223113016-407c802e/85/Trusted-Computing-_plate-form_-model-ppt-2-320.jpg)
![What is a TPM?
• A chip integrated into the platform
• The (alleged) purpose is to provide more
security
• It is a separate trusted co-processor
“The TPM represents a separate trusted
coprocessor, whose state cannot be
compromised by potentially malicious
host system software.”
IBM Research Report [4]](https://image.slidesharecdn.com/trustedcomputing1-240223113016-407c802e/85/Trusted-Computing-_plate-form_-model-ppt-3-320.jpg)
![Attestation
The TPM's most controversial feature is
attestation, the ability to measure the state
of a computer and send a signed message
certifying that particular hardware or
software is or isn't present. Most TC
opponents fear that this will be abused by
vendors [1].](https://image.slidesharecdn.com/trustedcomputing1-240223113016-407c802e/85/Trusted-Computing-_plate-form_-model-ppt-6-320.jpg)
![How?
• Protection from malware and detection of
compromised systems. [4] Shows that syslogd
has been compromised by a root kit.
• Tick counter, Timestamps are a security critical
parameter in KERBEROS.
• Provide stronger 2 factor authentication.](https://image.slidesharecdn.com/trustedcomputing1-240223113016-407c802e/85/Trusted-Computing-_plate-form_-model-ppt-8-320.jpg)
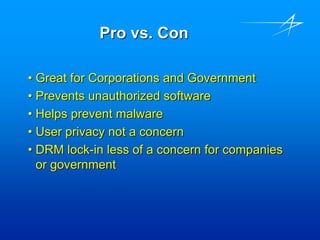
![Pro vs. Con
• “Trusted Computing requires you to surrender
control of your machine to the vendors of your
hardware and software, thereby making the
computer less trustworthy from the user’s
perspective” [11] Ross Anderson](https://image.slidesharecdn.com/trustedcomputing1-240223113016-407c802e/85/Trusted-Computing-_plate-form_-model-ppt-12-320.jpg)
![“For years Bill Gates has dreamed of
finding a way to make the Chinese pay
for software, TC looks like being the
answer to his prayer.” [11] Ross
Anderson.](https://image.slidesharecdn.com/trustedcomputing1-240223113016-407c802e/85/Trusted-Computing-_plate-form_-model-ppt-14-320.jpg)
![Bibliography
• [1] Andy Doman, Trusted Computing: A matter of Trust,
http://www.networkmagazine.com/shared/article/showArticle.jhtml?articleId=2210
2889
• [2] DigitalIDWorld, "Assuring Networked Data and Application Reliability", Digital ID
World Jan/Feb 2004 https://www.trustedcomputinggroup.org/press/1-
3412425E_SC.pdf
•
• [4] Reiner Sailer, et al, , "The Role of TPM in Enterprise Security",
https://www.trustedcomputinggroup.org/press/news_articles/rc23363.pdf
• [11] Ross Anderson, http://www.againsttcpa.com/index.shtml](https://image.slidesharecdn.com/trustedcomputing1-240223113016-407c802e/85/Trusted-Computing-_plate-form_-model-ppt-16-320.jpg)
