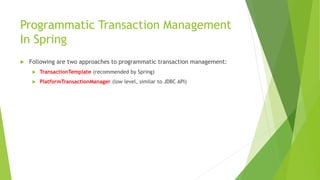
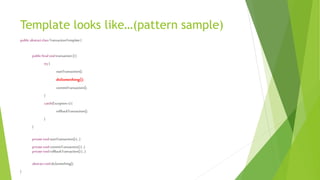
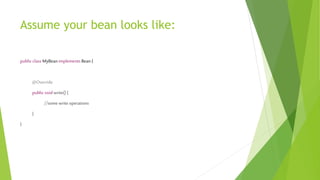
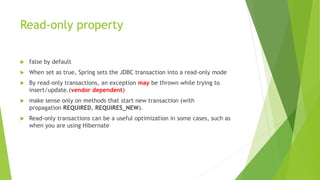
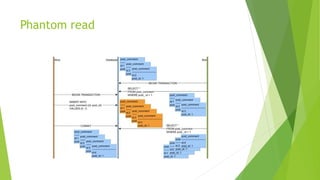
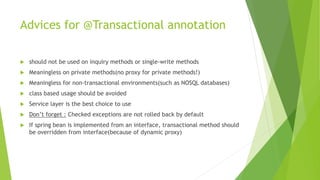
This document discusses transactions and concurrency in Java. It examines transaction management with the ACID properties and different transaction models including local, programmatic, and declarative. It describes how to create and end transactions using SQL commands as well as the use of autocommit. Concurrency management essentials and isolation levels in databases are also covered. Examples of implementing transactions using JDBC, Spring's TransactionTemplate and PlatformTransactionManager, and the @Transactional annotation are provided.