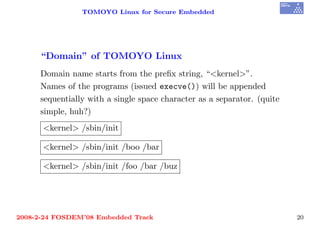
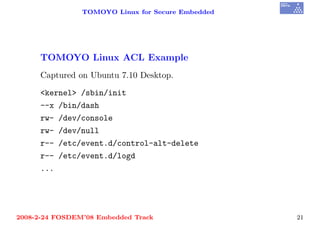
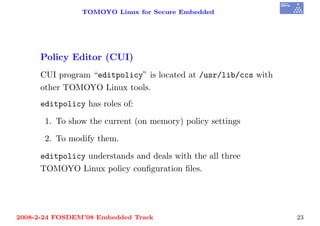
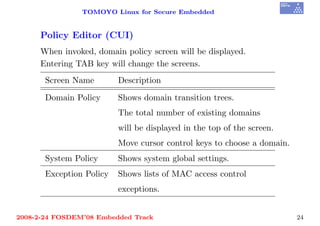
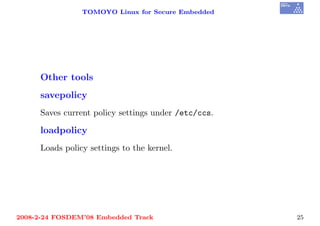
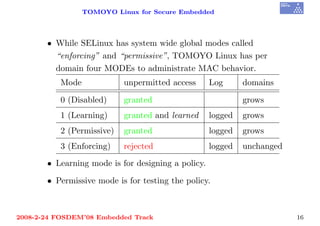
This document discusses TOMOYO Linux, a mandatory access control implementation for Linux. It provides an executive summary, describes key concepts like domains and profiles, and outlines features like the policy learning mode and policy editor tools. LiveCD and installation instructions are also covered. The goal of TOMOYO Linux is to provide usable mandatory access control for most users and administrators.
![TOMOYO Linux for Secure Embedded
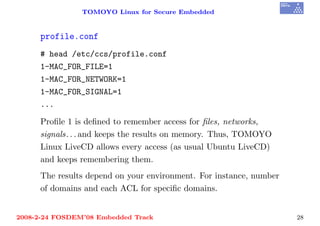
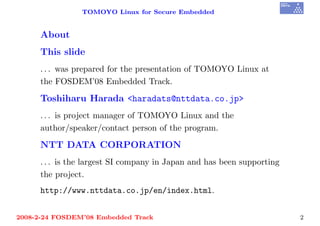
Profile definitions
Syntax
[Profile id(0-255)]-[Directive]=[Mode]
Example
1-COMMENT=----- Profile #1 Defs -----
1-MAC_FOR_FILE=1
1-MAC_FOR_NETWORK=1
2-COMMENT=----- Profile #2 Defs -----
2-MAC_FOR_FILE=2
2-MAC_FOR_NETWORK=2
2008-2-24 FOSDEM’08 Embedded Track 17](https://image.slidesharecdn.com/fosdem2008-pdf-090926064725-phpapp02/85/FOSDEM-08-TOMOYO-Linux-for-Secure-Embedded-18-320.jpg)