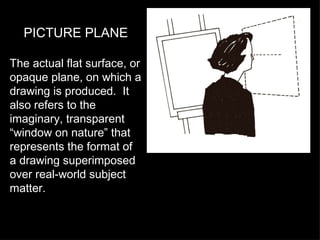
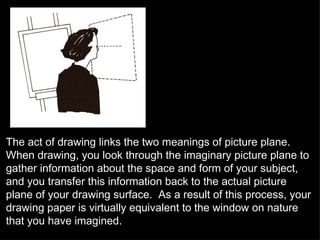
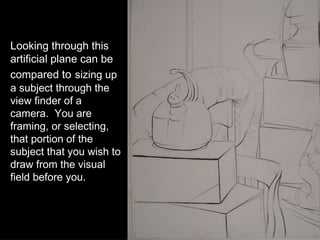
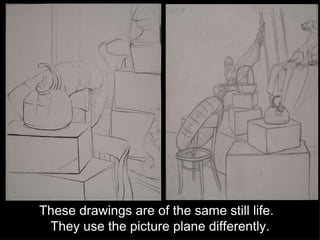
The picture plane refers to both the actual surface of the drawing and the imaginary transparent plane through which the artist views the subject. When drawing, the artist looks through the imaginary plane to observe the subject, then transfers this information to the actual drawing surface. Different uses of the picture plane can change the perceived spatial relationship between elements in the drawing.