Threat Intelligence Keys
•
0 likes•106 views
Type of Data Type of Data Collection Methods Type of Threat Intelligence Feeds
Report
Share
Report
Share
Download to read offline
Recommended
DPIA

A DPIA is a well-ordered list of data processing methods and purposes
A DPIA is also a proactive measure to safeguard and protect data using certified security mechanisms.
DPIA will help organisations to:
Identify
Fix problems at an early stage
Reducing the related costs
Damage to reputation
A Survey On Genetic Algorithm For Intrusion Detection System

The Internet has become a part of daily life and an essential tool today. Internet has been used as an important component of
business models. Therefore, It is very important to maintain a high level security to ensure safe and trusted communication of
information between various organizations.
Intrusion Detection Systems have become a needful component in terms of computer and network security. Intrusion detection is
one of the important security constraints for maintaining the integrity of information. Intrusion detection systems are the tools
used for prevention and detection of threats to computer systems. Various approaches have been applied in past that are less
effective to curb the menace of intrusion.
In this paper, a survey on applications of genetic algorithms in intrusion detection systems is carried out.
Synthesis of Polyurethane Solution (Castor oil based polyol for polyurethane)

Around 160 million hector unused is available in India. India is the world’s largest producer of castor oil,
producing over 75% of the total world’s supply. There are over a hundred companies in India-small and
medium-that are into castor oil production, producing a variety of the basic grades o castor oil. All the above
factors make it imperative that the India industry relooks at the castor oil sector in order to devise suitable
strategies to derive the most benefits from such an attractive confluence of factors. Castor oil is unique owing to
its exceptional diversity of application. The oil and its derivatives are used in over 100 different applications in
diverse industries such as paints, lubricants, pharma, cosmetics, paper, rubber and more. Recent developments
have successfully derived polyol from natural oils and synthesized range of PU product from them. However,
making flexible solution from natural oil polyol is still proving challenging. The goal of this thesis is to
understand the potentials and the limitations of natural oil as an alternative to petroleum polyol. An initial
attempt to understand natural oil polyol showed that flexible solution could be synthesized from castor oil,
which produced a rigid solution. Characterization results indicate that the glass transition temperature (Tg) was
the predominant factor that determines the rigidity of the solution. The high Tg of solution was attributed to the
low number of covalent bond between cross linkers.
Detecting Unknown Attacks Using Big Data Analysis

Nowadays threat of previously unknown cyber-attacks are increasing because existing security
systems are not able to detect them. Previously, leaking personal information by attacking the PC or
destroying the system was very common cyber attacks . But the goal of recent hacking attacks has changed
from leaking information and destruction of services to attacking large-scale systems such as critical
infrastructures and state agencies. In the other words, existing defence technologies to counter these attacks
are based on pattern matching methods which are very limited. Because of this fact, in the event of new and
previously unknown attacks, detection rate becomes very low and false negative increases. To defend
against these unknown attacks, which cannot be detected with existing technology, a new model based on
big data analysis techniques that can extract information from a variety of sources to detect future attacks is
proposed. The expectation with this model is future Advanced Persistent Threat (APT) detection and
prevention.
Recommended
DPIA

A DPIA is a well-ordered list of data processing methods and purposes
A DPIA is also a proactive measure to safeguard and protect data using certified security mechanisms.
DPIA will help organisations to:
Identify
Fix problems at an early stage
Reducing the related costs
Damage to reputation
A Survey On Genetic Algorithm For Intrusion Detection System

The Internet has become a part of daily life and an essential tool today. Internet has been used as an important component of
business models. Therefore, It is very important to maintain a high level security to ensure safe and trusted communication of
information between various organizations.
Intrusion Detection Systems have become a needful component in terms of computer and network security. Intrusion detection is
one of the important security constraints for maintaining the integrity of information. Intrusion detection systems are the tools
used for prevention and detection of threats to computer systems. Various approaches have been applied in past that are less
effective to curb the menace of intrusion.
In this paper, a survey on applications of genetic algorithms in intrusion detection systems is carried out.
Synthesis of Polyurethane Solution (Castor oil based polyol for polyurethane)

Around 160 million hector unused is available in India. India is the world’s largest producer of castor oil,
producing over 75% of the total world’s supply. There are over a hundred companies in India-small and
medium-that are into castor oil production, producing a variety of the basic grades o castor oil. All the above
factors make it imperative that the India industry relooks at the castor oil sector in order to devise suitable
strategies to derive the most benefits from such an attractive confluence of factors. Castor oil is unique owing to
its exceptional diversity of application. The oil and its derivatives are used in over 100 different applications in
diverse industries such as paints, lubricants, pharma, cosmetics, paper, rubber and more. Recent developments
have successfully derived polyol from natural oils and synthesized range of PU product from them. However,
making flexible solution from natural oil polyol is still proving challenging. The goal of this thesis is to
understand the potentials and the limitations of natural oil as an alternative to petroleum polyol. An initial
attempt to understand natural oil polyol showed that flexible solution could be synthesized from castor oil,
which produced a rigid solution. Characterization results indicate that the glass transition temperature (Tg) was
the predominant factor that determines the rigidity of the solution. The high Tg of solution was attributed to the
low number of covalent bond between cross linkers.
Detecting Unknown Attacks Using Big Data Analysis

Nowadays threat of previously unknown cyber-attacks are increasing because existing security
systems are not able to detect them. Previously, leaking personal information by attacking the PC or
destroying the system was very common cyber attacks . But the goal of recent hacking attacks has changed
from leaking information and destruction of services to attacking large-scale systems such as critical
infrastructures and state agencies. In the other words, existing defence technologies to counter these attacks
are based on pattern matching methods which are very limited. Because of this fact, in the event of new and
previously unknown attacks, detection rate becomes very low and false negative increases. To defend
against these unknown attacks, which cannot be detected with existing technology, a new model based on
big data analysis techniques that can extract information from a variety of sources to detect future attacks is
proposed. The expectation with this model is future Advanced Persistent Threat (APT) detection and
prevention.
A Survey: Comparative Analysis of Classifier Algorithms for DOS Attack Detection

In today's interconnected world, one of pervasive issue is how to protect system from intrusion based security attacks. It is an important issue to detect the intrusion attacks for the security of network communication.Denial of Service (DoS) attacks is evolving continuously. These attacks make network resources unavailable for legitimate users which results in massive loss of data, resources and money.Significance of Intrusion detection system (IDS) in computer network security well proven. Intrusion Detection Systems (IDSs) have become an efficient defense tool against network attacks since they allow network administrator to detect policy violations. Mining approach can play very important role in developing intrusion detection system. Classification is identified as an important technique of data mining. This paper evaluates performance of well known classification algorithms for attack classification. The key ideas are to use data mining techniques efficiently for intrusion attack classification. To implement and measure the performance of our system we used the KDD99 benchmark dataset and obtained reasonable detection rate.
RISK MITIGATION AND THREAT IDENTIFICATIONIntroductionInforma.docx

RISK MITIGATION AND THREAT IDENTIFICATION
Introduction
Information security in a modern organization exists primarily to manage information technology
(IT) risk. Managing risk is one of the key responsibilities of every manager within an
organization. In any well-developed risk management program, two formal processes are at
work. The first, risk identification and assessment, is discussed in this chapter; the second,
risk control, is the subject of the next chapter.
Each manager in the organization, regardless of his or her affiliation with one of the three
communities of interest, should focus on reducing risk as follows:
● General management must structure the IT and information security functions in ways
that will result in the successful defense of the organization’s information assets,
including data, hardware, software, procedures, and people.
● IT management must serve the information technology needs of the broader organization
and at the same time exploit the special skills and insights of the information
security community.
● Information security management must lead the way with skill, professionalism, and
flexibility as it works with the other communities of interest to balance the constant
trade-offs between information system utility and security.
Risk Management
If you know the enemy and know yourself, you need not fear the result of a hundred
battles. If you know yourself but not the enemy, for every victory gained you will also suffer a defeat. If you know neither the enemy nor yourself, you
will succumb in every battle.1
Accountability for Risk Management
All three communities of interest bear responsibility for the management of risks, and each
has a particular strategic role to play.
● Information security: Because members of the information security community best
understand the threats and attacks that introduce risk, they often take a leadership
role in addressing risk.
● Information technology: This group must help to build secure systems and ensure their
safe operation. For example, IT builds and operates information systems that are mindful
of operational risks and have proper controls implemented to reduce risk.
Management and users: When properly trained and kept aware of the threats faced by
the organization, this group plays a part in the early detection and response process.
Members of this community also ensure that sufficient resources (money and personnel)
are allocated to the information security and information technology groups to
meet the security needs of the organization. For example, business managers must
ensure that supporting records for orders remain intact in case of data entry error
or transaction corruption. Users must be made aware of threats to data and systems,
and educated on practices that minimize those threats.
All three communities of interest must work together to address every level of risk, ranging
from full-scale disasters (whether natural or human-made) to the smallest mistake ...
V1_I1_2012_Paper3.docx

Abstract-Intrusion Detection System used to discover attacks against computers and network Infrastructures. There are many techniques used to determine the IDS such as Outlier Detection Schemes for Anomaly Detection, K-Mean Clustering of monitoring data, classification detection and outlier detection. The data mining approaches help to determine what meets the criteria as an intrusion versus normal traffic, whether a system uses anomaly detection, misuse detection, target monitoring, or stealth probes. This paper attempts to evaluate, categorize, compares and summarizes the performance of data mining techniques to detect the intrusion.
Deep Learning based Threat / Intrusion detection system

The article is about a Threat/Intrusion Detection System, which could be used to detect such data leaks/breaches & take a preventive action to contain, if not stop the damage due to breach.
Study on Data Mining Suitability for Intrusion Detection System (IDS)

Intrusion Detection System used to discover attacks
against computers and network Infrastructures. There are many
techniques used to determine the IDS such as Outlier Detection
Schemes for Anomaly Detection, K-Mean Clustering of
monitoring data, classification detection and outlier detection.
The data mining approaches help to determine what meets the
criteria as an intrusion versus normal traffic, whether a system
uses anomaly detection, misuse detection, target monitoring, or
stealth probes. This paper attempts to evaluate, categorize,
compares and summarizes the performance of data mining
techniques to detect the intrusion
Understanding Cyber Threat Intelligence A Guide for Analysts.pdf

Improved Situational Awareness – Cyber Threat Intelligence provides organizations with a better understanding of the current threat landscape, including new and emerging threats.
Proactive Defense – By identifying potential threats before they become major issues, Cyber Threat Intelligence enables organizations to take a proactive approach to cybersecurity.
Cost Savings – Cyber Threat Intelligence can help organizations save money by minimizing the damage caused by cyber attacks and reducing the likelihood of future attacks.
Compliance – Cyber Threat Intelligence can help organizations maintain regulatory compliance by identifying and mitigating potential threats that could impact compliance.
Reputation Protection – Cyber attacks can damage an organization’s reputation. Cyber Threat Intelligence can help organizations proactively identify and mitigate potential threats to their reputation.
Conclusion
In today’s rapidly evolving cyber threat landscape, Cyber Threat Intelligence is critical for any organization that wants to protect its data, systems, and reputation. By having a dedicated Cyber Threat Intelligence Analyst on staff, organizations can stay ahead of potential threats and take a proactive approach to cybersecurity. At [Our Company Name], we are committed to providing our clients with the best possible Cyber Threat Intelligence services to ensure their cybersecurity success. Contact us today to learn more.
Implementing Cyber Threat Intelligence
Implementing Cyber Threat Intelligence can be a complex process, but it’s essential for organizations that want to stay ahead of potential cyber threats. Here are some steps organizations can take to implement Cyber Threat Intelligence successfully:
Define Objectives – The first step in implementing Cyber Threat Intelligence is to define the organization’s objectives. This includes identifying the data sources that will be used, the types of threats that will be monitored, and the reporting requirements.
Develop a Threat Intelligence Strategy – Once the objectives have been defined, the organization needs to develop a strategy for collecting, analyzing, and reporting on Cyber Threat Intelligence.
Choose the Right Tools and Technologies – Choosing the right tools and technologies is critical for successful Cyber Threat Intelligence. The organization needs to select tools that are compatible with their existing infrastructure and can provide the necessary functionality for collecting and analyzing data.
Establish a Threat Intelligence Team – Establishing a dedicated team to manage Cyber Threat Intelligence is essential. The team should include a Cyber Threat Intelligence Analyst, who is responsible for collecting and analyzing data, as well as other members who can help with reporting and response efforts.
Improved Situational Awareness – Cyber Threat Intelligence provides organizations with a better understanding of the current threat landscape, including new and emerging threats.
Proactive Def
Whitepaper- User Behavior-Based Anomaly Detection for Cyber Network Security

Whitepaper- User Behavior-Based Anomaly Detection for Cyber Network SecurityHappiest Minds Technologies
Fusion of data from multiple sources is generating new information from existing data. Now users can access any information from inside or outside of the organization very easily. It helps to increase the user productivity and knowledge shared within the organization. But this leads to a new area of network security threat, “Inside Threat”. Now users can share critical information of organization to outside the organization if he/she has access to the information. The current network security tool cannot prevent the new threat. In this paper, we address this issue by “Building real time anomaly detection system based on users’ current behavior and previous behavior”.Module 3_Lesson 7.pptx

This is about the lessons in Information, Assurance and Security. Complete module 3of lesson 7 are there so you could learn more about it. And may found helpful with your assignments, activities or etc.
The Insider Threat

This presentation was given by Eric Vaughan to a meeting of the Security Special Interest Group (SIG) of the Software Developers (SD) Forum, in Palo Alto, CA, in July 2008.
A Survey on Various Data Mining Technique in Intrusion Detection System

The intrusion detection plays an essential role in computer security. Data Mining refers to the process of extracting hidden, previously unknown and useful information from large databases. Thus data mining techniques help to detect patterns in the data set and use these patterns to detect future intrusions. Data Mining based Intrusion Detection System is combined with Multi-Agent System to improve the performance of the IDS. This paper concerned with the brief review of comparative study on applied data mining based intrusion detection techniques with their merit and demerits. This paper relay more number of applications of the data mining and also focuses extent of the data mining which will useful in the further research.
Digital Shadows and the NIST Cyber Security Framework

This mapping will help you visualize where Digital Shadows (and our SearchLight service) fits into your overall security program. It will also help you map where Digital Shadows helps across the CSF's: Identify, Protect, Detect, Respond, and Recover spectrum. To learn more about how Digital Shadows fits into your overall NIST Cybersecurity Framework strategy, you can try SearchLight for 7 days (no credit card required). Get started here: https://info.digitalshadows.com/test-drive-registration-datasheet.html
SIEM : Security Information and Event Management 

SIEM is a tool that collects, aggregates, normalizes the data and analyzes it according to pre-set rules and presents the data in human readable format
User Behavior based Anomaly Detection for Cyber Network Security

Fusion of data from multiple sources is generating new information from existing data. Now users
can access any information from inside or outside of the organization very easily. It helps to increase
the user productivity and knowledge shared within the organization. But this leads to a new area of
network security threat, “Inside Threat”. Now users can share critical information of organization to
outside the organization if he/she has access to the information. The current network security tool
cannot prevent the new threat. In this paper, we address this issue by “Building real time anomaly
detection system based on users’ current behavior and previous behavior”
Cyber Threat Intelligence

Cyber Threat Intelligence is a process in which information from different sources is collected, then analyzed to identify and detect threats against any environment. The information collected could be evidence-based knowledge that could support the context, mechanism, indicators, or implications about an already existing threat against an environment, and/or the knowledge about an upcoming threat that could potentially affect the environment. Credit: Marlabs Inc
C3602021025

International Journal of Computational Engineering Research (IJCER) is dedicated to protecting personal information and will make every reasonable effort to handle collected information appropriately. All information collected, as well as related requests, will be handled as carefully and efficiently as possible in accordance with IJCER standards for integrity and objectivity.
information security (Audit mechanism, intrusion detection, password manageme...

this slides contains the contents of Audit mechanism, intrusion detection, password management, general principals of system security and IP security
Phi 235 social media security users guide presentation

PHI 235 SOCIAL MEDIA SECURITY USERS GUIDE PRESENTATION
Outsmarting the Attackers A Deep Dive into Threat Intelligence.docx

Outsmarting the Attackers A Deep Dive into Threat Intelligence.docx
Verizon DBIR 2021

An overview of Verizon’s 2021 Data Breach Investigation Report: An Overall Summary for Industries, Incident Classification Patterns and SMBs
Dark Web Slangs-2

Escrow is related to financial transactions. When there are two parties in process of a transaction, there is a third party (neutral) that holds the 'escrow money'. This action is done to ensure that a transaction payment will be made to a seller on completion of items sent to a buyer. Until the buyer declares the seller has met the terms of purchase, the money will be held 'in escrow'.
More Related Content
Similar to Threat Intelligence Keys
A Survey: Comparative Analysis of Classifier Algorithms for DOS Attack Detection

In today's interconnected world, one of pervasive issue is how to protect system from intrusion based security attacks. It is an important issue to detect the intrusion attacks for the security of network communication.Denial of Service (DoS) attacks is evolving continuously. These attacks make network resources unavailable for legitimate users which results in massive loss of data, resources and money.Significance of Intrusion detection system (IDS) in computer network security well proven. Intrusion Detection Systems (IDSs) have become an efficient defense tool against network attacks since they allow network administrator to detect policy violations. Mining approach can play very important role in developing intrusion detection system. Classification is identified as an important technique of data mining. This paper evaluates performance of well known classification algorithms for attack classification. The key ideas are to use data mining techniques efficiently for intrusion attack classification. To implement and measure the performance of our system we used the KDD99 benchmark dataset and obtained reasonable detection rate.
RISK MITIGATION AND THREAT IDENTIFICATIONIntroductionInforma.docx

RISK MITIGATION AND THREAT IDENTIFICATION
Introduction
Information security in a modern organization exists primarily to manage information technology
(IT) risk. Managing risk is one of the key responsibilities of every manager within an
organization. In any well-developed risk management program, two formal processes are at
work. The first, risk identification and assessment, is discussed in this chapter; the second,
risk control, is the subject of the next chapter.
Each manager in the organization, regardless of his or her affiliation with one of the three
communities of interest, should focus on reducing risk as follows:
● General management must structure the IT and information security functions in ways
that will result in the successful defense of the organization’s information assets,
including data, hardware, software, procedures, and people.
● IT management must serve the information technology needs of the broader organization
and at the same time exploit the special skills and insights of the information
security community.
● Information security management must lead the way with skill, professionalism, and
flexibility as it works with the other communities of interest to balance the constant
trade-offs between information system utility and security.
Risk Management
If you know the enemy and know yourself, you need not fear the result of a hundred
battles. If you know yourself but not the enemy, for every victory gained you will also suffer a defeat. If you know neither the enemy nor yourself, you
will succumb in every battle.1
Accountability for Risk Management
All three communities of interest bear responsibility for the management of risks, and each
has a particular strategic role to play.
● Information security: Because members of the information security community best
understand the threats and attacks that introduce risk, they often take a leadership
role in addressing risk.
● Information technology: This group must help to build secure systems and ensure their
safe operation. For example, IT builds and operates information systems that are mindful
of operational risks and have proper controls implemented to reduce risk.
Management and users: When properly trained and kept aware of the threats faced by
the organization, this group plays a part in the early detection and response process.
Members of this community also ensure that sufficient resources (money and personnel)
are allocated to the information security and information technology groups to
meet the security needs of the organization. For example, business managers must
ensure that supporting records for orders remain intact in case of data entry error
or transaction corruption. Users must be made aware of threats to data and systems,
and educated on practices that minimize those threats.
All three communities of interest must work together to address every level of risk, ranging
from full-scale disasters (whether natural or human-made) to the smallest mistake ...
V1_I1_2012_Paper3.docx

Abstract-Intrusion Detection System used to discover attacks against computers and network Infrastructures. There are many techniques used to determine the IDS such as Outlier Detection Schemes for Anomaly Detection, K-Mean Clustering of monitoring data, classification detection and outlier detection. The data mining approaches help to determine what meets the criteria as an intrusion versus normal traffic, whether a system uses anomaly detection, misuse detection, target monitoring, or stealth probes. This paper attempts to evaluate, categorize, compares and summarizes the performance of data mining techniques to detect the intrusion.
Deep Learning based Threat / Intrusion detection system

The article is about a Threat/Intrusion Detection System, which could be used to detect such data leaks/breaches & take a preventive action to contain, if not stop the damage due to breach.
Study on Data Mining Suitability for Intrusion Detection System (IDS)

Intrusion Detection System used to discover attacks
against computers and network Infrastructures. There are many
techniques used to determine the IDS such as Outlier Detection
Schemes for Anomaly Detection, K-Mean Clustering of
monitoring data, classification detection and outlier detection.
The data mining approaches help to determine what meets the
criteria as an intrusion versus normal traffic, whether a system
uses anomaly detection, misuse detection, target monitoring, or
stealth probes. This paper attempts to evaluate, categorize,
compares and summarizes the performance of data mining
techniques to detect the intrusion
Understanding Cyber Threat Intelligence A Guide for Analysts.pdf

Improved Situational Awareness – Cyber Threat Intelligence provides organizations with a better understanding of the current threat landscape, including new and emerging threats.
Proactive Defense – By identifying potential threats before they become major issues, Cyber Threat Intelligence enables organizations to take a proactive approach to cybersecurity.
Cost Savings – Cyber Threat Intelligence can help organizations save money by minimizing the damage caused by cyber attacks and reducing the likelihood of future attacks.
Compliance – Cyber Threat Intelligence can help organizations maintain regulatory compliance by identifying and mitigating potential threats that could impact compliance.
Reputation Protection – Cyber attacks can damage an organization’s reputation. Cyber Threat Intelligence can help organizations proactively identify and mitigate potential threats to their reputation.
Conclusion
In today’s rapidly evolving cyber threat landscape, Cyber Threat Intelligence is critical for any organization that wants to protect its data, systems, and reputation. By having a dedicated Cyber Threat Intelligence Analyst on staff, organizations can stay ahead of potential threats and take a proactive approach to cybersecurity. At [Our Company Name], we are committed to providing our clients with the best possible Cyber Threat Intelligence services to ensure their cybersecurity success. Contact us today to learn more.
Implementing Cyber Threat Intelligence
Implementing Cyber Threat Intelligence can be a complex process, but it’s essential for organizations that want to stay ahead of potential cyber threats. Here are some steps organizations can take to implement Cyber Threat Intelligence successfully:
Define Objectives – The first step in implementing Cyber Threat Intelligence is to define the organization’s objectives. This includes identifying the data sources that will be used, the types of threats that will be monitored, and the reporting requirements.
Develop a Threat Intelligence Strategy – Once the objectives have been defined, the organization needs to develop a strategy for collecting, analyzing, and reporting on Cyber Threat Intelligence.
Choose the Right Tools and Technologies – Choosing the right tools and technologies is critical for successful Cyber Threat Intelligence. The organization needs to select tools that are compatible with their existing infrastructure and can provide the necessary functionality for collecting and analyzing data.
Establish a Threat Intelligence Team – Establishing a dedicated team to manage Cyber Threat Intelligence is essential. The team should include a Cyber Threat Intelligence Analyst, who is responsible for collecting and analyzing data, as well as other members who can help with reporting and response efforts.
Improved Situational Awareness – Cyber Threat Intelligence provides organizations with a better understanding of the current threat landscape, including new and emerging threats.
Proactive Def
Whitepaper- User Behavior-Based Anomaly Detection for Cyber Network Security

Whitepaper- User Behavior-Based Anomaly Detection for Cyber Network SecurityHappiest Minds Technologies
Fusion of data from multiple sources is generating new information from existing data. Now users can access any information from inside or outside of the organization very easily. It helps to increase the user productivity and knowledge shared within the organization. But this leads to a new area of network security threat, “Inside Threat”. Now users can share critical information of organization to outside the organization if he/she has access to the information. The current network security tool cannot prevent the new threat. In this paper, we address this issue by “Building real time anomaly detection system based on users’ current behavior and previous behavior”.Module 3_Lesson 7.pptx

This is about the lessons in Information, Assurance and Security. Complete module 3of lesson 7 are there so you could learn more about it. And may found helpful with your assignments, activities or etc.
The Insider Threat

This presentation was given by Eric Vaughan to a meeting of the Security Special Interest Group (SIG) of the Software Developers (SD) Forum, in Palo Alto, CA, in July 2008.
A Survey on Various Data Mining Technique in Intrusion Detection System

The intrusion detection plays an essential role in computer security. Data Mining refers to the process of extracting hidden, previously unknown and useful information from large databases. Thus data mining techniques help to detect patterns in the data set and use these patterns to detect future intrusions. Data Mining based Intrusion Detection System is combined with Multi-Agent System to improve the performance of the IDS. This paper concerned with the brief review of comparative study on applied data mining based intrusion detection techniques with their merit and demerits. This paper relay more number of applications of the data mining and also focuses extent of the data mining which will useful in the further research.
Digital Shadows and the NIST Cyber Security Framework

This mapping will help you visualize where Digital Shadows (and our SearchLight service) fits into your overall security program. It will also help you map where Digital Shadows helps across the CSF's: Identify, Protect, Detect, Respond, and Recover spectrum. To learn more about how Digital Shadows fits into your overall NIST Cybersecurity Framework strategy, you can try SearchLight for 7 days (no credit card required). Get started here: https://info.digitalshadows.com/test-drive-registration-datasheet.html
SIEM : Security Information and Event Management 

SIEM is a tool that collects, aggregates, normalizes the data and analyzes it according to pre-set rules and presents the data in human readable format
User Behavior based Anomaly Detection for Cyber Network Security

Fusion of data from multiple sources is generating new information from existing data. Now users
can access any information from inside or outside of the organization very easily. It helps to increase
the user productivity and knowledge shared within the organization. But this leads to a new area of
network security threat, “Inside Threat”. Now users can share critical information of organization to
outside the organization if he/she has access to the information. The current network security tool
cannot prevent the new threat. In this paper, we address this issue by “Building real time anomaly
detection system based on users’ current behavior and previous behavior”
Cyber Threat Intelligence

Cyber Threat Intelligence is a process in which information from different sources is collected, then analyzed to identify and detect threats against any environment. The information collected could be evidence-based knowledge that could support the context, mechanism, indicators, or implications about an already existing threat against an environment, and/or the knowledge about an upcoming threat that could potentially affect the environment. Credit: Marlabs Inc
C3602021025

International Journal of Computational Engineering Research (IJCER) is dedicated to protecting personal information and will make every reasonable effort to handle collected information appropriately. All information collected, as well as related requests, will be handled as carefully and efficiently as possible in accordance with IJCER standards for integrity and objectivity.
information security (Audit mechanism, intrusion detection, password manageme...

this slides contains the contents of Audit mechanism, intrusion detection, password management, general principals of system security and IP security
Phi 235 social media security users guide presentation

PHI 235 SOCIAL MEDIA SECURITY USERS GUIDE PRESENTATION
Outsmarting the Attackers A Deep Dive into Threat Intelligence.docx

Outsmarting the Attackers A Deep Dive into Threat Intelligence.docx
Similar to Threat Intelligence Keys (20)
A Survey: Comparative Analysis of Classifier Algorithms for DOS Attack Detection

A Survey: Comparative Analysis of Classifier Algorithms for DOS Attack Detection
RISK MITIGATION AND THREAT IDENTIFICATIONIntroductionInforma.docx

RISK MITIGATION AND THREAT IDENTIFICATIONIntroductionInforma.docx
Deep Learning based Threat / Intrusion detection system

Deep Learning based Threat / Intrusion detection system
Study on Data Mining Suitability for Intrusion Detection System (IDS)

Study on Data Mining Suitability for Intrusion Detection System (IDS)
Understanding Cyber Threat Intelligence A Guide for Analysts.pdf

Understanding Cyber Threat Intelligence A Guide for Analysts.pdf
Whitepaper- User Behavior-Based Anomaly Detection for Cyber Network Security

Whitepaper- User Behavior-Based Anomaly Detection for Cyber Network Security
A Survey on Various Data Mining Technique in Intrusion Detection System

A Survey on Various Data Mining Technique in Intrusion Detection System
Digital Shadows and the NIST Cyber Security Framework

Digital Shadows and the NIST Cyber Security Framework
User Behavior based Anomaly Detection for Cyber Network Security

User Behavior based Anomaly Detection for Cyber Network Security
information security (Audit mechanism, intrusion detection, password manageme...

information security (Audit mechanism, intrusion detection, password manageme...
Phi 235 social media security users guide presentation

Phi 235 social media security users guide presentation
Outsmarting the Attackers A Deep Dive into Threat Intelligence.docx

Outsmarting the Attackers A Deep Dive into Threat Intelligence.docx
More from SOCRadar Inc
Verizon DBIR 2021

An overview of Verizon’s 2021 Data Breach Investigation Report: An Overall Summary for Industries, Incident Classification Patterns and SMBs
Dark Web Slangs-2

Escrow is related to financial transactions. When there are two parties in process of a transaction, there is a third party (neutral) that holds the 'escrow money'. This action is done to ensure that a transaction payment will be made to a seller on completion of items sent to a buyer. Until the buyer declares the seller has met the terms of purchase, the money will be held 'in escrow'.
Cost for Failed Certificate Management Practices

The Impact of Unsecured Digital Identities report includes the results of this survey for five scenarios, including the operational and compliance costs, the cost of security exploits, and the likelihood of occurring in the next two years.
Types of impersonating

Using social engineering skills and of course other hacking skills, threat actors send legitimate-looking emails, impersonated domains or create completely cloned websites to create traps for organizations. In able to thwart these actions, you should know what the difference between these types of cybercrimes is.
Type of Malware

Malware is any software intentionally designed to cause damage to a computer, server, client, or computer network.
Type of Threat Actor

Threat Actor: cyber terrorist, hactivist, insider threat, organized hacker, state sponsored hacker
More from SOCRadar Inc (8)
Recently uploaded
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, Product School
Welocme to ViralQR, your best QR code generator.

Welcome to ViralQR, your best QR code generator available on the market!
At ViralQR, we design static and dynamic QR codes. Our mission is to make business operations easier and customer engagement more powerful through the use of QR technology. Be it a small-scale business or a huge enterprise, our easy-to-use platform provides multiple choices that can be tailored according to your company's branding and marketing strategies.
Our Vision
We are here to make the process of creating QR codes easy and smooth, thus enhancing customer interaction and making business more fluid. We very strongly believe in the ability of QR codes to change the world for businesses in their interaction with customers and are set on making that technology accessible and usable far and wide.
Our Achievements
Ever since its inception, we have successfully served many clients by offering QR codes in their marketing, service delivery, and collection of feedback across various industries. Our platform has been recognized for its ease of use and amazing features, which helped a business to make QR codes.
Our Services
At ViralQR, here is a comprehensive suite of services that caters to your very needs:
Static QR Codes: Create free static QR codes. These QR codes are able to store significant information such as URLs, vCards, plain text, emails and SMS, Wi-Fi credentials, and Bitcoin addresses.
Dynamic QR codes: These also have all the advanced features but are subscription-based. They can directly link to PDF files, images, micro-landing pages, social accounts, review forms, business pages, and applications. In addition, they can be branded with CTAs, frames, patterns, colors, and logos to enhance your branding.
Pricing and Packages
Additionally, there is a 14-day free offer to ViralQR, which is an exceptional opportunity for new users to take a feel of this platform. One can easily subscribe from there and experience the full dynamic of using QR codes. The subscription plans are not only meant for business; they are priced very flexibly so that literally every business could afford to benefit from our service.
Why choose us?
ViralQR will provide services for marketing, advertising, catering, retail, and the like. The QR codes can be posted on fliers, packaging, merchandise, and banners, as well as to substitute for cash and cards in a restaurant or coffee shop. With QR codes integrated into your business, improve customer engagement and streamline operations.
Comprehensive Analytics
Subscribers of ViralQR receive detailed analytics and tracking tools in light of having a view of the core values of QR code performance. Our analytics dashboard shows aggregate views and unique views, as well as detailed information about each impression, including time, device, browser, and estimated location by city and country.
So, thank you for choosing ViralQR; we have an offer of nothing but the best in terms of QR code services to meet business diversity!
Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™

In questo evento online gratuito, organizzato dalla Community Italiana di UiPath, potrai esplorare le nuove funzionalità di Autopilot, il tool che integra l'Intelligenza Artificiale nei processi di sviluppo e utilizzo delle Automazioni.
📕 Vedremo insieme alcuni esempi dell'utilizzo di Autopilot in diversi tool della Suite UiPath:
Autopilot per Studio Web
Autopilot per Studio
Autopilot per Apps
Clipboard AI
GenAI applicata alla Document Understanding
👨🏫👨💻 Speakers:
Stefano Negro, UiPath MVPx3, RPA Tech Lead @ BSP Consultant
Flavio Martinelli, UiPath MVP 2023, Technical Account Manager @UiPath
Andrei Tasca, RPA Solutions Team Lead @NTT Data
The Art of the Pitch: WordPress Relationships and Sales

Clients don’t know what they don’t know. What web solutions are right for them? How does WordPress come into the picture? How do you make sure you understand scope and timeline? What do you do if sometime changes?
All these questions and more will be explored as we talk about matching clients’ needs with what your agency offers without pulling teeth or pulling your hair out. Practical tips, and strategies for successful relationship building that leads to closing the deal.
GraphRAG is All You need? LLM & Knowledge Graph

Guy Korland, CEO and Co-founder of FalkorDB, will review two articles on the integration of language models with knowledge graphs.
1. Unifying Large Language Models and Knowledge Graphs: A Roadmap.
https://arxiv.org/abs/2306.08302
2. Microsoft Research's GraphRAG paper and a review paper on various uses of knowledge graphs:
https://www.microsoft.com/en-us/research/blog/graphrag-unlocking-llm-discovery-on-narrative-private-data/
DevOps and Testing slides at DASA Connect

My and Rik Marselis slides at 30.5.2024 DASA Connect conference. We discuss about what is testing, then what is agile testing and finally what is Testing in DevOps. Finally we had lovely workshop with the participants trying to find out different ways to think about quality and testing in different parts of the DevOps infinity loop.
Generative AI Deep Dive: Advancing from Proof of Concept to Production

Join Maher Hanafi, VP of Engineering at Betterworks, in this new session where he'll share a practical framework to transform Gen AI prototypes into impactful products! He'll delve into the complexities of data collection and management, model selection and optimization, and ensuring security, scalability, and responsible use.
UiPath Test Automation using UiPath Test Suite series, part 3

Welcome to UiPath Test Automation using UiPath Test Suite series part 3. In this session, we will cover desktop automation along with UI automation.
Topics covered:
UI automation Introduction,
UI automation Sample
Desktop automation flow
Pradeep Chinnala, Senior Consultant Automation Developer @WonderBotz and UiPath MVP
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovation With Your Product by VP of Product Design, Warner Music Group
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

💥 Speed, accuracy, and scaling – discover the superpowers of GenAI in action with UiPath Document Understanding and Communications Mining™:
See how to accelerate model training and optimize model performance with active learning
Learn about the latest enhancements to out-of-the-box document processing – with little to no training required
Get an exclusive demo of the new family of UiPath LLMs – GenAI models specialized for processing different types of documents and messages
This is a hands-on session specifically designed for automation developers and AI enthusiasts seeking to enhance their knowledge in leveraging the latest intelligent document processing capabilities offered by UiPath.
Speakers:
👨🏫 Andras Palfi, Senior Product Manager, UiPath
👩🏫 Lenka Dulovicova, Product Program Manager, UiPath
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

In today's fast-changing business world, Companies that adapt and embrace new ideas often need help to keep up with the competition. However, fostering a culture of innovation takes much work. It takes vision, leadership and willingness to take risks in the right proportion. Sachin Dev Duggal, co-founder of Builder.ai, has perfected the art of this balance, creating a company culture where creativity and growth are nurtured at each stage.
Epistemic Interaction - tuning interfaces to provide information for AI support

Paper presented at SYNERGY workshop at AVI 2024, Genoa, Italy. 3rd June 2024
https://alandix.com/academic/papers/synergy2024-epistemic/
As machine learning integrates deeper into human-computer interactions, the concept of epistemic interaction emerges, aiming to refine these interactions to enhance system adaptability. This approach encourages minor, intentional adjustments in user behaviour to enrich the data available for system learning. This paper introduces epistemic interaction within the context of human-system communication, illustrating how deliberate interaction design can improve system understanding and adaptation. Through concrete examples, we demonstrate the potential of epistemic interaction to significantly advance human-computer interaction by leveraging intuitive human communication strategies to inform system design and functionality, offering a novel pathway for enriching user-system engagements.
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

In this session I delve into the encryption technology used in Microsoft 365 and Microsoft Purview. Including the concepts of Customer Key and Double Key Encryption.
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

The publishing industry has been selling digital audiobooks and ebooks for over a decade and has found its groove. What’s changed? What has stayed the same? Where do we go from here? Join a group of leading sales peers from across the industry for a conversation about the lessons learned since the popularization of digital books, best practices, digital book supply chain management, and more.
Link to video recording: https://bnctechforum.ca/sessions/selling-digital-books-in-2024-insights-from-industry-leaders/
Presented by BookNet Canada on May 28, 2024, with support from the Department of Canadian Heritage.
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

91mobiles recently conducted a Smart TV Buyer Insights Survey in which we asked over 3,000 respondents about the TV they own, aspects they look at on a new TV, and their TV buying preferences.
Recently uploaded (20)
FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf

FIDO Alliance Osaka Seminar: Passkeys and the Road Ahead.pdf
How world-class product teams are winning in the AI era by CEO and Founder, P...

How world-class product teams are winning in the AI era by CEO and Founder, P...
Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™

Le nuove frontiere dell'AI nell'RPA con UiPath Autopilot™
The Art of the Pitch: WordPress Relationships and Sales

The Art of the Pitch: WordPress Relationships and Sales
Free Complete Python - A step towards Data Science

Free Complete Python - A step towards Data Science
Monitoring Java Application Security with JDK Tools and JFR Events

Monitoring Java Application Security with JDK Tools and JFR Events
FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf

FIDO Alliance Osaka Seminar: FIDO Security Aspects.pdf
Generative AI Deep Dive: Advancing from Proof of Concept to Production

Generative AI Deep Dive: Advancing from Proof of Concept to Production
UiPath Test Automation using UiPath Test Suite series, part 3

UiPath Test Automation using UiPath Test Suite series, part 3
De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...

De-mystifying Zero to One: Design Informed Techniques for Greenfield Innovati...
Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...

Dev Dives: Train smarter, not harder – active learning and UiPath LLMs for do...
Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...

Builder.ai Founder Sachin Dev Duggal's Strategic Approach to Create an Innova...
Epistemic Interaction - tuning interfaces to provide information for AI support

Epistemic Interaction - tuning interfaces to provide information for AI support
Encryption in Microsoft 365 - ExpertsLive Netherlands 2024

Encryption in Microsoft 365 - ExpertsLive Netherlands 2024
Transcript: Selling digital books in 2024: Insights from industry leaders - T...

Transcript: Selling digital books in 2024: Insights from industry leaders - T...
Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf

Smart TV Buyer Insights Survey 2024 by 91mobiles.pdf
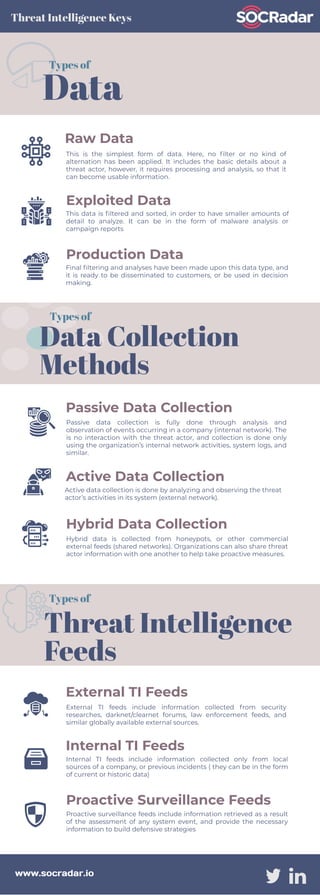
Threat Intelligence Keys
- 1. Raw Data This is the simplest form of data. Here, no filter or no kind of alternation has been applied. It includes the basic details about a threat actor, however, it requires processing and analysis, so that it can become usable information. Exploited Data This data is filtered and sorted, in order to have smaller amounts of detail to analyze. It can be in the form of malware analysis or campaign reports Production Data Final filtering and analyses have been made upon this data type, and it is ready to be disseminated to customers, or be used in decision making. Data Types of Threat Intelligence Keys Passive Data Collection Passive data collection is fully done through analysis and observation of events occurring in a company (internal network). The is no interaction with the threat actor, and collection is done only using the organization’s internal network activities, system logs, and similar. Active Data Collection Active data collection is done by analyzing and observing the threat actor’s activities in its system (external network). Hybrid Data Collection Hybrid data is collected from honeypots, or other commercial external feeds (shared networks). Organizations can also share threat actor information with one another to help take proactive measures. Data Collection Methods Types of External TI Feeds External TI feeds include information collected from security researches, darknet/clearnet forums, law enforcement feeds, and similar globally available external sources. Internal TI Feeds Internal TI feeds include information collected only from local sources of a company, or previous incidents ( they can be in the form of current or historic data) Proactive Surveillance Feeds Proactive surveillance feeds include information retrieved as a result of the assessment of any system event, and provide the necessary information to build defensive strategies www.socradar.io Types of Threat Intelligence Feeds
